Attached files
| file | filename |
|---|---|
| EX-32.2 - EX-32.2 - Trinity Capital Inc. | tcpp-20201231xex32d2.htm |
| EX-32.1 - EX-32.1 - Trinity Capital Inc. | tcpp-20201231xex32d1.htm |
| EX-31.2 - EX-31.2 - Trinity Capital Inc. | tcpp-20201231xex31d2.htm |
| EX-31.1 - EX-31.1 - Trinity Capital Inc. | tcpp-20201231xex31d1.htm |
| EX-10.13 - EX-10.13 - Trinity Capital Inc. | tcpp-20201231xex10d13.htm |
| EX-4.9 - EX-4.9 - Trinity Capital Inc. | tcpp-20201231xex4d9.htm |
UNITED STATES
SECURITIES AND EXCHANGE COMMISSION
Washington, D.C. 20549
FORM 10-K
(Mark One)
⌧ | ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 |
For the Fiscal Year Ended December 31, 2020
OR
◻ | TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 |
Commission file number: 000-56139
TRINITY CAPITAL INC.
(Exact name of registrant as specified in its charter)
Maryland | 35-2670395 |
(State or other jurisdiction of incorporation or | (IRS Employer Identification No.) |
3075 West Ray Road | 85226 |
(Address of principal executive offices) | (Zip Code) |
(480) 374-5350
(Registrant’s telephone number, including area code)
Securities registered pursuant to Section 12(b) of the Act:
Title of Each Class |
| Trading Symbol(s) |
| Name of each exchange on which registered |
Common Stock, par value $0.001 per share | | TRIN | | Nasdaq Global Select Market |
Securities registered pursuant to Section 12(g) of the Act: None
Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. Yes ◻ No ⌧
Indicate by check mark if the registrant is not required to file reports pursuant to Section 13 or 15(d) of the Act. Yes ◻ No ⌧
Indicate by check mark whether the registrant (1) has filed all reports required to be filed by Section 13 or 15(d) of the Securities Exchange Act of 1934 during the preceding 12 months (or for such shorter period that the registrant was required to file such reports), and (2) has been subject to such filing requirements for the past 90 days. Yes ⌧ No ◻
Indicate by check mark whether the registrant has submitted electronically every Interactive Data File required to be submitted pursuant to Rule 405 of Regulation S-T (§232.405 of this chapter) during the preceding 12 months (or for such shorter period that the registrant was required to submit such files). Yes ◻ No ◻
Indicate by check mark whether the registrant is a large accelerated filer, an accelerated filer, a non-accelerated filer, a smaller reporting company, or an emerging growth company. See the definitions of “large accelerated filer,” “accelerated filer”, “smaller reporting company” and “emerging growth company” in Rule 12b-2 of the Exchange Act:
Large accelerated filer | ◻ | Accelerated filer | ◻ |
Non-accelerated filer | ⌧ | Smaller reporting company | ◻ |
|
| Emerging growth company | ⌧ |
If an emerging growth company, indicate by check mark if the registrant has elected not to use the extended transition period for complying with any new or revised financial accounting standards provided pursuant to Section 13(a) of the Exchange Act. ◻
Indicate by check mark whether the registrant has filed a report on and attestation to its management’s assessment of the effectiveness of its internal control over financial reporting under Section 404(b) of the Sarbanes-Oxley Act (15 U.S.C. 7262(b)) by the registered public accounting firm that prepared or issued its audit report. ◻
Indicate by check mark whether the registrant is a shell Company (as defined in Rule 12b-2 of the Act). Yes ◻ No ⌧
The aggregate market value of the common stock held by non-affiliates of the registrant as of June 30, 2020 has not been provided because trading of the registrant’s common stock on the Nasdaq Global Select Market did not commence until January 29, 2021.
As of March 3, 2021, the registrant had 26,415,275 shares of common stock ($0.001 par value per share) outstanding.
DOCUMENTS INCORPORATED BY REFERENCE
Portions of the registrant’s definitive Proxy Statement for its 2021 Annual Meeting of Stockholders, to be filed with the Securities and Exchange Commission within 120 days following the end of the registrant’s fiscal year, are incorporated by reference into Part III of this annual report on Form 10-K.
TRINITY CAPITAL INC.
FORM 10-K
2
Cautionary Note Regarding Forward-Looking Statements
This annual report on Form 10-K contains forward-looking statements that involve substantial risks and uncertainties. Such statements involve known and unknown risks, uncertainties and other factors, and undue reliance should not be placed thereon. Any statements about our expectations, beliefs, plans, predictions, forecasts, objectives, assumptions or future events or performance are not historical facts and may be forward-looking. These statements are often, but not always, made through the use of words or phrases such as “anticipate,” “believes,” “can,” “could,” “may,” “predicts,” “potential,” “should,” “will,” “estimate,” “plans,” “projects,” “continuing,” “ongoing,” “expects,” “intends” and similar words or phrases. Accordingly, these statements are only predictions and involve estimates, known and unknown risks, assumptions and uncertainties that could cause actual results to differ materially from those expressed in them. Our actual results could differ materially from those anticipated in such forward-looking statements as a result of several factors discussed under Item 1A. “Risk Factors” of Part I of this annual report on Form 10-K, including, but not limited to, the following:
| ● | our limited operating history as a business development company (“BDC”); |
| ● | our future operating results, including the impact of the SARS-CoV-2 (“COVID-19”) pandemic; |
| ● | our dependence upon our management team and key investment professionals; |
| ● | our ability to manage our business and future growth; |
| ● | risks related to investments in growth stage companies, other venture capital-backed companies and generally U.S. companies; |
| ● | the ability of our portfolio companies to achieve their objectives; |
| ● | the use of leverage; |
| ● | risks related to the uncertainty of the value of our portfolio investments; |
| ● | changes in political, economic or industry conditions, the interest rate environment or conditions affecting the financial and capital markets, including as a result of the COVID-19 pandemic; |
| ● | uncertainty surrounding the financial and/or political stability of the United States, the United Kingdom, the European Union and China, including as a result of the COVID-19 pandemic; |
| ● | the dependence of our future success on the general economy and its impact on the industries in which we invest; |
| ● | risks related to changes in interest rates, our expenses, and other general economic conditions and the effect on our net investment income; |
| ● | the effect of the decommissioning of LIBOR; |
| ● | the effect of changes in tax laws and regulations and interpretations thereof; |
| ● | the impact on our business of new or amended legislation or regulations; |
| ● | risks related to market volatility, including general price and volume fluctuations in stock markets; |
| ● | our ability to make distributions, including as a result of the COVID-19 pandemic; and |
| ● | our ability to maintain our status as a BDC under the Investment Company Act of 1940, as amended and qualify annually for tax treatment as a regulated investment company under Subchapter M of the Internal Revenue Code of 1986, as amended. |
Additionally, there may be other risks that are otherwise described from time to time in the reports that we file with the Securities and Exchange Commission. Any forward-looking statements in this annual report on Form 10-K should be considered in light of various important factors, including the risks and uncertainties listed above, as well as others. All forward-looking statements are necessarily only estimates of future results, and there can be no assurance that actual results will not differ materially from expectations, and, therefore, you are cautioned not to place undue reliance on such statements. Any forward-looking statements are qualified in their entirety by reference to the risk factors discussed throughout this annual report on Form 10-K. See “Item 1A. Risk Factors.” Further, any forward-looking statement speaks only as of the date on which it is made, and we undertake no obligation to update any forward-looking statement to reflect events or circumstances after the date on which the statement is made or to reflect the occurrence of unanticipated events. Because we are an investment company, the forward-looking statements and projections contained in this annual report on Form 10-K are excluded from the safe harbor protections provided by Section 21E of the Securities Exchange Act of 1934, as amended (the “Exchange Act”) (the “safe harbor” provision of the Private Securities Litigation Reform Act of 1995).
3
Except where the context suggests otherwise, the terms “we,” “us,” “our,” “the Company,” and “Trinity” refer to Trinity Capital Inc. and its consolidated subsidiaries.
Organization
Trinity Capital Inc. (“TCI”), incorporated in Maryland on August 12, 2019, is an internally managed, closed-end, non-diversified management investment company that has elected to be regulated as a business development company (“BDC”) under the Investment Company Act of 1940, as amended (the “1940 Act”). Because TCI is internally managed, all of the executive officers and employees are employed by the Company. Therefore, the Company does not pay any external investment advisory fees, but instead directly incurs the operating costs associated with employing investment and portfolio management professionals.
On January 16, 2020, the Company completed a private equity offering (the “Private Common Stock Offering”) of shares of its common stock pursuant to which it issued and sold 7,000,000 shares for gross proceeds of approximately $105.0 million. An over-allotment option related to the Private Common Stock Offering was exercised in full and on January 29, 2020 the Company issued and sold an additional 1,333,333 shares of its common stock for gross proceeds of approximately $20 million. As a result, in total, the Company issued and sold 8,333,333 shares of its common stock for total aggregate gross proceeds of approximately $125.0 million.
Concurrent with the initial closing of the Private Common Stock Offering, the Company completed a private debt offering (the “144A Note Offering” and together with the Private Common Stock Offering, the “Private Offerings”) of $105.0 million in aggregate principal amount of the Company’s unsecured 7.00% Notes due 2025 (the “2025 Notes”). An over-allotment option related to the 144A Note Offering was exercised in full and on January 29, 2020 the Company issued and sold an additional $20.0 million in aggregate principal amount of the 2025 Notes. As a result, the Company issued and sold $125.0 million in aggregate principal amount of the 2025 Notes.
On January 16, 2020, through a series of transactions (the “Formation Transactions”), we acquired Trinity Capital Investment, LLC ( “TCI, LLC”), Trinity Capital Fund II, L.P. (“Fund II”), Trinity Capital Fund III, L.P. (“Fund III”), Trinity Capital Fund IV, L.P. (“Fund IV”) and Trinity Sidecar Income Fund, L.P. (“Sidecar Fund,” and collectively, the “Legacy Funds”) and all of their respective assets (the “Legacy Assets”), including their respective investment portfolios (the “Legacy Portfolio”), as well as Trinity Capital Holdings, LLC (“Trinity Capital Holdings”), a holding company whose subsidiaries managed and/or had the right to receive fees from certain of the Legacy Funds. We used a portion of the proceeds from the Private Offerings to complete these transactions.
In the Formation Transactions, the Legacy Funds were merged with and into the Company, and we issued 9,183,185 shares of our common stock for an aggregate amount of approximately $137.7 million and paid approximately $108.7 million in cash to the Legacy Funds’ investors, which included the general partners/managers of the Legacy Funds (the “Legacy Investors”), to acquire the Legacy Funds and all of their respective assets, including the Legacy Portfolio. Our senior management team, led by Steven L. Brown, comprises the majority of the senior management team that managed the Legacy Funds and sourced the Legacy Portfolio.
As part of the Formation Transactions, we also acquired 100% of the equity interests of Trinity Capital Holdings for an aggregate purchase price of $10.0 million, which was comprised of 533,332 shares of our common stock, totaling approximately $8.0 million, and approximately $2.0 million in cash. In connection with the acquisition of such equity interests, the Company also assumed a $3.5 million severance related liability with respect to a former member of certain general partners of certain Legacy Funds. In connection with the acquisition of Trinity Capital Holdings, approximately $13.5 million (consisting of the aggregate purchase price and severance related liability assumed) was expensed to Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds in the Consolidated Statements of Operations. As a result of the Formation Transactions, Trinity Capital Holdings became a wholly owned subsidiary of the Company.
4
Trinity Funding 1, LLC (“TF1”) was formed on August 14, 2019 as a wholly owned subsidiary of Fund II to serve as a bankruptcy-remote entity for purposes of securing lending. On January 16, 2020, in connection with the Formation Transactions, the Company acquired TF1 through Fund II and became a party to, and assumed, a $300 million credit agreement (as amended, the “Credit Facility”) with Credit Suisse AG (“Credit Suisse”) through TF1. TF1 is included as a consolidated subsidiary of TCI in TCI’s consolidated financial statements.
On January 29, 2021, our common stock began trading on the Nasdaq Global Select Market under the ticker symbol “TRIN,” and we completed our initial public offering of our common stock, par value $0.001, (“IPO”) on February 2, 2021.
In connection with the filing of our 2020 annual tax return, TCI will elect to be treated as a regulated investment company (“RIC”) under Subchapter M of the Internal Revenue Code of 1986, as amended (the “Code”), for U.S. federal income tax purposes. As a result, the Company generally does not pay corporate-level U.S. federal income taxes on any net ordinary taxable income or capital gains that it distributes to its stockholders.
Overview
We provide debt, including loans and equipment financings, to growth stage companies, including venture-backed companies and companies with institutional equity investors. Our investment objective is to generate current income and, to a lesser extent, capital appreciation through our investments. We seek to achieve our investment objective by making investments consisting primarily of term loans and equipment financings and, to a lesser extent, working capital loans, equity and equity-related investments. Our equipment financings involve loans for general or specific use, including acquiring equipment, that are secured by the equipment or other assets of the portfolio company. In addition, we may obtain warrants or contingent exit fees from many of our portfolio companies, providing an additional potential source of investment returns. The warrants entitle us to purchase preferred or common ownership shares of a portfolio company, and we typically target the amount of such warrants to scale in proportion to the amount of the debt or equipment financing. Contingent exit fees are cash fees payable upon the consummation of certain trigger events, such as a successful change of control or initial public offering of the portfolio company. In addition, we may obtain rights to purchase additional shares of our portfolio companies in subsequent equity financing rounds.
We target investments in growth stage companies with institutional investor support, experienced management teams, promising products and offerings, and large expanding markets. We define “growth stage companies” as companies that have significant ownership and active participation by sponsors and expected annual revenues of up to $100 million. These companies typically have begun to have success selling their products to the market and need additional capital to expand their operations and sales. Despite often achieving growing revenues, these types of companies typically have limited financing options to fund their growth. Equity, being dilutive in nature, is generally the most expensive form of capital available, while traditional bank financing is rarely available, given the lifecycle stage of these companies. Financing from us bridges this financing gap, providing companies with growth capital, which may result in improved profitability, less dilution for all equity investors, and increased enterprise value. Subject to the requirements of the 1940 Act, we are not limited to investing in any particular industry or geographic area and seek to invest in under-financed segments of the private credit markets.
Our loans and equipment financings may have initial interest-only periods of up to 24 months and generally fully amortize over a total term of up to 60 months. These investments are typically secured by a blanket first position lien, a specific asset lien on mission-critical assets and/or a blanket second position lien. We may also make a limited number of direct equity and equity-related investments in conjunction with our debt investments. We target growth stage companies that have recently issued equity to raise cash to offset potential cash flow needs related to projected growth, have achieved positive cash flow to cover debt service, or have institutional investors committed to providing additional funding. A loan or equipment financing may be structured to tie the amortization of the loan or equipment financing to the portfolio company’s projected cash balances while cash is still available for operations. As such, the loan or equipment financing may have a reduced risk of default. We believe that the amortizing nature of our investments will mitigate risk and significantly reduce the risk of our investments over a relatively short period. We focus on protecting and recovering principal in each investment and structure our investments to provide downside protection.
5
Our loans and equipment financings generally range from $2 million to $30 million and we generally limit each loan or equipment financing to approximately five percent or less of our total assets. We believe investments of this scale are generally sufficient to support near-term growth needs of most growth stage companies. We seek to structure our loans and equipment financings such that amortization of the amount invested quickly reduces our risk exposure. Leveraging the experience of our investment professionals, we seek to target companies at their growth stage of development and to identify financing opportunities ignored by the traditional direct lending community.
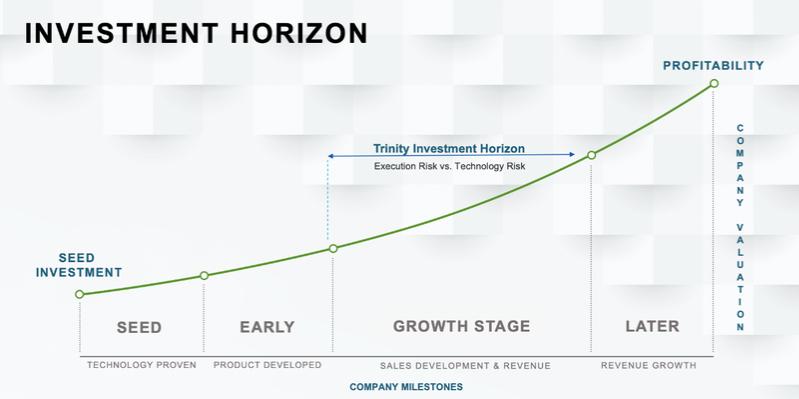
The following illustrates the lifecycle stage at which we seek to invest in our portfolio companies, although we may, at our discretion, invest in other lifecycle stages.
Human Capital Resources and Management Team
We are an internally managed BDC employing 34 dedicated professionals as of December 31, 2020, including 17 investment, origination and portfolio management professionals, all of whom have experience working on investment and financing transactions for growth and early-stage companies. All of our employees are located in the United States.
Our management team has prior management experience, including with early-stage tech startups, and employs a highly systematized approach. Our senior management team, led by Steven L. Brown, comprises the majority of the senior management team that managed the Legacy Funds and sourced the Legacy Portfolio.
All investment decisions are made by the Investment Committee, whose members consist of Steven L. Brown, Gerald Harder, Kyle Brown and Ron Kundich. We consider these individuals to be our portfolio managers. The Investment Committee approves proposed investments by majority consent, which majority must include Steven L. Brown, in accordance with investment guidelines and procedures established by the Investment Committee.
Our employees drive the success of our business and investment strategy, including achieving our investment objective. We offer competitive compensation, benefits and training programs to develop our employees’ skills and expertise. We are committed to providing a safe, harassment-free work environment guided by principles of fair and equal treatment and focused on employee engagement.
In response to the COVID-19 pandemic, we instituted a temporary work-from-home policy in March 2020, during which our employees primarily worked remotely without disruption to our operations. In May 2020, we began to allow healthy employees to work in the office if they so choose.
6
Potential Competitive Advantages
We believe that we are one of only a select group of specialty lenders that has our depth of knowledge, experience, and track record in lending to growth stage companies. Further, we are one of an even smaller subset of specialty lenders that offers both loans and equipment financings. Our other potential competitive advantages include:
• In-house engineering and operations expertise to evaluate growth stage companies’ business products and plans.
We have a history of employing technology experts, including those with engineering and operations expertise, who have developed proven technology and hold patents in their names, as well as executives and other employees who have experience with the products and business plans of growth stage companies. The expertise, knowledge and experience of these individuals allows them to understand and evaluate the business plans, products and financing needs of growth stage companies, including the risks related thereto.
• Direct origination networks that benefit from relationships with venture banks, institutional equity investors and entrepreneurs built during the term of operations of the Legacy Funds, which began in 2008.
We seek to be the first contact for venture bankers who focus on growth stage companies and who have a portfolio company that would benefit from term debt or equipment financings. We have established relationships with the major technology banks over the last 10 years in every major market across the United States and have established standard intercreditor and subordination agreements, which we believe make working with technology banks seamless in most regions across the United States. These banks often will provide revolving credit facilities to growth stage companies and we seek to provide term debt and/or equipment financings to their portfolio companies.
We also focus on sourcing deals from the partners of growth stage institutional investors, including growth stage venture capital firms and private equity firms. We focus on building relationships with investors who have raised recent funds and have the ability to provide ongoing support to their portfolio companies.
We receive referrals directly to the executive officers of growth stage companies from these various stakeholders. Most of these stakeholders have board seats on the portfolio companies referred to us, are intimately involved in the business of such portfolio companies and generally serve as our advocates when term sheets are negotiated. We also receive introductions to companies for potential investment opportunities from executive officers with whom we have had business relationships at former portfolio companies.
• A dedicated staff of professionals covering credit origination and underwriting, as well as portfolio management functions.
We have a broad team of professionals focused on every aspect of the investment lifecycle. We have a credit origination and underwriting team that manages and oversees our investment process from identification of investment opportunity through negotiations of final term sheet and investment in a portfolio company. Our investment management and oversight activities are separate from our origination and underwriting activities. The team members serving our investment management and oversight functions have significant operating experience and are not associated with our origination function to avoid any biased views of performance. This structure helps our originators focus on identifying investment opportunities and building relationships with our portfolio companies.
• A proprietary credit rating system and regimented process for evaluating and underwriting prospective portfolio companies.
Historically, our management team has received significant prospective investment opportunities. In order to quickly review investment opportunities and evaluate risks, we have developed a detailed and consistent credit rating system. This system allows our analysts to receive a full set of financial statements and projections and quickly fill out a rating sheet for each potential investment, which includes using a series of weighted calculations to provide an initial “pass” or “fail” rating on the potential investment, as well as identifying specific risks for further consideration.
7
• Scalable software platforms developed during the term of operations of the Legacy Funds, which support our underwriting processes and loan monitoring functions.
We have an internally developed pipeline management tool which gives us a detailed look at our performance in real time. We believe our historical metrics generally predict our quarterly funding needs based upon the number of prospective investment opportunities we have at varying stages of our origination process. We believe this granular look at our underwriting process gives us the ability to increase or decrease marketing efforts in order to manage available capital and achieve our deployment goals.
Market Opportunity
We believe that an attractive market opportunity exists for providing debt and equipment financings to growth stage companies for the following reasons:
| • | Growth stage companies have generally been underserved by traditional lending sources; |
| • | Unfulfilled demand exists for loans and equipment financings to growth stage companies due to the complexity of evaluating risk in these investments; |
| • | Debt investments with warrants are less dilutive than traditional equity financing and complement equity financing from venture capital and private equity funds; |
| • | Equity funding of growth stage companies, including venture capital backed companies, has increased steadily over the last ten years, resulting in new lending and equipment financing opportunities. |
| • | We estimate that the annual U.S. venture debt and equipment financing market in 2020 exceeded $23 billion. We believe that the equipment financing market is even more fragmented, with the majority of equipment financing providers unable to fund investments for more than $10 million. We believe there are significant growth opportunities for us to expand our market share in the venture debt market and become a one-stop shop for loans and equipment financings for growth stage companies. |
Growth Stage Companies are Underserved by Traditional Lenders.
We believe many viable growth stage companies have been unable to obtain sufficient growth financing from traditional lenders, including financial services companies such as commercial banks and finance companies, because traditional lenders have continued to consolidate and have adopted a more risk-averse approach to lending. More importantly, we believe traditional lenders are typically unable to underwrite the risk associated with these companies effectively.
The cash flow characteristics of many growth stage companies include significant research and development expenditures and high projected revenue growth, thus often making such companies difficult to evaluate from a credit perspective. In addition, the balance sheets of many of these companies often include a disproportionately large amount of intellectual property assets, which can be difficult to value. Finally, the speed of innovation in technology and rapid shifts in consumer demand and market share add to the difficulty in evaluating these companies.
Due to the difficulties described above, we believe traditional lenders generally refrain from lending and/or providing equipment financing to growth stage companies, instead preferring the risk-reward profile of traditional fixed asset-based lending. We believe traditional lenders generally do not have flexible product offerings that meet the needs of growth stage companies. The financing products offered by traditional lenders typically impose restrictive covenants and conditions on borrowers, including limiting cash outflows and requiring a significant depository relationship to facilitate rapid liquidation.
8
Unfulfilled Demand for Loans and Equipment Financings to Growth Stage Companies.
Private capital in the form of debt and equipment financing from specialty finance companies continues to be an important source of funding for growth stage companies. We believe that the level of demand for debt and equipment financing is a function of the level of annual venture equity investment activity and can be as much as 20% to 30% of such investment activity. We believe this market is largely served by a handful of venture banks, with whom our products generally do not compete, and a relative few term lenders and lessors.
We believe that demand for debt and equipment financing to growth stage companies is currently underserved, given the high level of activity in venture capital equity market for the growth stage companies in which we invest. We believe certain venture lending companies have begun to focus on larger investment opportunities, potentially creating additional opportunities for us in the near term. Our senior management team has seen a significant increase in the number of potential investment opportunities over the last ten years.
Debt Investments with Warrants Complement Equity Financing from Venture Capital and Private Equity Funds.
We believe that growth stage companies and their financial sponsors will continue to view debt and equipment financing as an attractive source of capital because it augments the capital provided by venture capital and private equity funds. We believe that our debt investments, including loans and equipment financings, will provide access to growth capital that otherwise may only be available through incremental equity investments by new or existing equity investors. As such, we intend to provide portfolio companies and their financial sponsors with an opportunity to diversify their capital sources. Generally, we believe many growth stage companies target a portion of their capital to be debt and equipment financing in an attempt to minimize ownership dilution to existing investors and company founders. In addition, because growth stage companies generally reach a more mature stage prior to reaching a liquidity event, we believe our investments could provide the capital needed to grow or recapitalize during the extended growth period sometimes required prior to liquidity events.
Investment Philosophy, Strategy and Process
Overview
We lend money in the form of term loans and equipment financings and, to a lesser extent, working capital loans to growth stage companies. Investors may receive returns from three sources — the loan’s interest payments or equipment financing payments and the associated contractual fees; the final principal payment; and, contingent upon a successful change of control or initial public offering, proceeds from the equity positions or contingent exit fees obtained at loan or equipment financing origination.
We primarily seek to invest in loans and equipment financings to growth stage companies that have generally completed product development and are in need of capital to fund revenue growth. We believe a lack of profitability often limits these companies’ ability to access traditional bank financing and our in-house engineering and operations experience allows us to better understand this risk and earn what we believe to be higher overall returns and better risk-adjusted returns than those associated with traditional bank loans.
Subject to the requirements under the 1940 Act, which require that we invest at least 70% of our total assets in qualifying assets, we may also engage in other lending activities by investing in assets that are not qualifying assets under the requirements of the 1940 Act, including asset-backed lending, which may constitute up to 30% of our total assets.
We believe good candidates for loans and equipment financings appear in all business sectors. We are not limited to investing in any particular industry or geographic area and seek to invest in under-financed segments of the private credit markets. We believe in diversification and do not intend to specialize in any one sector. Our portfolio companies are selected from a wide range of industries, technologies and geographic regions. Since we focus on investing in portfolio companies alongside venture capital firms and technology banks, we anticipate that most of our opportunities will come from sectors that those sources finance.
9
Characteristics of Target Portfolio Companies
We seek to invest in a cross-section of growth stage companies. In addition to the criteria discussed in this annual report on Form 10-K, we may consider other factors such as portfolio company size, industry, historical revenue growth, management’s revenue growth projections, relevant operating margins, competition, management capabilities and geographic concentration. We will evaluate prospective portfolio companies quantitatively and qualitatively, and determine investments based on the key factors, including the following items:
| • | Recent, concurrent, or future funding by a venture capital firm; |
| • | Strong, experienced and flexible management team; |
| • | Successful, market-proven product and/or service with some proprietary characteristics; |
| • | Application of proven technologies that enable their customers to reduce costs, improve strategic positioning or fundamentally change the competitive nature of their industries; |
| • | Detailed business plan with multi-year projections that cover the full term of our investment; and |
| • | A defined exit strategy with identified potential acquirers. |
Investment Structure
We seek to structure portfolio investments to mitigate risk and provide attractive risk-adjusted returns for our investors while meeting portfolio companies financing needs. Typically, our loans, equipment financings and equity and equity-related investments take one of the following forms:
| • | Term Debt and Working Capital Loans. Term debt and working capital loans typically have initial interest-only periods of up to 24 months and may then fully amortize over a total term of up to 60 months. The annual stated interest rate on these loans typically has ranged from 8% to 14%. |
| • | Equipment Financings. Typically, an equipment financing is structured as fully amortizing over a period of up to 60 months. The specific terms of each equipment financing depend on the creditworthiness of the portfolio company and the projected value of the financed assets. Occasionally, we offer an initial period at a lower finance factor to companies with stronger creditworthiness, which is analogous to an interest-only period on a term loan. Annual interest rates on equipment financings typically have ranged from 7% to 14%. |
| • | Additional Deal Considerations. Additional deal considerations typically have included upfront fees of up to 2% of the invested principal, upfront structuring fees of approximately one-half month of finance payments for equipment financings, an upfront deposit of up to three months for equipment financings, and have final payments on average of 8% of invested principal. |
| • | Equity and Equity-Related Securities. We may also seek to obtain warrants entitling us to purchase preferred or common ownership shares of a portfolio company. We typically target the amount of such warrants to scale in proportion to the amount of the debt or equipment financing. We also attempt to structure such warrants so that the exercise price of the warrants will either be the price paid by venture capital investors in the most recent financing round or a current option price set by the portfolio company. Our typical exercise period for warrants is seven to 10 years. In addition, we may obtain rights to purchase additional shares of our portfolio companies in subsequent equity financing rounds. |
Concentration Limits; Security
We endeavor to maintain reasonable limits of concentration to specific industries, technologies and geographic regions. By their nature, these limits are subjective and are applied solely at the discretion of management.
10
In all our loans, we seek to take a security position in all of the assets of the portfolio company, including intellectual property, if available. From time to time, we may agree to take a security position in less than the total amount of assets. In the case of equipment financings, for instance, the security interest may extend only to the asset(s) financed.
In addition, we seek to enter into standard intercreditor agreements with the major technology banks that we anticipate engaging with, making work-out situations much easier and less contentious. Where and when possible, we will execute deposit account control agreements with our portfolio companies giving us ongoing access to their bank accounts for purposes of ensuring access to our collateral in a default. In all cases, we seek to put in place Uniform Commercial Code filings to perfect our position, and to update these filings frequently to reflect changes in our collateral.
Investment Process

Investment Originations; New Deals Referred
We have a multi-channel sourcing strategy focused primarily on growth stage venture capital firms, private equity firms, technology banks and, to a lesser extent, brokers who focus on our business. We have established relationships with the major technology banks and have established standard intercreditor and subordination agreements, which make working with technology banks seamless in most regions across United States.
We continue to expand our originations team internally in order to continue to focus on building relationships with individuals at top tier venture capital firms as well as building out connections to a nationwide network of technology bankers. We have developed proprietary internal systems and technology to give our originations and marketing team real time information about the broader market and our investment pipeline, which we leverage to attempt to become and maintain our relationship as the first call for our referral sources.
11
Initial Rating
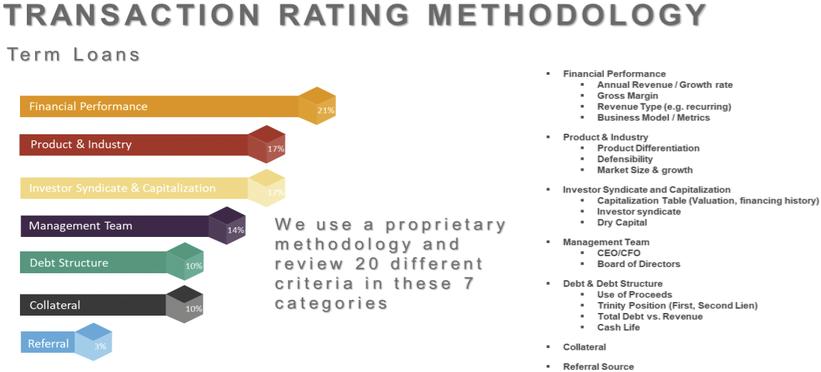
The following illustrates our transaction rating methodology for term loans.
The following illustrates our transaction rating methodology for equipment financings.
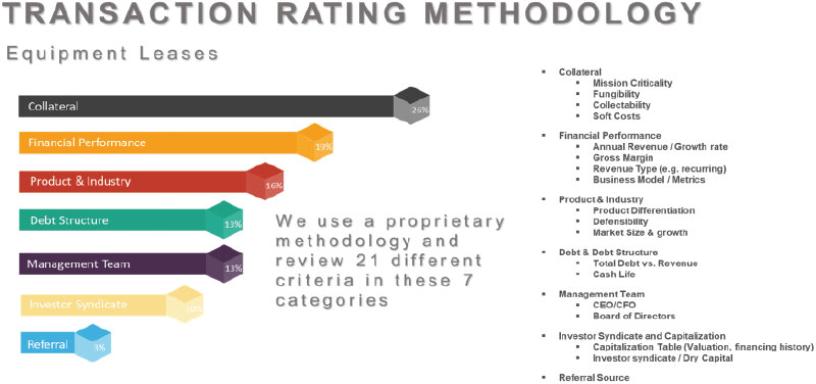
Our initial rating of every opportunity is based on six factors:
| (1) | the portfolio company’s investors, specifically their ability and likelihood to provide ongoing financial support as needed; |
| (2) | the experience and strength of the portfolio company’s management team and board of directors; |
| (3) | the portfolio company’s products or services and the market needs that they fulfill; |
| (4) | the portfolio company’s historical and projected financial performance, including a review of revenue potential, growth, gross margins and other metrics; |
| (5) | debt structure and cash life; and |
12
| (6) | other factors such as intellectual property, collateral, corporate governance, or other items that are deemed to be relevant by the due diligence team. |
Investment opportunities that score an acceptable initial rating are moved on for further consideration.
Preliminary Due Diligence and Executive Summary
The next phase of the due diligence process involves a structured call with the management team of the prospective portfolio company. Following the management call, if the opportunity still appears to be worthy of consideration, an executive summary memorandum is prepared by the due diligence team for consideration and voting by the Investment Committee. The executive summary memorandum is distributed to the Investment Committee, and the deal terms for the investment are defined. If approved by the Investment Committee, we issue a term sheet to the prospective portfolio company.
Confirmatory Due Diligence and On-Site Meeting
If the term sheet offered by us is accepted by the prospective portfolio company, the process of obtaining additional confirmatory due diligence begins. The confirmatory due diligence process typically includes calls with the venture capital partners responsible for the equity financing of the portfolio company, as well as key customers, suppliers, partners, or other stakeholders as may be deemed relevant by the due diligence team. Additional financial analysis is performed, in order to confirm the cash life assumptions that were made prior to term sheet issuance. In the case of an equipment financing, or term loan in which fixed assets make up a significant portion of our collateral, the due diligence team completes an analysis of the equipment or fixed assets being financed, which may include calls to the original manufacturer and/or any dealers, resellers, or refurbishing companies, to evaluate the value of the equipment at inception, as well as the useful life and anticipated value throughout the life of our holding period. Occasionally, we may engage the assistance of an appraiser to assist in valuations.
The final step in the confirmatory diligence process generally involves an on-site meeting, at which members of our due diligence team meet with the management team of the prospective portfolio company for a final review of the portfolio company’s financial performance and forward-looking plans. This meeting is typically held at the business offices of the portfolio company; however, occasionally the meeting will be held via video teleconference if travel to the portfolio company is not possible. One or more members of the Investment Committee will attend the on-site meeting if possible.
Underwriting Report and Investment Committee Vote
Assuming that the confirmatory due diligence process reveals no issues that would cause the due diligence team to recommend against the proposed investment, the due diligence team prepares an Investment Underwriting Report (“IUR”), which is distributed to the Investment Committee. The Investment Committee then meets to discuss and review the deal terms and IUR regarding the proposed investment and a vote takes place. A majority of the Investment Committee, which majority must include Steven L. Brown, is required to approve the transaction.
Investment Management and Oversight
Our investment management and oversight activities are separate from our origination and underwriting activities. The team members serving our investment management and oversight functions have significant operating experience and are not associated with our origination function to avoid any biased views of performance. Beyond the dedicated portfolio management team, all of our management team members and investment professionals are typically involved at various times with our portfolio companies and investments. Our portfolio management team reviews our portfolio companies’ monthly or quarterly financial statements and compares actual results to the portfolio companies’ projections. Additionally, the portfolio management team may initiate periodic calls with the portfolio company’s venture capital partners and its management team and may obtain observer rights on the portfolio company’s board of directors. Our management team and investment professionals anticipate potential problems by monitoring reporting requirements and having frequent calls with the management teams of our portfolio companies.
13
Investment Risk Rating System
Our portfolio management team uses an ongoing investment risk rating system to characterize and monitor our outstanding loans and equipment financings. Our portfolio management team monitors and, when appropriate, recommends changes to the investment risk ratings. Our Investment Committee reviews the recommendations and/or changes to the investment risk ratings, which are submitted on a quarterly basis to the Audit Committee (the “Audit Committee”) of our Board of Directors (the “Board”) and the Board.
From time to time, we will identify investments that require closer monitoring or become work-out assets. We will develop a workout strategy for workout assets and our Investment Committee will monitor the progress against the strategy. We may incur losses from our investing activities; however, we work with our troubled portfolio companies in order to recover as much of our investments as is practicable, including possibly taking control of the portfolio company. The risk rating system allows for early detection of issues and escalation to avoid credit losses.
For our investment risk rating system, we review seven different criteria and, based on our review of such criteria, we assign a risk rating on a scale of 1 to 5, as set forth in the following illustration.

As of December 31, 2020, the Company’s debt investment portfolio had a weighted average risk rating score of 3.2.
Managerial Assistance
As a BDC, we are required to offer, and provide upon request, managerial assistance to our portfolio companies. This assistance could involve, among other things, monitoring the operations of our portfolio companies, participating in board and management meetings, consulting with and advising officers of portfolio companies and providing other organizational and financial guidance. We may, from time to time, receive fees for these services. In the event that such fees are received, we expect that they will be incorporated into our operating income and passed through to our stockholders, given the nature of our structure as an internally managed BDC. See “— Regulation as a Business Development Company — Significant Managerial Assistance” for additional information.
Competition
Our prospective markets are highly competitive and are characterized by competitive factors that vary based upon product and geographic region. Competitors vary and may include captive and independent finance companies, other BDCs, equity and debt focused public and private funds, commercial banks and thrift institutions, industrial banks, community banks, leasing companies, hedge funds, insurance companies, mortgage companies, manufacturers and vendors, and other financing providers. There has been substantial competition for attractive investment opportunities in the venture capital business, in particular.
14
These lenders will typically offer lower finance rates than non-bank finance companies (including us), but will require cash depository relationships, blanket liens and will often have certain performance and cash covenants, all of which make their lending program less flexible and, we believe, less attractive to borrowers. We compete, in part, on the basis of pricing, terms and structure. For additional information concerning the competitive risks we face, refer to “Item 1A. Risk Factors – Risks Relating to Our Business and Structure – We operate in a highly competitive market for investment opportunities, which could reduce returns and result in losses.”
Emerging Growth Company
The Company is an emerging growth company as defined in the Jumpstart Our Business Startups Act of 2012 (the “JOBS Act”) and is eligible to take advantage of certain specified reduced disclosure and other requirements that are otherwise generally applicable to public companies that are not “emerging growth companies” including not being required to comply with the auditor attestation requirements of Section 404 of the Sarbanes-Oxley Act of 2002 (the “Sarbanes-Oxley Act”). Although we have not made a determination whether to take advantage of any or all of these exemptions, we expect to remain an emerging growth company for up to five years following the completion of our IPO or until the earliest of:
| • | the last day of the first fiscal year in which our annual gross revenues exceed $1.07 billion; |
| • | December 31 of the fiscal year that we become a “large accelerated filer” as defined in Rule 12b-2 under the Exchange Act which would occur if the market value of the shares of our common stock that is held by non-affiliates exceeds $700.0 million as of the last business day of our most recently completed second fiscal quarter and we have been publicly reporting for at least 12 months; or |
| • | the date on which we have issued more than $1.0 billion in non-convertible debt securities during the preceding three-year period. |
In addition, we will take advantage of the extended transition period provided in Section 7(a)(2)(B) of the Securities Act for complying with new or revised accounting standards.
Regulation as a Business Development Company
We have elected to be regulated as a BDC under the 1940 Act. The 1940 Act contains prohibitions and restrictions relating to transactions between BDCs and their affiliates, principal underwriters and affiliates of those affiliates or underwriters. The 1940 Act requires a majority of the members of the board of directors of a BDC be persons other than “interested persons,” as that term is defined in the 1940 Act. In addition, the 1940 Act provides that we may not change the nature of our business so as to cease to be, or to withdraw our election as, a BDC unless approved by a majority of our outstanding voting securities.
The 1940 Act defines “a majority of the outstanding voting securities” as the lesser of (i) 67% or more of the voting securities present at a meeting if the holders of more than 50% of our outstanding voting securities are present or represented by proxy or (ii) more than 50% of our outstanding voting securities.
Qualifying Assets. Under the 1940 Act, a BDC may not acquire any asset other than assets of the type listed in Section 55(a) of the 1940 Act, which are referred to as qualifying assets, unless, at the time the acquisition is made, qualifying assets represent at least 70% of the BDC’s total assets. The principal categories of qualifying assets relevant to our business are any of the following:
| (1) | Securities purchased in transactions not involving any public offering from the issuer of such securities, which issuer (subject to certain limited exceptions) is an eligible portfolio company, or from any person who is, or has been during the preceding 13 months, an affiliated person of an eligible portfolio company, or from any other |
15
| person, subject to such rules as may be prescribed by the SEC. An eligible portfolio company is defined in the 1940 Act as any issuer which: |
| a. | is organized under the laws of, and has its principal place of business in, the United States; |
| b. | is not an investment company (other than a small business investment company wholly owned by the BDC) or a company that would be an investment company but for certain exclusions under the 1940 Act; and |
| c. | satisfies any of the following: |
| i. | does not have any class of securities that is traded on a national securities exchange; |
| ii. | has a class of securities listed on a national securities exchange, but has an aggregate market value of outstanding voting and non-voting common equity of less than $250 million; |
| iii. | is controlled by a BDC or a group of companies including a BDC and the BDC has an affiliated person who is a director of the eligible portfolio company; or |
| iv. | is a small and solvent company having total assets of not more than $4 million and capital and surplus of not less than $2 million; |
| (2) | Securities of any eligible portfolio company controlled by us; |
| (3) | Securities purchased in a private transaction from a U.S. issuer that is not an investment company or from an affiliated person of the issuer, or in transactions incident thereto, if the issuer is in bankruptcy and subject to reorganization or if the issuer, immediately prior to the purchase of its securities was unable to meet its obligations as they came due without material assistance other than conventional lending or financing arrangements; |
| (4) | Securities of an eligible portfolio company purchased from any person in a private transaction if there is no ready market for such securities and we already own 60% of the outstanding equity of the eligible portfolio company; |
| (5) | Securities received in exchange for or distributed on or with respect to securities described in (1) through (4) above, or pursuant to the exercise of warrants or rights relating to such securities; or |
| (6) | Cash, cash equivalents, U.S. government securities or high-quality debt securities maturing in one year or less from the time of investment. |
In addition, a BDC must be operated for the purpose of making investments in the types of securities described in (1), (2) or (3) above.
Significant Managerial Assistance. A BDC must have been organized and have its principal place of business in the United States and must be operated for the purpose of making investments in the types of securities described above. However, in order to count portfolio securities as qualifying assets for the purpose of the 70% test, the BDC must either control the issuer of the securities or must offer to make available to the issuer of the securities (other than small and solvent companies described above) significant managerial assistance. However, where the BDC purchases such securities in conjunction with one or more other persons acting together, one of the other persons in the group may make available such managerial assistance. Making available significant managerial assistance means, among other things, any arrangement whereby the BDC, through its directors, officers or employees, offers to provide and, if accepted, does so provide, significant guidance and counsel concerning the management, operations or business objectives and policies of a portfolio company through monitoring of portfolio company operations, selective participation in board and
16
management meetings, consulting with and advising a portfolio company’s officers or other organizational or financial guidance.
Temporary Investments. Pending investment in other types of qualifying assets, as described above, our investments can consist of cash, cash equivalents, U.S. government securities or high quality debt securities maturing in one year or less from the time of investment, which are referred to herein, collectively, as temporary investments, so that 70% of our assets would be qualifying assets.
Issuance of Derivative Securities. Under the 1940 Act, a BDC is subject to restrictions on the issuance, terms and amount of warrants, options, restricted stock or rights to purchase shares of capital stock that it may have outstanding at any time. In particular, the amount of capital stock that would result from the conversion or exercise of all outstanding warrants, options or rights to purchase capital stock cannot exceed 25% of the BDC’s total outstanding shares of capital stock. This amount is reduced to 20% of the BDC’s total outstanding shares of capital stock if the amount of warrants, options or rights issued pursuant to an executive compensation plan would exceed 15% of the BDC’s total outstanding shares of capital stock. We intend to apply for exemptive relief from the SEC to permit us to issue restricted stock and restricted stock units to our employees, officers and directors subject to the above conditions, among others; although there can be no assurance or guarantee that such exemptive relief will be received from the SEC.
Senior Securities; Coverage Ratio. We are generally permitted, under specified conditions, to issue multiple classes of indebtedness and one class of stock senior to our Common Stock if our asset coverage, as defined in the 1940 Act, is at least equal to 150% immediately after each such issuance. In connection with the organization of the Company, the Board and our initial sole stockholder authorized us to adopt the 150% asset coverage ratio. This means we are permitted to borrow $2 for investment purposes for every $1 of investor equity. For a discussion of the risks associated with leverage refer to Item 1A. Risk Factors — Risks Relating to Our Business and Structure — Regulations governing our operation as a BDC affect our ability to, and the way in which we, raise additional capital.”
Code of Ethics. We have adopted a code of ethics pursuant to Rule 17j-1 under the 1940 Act that establishes procedures for personal investments and restricts certain personal securities transactions. Personnel subject to the code are permitted to invest in securities for their personal investment accounts, including securities that may be purchased or held by us, so long as such investments are made in accordance with the code’s requirements.
Affiliated Transactions. We are prohibited under the 1940 Act from conducting certain transactions with our affiliates without the prior approval of our directors who are not interested persons and, in some cases, the prior approval of the SEC.
Other. We will be periodically examined by the SEC for compliance with the 1940 Act and be subject to the periodic reporting and related requirements of the Exchange Act.
We are also required to provide and maintain a bond issued by a reputable fidelity insurance company to protect against larceny and embezzlement. Furthermore, as a BDC, we are prohibited from protecting any director or officer against any liability to stockholders arising from willful misfeasance, bad faith, gross negligence or reckless disregard of the duties involved in the conduct of such person’s office.
We are also required to designate a chief compliance officer and to adopt and implement written policies and procedures reasonably designed to prevent violation of the federal securities laws and to review these policies and procedures annually for their adequacy and the effectiveness of their implementation.
Taxation as a Regulated Investment Company
In connection with the filing of our 2020 annual tax return, we will elect to be treated and to qualify each year thereafter as a RIC for U.S. federal income tax purposes. As a RIC, we generally will not have to pay corporate-level U.S. federal income taxes on any ordinary income or capital gains that we distribute to stockholders as distributions. To qualify as a RIC, we must, among other things, meet certain source-of-income and asset diversification requirements (as described below). In addition, in order to obtain RIC tax benefits, we must distribute to stockholders, for each taxable
17
year, at least 90% of our “investment company taxable income,” which is generally its ordinary income plus the excess of realized net short-term capital gains over realized net long-term capital losses (the “Annual Distribution Requirement”).
If we:
| • | qualify as a RIC; and |
| • | satisfy the Annual Distribution Requirement, |
then we will not be subject to U.S. federal income tax on the portion of income we distribute (or are deemed to distribute) to stockholders. We will be subject to U.S. federal income tax at the regular corporate rates on any income or capital gains not distributed (or deemed distributed) to stockholders.
We are subject to a 4% nondeductible U.S. federal excise tax on certain undistributed income unless we distribute in a timely manner an amount at least equal to the sum of (i) 98% of net ordinary income for each calendar year, (ii) 98.2% of the amount by which capital gains exceeds capital losses (adjusted for certain ordinary losses) for the one-year period ending October 31 in that calendar year and (iii) certain undistributed amounts from previous years on which we paid no U.S. federal income tax (the “Excise Tax Avoidance Requirement”). While we intend to distribute any income and capital gains in order to avoid imposition of this 4% U.S. federal excise tax, we may not be successful in avoiding entirely the imposition of this tax. In that case, we will be liable for the tax only on the amount by which we do not meet the foregoing distribution requirement.
In order to qualify as a RIC for U.S. federal income tax purposes, we must, among other things:
| • | continue to qualify as a BDC under the 1940 Act at all times during each taxable year; |
| • | derive in each taxable year at least 90% of gross income from dividends, interest, payments with respect to loans of certain securities, gains from the sale of stock or other securities or foreign currencies, net income from certain “qualified publicly traded partnerships,” or other income derived with respect to the business of investing in such stock or securities (the “90% Income Test”); and |
| • | diversify our holdings so that at the end of each quarter of the taxable year: |
| o | at least 50% of the value of our assets consists of cash, cash equivalents, U.S. Government securities, securities of other RICs, and other securities if such other securities of any one issuer do not represent more than 5% of the value of our assets or more than 10% of the outstanding voting securities of the issuer; and |
| o | no more than 25% of the value of our assets is invested in the (i) securities, other than U.S. government securities or securities of other RICs, of one issuer, (ii) securities of two or more issuers that are controlled, as determined under applicable Code rules, by us and that are engaged in the same or similar or related trades or businesses or (iii) securities of one or more “qualified publicly traded partnerships” (the “Diversification Tests”). |
We may be required to recognize taxable income in circumstances in which we do not receive cash. For example, if we hold debt obligations that are treated under applicable tax rules as having original issue discount (such as debt instruments with payment-in-kind, or PIK, interest or, in certain cases, increasing interest rates or issued with warrants), we must include in income each year a portion of the original issue discount that accrues over the life of the obligation, regardless of whether cash representing such income is received by us in the same taxable year. We may also have to include in income other amounts that we have not yet received in cash, such as PIK interest and deferred loan origination fees that are paid after origination of the loan. Because any original issue discount or other amounts accrued will be included in our investment company taxable income for the year of accrual, we may be required to make a distribution to
18
stockholders in order to satisfy the Annual Distribution Requirement, even though we will not have received the corresponding cash amount.
Although we do not presently expect to do so, we are authorized to borrow funds, to sell assets and to make taxable distributions of our stock and debt securities in order to satisfy distribution requirements. Our ability to dispose of assets to meet distribution requirements may be limited by (i) the illiquid nature of our portfolio and/or (ii) other requirements relating to our status as a RIC, including the Diversification Tests. If we dispose of assets in order to meet the Annual Distribution Requirement or the Excise Tax Avoidance Requirement, we may make such dispositions at times that, from an investment standpoint, are not advantageous. If we are unable to obtain cash from other sources to satisfy the Annual Distribution Requirement, we may fail to qualify for tax treatment as a RIC and become subject to tax as an ordinary corporation.
Under the 1940 Act, we are not permitted to make distributions to our stockholders while debt obligations and other senior securities are outstanding unless certain “asset coverage” tests are met. If we are prohibited from making distributions, we may fail to qualify for tax treatment as a RIC and become subject to tax as an ordinary corporation.
Certain of our investment practices may be subject to special and complex U.S. federal income tax provisions that may, among other things: (i) disallow, suspend or otherwise limit the allowance of certain losses or deductions; (ii) convert lower taxed long-term capital gain into higher taxed short-term capital gain or ordinary income; (iii) convert an ordinary loss or a deduction into a capital loss (the deductibility of which is more limited); (iv) cause us to recognize income or gain without a corresponding receipt of cash; (v) adversely affect the time as to when a purchase or sale of securities is deemed to occur; (vi) adversely alter the characterization of certain complex financial transactions; and (vii) produce income that will not be qualifying income for purposes of the 90% Income Test described above. We will monitor our transactions and may make certain tax decisions in order to mitigate the potential adverse effect of these provisions.
A RIC is limited in its ability to deduct expenses in excess of its “investment company taxable income” (which is, generally, ordinary income plus the excess of net short-term capital gains over net long-term capital losses). If our expenses in a given year exceed investment company taxable income, we would experience a net operating loss for that year. However, a RIC is not permitted to carry forward net operating losses to subsequent years. In addition, expenses can be used only to offset investment company taxable income, not net capital gain. Due to these limits on the deductibility of expenses, we may, for tax purposes, have aggregate taxable income for several years that we are required to distribute and that is taxable to stockholders even if such income is greater than the aggregate net income we actually earned during those years. Such required distributions may be made from cash assets or by liquidation of investments, if necessary. We may realize gains or losses from such liquidations. In the event we realize net capital gains from such transactions, a stockholder may receive a larger capital gain distribution than it would have received in the absence of such transactions.
Failure to Qualify as a RIC
If we have previously qualified as RIC, but are subsequently unable to qualify for treatment as a RIC, and certain cure provisions are not met, we would be subject to tax on all of our taxable income (including net capital gains) at regular corporate rates. We would not be able to deduct distributions to stockholders, nor would distributions be required to be made. Distributions, including distributions of net long-term capital gain, would generally be taxable to stockholders as ordinary dividend income to the extent of our current and accumulated earnings and profits. Subject to certain limitations under the Code, corporate stockholders would be eligible to claim a dividend received deduction with respect to such dividend and non-corporate stockholders would generally be able to treat such distributions as “qualified dividend income,” which is subject to reduced rates of U.S. federal income tax. Distributions in excess of current and accumulated earnings and profits would be treated first as a return of capital to the extent of the stockholder’s tax basis, and any remaining distributions would be treated as a capital gain. In order to requalify as a RIC, in addition to the other requirements discussed above, we would be required to distribute all previously undistributed earnings attributable to the period we failed to qualify as a RIC by the end of the first year that we intend to requalify as a RIC. If we fail to requalify as a RIC for a period greater than two taxable years, we may be subject to regular corporate tax on any net built-in gains with respect to certain assets (i.e., the excess of the aggregate gains, including items of income, over
19
aggregate losses that would have been realized with respect to such assets if we had been liquidated) that we elect to recognize on requalification or when recognized over the next five years.
Corporate Information
Our principal executive offices are located at 3075 W. Ray Rd, Suite 525, Chandler, Arizona 85226. We maintain a website on the Internet at www.trincapinvestment.com. We make available, free of charge, on our website our proxy statement, annual report on Form 10-K, quarterly reports on Form 10-Q, current reports on Form 8-K and amendments to those reports as soon as reasonably practicable after we electronically file such material with, or furnish it to, the Securities and Exchange Commission, or SEC. Information contained on our website is not incorporated by reference into this annual report on Form 10-K, and you should not consider that information to be part of this annual report on Form 10-K.
We file annual, quarterly and current periodic reports, proxy statements and other information with the SEC, under the Securities Exchange Act of 1934, as amended, or the Exchange Act. In addition, the SEC maintains an Internet website, at www.sec.gov, that contains reports, proxy and information statements, and other information regarding issuers, including us, who file documents electronically with the SEC.
You should carefully consider the risks and uncertainties described below, together with all of the other information in this annual report on Form 10-K, including “Management’s Discussion and Analysis of Financial Condition and Results of Operations” and our consolidated financial statements and related notes. Our business, operating results, financial condition, or prospects could be materially and adversely affected by any of these risks and uncertainties. If any of these risks occurs, the trading price of our common stock could decline, and you might lose all or part of your investment. Our business, operating results, financial performance, or prospects could also be harmed by risks and uncertainties not currently known to us or that we currently do not believe are material.
Summary of Principal Risk Factors
The following is a summary of the principal risks that you should carefully consider before investing in our securities and is followed by a more detailed discussion of the material risks related to us and an investment in our securities.
We are subject to risks related to our business and structure, including, but not limited to the following:
| ● | We have a limited operating history as a BDC. |
| ● | We depend upon our senior management team and investment professionals, including the members of our Investment Committee, for our success. |
| ● | Our business model depends to a significant extent upon strong referral relationships with venture capital sponsors, and our inability to develop or maintain these relationships, or the failure of these relationships to generate investment opportunities, could adversely affect our business. |
| ● | Global economic, political and market conditions, including uncertainty about the financial stability of the United States, could have a significant adverse effect on our business, financial condition and results of operations. |
| ● | Regulations governing our operations as a BDC affect our ability to and the way in which we raise additional capital. |
| ● | Changes in laws or regulations governing our operations may adversely affect our business or cause us to alter our business strategy. |
| ● | Provisions in our credit facilities may limit our operations. |
| ● | We are exposed to risks associated with changes in interest rates, including the decommissioning of LIBOR. |
| ● | Most or a substantial portion of our portfolio investments will be recorded at fair value as determined in good faith by the Board and, as a result, there may be uncertainty as to the value of our portfolio investments. |
20
| ● | The Board may change our investment objective, operating policies and strategies without prior notice or stockholder approval, the effects of which may be adverse. |
| ● | Any failure in cyber security systems, as well as the occurrence of events unanticipated in our disaster recovery systems and management continuity planning, could impair our ability to conduct business effectively. |
We are subject to risks related to our investments, including, but not limited to the following:
| ● | Our investments are very risky and highly speculative and a lack of liquidity in our investments may adversely affect us. |
| ● | Our investment strategy focuses on growth stage companies which are subject to many risks, including dependence on the need to raise additional capital, volatility, intense competition, shortened product life cycles, changes in regulatory and governmental programs, periodic downturns, below investment grade ratings, which could cause you to lose all or part of your investment in us. |
| ● | The equipment financing industry is highly competitive and competitive forces could adversely affect the financing rates and resale prices that we may realize on our equipment financing investment portfolio and the prices that we have to pay to acquire our investments. |
| ● | The COVID-19 pandemic has caused severe disruptions in the global economy and has disrupted financial activity in the areas in which we or our portfolio companies operate. |
| ● | Economic recessions or downturns could impair our portfolio companies and harm our operating results. |
| ● | Our investments are geographically concentrated, which may result in a single occurrence in a particular geographic area having a disproportionate negative impact on our investment portfolio. |
| ● | We may be subject to risks associated with our investments in senior loans, junior debt securities and covenant-lite loans. |
Risks related to an investment in our securities include, but are not limited to, the following:
| ● | We may not be able to pay distributions, our distributions may not grow over time and/or a portion of our distributions may be a return of capital. |
| ● | Investing in our common stock may involve an above-average degree of risk, including the risk of dilution. |
| ● | The market value of our securities may fluctuate significantly, which may make it difficult to resell our securities, including at an attractive price. |
| ● | We may borrow money, which may magnify the potential for gain or loss and may increase the risk of investing in us. |
| ● | Our 2025 Notes and our 6.00% Convertible Notes due 2025 (the “Convertible Notes”) are each unsecured and therefore effectively subordinated to any secured indebtedness we currently have outstanding or may incur in the future and rank pari passu with, or equal to, all outstanding and future unsecured unsubordinated indebtedness issued by us and our general liabilities. |
We are subject to risks related to U.S. federal income tax including, but not limited to, the following:
| ● | We will be subject to corporate-level U.S. federal income tax if we are unable to qualify or maintain qualification as a RIC under Subchapter M of the Code. |
| ● | We may have difficulty paying our required distributions if we recognize income before, or without, receiving cash representing such income. |
Risks Related to Our Business and Structure
We have limited operating history as a BDC.
We were formed on August 12, 2019 to acquire the assets of the Legacy Funds and have limited operating history as a combined entity or as a BDC. As a result, we are subject to the business risks and uncertainties associated with recently formed businesses, including the risk that we will not achieve our investment objective and the value of a stockholder’s investment could decline substantially or become worthless. In addition, we may be unable to generate sufficient revenue from our operations to make or sustain distributions to our stockholders.
21
The 1940 Act and the Code impose numerous constraints on the operations of BDCs and RICs that do not apply to the other types of investment vehicles and did not apply to the Legacy Funds. For example, under the 1940 Act, BDCs are required to invest at least 70% of their total assets primarily in securities of qualifying U.S. private or thinly traded companies. Moreover, qualification for RIC tax treatment under Subchapter M of the Code requires, among other things, satisfaction of source-of-income, diversification and other requirements. The failure to comply with these provisions in a timely manner could prevent us from qualifying as a BDC or RIC or could force us to pay unexpected taxes and penalties, which could be material. Our management team’s lack of experience in managing a portfolio of assets under such constraints may hinder our ability to take advantage of attractive investment opportunities and, as a result, achieve our investment objective.
We depend upon our senior management team and investment professionals, including the members of the Investment Committee, for our success.
Our ability to achieve our investment objective and to make distributions to our stockholders depends upon the performance of our senior management. We depend on the investment expertise, skill and network of business contacts of our senior management team and investment professionals, including the members of the Investment Committee, who evaluate, negotiate, structure, execute, monitor and service our investments. Our success depends to a significant extent on the continued service and coordination of these individuals. The departure of any of these individuals or competing demands on their time in the future could have a material adverse effect on our ability to achieve our investment objective. Further, if these individuals do not maintain their existing relationships with financial institutions, sponsors and investment professionals and do not develop new relationships with other sources of investment opportunities, we may not be able to grow our investment portfolio or achieve our investment objective. This could have a material adverse effect on our financial condition and results of operations.
Our business model depends to a significant extent upon strong referral relationships with venture capital sponsors, and our inability to develop or maintain these relationships, or the failure of these relationships to generate investment opportunities, could adversely affect our business.
We expect that members of our management team will maintain their relationships with venture capital sponsors, and we will rely to a significant extent upon these relationships to provide us with our deal flow. If we fail to maintain our existing relationships, our relationships become strained as a result of enforcing our rights with respect to non-performing investments in protecting our investments or we fail to develop new relationships with other firms or sources of investment opportunities, then we will not be able to grow our investment portfolio. In addition, persons with whom members of our management team have relationships are not obligated to provide us with investment opportunities and, therefore, there is no assurance that such relationships will lead to the origination of debt or other investments.
Our financial condition and results of operations depend on our ability to manage our business effectively.
Our ability to achieve our investment objective and grow depends on our ability to manage our business. This depends, in turn, on our ability to identify, invest in and monitor companies that meet our investment criteria. The achievement of our investment objective depends upon the execution of our investment process and our access to financing on acceptable terms. Our senior origination professionals and other investment personnel may be called upon to provide managerial assistance to our portfolio companies. These activities may distract them or slow our rate of investment. Any failure to manage our business and our future growth effectively could have a material adverse effect on our business, financial condition, results of operations and prospects. Our results of operations depend on many factors, including the availability of opportunities for investment, readily accessible short and long-term funding alternatives in the financial markets and economic conditions. Furthermore, if we cannot successfully operate our business or implement our investment policies and strategies, it could negatively impact our ability to pay distributions or other distributions and you may lose all or part of your investment.
We are subject to certain regulatory restrictions that may adversely affect our business.
As an internally managed BDC, the size and categories of our assets under management are limited, and we will be unable to offer as wide a variety of financial products to prospective portfolio companies and sponsors (potentially
22
limiting the size and diversification of our asset base). We therefore may not achieve efficiencies of scale and greater management resources available to externally managed BDCs.
Additionally, as an internally managed BDC, our ability to offer more competitive and flexible compensation structures, such as offering both a profit-sharing plan and a long-term incentive plan, is subject to the limitations imposed by the 1940 Act, which may limit our ability to attract and retain talented investment management professionals. As such, these limitations could inhibit our ability to grow, pursue our business plan and attract and retain professional talent, any or all of which may have a negative impact on our business, financial condition and results of operations.
You will not have the opportunity to evaluate the economic merits, transaction terms or other financial or operational data concerning our investments prior to making an investment in us.
You will not have the opportunity to evaluate the economic merits, transaction terms or other financial or operational data concerning our investments prior to making an investment in us. You must rely on our investment professionals and the Board to implement our investment policies, to evaluate our investment opportunities and to structure the terms of our investments. Because investors are not able to evaluate our investments in advance of making an investment in us, an investment in us may entail more risk than other types of offerings. This additional risk may hinder your ability to achieve your own personal investment objective related to portfolio diversification, risk-adjusted investment returns and other objectives.
Our management team and/or members of the Investment Committee may, from time to time, possess material nonpublic information, limiting our investment discretion.
Our management team and/or the members of the Investment Committee may serve as directors of, or in a similar capacity with, companies in which we invest, the securities of which are purchased or sold on our behalf. In the event that material nonpublic information is obtained with respect to such companies, or we become subject to trading restrictions under the internal trading policies of those companies or as a result of applicable law or regulations, we could be prohibited for a period of time from purchasing or selling the securities of such companies, and this prohibition may have a material adverse effect on us.
We operate in a highly competitive market for investment opportunities, which could reduce returns and result in losses.
Our competitors include both existing and newly formed equity and debt focused public and private funds, other BDCs, investment banks, venture-oriented commercial banks, commercial financing companies and, to the extent they provide an alternative form of financing, private equity and hedge funds. Many of our competitors are substantially larger and have considerably greater financial, technical and marketing resources than us. For example, some competitors may have a lower cost of capital and access to funding sources (including deposits) that are not available to us. In addition, some of our competitors may have higher risk tolerances or different risk assessments than we have. Furthermore, many of our competitors are not subject to the regulatory restrictions that the 1940 Act imposes on us as a BDC or to the distribution and other requirements we must satisfy to maintain our ability to be subject to tax as a RIC. These characteristics could allow our competitors to consider a wider variety of investments, establish more relationships and offer better pricing and more flexible structuring than we are able to offer.
The competitive pressures we face may have a material adverse effect on our financial condition, results of operations and cash flows. We believe that some competitors may make loans with rates that are comparable or lower than our rates. We may lose some investment opportunities if we do not match our competitors’ pricing, terms and structure. However, if we match our competitors’ pricing, terms and structure, we may experience decreased net interest income, lower yields and increased risk of credit loss. As a result of this competition, we may not be able to take advantage of attractive investment opportunities from time to time, and we may not be able to identify and make investments that are consistent with our investment objective.
23
In addition, we believe a significant part of our competitive advantage stems from the fact that the market for investments in small, fast-growing, private companies is underserved by traditional commercial banks and other financing sources. A significant increase in the number and/or the size of our competitors in this target market could force us to accept less attractive investment terms.
The capital markets are currently in a period of disruption and economic uncertainty. Such market conditions have materially and adversely affected debt and equity capital markets, which have had, and may continue to have, a negative impact on our business and operations.
The U.S. capital markets have experienced extreme volatility and disruption following the global outbreak of COVID-19 that began in December 2019, as evidenced by the volatility in global stock markets as a result of, among other things, uncertainty surrounding the COVID-19 pandemic and the fluctuating price of commodities such as oil. Despite actions of the U.S. federal government and foreign governments, these events have contributed to unpredictable general economic conditions that are materially and adversely impacting the broader financial and credit markets and reducing the availability of debt and equity capital for the market as a whole. These conditions could continue for a prolonged period of time or worsen in the future.
Given the ongoing and dynamic nature of the circumstances, it is difficult to predict the full impact of the COVID-19 pandemic on our business. The extent of such impact will depend on future developments, which are highly uncertain, including when the coronavirus can be controlled and abated and whether there will be additional economic shutdowns. As the result of the COVID-19 pandemic and the related adverse local and national economic consequences, we could be subject to any of the following risks, any of which could have a material, adverse effect on our business, financial condition, liquidity, and results of operations:
• Current market conditions may make it difficult to raise equity capital because, subject to some limited exceptions, as a BDC, we are generally not able to issue additional shares of our common stock at a price less than the NAV per share without first obtaining approval for such issuance from our stockholders and our independent directors. In addition, these market conditions may make it difficult to access or obtain new indebtedness with similar terms to our existing indebtedness.
• Significant changes or volatility in the capital markets may also have a negative effect on the valuations of our investments. While most of our investments are not publicly traded, applicable accounting standards require us to assume as part of our valuation process that our investments are sold in a principal market to market participants (even if we plan on holding an investment through its maturity).
• Significant changes in the capital markets, such as the recent disruption in economic activity caused by the COVID-19 pandemic, have adversely affected, and may continue to adversely affect, the pace of our investment activity and economic activity generally. Additionally, the recent disruption in economic activity caused by the COVID-19 pandemic has had, and may continue to have, a negative effect on the potential for liquidity events involving our investments. The illiquidity of our investments may make it difficult for us to sell such investments to access capital if required, and as a result, we could realize significantly less than the value at which we have recorded our investments if we were required to sell them for liquidity purposes. An inability to raise or access capital, and any required sale of all or a portion of our investments as a result, could have a material adverse effect on our business, financial condition or results of operations.
The current period of capital markets disruption and economic uncertainty may make it difficult to extend the maturity of, or refinance, our existing indebtedness or obtain new indebtedness and any failure to do so could have a material adverse effect on our business, financial condition or results of operations.
Current market conditions may make it difficult to extend the maturity of or refinance our existing indebtedness or obtain new indebtedness with similar terms and any failure to do so could have a material adverse effect on our business. The debt capital that will be available to us in the future, if at all, may be at a higher cost and on less favorable terms and conditions than what we currently experience, including being at a higher cost in rising rate environments. If we are unable to raise or refinance debt, then our equity investors may not benefit from the potential for increased returns on equity resulting from leverage and we may be limited in our ability to make new
24
commitments or to fund existing commitments to our portfolio companies. An inability to extend the maturity of, or refinance, our existing indebtedness or obtain new indebtedness could have a material adverse effect on our business, financial condition or results of operations.
Capital markets may experience periods of disruption and instability. Such market conditions may materially and adversely affect debt and equity capital markets in the United States and abroad, which may have a negative impact on our business and operations.
From time-to-time, capital markets may experience periods of disruption and instability. During such periods of market disruption and instability, we and other companies in the financial services sector may have limited access, if available, to alternative markets for debt and equity capital. Equity capital may be difficult to raise because, subject to some limited exceptions which will apply to us as a BDC, we will generally not be able to issue additional shares of our common stock at a price less than net asset value without first obtaining approval for such issuance from our stockholders and our independent directors. In addition, our ability to incur indebtedness (including by issuing preferred stock) is limited by applicable regulations such that our asset coverage, as defined in the 1940 Act, must equal at least 150% immediately after each time we incur indebtedness. The debt capital that will be available, if at all, may be at a higher cost and on less favorable terms and conditions in the future. Any inability to raise capital could have a negative effect on our business, financial condition and results of operations.
Given the extreme volatility and dislocation in the capital markets over the past several years, many BDCs have faced, and may in the future face, a challenging environment in which to raise or access capital. In addition, significant changes in the capital markets, including the extreme volatility and disruption over the past several years, has had, and may in the future have, a negative effect on the valuations of our investments and on the potential for liquidity events involving these investments. While most of our investments are not publicly traded, applicable accounting standards require us to assume as part of our valuation process that our investments are sold in a principal market to market participants (even if we plan on holding an investment through its maturity). As a result, volatility in the capital markets can adversely affect our investment valuations. Further, the illiquidity of our investments may make it difficult for us to sell such investments if required and to value such investments. Consequently, we may realize significantly less than the value at which we carry our investments. An inability to raise capital, and any required sale of our investments for liquidity purposes, could have a material adverse impact on our business, financial condition or results of operations. In addition, a prolonged period of market illiquidity may cause us to reduce the volume of loans and debt securities we originate and/or fund and adversely affect the value of our portfolio investments, which could have a material and adverse effect on our business, financial condition, results of operations and cash flows.
We may need to raise additional capital to grow because we must distribute most of our income.
We may need additional capital to fund new investments and grow our portfolio of investments through public and/or private offerings of both debt and equity. Unfavorable economic conditions could increase our funding costs or result in a decision by lenders not to amend outstanding credit facilities or extend credit to us. A reduction in the availability of new capital could limit our ability to grow. In addition, we are required to distribute each taxable year an amount at least equal to 90% of our “investment company taxable income” (i.e., our net ordinary income and net short-term capital gains in excess of net long-term capital losses, if any) to our stockholders to continue to be taxed as a RIC. As a result, these earnings are not available to fund new investments.
We could raise capital through other channels.
The Board may determine to raise additional capital through other channels, including through private or public offerings. Capital raised through other channels could subject us to additional regulatory requirements. These additional provisions could affect our stockholders and limit our ability to take certain actions. In addition, if capital is raised through other channels, we would have to use financial and other resources to file any required registration statements and to comply with any additional regulatory requirements.
25
Regulations governing our operation as a BDC affect our ability to and the way in which we raise additional capital.
We issued the 2025 Notes and the Convertible Notes, and assumed the Credit Facility through our wholly owned subsidiary, Trinity Funding 1, LLC, and may issue other debt securities or preferred stock and/or borrow money from other banks or other financial institutions, which we refer to collectively as “senior securities,” up to the maximum amount permitted by the 1940 Act. Under the provisions of the 1940 Act, we are permitted as a BDC to issue senior securities in amounts such that our asset coverage ratio, as defined in the 1940 Act, equals at least 150% (if certain requirements are met) of total assets less all liabilities and indebtedness not represented by senior securities immediately after each issuance of senior securities. We have satisfied the requirements to increase our asset coverage ratio to 150%, including stockholder and Board approval. Under a 150% asset coverage ratio, we could potentially borrow $2 for investment purposes of every $1 of investor equity.
If the value of our assets declines, we may be unable to satisfy this test. If that happens, we may be required to sell a portion of our investments and, depending on the nature of our leverage, repay a portion of our indebtedness at a time when such sales may be disadvantageous. This could have a material adverse effect on our operations, and we may not be able to make distributions in an amount sufficient to be subject to taxation as a RIC, or at all. See “— Risks Related to our Business and Structure” We may borrow money, which may magnify the potential for gain or loss and may increase the risk of investing in us.” In addition, issuance of securities could dilute the percentage ownership of our current stockholders in us.
No person or entity from which we borrow money will have a veto power or a vote in approving or changing any of our fundamental policies. If we issue preferred stock, the preferred stock would rank “senior” to common stock in our capital structure, preferred stockholders would have separate voting rights on certain matters and might have other rights, preferences or privileges more favorable than those of our common stockholders, and the issuance of preferred stock could have the effect of delaying, deferring or preventing a transaction or a change of control that might involve a premium price for holders of our common stock or otherwise be in your best interest. Holders of our common stock will directly or indirectly bear all of the costs associated with offering and servicing any preferred stock that we issue. In addition, any interests of preferred stockholders may not necessarily align with the interests of holders of our common stock and the rights of holders of shares of preferred stock to receive distributions would be senior to those of holders of shares of our common stock.
In addition, while any senior securities remain outstanding, we will be required to make provisions to prohibit any dividend distribution to our stockholders or the repurchase of such securities or shares unless we meet the applicable asset coverage ratios at the time of the dividend distribution or repurchase. We will also be permitted to borrow amounts up to 5% of the value of our total assets for temporary or emergency purposes, which borrowings would not be considered senior securities.
We may borrow money, which may magnify the potential for gain or loss and may increase the risk of investing in us.
As part of our business strategy, we issued the 2025 Notes and the Convertible Notes, and assumed the Credit Facility through our wholly owned subsidiary, Trinity Funding 1, LLC, and we may borrow from and issue senior debt securities to banks, insurance companies and other lenders or investors. Holders of these senior securities or other credit facilities will have claims on our assets that are superior to the claims of our stockholders. Leverage magnifies the potential for loss on investments in our indebtedness and on invested equity capital. As we use leverage to partially finance our investments, you will experience increased risks of investing in our securities. If the value of our assets increases, then leveraging would cause the net asset value attributable to our common stock to increase more sharply than it would have had we not leveraged. Conversely, if the value of our assets decreases, leveraging would cause net asset value to decline more sharply than it otherwise would have had we not leveraged our business. Similarly, any increase in our income in excess of interest payable on the borrowed funds would cause our net investment income to increase more than it would without the leverage, while any decrease in our income would cause net investment income to decline more sharply than it would have had we not borrowed. Such a decline could negatively affect our ability to pay common stock distributions, scheduled debt payments or other payments related to our securities. Our ability to service any borrowings that we incur will depend largely on our financial performance and will be subject to prevailing economic conditions and competitive pressures. Leverage is generally considered a speculative investment technique.
26
The following table illustrates the effect of leverage on returns from an investment in our common stock assuming various annual returns on our portfolio, net of expenses. Leverage generally magnifies the return of stockholders when the portfolio return is positive and magnifies their losses when the portfolio return is negative. The calculations in the table below are hypothetical, and actual returns may be higher or lower than those appearing in the table below.
| Assumed Return on Our Portfolio | ||||||||
| (Net of Expenses) | ||||||||
| -10% | | -5% | | 0% | | 5% | | 10% |
Corresponding return to common stockholder (1) | (30.5)% | | (18.8)% | | (7.0)% | | 4.7% | | 16.4% |
(1) | Assumes (i) $559.7 million in total assets, (ii) $310.0 million in outstanding principal indebtedness, (iii) $238.7 million in net assets as of December 31, 2020 and (iv) weighted average interest rate, excluding fees (such as fees on undrawn amounts and amortization of financing costs), of 5.4% as of December 31, 2020. |
See “Management’s Discussion and Analysis of Financial Condition and Results of Operations — Financial Condition, Liquidity and Capital Resources” for more information regarding our borrowings.
If we fail to maintain an effective system of internal control over financial reporting, we may not be able to accurately report our financial results or prevent fraud. As a result, stockholders could lose confidence in our financial and other public reporting, which could harm our business and the market price of our common stock.
We are not required to comply with certain requirements of the Sarbanes-Oxley Act, including the internal control evaluation and certification requirements of Section 404 of that statute (“Section 404”), and will not be required to comply with all of those requirements until we have been subject to the reporting requirements of the Exchange Act for a specified period of time or, in the case of the auditor\ attestation requirements of Section 404 of the Sarbanes-Oxley Act, the date we are no longer an emerging growth company under the JOBS Act. Accordingly, our internal controls over financial reporting do not currently meet all of the standards contemplated by Section 404 that we will eventually be required to meet. We are in the process of addressing our internal controls over financial reporting and are establishing formal procedures, policies, processes and practices related to financial reporting and to the identification of key financial reporting risks, assessment of their potential impact and linkage of those risks to specific areas and activities within the Company.
Additionally, we have begun the process of documenting our internal control procedures to satisfy the requirements of Section 404, which requires annual management assessments of the effectiveness of our internal controls over financial reporting. Our independent registered public accounting firm will not be required to formally attest to the effectiveness of our internal control over financial reporting until the later of the year following our first annual report required to be filed with the SEC pursuant to the Exchange Act, or the date we are no longer an emerging growth company under the JOBS Act. Because we do not currently have comprehensive documentation of our internal controls and have not yet tested our internal controls in accordance with Section 404, we cannot conclude in accordance with Section 404 that we do not have a material weakness in our internal control over financial reporting or a combination of significant deficiencies that could result in the conclusion that we have a material weakness in our internal control over financial reporting. As a public entity, we will be required to complete our initial management assessment of our internal control over financial reporting in a timely manner. If we are not able to implement the requirements of Section 404 in a timely manner or with adequate compliance, our operations, financial reporting, or financial results could be adversely affected. Matters impacting our internal controls may cause us to be unable to report our financial information on a timely basis and thereby subject us to adverse regulatory consequences, including sanctions by the SEC or violations of applicable stock exchange listing rules, and result in a breach of the covenants under the agreements governing any of our financing arrangements. There could also be a negative reaction in the financial markets due to a loss of investor confidence in us and the reliability of our financial statements. Confidence in the reliability of our financial statements could also suffer if we or our independent registered public accounting firm were to report a material weakness in our internal control over financial reporting. This could materially adversely affect us and lead to a decline in the market price of our common stock.
27
Provisions in our credit facilities may limit our operations.
At our discretion, we may utilize the leverage available under the Credit Facility for investment and operating purposes. Additionally, we may in the future enter into additional credit facilities. To the extent we borrow money to make investments, the applicable credit facility may be backed by all or a portion of our loans and securities on which the lender will have a security interest. We may pledge up to 100% of our assets and may grant a security interest in all of our assets under the terms of any debt instrument we enter into with a lender. We expect that any security interests we grant will be set forth in a pledge and security agreement and evidenced by the filing of financing statements by the agent for the lenders. In addition, we expect that the custodian for our securities serving as collateral for such loan would include in its electronic systems notices indicating the existence of such security interests and, following notice of occurrence of an event of default, if any, and during its continuance, will only accept transfer instructions with respect to any such securities from the lenders or their designee. If we were to default under the terms of any debt instrument, the agent for the applicable lenders would be able to assume control of the timing of disposition of any or all of our assets securing such debt, which would have a material adverse effect on our business, financial condition, results of operations and cash flows.
In addition, any security interests and/or negative covenants required by any credit facility may limit our ability to create liens on assets to secure additional debt and may make it difficult for us to restructure or refinance indebtedness at or prior to maturity or obtain additional debt or equity financing. In addition, if our borrowing base under any credit facility were to decrease, we may be required to secure additional assets in an amount sufficient to cure any borrowing base deficiency. In the event that all of our assets are secured at the time of such a borrowing base deficiency, we could be required to repay advances under the credit facility or make deposits to a collection account, either of which could have a material adverse impact on our ability to fund future investments and to make distributions.
In addition, we may be subject to limitations as to how borrowed funds may be used, which may include restrictions on geographic and industry concentrations, loan size, payment frequency and status, average life, collateral interests and investment ratings, as well as regulatory restrictions on leverage which may affect the amount of funding that may be obtained. There may also be certain requirements relating to portfolio performance, including required minimum portfolio yield and limitations on delinquencies and charge-offs, a violation of which could limit further advances and, in some cases, result in an event of default. An event of default under a credit facility could result in an accelerated maturity date for all amounts outstanding thereunder, which could have a material adverse effect on our business and financial condition. This could reduce our liquidity and cash flow and impair our ability to grow our business.
Any defaults under a credit facility could adversely affect our business.
In the event we default under any credit facility or other borrowings, our business could be adversely affected as we may be forced to sell a portion of our investments quickly and prematurely at what may be disadvantageous prices to us in order to meet our outstanding payment obligations and/or support working capital requirements under the credit facility, any of which would have a material adverse effect on our business, financial condition, results of operations and cash flows. In addition, following any such default, the agent for the lenders under such credit facility could assume control of the disposition of any or all of our assets, including the selection of such assets to be disposed and the timing of such disposition, which would have a material adverse effect on our business, financial condition, results of operations and cash flows.
We are exposed to risks associated with changes in interest rates.
Because we may borrow money to make investments, our net investment income will depend, in part, upon the difference between the rate at which we borrow funds and the rate at which we invest those funds. As a result, we can offer no assurance that a significant change in market interest rates will not have a material adverse effect on our net investment income. A reduction in the interest rates on new investments relative to interest rates on current investments could have an adverse impact on our net investment income. However, an increase in interest rates could decrease the value of any investments we hold which earn fixed interest rates and also could increase our interest expense, thereby decreasing our net income. Also, an increase in interest rates available to investors could make an
28
investment in our common stock less attractive if we are not able to increase our distribution rate, which could reduce the value of our common stock. Further, rising interest rates could also adversely affect our performance if such increases cause our borrowing costs to rise at a rate in excess of the rate that our investments yield.
In periods of rising interest rates, to the extent we borrow money subject to a floating interest rate, our cost of funds would increase, which could reduce our net investment income. Further, rising interest rates could also adversely affect our performance if we hold investments with floating interest rates, subject to specified minimum interest rates (such as a LIBOR floor), while at the same time engaging in borrowings subject to floating interest rates not subject to such minimums. In such a scenario, rising interest rates may increase our interest expense, even though our interest income from investments is not increasing in a corresponding manner as a result of such minimum interest rates.
If general interest rates rise, there is a risk that the portfolio companies in which we hold floating rate securities will be unable to pay escalating interest amounts, which could result in a default under their loan documents with us. Rising interest rates could also cause portfolio companies to shift cash from other productive uses to the payment of interest, which may have a material adverse effect on their business and operations and could, over time, lead to increased defaults. In addition, rising interest rates may increase pressure on us to provide fixed rate loans to our portfolio companies, which could adversely affect our net investment income, as increases in our cost of borrowed funds would not be accompanied by increased interest income from such fixed-rate investments.
On July 27, 2017, the United Kingdom’s Financial Conduct Authority (the “FCA”), which regulates LIBOR, announced that it intends to phase out LIBOR by the end of 2021. It is unclear if at that time whether LIBOR will cease to exist or if new methods of calculating LIBOR will be established such that it continues to exist after 2021. The U.S. Federal Reserve, in conjunction with the Alternative Reference Rates Committee, a steering committee comprised of large U.S. financial institutions, is considering replacing U.S. dollar LIBOR with a new index calculated by short term repurchase agreements, backed by Treasury securities called the Secured Overnight Financing Rate (“SOFR”). The first publication of SOFR was released in April 2018. Whether or not SOFR attains market traction as a LIBOR replacement remains a question and the future of LIBOR at this time is uncertain. In addition, on March 25, 2020, the FCA stated that although the central assumption that firms cannot rely on LIBOR being published after the end of 2021 has not changed, the outbreak of COVID-19 has delayed the timing of many firms’ transition planning, and the FCA will continue to assess the impact of the COVID-19 outbreak on transition timelines and update the marketplace as soon as possible. Furthermore, on November 30, 2020, Intercontinental Exchange, Inc. (“ICE”) announced that the ICE Benchmark Administration Limited, a wholly owned subsidiary of ICE and the administrator of LIBOR, will consult in early December 2020 to consider extending the LIBOR transition deadline to the end of June 2023. The consultation was published on December 4, 2020 and was open for feedback until late January 2021. Despite this potential extension of the US LIBOR transition deadline, US regulators continue to urge financial institutions to stop entering into new LIBOR transactions by the end of 2021. Although SOFR appears to be the preferred replacement rate for U.S. dollar LIBOR, at this time, it is not possible to predict the effect of any such changes, any establishment of alternative reference rates or any other reforms to LIBOR that may be enacted. The elimination of LIBOR or any other changes or reforms to the determination or supervision of LIBOR could have an adverse impact on the market for or value of any LIBOR-linked securities, loans, and other financial obligations or extensions of credit held by or due to us or on our overall financial condition or results of operations. In addition, if LIBOR ceases to exist, we may need to renegotiate credit agreements extending beyond 2021 with our portfolio companies that utilize LIBOR as a factor in determining the interest rate, in order to replace LIBOR with the new standard that is established, which may have an adverse effect on our overall financial condition or results of operations. Following the replacement of LIBOR, some or all of these credit agreements may bear interest a lower interest rate, which could have an adverse impact on our results of operations. Furthermore, under the Credit Facility with Credit Suisse, borrowings generally will bear interest at a rate of the three-month LIBOR plus 3.25%. If LIBOR ceases to exist, we will need to renegotiate certain terms of the Credit Facility. If we are unable to do so, amounts drawn under the Credit Facility may bear interest at a higher rate, which would increase the cost of our borrowings and, in turn, affect our results of operations.
29
Falling interest rates may negatively impact our investment income.
As a result of the decision by the Federal Reserve Board to decrease the target range for the federal funds rate in response to the COVID-19 pandemic, interest rates have decreased. Some of our credit agreements with our portfolio companies utilize the prime rate as a factor in determining interest rate. However, under the Credit Facility, borrowing generally will bear interest at a rate of the three-month LIBOR plus 3.25%. Accordingly, a reduction in interest rates will result in a decrease in our total investment income unless limited by interest rate floors. Further, our net investment income could decrease if there is not a corresponding decrease in the interest that we pay on our borrowings.
If we do not invest a sufficient portion of our assets in qualifying assets, we could fail to qualify as a BDC, which would have a material adverse effect on our business, financial condition and results of operations.
As a BDC, we may not acquire any assets other than “qualifying assets” unless, at the time of and after giving effect to such acquisition, at least 70% of our total assets are qualifying assets. We believe that most of the investments that we may acquire in the future will constitute qualifying assets. However, we may be precluded from investing in what we believe are attractive investments if such investments are not qualifying assets for purposes of the 1940 Act. If we do not invest a sufficient portion of our assets in qualifying assets, we could violate the 1940 Act provisions applicable to BDCs. As a result of such violation, specific rules under the 1940 Act could prevent us, for example, from making follow-on investments in existing portfolio companies which could result in the dilution of our position or could require us to dispose of investments at inappropriate times in order to come into compliance with the 1940 Act. If we need to dispose of investments quickly, it could be difficult to dispose of such investments on favorable terms. We may not be able to find a buyer for such investments and, even if we do find a buyer, we may have to sell the investments at a substantial loss. Any such outcomes would have a material adverse effect on our business, financial condition, results of operations, and cash flows.
Most or a substantial portion of our portfolio investments will be recorded at fair value as determined in good faith by the Board and, as a result, there may be uncertainty as to the value of our portfolio investments.
Under the 1940 Act, we are required to carry our portfolio investments at market value or if there is no readily available market value, at fair value as determined by the Board. Most or a substantial portion of our portfolio investments may take the form of securities that are not publicly traded. The fair value of securities and other investments that are not publicly traded may not be readily determinable, and we value these securities at fair value as determined in good faith by the Board, including to reflect significant events affecting the value of our securities. As part of the valuation process, we may take into account the following types of factors, if relevant, in determining the fair value of our investments:
• a comparison of the portfolio company’s securities to publicly traded securities;
• the enterprise value of a portfolio company;
• the nature and realizable value of any collateral;
• the portfolio company’s ability to make payments and its earnings and discounted cash flow;
• the markets in which the portfolio company does business; and
• changes in the interest rate environment and the credit markets generally that may affect the price at which similar investments may be made in the future and other relevant factors.
We expect that most of our investments (other than cash and cash equivalents) will be classified as Level 3 in the fair value hierarchy and require disclosures about the level of disaggregation along with the inputs and valuation techniques we use to measure fair value. This means that our portfolio valuations are based on unobservable inputs and our own assumptions about how market participants would price the asset or liability in question. Inputs into the determination of fair value of our portfolio investments require significant management judgment or estimation. Even if observable market data is available, such information may be the result of consensus pricing information or broker quotes, which include a disclaimer that the broker would not be held to such a price in an actual transaction. The
30
non-binding nature of consensus pricing and/or quotes accompanied by disclaimers materially reduces the reliability of such information. We employ the services of one or more independent service providers to review the valuation of these securities. The types of factors that the Board may take into account in determining the fair value of our investments generally include, as appropriate, comparison to publicly traded securities including such factors as yield, maturity and measures of credit quality, the enterprise value of a portfolio company, the nature and realizable value of any collateral, the portfolio company’s ability to make payments and its earnings and discounted cash flow, the markets in which the portfolio company does business and other relevant factors. Because such valuations, and particularly valuations of private securities and private companies, are inherently uncertain, may fluctuate over short periods of time and may be based on estimates, our determinations of fair value may differ materially from the values that would have been used if a ready market for these securities existed. Due to this uncertainty in the value of our portfolio investments, a fair value determination may cause net asset value on a given date to materially understate or overstate the value that we may ultimately realize upon one or more of our investments. As a result, investors purchasing shares of our common stock based on an overstated net asset value would pay a higher price than the value of the investments might warrant. Conversely, investors selling shares during a period in which the net asset value understates the value of investments will receive a lower price for their shares than the value the investment portfolio might warrant.
We will adjust quarterly the valuation of our portfolio to reflect the determination of the Board of the fair value of each investment in our portfolio. Any changes in fair value are recorded in our statements of operations as net change in unrealized gain (loss) on investments.
The Board may change our investment objective, operating policies and strategies without prior notice or stockholder approval, the effects of which may be adverse.
The Board has the authority, except as otherwise prohibited by the 1940 Act, to modify or waive certain of our operating policies and strategies without prior notice and without stockholder approval. However, absent stockholder approval, we may not change the nature of our business so as to cease to be, or withdraw our election as, a BDC. Under Maryland law, we also cannot be dissolved without prior stockholder approval except by judicial action. We cannot predict the effect any changes to our current operating policies and strategies would have on our business, operating results and the price value of our common stock. Nevertheless, any such changes could adversely affect our business and impair our ability to make distributions.
Internal and external cyber threats, as well as other disasters, could impair our ability to conduct business effectively.
The occurrence of a disaster, such as a cyber-attack against us or against a third party that has access to our data or networks, a natural catastrophe, an industrial accident, failure of our disaster recovery systems, or consequential employee error, could have an adverse effect on our ability to communicate or conduct business, negatively impacting our operations and financial condition. This adverse effect can become particularly acute if those events affect our electronic data processing, transmission, storage, and retrieval systems, or impact the availability, integrity, or confidentiality of our data.
We depend heavily upon computer systems to perform necessary business functions. Despite our implementation of a variety of security measures, our computer systems, networks, and data, like those of other companies, could be subject to cyber-attacks and unauthorized access, use, alteration, or destruction, such as from physical and electronic break-ins or unauthorized tampering. If one or more of these events occurs, it could potentially jeopardize the confidential, proprietary, and other information processed, stored in, and transmitted through our computer systems and networks. Such an attack could cause interruptions or malfunctions in our operations, which could result in financial losses, litigation, regulatory penalties, client dissatisfaction or loss, reputational damage, and increased costs associated with mitigation of damages and remediation.
Third parties with which we do business may also be sources of cybersecurity or other technological risk. We outsource certain functions, and these relationships allow for the storage and processing of our information, as well as client, counterparty, employee, and borrower information. While we engage in actions to reduce our exposure resulting from outsourcing, ongoing threats may result in unauthorized access, loss, exposure, destruction, or other
31
cybersecurity incidents that adversely affects our data, resulting in increased costs and other consequences as described above.
We and our third-party providers are currently impacted by quarantines and similar measures being enacted by governments in response to the COVID-19 pandemic that are obstructing the regular functioning of business workforces (including requiring employees to work from external locations and their homes). In response to the COVID-19 pandemic, we instituted a work from home policy until it was deemed safe to return to the office. We have since reopened our principal office but permit employees to work from home on a voluntary basis. An extended period of remote working, whether by us or our third-party providers, could strain technology resources and introduce operational risks, including heightened cybersecurity risk. Remote working environments may be less secure and more susceptible to hacking attacks, including phishing and social engineering attempts that seek to exploit the COVID-19 pandemic. Accordingly, the risks described above are heightened under current conditions.
We may incur lender liability as a result of our lending activities.
In recent years, a number of judicial decisions have upheld the right of borrowers and others to sue lending institutions on the basis of various evolving legal theories, collectively termed “lender liability.” Generally, lender liability is founded on the premise that a lender has either violated a duty, whether implied or contractual, of good faith and fair dealing owed to the borrower or has assumed a degree of control over the borrower resulting in the creation of a fiduciary duty owed to the borrower or its other creditors or stockholders. We may be subject to allegations of lender liability, which could be time-consuming and expensive to defend and result in significant liability.
We may incur liability as a result of providing managerial assistance to our portfolio companies.
In the course of providing significant managerial assistance to certain portfolio companies, certain of our management and directors may serve as directors on the boards of such companies. To the extent that litigation arises out of investments in these companies, our management and directors may be named as defendants in such litigation, which could result in an expenditure of our funds, through our indemnification of such officers and directors, and the diversion of management time and resources.
Our management team and investment professionals may not be able to achieve the same or similar returns as those achieved by the Legacy Funds or by such persons while they were employed at prior positions.
The track record and achievements of our management team and investment professionals are not necessarily indicative of future results that will be achieved by us. As a result, we may not be able to achieve the same or similar returns as those achieved by our management team and investment professionals at their prior positions, including at the Legacy Funds.
Risks Related to Our Investments
Our investment strategy focuses on growth stage companies, which are subject to many risks, including dependence on the need to raise additional capital, volatility, intense competition, shortened product life cycles, changes in regulatory and governmental programs, periodic downturns, below investment grade ratings, which could cause you to lose all or part of your investment in us.
We invest primarily in growth stage companies, many of which may have narrow product lines and small market shares, which tend to render them more vulnerable to competitors’ actions and market conditions, as well as to general economic downturns, compared to more mature companies. The revenues, income (or losses), and projected financial performance and valuations of growth stage companies can and often do fluctuate suddenly and dramatically. For these reasons, investments in our portfolio companies, if rated by one or more ratings agency, would typically be rated below “investment grade,” which refers to securities rated by ratings agencies below the four highest rating categories. Our target growth stage companies are geographically concentrated and are therefore highly susceptible to materially negative local, political, natural and economic events. In addition, high growth industries are generally characterized by abrupt business cycles and intense competition. Overcapacity in high growth
32
industries, together with cyclical economic downturns, may result in substantial decreases in the value of many growth stage companies and/or their ability to meet their current and projected financial performance to service our debt. Furthermore, growth stage companies also typically rely on venture capital and private equity investors, or initial public offerings, or sales for additional capital.
Venture capital firms in turn rely on their limited partners to pay in capital over time in order to fund their ongoing and future investment activities. To the extent that venture capital firms’ limited partners are unable or choose not to fulfill their ongoing funding obligations, the venture capital firms may be unable to continue operationally and/or financially supporting the ongoing operations of our portfolio companies which could materially and adversely impact our financing arrangement with the portfolio company.
These companies, their industries, their products and customer demand and the outlook and competitive landscape for their industries are all subject to change, which could adversely impact their ability to execute their business plans and generate cash flow or raise additional capital that would serve as the basis for repayment of our loans. Therefore, our growth stage companies may face considerably more risk of loss than do companies at other stages of development.
The equipment financing industry is highly competitive and competitive forces could adversely affect the financing rates and resale prices that we may realize on our equipment financing investment portfolio and the prices that we have to pay to acquire our investments.
As part of our investment strategy, we engage in equipment financing, through which we finance equipment to growth stage companies. Equipment manufacturers, corporations, partnerships and others offer users an alternative to the purchase of most types of equipment with payment terms that vary widely depending on the type of financing, the lease or loan term and the type of equipment. In seeking equipment financing transactions, we will compete with financial institutions, manufacturers and public and private leasing companies, many of which may have greater financial resources than us.
Some types of equipment are under special government regulation which may make the equipment more costly to acquire, own, maintain under equipment financings and sell.
The use, maintenance and ownership of certain types of equipment are regulated by federal, state and/or local authorities. Regulations may impose restrictions and financial burdens on our ownership and operation of equipment. Changes in government regulations, industry standards or deregulation may also affect the ownership, operation and resale value of equipment. For example, certain types of equipment are subject to extensive safety and operating regulations imposed by government and/or industry self- regulatory organizations which may make these types of equipment more costly to acquire, own, maintain under equipment financings and sell. These agencies or organizations may require changes or improvements to equipment, and we may have to spend our own capital to comply. These changes may also require the equipment to be removed from service for a period of time. The terms of equipment financings may provide for payment reductions if the equipment must remain out of service for an extended period or is removed from service. We may then have reduced operating revenues from equipment financings for these items of equipment. If we did not have the capital to make a required change, we might be required to sell the affected equipment or to sell other items of its equipment in order to obtain the necessary cash; in either event, we could suffer a loss on our investment and might lose future revenues, and we might also have adverse tax consequences.
We are subject to risks inherent in the equipment financing business that may adversely affect our ability to finance our portfolio on terms that will permit us to generate profitable rates of return for investors.
A number of economic conditions and market factors, many of which we cannot control, could threaten our ability to operate profitably. These include changes in economic conditions, including fluctuations in demand for equipment, interest rates and inflation rates; the timing of purchases and the ability to forecast technological advances for equipment; technological and economic obsolescence; and increases in our expenses.
33
Demand for equipment fluctuates, and periods of weak demand could adversely affect equipment financing rates and resale prices that we may realize on our investment portfolio while periods of high demand could adversely affect the prices that we have to pay to acquire our investments. Such fluctuations in demand could therefore adversely affect the ability of a leasing program to invest its capital in a timely and profitable manner. Equipment lessors have experienced a more difficult market in which to make suitable investments during historical periods of reduced growth and recession in the U.S. economy as a result of the softening demand for capital equipment during these periods. An economic recession resulting in lower levels of capital expenditure by businesses may result in more used equipment becoming available on the market and downward pressure on prices and equipment financing rates due to excess inventory. Periods of low interest rates exert downward pressure on equipment financing rates and may result in less demand for equipment financings. Furthermore, a decline in corporate expansion or demand for capital goods could delay investment of our capital, and its production of financing revenues. There can be no assurance as to what future developments may occur in the economy in general or in the demand for equipment and other asset-based financing in particular.
Global economic, political and market conditions, including uncertainty about the financial stability of the United States, could have a significant adverse effect on our business, financial condition and results of operations.
Downgrades by rating agencies to the U.S. government’s credit rating or concerns about its credit and deficit levels in general could cause interest rates and borrowing costs to rise, which may negatively impact both the perception of credit risk associated with our debt portfolio and our ability to access the debt markets on favorable terms. In addition, a decreased U.S. government credit rating could create broader financial turmoil and uncertainty, which may weigh heavily on our financial performance and the value of our common stock.
Deterioration in the economic conditions in the Eurozone and globally, including instability in financial markets, may pose a risk to our business. In recent years, financial markets have been affected at times by a number of global macroeconomic and political events, including the following: large sovereign debts and fiscal deficits of several countries in Europe and in emerging markets jurisdictions, levels of non-performing loans on the balance sheets of European banks, the potential effect of any European country leaving the Eurozone, the potential effect of the United Kingdom leaving the European Union, and market volatility and loss of investor confidence driven by political events. Market and economic disruptions have affected, and may in the future affect, consumer confidence levels and spending, personal bankruptcy rates, levels of incurrence and default on consumer debt and home prices, among other factors. We cannot assure you that market disruptions in Europe, including the increased cost of funding for certain governments and financial institutions, will not impact the global economy, and we cannot assure you that assistance packages will be available, or if available, be sufficient to stabilize countries and markets in Europe or elsewhere affected by a financial crisis. To the extent uncertainty regarding any economic recovery in Europe negatively impacts consumer confidence and consumer credit factors, our and our portfolio companies’ business, financial condition and results of operations could be significantly and adversely affected.
The Chinese capital markets have also experienced periods of instability over the past several years. The current political climate has also intensified concerns about a potential trade war between the U.S. and China in connection with each country’s recent or proposed tariffs on the other country’s products. These market and economic disruptions and the potential trade war with China have affected, and may in the future affect, the U.S. capital markets, which could adversely affect our and our portfolio companies’ business, financial condition or results of operations.
The current global financial market situation, as well as various social and political circumstances in the U.S. and around the world (including wars and other forms of conflict, terrorist acts, security operations and catastrophic events such as fires, floods, earthquakes, tornadoes, hurricanes and global health epidemics), may contribute to increased market volatility and economic uncertainties or deterioration in the U.S. and worldwide. For example, the recent outbreak of COVID-19 in many countries continues to adversely impact global commercial activity, and has contributed to significant volatility in financial markets. The outbreak of COVID-19 may have a material adverse impact on the ability of our portfolio companies to fulfill their end customers’ orders due to supply chain delays, limited access to key commodities or technologies or other events that impact their manufacturers or their suppliers. Such events have
34
affected, and may in the future affect, the global and U.S. capital markets, and our business, financial condition or results of operations.
Additionally, the U.S. government’s credit and deficit concerns, the European sovereign debt crisis, and the potential trade war with China could cause interest rates to be volatile, which may negatively impact our and our portfolio companies’ ability to access the debt markets on favorable terms.
The COVID-19 pandemic has caused severe disruptions in the global economy and has disrupted financial activity in the areas in which we or our portfolio companies operate.
The COVID-19 pandemic has resulted in widespread outbreaks of illness and numerous deaths, adversely impacted global and U.S. commercial activity and contributed to significant volatility in certain equity and debt markets. The global impact of the outbreak is rapidly evolving, and many countries and localities, including the U.S. and states in which our portfolio companies operate, have reacted by instituting quarantines, prohibitions on travel and the closure of offices, businesses, schools, retail stores and other public venues. Businesses are also implementing similar precautionary measures. Such measures, as well as the general uncertainty surrounding the dangers and impact of the COVID-19 pandemic, have created significant disruption in supply chains and economic activity and are having a particularly adverse impact on transportation, hospitality, tourism, entertainment and other industries, including industries in which certain of our portfolio companies operate. The impact of the COVID-19 pandemic has led to significant volatility and declines in the global public equity markets and it is uncertain how long this volatility will continue. As the COVID-19 pandemic continues to spread, the potential impacts, including a global, regional or other economic recession, are increasingly uncertain and difficult to assess. Although the Federal Food and Drug Administration authorized certain vaccines for emergency use starting in December 2020, it remains unclear how quickly the vaccines will be distributed nationwide and globally or when “herd immunity” will be achieved and the restrictions that were imposed to slow the spread of the virus will be lifted entirely. The delay in distributing the vaccines could cause people to self-isolate and not participate in the economy at pre-pandemic levels for a prolonged period of time.
Even after the COVID-19 pandemic subsides, the U.S. economy and most other major global economies may continue to experience a recession, and we anticipate our business and operations could be materially adversely affected by a prolonged recession in the United States and other major markets. Some economists and major investment banks have expressed concern that the continued spread of the virus globally could lead to a world-wide economic downturn, the impacts of which could last for some time after the COVID-19 pandemic is controlled and/or abates.
The COVID-19 pandemic (including the preventative measures taken in response thereto) has to date (i) created significant business disruption issues for certain of our portfolio companies, and (ii) materially and adversely impacted the value and performance of certain of our portfolio companies. The COVID-19 pandemic is having a particularly adverse impact on industries in which certain of our portfolio companies operate, including manufacturing and retail. Certain of our portfolio companies in other industries have also been significantly impacted. The COVID-19 pandemic is continuing as of the filing date of this annual report on Form 10-K, and its extended duration may have further adverse impacts on our portfolio companies after December 31, 2020, including for the reasons described herein. Although on March 27, 2020, the U.S. government enacted the Coronavirus Aid, Relief, and Economic Security Act (the “CARES Act”), which contains provisions intended to mitigate the adverse economic effects of the COVID-19 pandemic, it is uncertain whether, or how much, our portfolio companies have benefited or may benefit from the CARES Act or any other subsequent legislation intended to provide financial relief or assistance. As a result of this disruption and the pressures on their liquidity, certain of our portfolio companies have been, or may continue to be, incentivized to draw on most, if not all, of the unfunded portion of any revolving or delayed draw term loans made by us, subject to availability under the terms of such loans.
Further, disruptions in the capital markets caused by the COVID-19 pandemic have increased the spread between the yields realized on risk-free and higher risk securities, resulting in illiquidity in parts of the capital markets. These and future market disruptions and/or illiquidity would be expected to have an adverse effect on our business, financial condition, results of operations and cash flows.
35
Unfavorable economic conditions also would be expected to increase our funding costs, limit our access to the capital markets or result in a decision by lenders not to extend credit to us. These events have limited and could continue to limit our investment originations, limit our ability to grow and have a material negative impact on our and our portfolio companies’ operating results and the fair values of our debt and equity investments.
Political, social and economic uncertainty, including uncertainty related to the COVID-19 pandemic, creates and exacerbates risks.
Social, political, economic and other conditions and events (such as natural disasters, epidemics and pandemics, terrorism, conflicts and social unrest) will occur that create uncertainty and have significant impacts on issuers, industries, governments and other systems, including the financial markets, to which companies and their investments are exposed. As global systems, economies and financial markets are increasingly interconnected, events that once had only local impact are now more likely to have regional or even global effects. Events that occur in one country, region or financial market will, more frequently, adversely impact issuers in other countries, regions or markets, including in established markets such as the U.S. These impacts can be exacerbated by failures of governments and societies to adequately respond to an emerging event or threat.
Uncertainty can result in or coincide with, among other things: increased volatility in the financial markets for securities, derivatives, loans, credit and currency; a decrease in the reliability of market prices and difficulty in valuing assets (including portfolio company assets); greater fluctuations in spreads on debt investments and currency exchange rates; increased risk of default (by both government and private obligors and issuers); further social, economic, and political instability; nationalization of private enterprise; greater governmental involvement in the economy or in social factors that impact the economy; changes to governmental regulation and supervision of the loan, securities, derivatives and currency markets and market participants and decreased or revised monitoring of such markets by governments or self-regulatory organizations and reduced enforcement of regulations; limitations on the activities of investors in such markets; controls or restrictions on foreign investment, capital controls and limitations on repatriation of invested capital; the significant loss of liquidity and the inability to purchase, sell and otherwise fund investments or settle transactions (including, but not limited to, a market freeze); unavailability of currency hedging techniques; substantial, and in some periods extremely high, rates of inflation, which can last many years and have substantial negative effects on credit and securities markets as well as the economy as a whole; recessions; and difficulties in obtaining and/or enforcing legal judgments.
For example, the COVID-19 pandemic has led to and for an unknown period of time will continue to lead to disruptions in local, regional, national and global markets and economies affected thereby. With respect to the U.S. credit markets, this outbreak has resulted in, and until fully resolved is likely to continue to result in, the following, among other things: (i) government imposition of various forms of shelter in place orders and the closing of “non-essential” businesses, resulting in significant disruption to the businesses of many middle-market loan borrowers, including supply chains, demand and practical aspects of their operations, as well as in lay-offs of employees, and, while these effects are hoped to be temporary, some effects could be persistent or even permanent; (ii) increased draws by borrowers on revolving lines of credit; (iii) increased requests by borrowers for amendments and waivers of their credit agreements to avoid default, increased defaults by such borrowers and/or increased difficulty in obtaining refinancing at the maturity dates of their loans; (iv) volatility and disruption of these markets including greater volatility in pricing and spreads and difficulty in valuing loans during periods of increased volatility, and liquidity issues; and (v) rapidly evolving proposals and/or actions by state and federal governments to address problems being experienced by the markets and by businesses and the economy in general which will not necessarily adequately address the problems facing the loan market and businesses. This outbreak is having, and any future outbreaks could have, an adverse impact on the markets and the economy in general, which could have a material adverse impact on, among other things, the ability of lenders to originate loans, the volume and type of loans originated, and the volume and type of amendments and waivers granted to borrowers and remedial actions taken in the event of a borrower default, each of which could negatively impact the amount and quality of loans available for investment by us and returns to us, among other things. As of the date of this annual report on Form 10-K, it is impossible to determine the scope of this outbreak, or any future outbreaks, how long any such outbreak, market disruption or uncertainties may last, the effect any governmental actions will have or the full potential impact on us and our portfolio companies.
36
Although it is impossible to predict the precise nature and consequences of these events, or of any political or policy decisions and regulatory changes occasioned by emerging events or uncertainty on applicable laws or regulations that impact us, our portfolio companies and our investments, it is clear that these types of events are impacting and will, for at least some time, continue to impact us and our portfolio companies. For example, growth stage companies in which we may invest are being significantly impacted by these emerging events and the uncertainty caused by these events. The effects of a public health emergency may materially and adversely impact (i) the value and performance of us and our portfolio companies, (ii) the ability of our borrowers to continue to meet loan covenants or repay loans provided by us on a timely basis or at all, which may require us to restructure our investments or write down the value of our investments, (iii) our ability to repay debt obligations, on a timely basis or at all, or (iv) our ability to source, manage and divest investments and achieve our investment objectives, all of which could result in significant losses to us.
If the economy is unable to substantially reopen, and high levels of unemployment continue for an extended period of time, loan delinquencies, loan nonaccruals, problem assets, and bankruptcies may increase. In addition, collateral for our loans may decline in value, which could cause loan losses to increase and the net worth and liquidity of loan guarantors could decline, impairing their ability to honor commitments to us. An increase in loan delinquencies and non-accruals or a decrease in loan collateral and guarantor net worth could result in increased costs and reduced income which would have a material adverse effect on our business, financial condition or results of operations.
We will also be negatively affected if the operations and effectiveness of us or a portfolio company (or any of the key personnel or service providers of the foregoing) are compromised or if necessary or beneficial systems and processes are disrupted.
Any public health emergency, including the COVID-19 pandemic or any outbreak of other existing or new epidemic diseases, or the threat thereof, and the resulting financial and economic market uncertainty could have a significant adverse impact on us and the fair value of our investments and our portfolio companies.
The extent of the impact of any public health emergency, including the COVID-19 pandemic, on our and our portfolio companies’ operational and financial performance will depend on many factors, including the duration and scope of such public health emergency, the actions taken by governmental authorities to contain its financial and economic impact, the extent of any related travel advisories and restrictions implemented, the impact of such public health emergency on overall supply and demand, goods and services, investor liquidity, consumer confidence and levels of economic activity and the extent of its disruption to important global, regional and local supply chains and economic markets, all of which are highly uncertain and cannot be predicted. In addition, our and our portfolio companies’ operations may be significantly impacted, or even temporarily or permanently halted, as a result of government quarantine measures, voluntary and precautionary restrictions on travel or meetings and other factors related to a public health emergency, including its potential adverse impact on the health of any of our or our portfolio companies’ personnel. This could create widespread business continuity issues for us and our portfolio companies.
These factors may also cause the valuation of our investments to differ materially from the values that we may ultimately realize. Our valuations, and particularly valuations of private investments and private companies, are inherently uncertain, may fluctuate over short periods of time and are often based on estimates, comparisons and qualitative evaluations of private information. As a result, our valuations may not show the completed or continuing impact of the COVID-19 pandemic and the resulting measures taken in response thereto. Any public health emergency, including the COVID-19 pandemic or any outbreak of other existing or new epidemic diseases, or the threat thereof, and the resulting financial and economic market uncertainty could have a significant adverse impact on us and the fair value of our investments and our portfolio companies.
Economic recessions or downturns could impair our portfolio companies and harm our operating results.
Many of our portfolio companies may be susceptible to economic slowdowns or recessions and may be unable to repay our debt investments during these periods. The recent global outbreak of COVID-19 has disrupted economic markets, and the prolonged economic impact is uncertain. Some economists and major investment banks have
37
expressed concern that the continued spread of the virus globally could lead to a worldwide economic downturn. Many manufacturers of goods in China and other countries in Asia have seen a downturn in production due to the suspension of business and temporary closure of factories in an attempt to curb the spread of the illness. As the impact of the COVID-19 pandemic spreads to other parts of the world, similar impacts may occur with respect to affected countries. In the past, instability in the global capital markets resulted in disruptions in liquidity in the debt capital markets, significant write-offs in the financial services sector, the re-pricing of credit risk in the broadly syndicated credit market and the failure of major domestic and international financial institutions. In particular, in past periods of instability, the financial services sector was negatively impacted by significant write-offs as the value of the assets held by financial firms declined, impairing their capital positions and abilities to lend and invest. In addition, continued uncertainty surrounding the negotiation of trade deals between Britain and the European Union following the United Kingdom’s exit from the European Union and uncertainty between the United States and other countries, including China, with respect to trade policies, treaties, and tariffs, among other factors, have caused disruption in the global markets. There can be no assurance that market conditions will not worsen in the future.
In an economic downturn, we may have non-performing assets or non-performing assets may increase, and the value of our portfolio is likely to decrease during these periods. Adverse economic conditions may also decrease the value of any collateral securing our loans. A severe recession may further decrease the value of such collateral and result in losses of value in our portfolio and a decrease in our revenues, net income, assets and net worth. Unfavorable economic conditions also could increase our funding costs, limit our access to the capital markets or result in a decision by lenders not to extend credit to us on terms we deem acceptable. These events could prevent us from increasing investments and harm our operating results.
The occurrence of recessionary conditions and/or negative developments in the domestic and international credit markets may significantly affect the markets in which we do business, the value of our investments, and our ongoing operations, costs and profitability. Any such unfavorable economic conditions, including rising interest rates, may also increase our funding costs, limit our access to capital markets or negatively impact our ability to obtain financing, particularly from the debt markets. In addition, any future financial market uncertainty could lead to financial market disruptions and could further impact our ability to obtain financing. These events could limit our investment originations, limit our ability to grow and negatively impact our operating results and financial condition.
Our investments are geographically concentrated, which may result in a single occurrence in a particular geographic area having a disproportionate negative impact on our investment portfolio.
Investments in a particular geographic region may be particularly susceptible to economic conditions and regulatory requirements. To the extent our investments are concentrated in a particular region or group of regions, our investment portfolio may be more volatile than a more geographically investment portfolio. Any deterioration in the economy, or adverse events in such regions, may increase the rate of delinquency and default experience (and as a consequence, losses) with respect to our investments in such region. Our investments are geographically concentrated in the Western and Northeastern part of the United States. As result, we may be more susceptible to being adversely affected by any single occurrence in those regions.
For example, portfolio companies in California, may be particularly susceptible to certain types of hazards, such as earthquakes, floods, mudslides, wildfires and other national disasters, which could have a negative impact on their business and negatively impacting such company’s ability to meet their obligations under their debt securities that we hold. Additionally, adverse economic conditions or other factors particularly affecting a specific region could increase the risk of loss on our investments.
Our investments in leveraged portfolio companies may be risky, and you could lose all or part of your investment.
Investment in leveraged companies involves a number of significant risks. Leveraged companies in which we invest may have limited financial resources and may be unable to meet their obligations under their debt securities that we hold. Such developments may be accompanied by a deterioration in the value of any collateral and a reduction in the likelihood of our realizing any guarantees that we may have obtained in connection with our
38
investment. In addition, our junior secured loans are generally subordinated to senior loans. As such, other creditors may rank senior to us in the event of an insolvency.
In addition, investing in small, fast-growing, private companies involves a number of significant risks, including the following:
• these companies may have limited financial resources and may be unable to meet their obligations under their debt securities that we hold. This failure to meet obligations may be accompanied by a deterioration in the value of any collateral and a reduction in the likelihood of us realizing any guarantees we may have obtained in connection with our investment;
• they typically have shorter operating histories, narrower product lines and smaller market shares than larger businesses, which tend to render them more vulnerable to competitors’ actions, market conditions, and general economic downturns;
• they are more likely to depend on the management talents and efforts of a small group of persons; therefore, the death, disability, resignation or termination of one or more of these persons could have a material adverse impact on our portfolio company and, in turn, on us;
• they generally have less predictable operating results, may from time to time be parties to litigation, may be engaged in rapidly changing businesses with products subject to a substantial risk of obsolescence, and may require substantial additional capital to support their operations, finance expansion, or maintain their competitive position. In addition, our executive officers and directors may, in the ordinary course of business, be named as defendants in litigation arising from our investments in the portfolio companies; and
• they may have difficulty accessing the capital markets to meet future capital needs, which may limit their ability to grow or to repay their outstanding debt upon maturity.
Our investments are very risky and highly speculative.
We invest primarily in secured loans and select equity and equity-related investments issued by, and provide equipment financing to, small, fast-growing private companies. We invest primarily in secured loans made to companies whose debt has generally not been rated by any rating agency, although we would expect such debt, if rated, to fall below investment grade. Securities rated below investment grade are often referred to as “high yield” securities and “junk bonds,” and are considered “high risk” and speculative in nature compared to debt instruments that are rated above investment grade.
Generally, little public information exists about these companies, and we are required to rely on the ability of our senior management team and investment professionals to obtain adequate information to evaluate the potential returns from investing in these companies. If we are unable to uncover all material information about these companies, we may not make a fully informed investment decision, and we may lose money on our investments. Also, privately held companies frequently have less diverse product lines and smaller market presence than larger competitors. These factors could adversely affect our investment returns as compared to companies investing primarily in the securities of public companies.
Senior Secured Loans. There is a risk that the collateral securing our loans may decrease in value over time, may be difficult to sell in a timely manner, may be difficult to appraise and may fluctuate in value based upon the success of the business and market conditions, including as a result of the inability of the portfolio company to raise additional capital. In some circumstances, our liens on the collateral securing our loans could be subordinated to claims of other creditors. In addition, deterioration in a portfolio company’s financial condition and prospects, including its inability to raise additional capital, may be accompanied by deterioration in the value of the collateral for the loan. Consequently, the fact that a loan is secured does not guarantee that we will receive principal and interest payments according to the loan’s terms, or at all, or that we will be able to collect on the loan should we be compelled to enforce our remedies.
39
Second Lien Secured Loans. In structuring our loans, we may subordinate our security interest in certain assets of a borrower to another lender, usually a bank. In these situations, all of the risks identified above in Senior Secured Loans would be true and additional risks inherent in holding a junior security position would also be present.
Equity and Equity-Related Investments. When we invest in secured loans, we may acquire equity and equity-related securities as well. In addition, we may invest directly in the equity and equity-related securities of portfolio companies. The equity and equity-related interests we receive may not appreciate in value and may in fact decline in value. Accordingly, we may not be able to realize gains from our equity and equity- related interests, and any gains that we do realize on the disposition of any equity and equity-related interests may not be sufficient to offset any other losses we experience.
In addition, we have invested in and may in the future invest in or obtain significant exposure to “covenant-lite” loans. We use the term “covenant-lite” loans to refer generally to loans that do not have a complete set of financial maintenance covenants. Generally, covenant-lite loans provide borrower companies more freedom to negatively impact lenders because their covenants are incurrence-based, which means they are only tested and can only be breached following an affirmative action of the borrower, rather than by a deterioration in the borrower’s financial condition. Accordingly, because we invest in and have exposure to covenant-lite loans, we may have fewer rights against a borrower and may have a greater risk of loss on such investments as compared to investments in or exposure to loans with financial maintenance covenants.
Investing in small, fast-growing companies involves a high degree of risk, and our financial results may be affected adversely if one or more of our significant portfolio investments defaults on its loans or fails to perform as we expect.
Our portfolio will consist primarily of debt, equity and equity-related investments in small privately owned companies. Investing in these companies involves a number of significant risks. Typically, the debt in which we invest is not initially rated by any rating agency; however, we believe that if such investments were rated, they would be below investment grade. Securities rated below investment grade are often referred to as “high yield” securities and “junk bonds,” and are considered “high risk” and speculative in nature compared to debt instruments that are rated above investment grade. Compared to larger publicly owned companies, these companies may be in a weaker financial position and may experience wider variations in their operating results, which may make them more vulnerable to economic downturns. Typically, these companies need more capital to compete; however, their access to capital is limited and their cost of capital is often higher than that of their competitors. Our portfolio companies will face intense competition from larger companies with greater financial, technical, and marketing resources and their success typically depends on the managerial talents and efforts of an individual or a small group of persons. Therefore, the loss of any of its key employees could affect a portfolio company’s ability to compete effectively and harm its financial condition. Further, some of these companies will conduct business in regulated industries that are susceptible to regulatory changes. These factors could impair the cash flow of our portfolio companies and result in other events, such as bankruptcy. These events could limit a portfolio company’s ability to repay its obligations to us, which may have an adverse effect on the return on, or the recovery of, our investment in these businesses. Deterioration in a borrower’s financial condition and prospects may be accompanied by deterioration in the value of the loan’s collateral.
Many of these companies cannot obtain financing from public capital markets or from traditional credit sources, such as commercial banks. Accordingly, loans made to these types of companies pose a higher default risk than loans made to companies that have access to traditional credit sources.
We may be subject to risks associated with our investments in covenant-lite loans.
We have invested in and may in the future invest in or obtain significant exposure to covenant-lite loans, which means the obligations contain fewer maintenance covenants than other obligations, or no maintenance covenants, and may not include terms that allow the lender to monitor the financial performance of the borrower, including financial ratios, and declare a default if certain financial criteria are breached. While these loans may still contain other collateral protections, a covenant-lite loan may carry more risk than a covenant-heavy loan made by the same borrower as it does not require the borrower to provide affirmation that certain specific financial tests have been satisfied on a routine basis as is generally required under a covenant-heavy loan agreement. Generally, covenant-lite loans provide
40
borrowers more freedom to negatively impact lenders because their covenants, if any, tend to be incurrence-based, which means they are only tested and can only be breached following an affirmative action of the borrower, rather than by a deterioration in the borrower’s financial condition. Our investment in or exposure to a covenant-lite loan may potentially hinder our ability to reprice credit risk associated with the issuer and reduce our ability to restructure a problematic loan and mitigate potential loss. As a result, our exposure to losses may be increased, which could result in an adverse impact on our revenues, net income and net asset value.
We may be subject to risks associated with our investments in senior loans.
We invest in senior secured loans. Senior secured loans are usually rated below investment grade or may also be unrated. As a result, the risks associated with senior secured loans may be considered by credit rating agencies to be similar to the risks of below investment grade fixed income instruments, although senior secured loans are senior and secured in contrast to other below investment grade fixed income instruments, which are often subordinated or unsecured. Investment in senior secured loans rated below investment grade is considered speculative because of the credit risk of their issuers. Such companies are more likely than investment grade issuers to default on their payments of interest and principal owed to us, and such defaults could have a material adverse effect on our performance. An economic downturn would generally lead to a higher non-payment rate, and a senior secured loan may lose significant market value before a default occurs. Moreover, any specific collateral used to secure a senior secured loan may decline in value or become illiquid, which would adversely affect the senior secured loan’s value.
There may be less readily available and reliable information about most senior secured loans than is the case for many other types of securities, including securities issued in transactions registered under the Securities Act or registered under the Exchange Act. As a result, we will rely primarily on our own evaluation of a borrower’s credit quality rather than on any available independent sources. Therefore, we will be particularly dependent on the analytical abilities of our management team and investment professionals.
In general, the secondary trading market for senior secured loans is not well developed. No active trading market may exist for certain senior secured loans, which may make it difficult to value them. Illiquidity and adverse market conditions may mean that we may not be able to sell senior secured loans quickly or at a fair price. To the extent that a secondary market does exist for certain senior secured loans, the market for them may be subject to irregular trading activity, wide bid/ask spreads and extended trade settlement periods.
We may be subject to risks associated with our investments in junior debt securities.
We may invest in junior debt securities. Although certain junior debt securities are typically senior to common stock or other equity securities, the equity and debt securities in which we invest may be subordinated to substantial amounts of senior debt, all or a significant portion of which may be secured. Such subordinated investments may be characterized by greater credit risks than those associated with the senior obligations of the same issuer. These subordinated securities may not be protected by all of the financial covenants, such as limitations upon additional indebtedness, typically protecting such senior debt. Holders of junior debt generally are not entitled to receive full payments in bankruptcy or liquidation until senior creditors are paid in full. Holders of equity are not entitled to payments until all creditors are paid in full. In addition, the remedies available to holders of junior debt are normally limited by restrictions benefiting senior creditors. In the event any portfolio company cannot generate adequate cash flow to meet senior debt service, we may suffer a partial or total loss of capital invested.
Second priority liens on collateral securing loans that we make to our portfolio companies may be subject to control by senior creditors with first priority liens. If there is a default, the value of the collateral may not be sufficient to repay in full both the first priority creditors and us.
Certain loans that we make are secured by a second priority security interest in the same collateral pledged by a portfolio company to secure senior debt owed by the portfolio company to commercial banks or other traditional lenders. Often the senior lender has procured covenants from the portfolio company prohibiting the incurrence of additional secured debt without the senior lender’s consent. Prior to and as a condition of permitting the portfolio company to borrow money from us secured by the same collateral pledged to the senior lender, the senior lender will require assurances that it will control the disposition of any collateral in the event of bankruptcy or other default. In
41
many such cases, the senior lender will require us to enter into an intercreditor agreement prior to permitting the portfolio company to borrow from us. Typically the intercreditor agreements we will be requested to execute will expressly subordinate our debt instruments to those held by the senior lender and further provide that the senior lender shall control: (1) the commencement of foreclosure or other proceedings to liquidate and collect on the collateral; (2) the nature, timing, and conduct of foreclosure or other collection proceedings; (3) the amendment of any collateral document; (4) the release of the security interests in respect of any collateral; and (5) the waiver of defaults under any security agreement. Because of the control we may cede to senior lenders under intercreditor agreements we may enter, we may be unable to realize the proceeds of any collateral securing some of our loans.
If the assets securing the loans that we make decrease in value, then we may lack sufficient collateral to cover losses.
We believe that our borrowers generally are able to repay our loans from their available capital, future capital-raising transactions or current and/or future cash flow from operations. However, to attempt to mitigate credit risks, we typically take a secured collateral position. There is a risk that the collateral securing our secured loans may decrease in value over time, may be difficult to sell in a timely manner, may be difficult to appraise, may be liquidated at a price lower than what we consider to be fair value and may fluctuate in value based upon the success of the business and market conditions, including as a result of the inability of a borrower to raise additional capital.
In some circumstances, other creditors have claims having priority over our senior lien. Although for certain borrowers, we may be the only form of secured debt (other than potentially specific equipment financing), other borrowers may also have other senior secured debt, such as revolving loans and/or term loans, having priority over our senior lien. At the time of underwriting our loans, we generally only consider growth capital loans for prospective borrowers with sufficient collateral that covers the value of our loan as well as the revolving and/or term loans that may have priority over our senior lien; however, there may be instances in which we have incorrectly estimated the current or future potential value of the underlying collateral or the underlying collateral value has decreased, in which case our ability to recover our investment may be materially and adversely affected.
In addition, a substantial portion of the assets securing our investment may be in the form of intellectual property, inventory and equipment and, to a lesser extent, cash and accounts receivable. Intellectual property, if any, that is securing our loan could lose value if, among other things, the borrower’s rights to the intellectual property are challenged or if the borrower’s license to the intellectual property is revoked or expires. Inventory may not be adequate to secure our loan if our valuation of the inventory at the time that we made the loan was not accurate or if there is a reduction in the demand for the inventory.
Similarly, any equipment securing our loan may not provide us with the anticipated security if there are changes in technology or advances in new equipment that render the particular equipment obsolete or of limited value, or if the borrower fails to adequately maintain or repair the equipment. The residual value of the equipment at the time we would take possession may not be sufficient to satisfy the outstanding debt and we could experience a loss on the disposition of the equipment. Any one or more of the preceding factors could materially impair our ability to recover our investment in a foreclosure.
Our portfolio may be exposed in part to one or more specific industries, which may subject us to a risk of significant loss in a particular investment or investments if there is a downturn in that particular industry.
Our portfolio may be exposed in part to one or more specific industries. A downturn in any particular industry in which we are invested could significantly impact the aggregate returns we realize. If an industry in which we have significant investments suffers from adverse business or economic conditions, as these industries have to varying degrees, a material portion of our investment portfolio could be affected adversely, which, in turn, could adversely affect our financial position and results of operations.
42
Our investment portfolio’s concentration in technology-related companies is subject to many risks, including volatility, intense competition, shortened product life cycles, changes in regulatory and governmental programs and periodic downturns, and you could lose all or part of your investment.
As of December 31, 2020, investments in technology-related companies in the professional, scientific and technical services industry represented approximately 16.0% of the fair value of our investment portfolio, and many of these technology-related companies have narrow product lines and small market shares, which tend to render them more vulnerable to competitors’ actions and market conditions, as well as to general economic downturns. The revenues, income (or losses), and valuations of technology-related companies can and often do fluctuate suddenly and dramatically. In addition, technology-related industries are generally characterized by abrupt business cycles and intense competition. Overcapacity in technology- related industries, together with cyclical economic downturns, may result in substantial decreases in the market capitalization of many technology-related companies. Such decreases in market capitalization may occur again, and any future decreases in technology-related company valuations may be substantial and may not be temporary in nature. Therefore, our portfolio companies may face considerably more risk of loss than do companies in other industry sectors.
Because of rapid technological change, the average selling prices of products and some services provided by technology-related companies have historically decreased over their productive lives. As a result, the average selling prices of products and services offered by technology-related companies may decrease over time, which could adversely affect their operating results, their ability to meet obligations under their debt securities and the value of their equity securities. This could, in turn, materially adversely affect our business, financial condition and results of operations.
Investments that we may make in sustainable and renewable technology companies will be subject to substantial operational risks, such as underestimated cost projections, unanticipated operation and maintenance expenses, loss of government subsidies, and inability to deliver cost-effective alternative energy solutions compared to traditional energy products. In addition, sustainable and renewable technology companies employ a variety of means of increasing cash flow, including increasing utilization of existing facilities, expanding operations through new construction or acquisitions, or securing additional long-term contracts. Thus, some energy companies may be subject to construction risk, acquisition risk or other risks arising from their specific business strategies. Furthermore, production levels for solar, wind and other renewable energies may be dependent upon adequate sunlight, wind, or biogas production, which can vary from market to market and period to period, resulting in volatility in production levels and profitability. Demand for sustainable and renewable technology is also influenced by the available supply and prices for other energy products, such as coal, oil and natural gases. A change in prices in these energy products could reduce demand for alternative energy.
A disease pandemic or natural disaster may also impact investments that we may make in technology- related portfolio companies. The nature and level of natural disasters cannot be predicted and may be exacerbated by global climate change. A disease pandemic or major disaster, such as an earthquake, tsunami, flood or other catastrophic event could result in disruption to the business and operations of any such technology-related portfolio companies.
We may invest in technology-related companies that are reliant on U.S. and foreign regulatory and governmental programs. Any material changes or discontinuation, due to change in administration or U.S. Congress or otherwise could have a material adverse effect on the operations of a portfolio company in these industries and, in turn, impair our ability to timely collect principal and interest payments owed to us to the extent applicable.
We may invest in technology-related companies that do not have venture capital or private equity firms as equity investors, and these companies may entail a higher risk of loss than do companies with institutional equity investors, which could increase the risk of loss of your investment.
Our portfolio companies may require substantial additional equity financing to satisfy their continuing working capital and other cash requirements and, in most instances, to service the interest and principal payments on our investment. Portfolio companies that do not have venture capital or private equity investors may be unable to raise any additional capital to satisfy their obligations or to raise sufficient additional capital to reach the next stage of development. Portfolio companies that do not have venture capital or private equity investors may be less financially
43
sophisticated and may not have access to independent members to serve on their boards, which means that they may be less successful than portfolio companies sponsored by venture capital or private equity firms. Accordingly, financing these types of companies may entail a higher risk of loss than would financing companies that are sponsored by venture capital or private equity firms.
Our relationship with certain portfolio companies may expose us to our portfolio companies’ trade secrets and confidential information which may require us to be parties to non-disclosure agreements and restrict us from engaging in certain transactions.
Our relationship with some of our portfolio companies may expose us to our portfolio companies’ trade secrets and confidential information (including transactional data and personal data about their employees and clients) which may require us to be parties to non-disclosure agreements and restrict us from engaging in certain transactions. Unauthorized access or disclosure of such information may occur, resulting in theft, loss or other misappropriation. Any theft, loss, improper use, such as insider trading or other misappropriation of confidential information could have a material adverse impact on our competitive positions, our relationship with our portfolio companies and our reputation and could subject us to regulatory inquiries, enforcement and fines, civil litigation (which may cause us to incur significant expense or expose us to losses) and possible financial liability or costs.
Our investment portfolio’s concentration in the manufacturing industry is subject to various risks, including interruptions to the manufacturing process and costs of raw materials and energy, which may adversely affect our performance.
As of December 31, 2020, investments in the manufacturing industry represented approximately 20.2% of the fair value of our investment portfolio. Generally, our investments in the manufacturing industry are subject to various risks including safety or product liability issues, costs of raw materials and energy, including crude oil, and competition in global markets. The manufacturing industry is highly competitive, which puts pressure on prices. Prices are subject to international supply and demand as well as to the purchase costs of raw materials and energy. Markets for these products, as well as prices for raw materials and energy used by the manufacturing industry, are cyclical and volatile and the costs of raw materials and energy represent a substantial portion of the industry’s production costs and operating expenses. In addition, manufacturing facilities are subject to planned and unplanned production shutdowns, turnarounds and outages, which could have an adverse effect on long-term production. Companies in this industry are also subject to extensive federal, state, local and foreign environmental, health and safety laws and regulations concerning, among other things, emissions in the air, discharges to land and water and the generation, handling, treatment and disposal of hazardous waste and other materials. These requirements, and enforcement of these requirements, may become more stringent in the future. In addition, future regulatory or other developments could also restrict or eliminate the use of, or require manufacturing companies to make modifications to, their products, packaging, manufacturing processes and technology, which could have a significant adverse impact on its financial condition, results of operations and cash flows. Any of these interruptions to a manufacturing company in which we invest could adversely affect our performance.
Our investment portfolio’s concentration in the consumer and retail industry faces considerable uncertainties. Continued adverse changes in the economy may adversely affect consumer spending, which could negatively impact our business.
As of December 31, 2020, investments in the consumer and retail industry represented approximately 15.4% of the fair value of our investment portfolio. The consumer and retail industry is heavily dependent on discretionary consumer spending patterns. Our investments in the consumer and retail industry will be sensitive to numerous factors that affect discretionary consumer income, including adverse general economic conditions, changes in employment trends and levels of unemployment, increases in interest rates, weather, a significant rise in energy or food prices or other events or actions that may lead to a decrease in consumer confidence or a reduction in discretionary income. In addition, in a period of inflationary pricing, increased fuel costs may discourage customers from driving to retail locations, reducing store traffic and possibly sales. Declines in consumer spending, especially for extended periods, could have a material adverse effect on a portfolio company’s business, financial condition and results of operations. If a consumer and retail company in which we invest is unable to navigate these risks, our performance may be adversely affected.
44
Our investments in the life sciences industry are subject to various risks, including extensive government regulation, litigation risk and certain other risks particular to that industry, which may adversely affect the performance of such investments.
We may invest in companies in the life sciences industry that are subject to extensive regulation by the Food and Drug Administration and to a lesser extent, other federal, state and other foreign agencies. If any of these portfolio companies fail to comply with applicable regulations, they could be subject to significant penalties and claims that could materially and adversely affect their operations. Portfolio companies that produce medical devices or drugs are subject to the expense, delay and uncertainty of the regulatory approval process for their products and, even if approved, these products may not be accepted in the marketplace. In addition, governmental budgetary constraints effecting the regulatory approval process, new laws, regulations or judicial interpretations of existing laws and regulations might adversely affect a portfolio company in this industry. Portfolio companies in the life sciences industry may also have a limited number of suppliers of necessary components or a limited number of manufacturers for their products, and therefore face a risk of disruption to their manufacturing process if they are unable to find alternative suppliers when needed, including in response to any supply chain disruptions resulting from the COVID-19 pandemic. Any of these factors could materially and adversely affect the operations of a portfolio company in this industry and, in turn, impair our ability to timely collect principal and interest payments owed to us and consequently may adversely affect the performance of such investments.
The main industry sectors around which we intend to develop our investments are all capital intensive.
The industry sectors in which we make investments, technology, business services and industrial, are each capital intensive. Currently, financing for capital-intensive companies remains difficult. In some successful companies, we believe we may need to invest more than we currently have planned to invest in these companies. There can be no assurance that we will have the capital necessary to make such investments. In addition, investing greater than planned amounts in our portfolio companies could limit our ability to pursue new investments and fund follow-on investments. Both of these situations could cause us to miss investment opportunities or limit our ability to protect existing investments from dilution or other actions or events that would decrease the value and potential return from these investments.
The majority of our portfolio companies will need multiple rounds of additional financing to repay their debts to us and continue operations. Our portfolio companies may not be able to raise additional financing, which could harm our investment returns.
The majority of our portfolio companies will often require substantial additional equity financing to satisfy their continuing working capital and other cash requirements and, in most instances, to service the interest and principal payments on our investment. Each round of venture financing is typically intended to provide a company with only enough capital to reach the next stage of development. We cannot predict the circumstances or market conditions under which our portfolio companies will seek additional capital. It is possible that one or more of our portfolio companies will not be able to raise additional financing or may be able to do so only at a price or on terms unfavorable to us, either of which would negatively impact our investment returns. Some of these companies may be unable to obtain sufficient financing from private investors, public capital markets or traditional lenders. This may have a significant impact if the companies are unable to obtain certain federal, state or foreign agency approval for their products or the marketing thereof, of if regulatory review processes extend longer than anticipated, and the companies need continued funding for their operations during these times. Accordingly, financing these types of companies may entail a higher risk of loss than would financing companies that are able to utilize traditional credit sources.
If our portfolio companies are unable to commercialize their technologies, products, business concepts or services, the returns on our investments could be adversely affected.
The value of our investments in our portfolio companies may decline if they are not able to commercialize their technology, products, business concepts or services. Additionally, although some of our portfolio companies may already have a commercially successful product or product line at the time of our investment, information technology, e-commerce, life science, and energy technology-related products and services often have a more limited market or life
45
span than products in other industries. Thus, the ultimate success of these companies often depends on their ability to continually innovate in increasingly competitive markets. If they are unable to do so, our investment returns could be adversely affected and their ability to service their debt obligations to us over the term of the loan could be impaired. Our portfolio companies may be unable to acquire or develop any new products successfully, and the intellectual property they currently hold may not remain viable. Even if our portfolio companies are able to develop commercially viable products, the market for new products and services is highly competitive and rapidly changing. Neither our portfolio companies nor we will have any control over the pace of technology development. Commercial success is difficult to predict, and the marketing efforts of our portfolio companies may not be successful.
If our portfolio companies are unable to protect their intellectual property rights, our business and prospects could be harmed, and if portfolio companies are required to devote significant resources to protecting their intellectual property rights, the value of our investment could be reduced.
Our future success and competitive position will depend in part upon the ability of our portfolio companies to obtain, maintain and protect proprietary technology used in their products and services. Our portfolio companies will rely, in part, on patent, trade secret, and trademark law to protect that technology, but competitors may misappropriate their intellectual property, and disputes as to ownership of intellectual property may arise. Portfolio companies may, from time to time, be required to institute litigation to enforce their patents, copyrights, or other intellectual property rights; protect their trade secrets; determine the validity and scope of the proprietary rights of others; or defend against claims of infringement. Such litigation could result in substantial costs and diversion of resources. Similarly, if a portfolio company is found to infringe or misappropriate a third-party’s patent or other proprietary rights, it could be required to pay damages to the third-party, alter its products or processes, obtain a license from the third-party, and/or cease activities utilizing the proprietary rights, including making or selling products utilizing the proprietary rights. Any of the foregoing events could negatively affect both the portfolio company’s ability to service our debt investment and the value of any related debt and equity securities that we own, as well as any collateral securing our investment.
Loans may become nonperforming for a variety of reasons.
A loan or debt obligation may become non-performing for a variety of reasons. Such non-performing loans may require substantial workout negotiations or restructuring that may entail, among other things, a substantial reduction in the interest rate, a substantial write-down of the principal amount of the loan and/or the deferral of payments. In addition, such negotiations or restructuring may be quite extensive and protracted over time, and therefore may result in substantial uncertainty with respect to the ultimate recovery. We may also incur additional expenses to the extent that it is required to seek recovery upon a default on a loan or participate in the restructuring of such obligation. The liquidity for defaulted loans may be limited, and to the extent that defaulted loans are sold, it is highly unlikely that the proceeds from such sale will be equal to the amount of unpaid principal and interest thereon. In connection with any such defaults, workouts or restructuring, although we exercise voting rights with respect to an individual loan, we may not be able to exercise votes in respect of a sufficient percentage of voting rights with respect to such loan to determine the outcome of such vote.
The lack of liquidity in our investments may adversely affect our business.
All of our assets may be invested in illiquid securities, and a substantial portion of our investments in leveraged companies will be subject to legal and other restrictions on resale or will otherwise be less liquid than more broadly traded public securities. The illiquidity of these investments may make it difficult for us to sell such investments when desired. In addition, if we are required to liquidate all or a portion of our portfolio quickly, we may realize significantly less than the value at which we have previously recorded these investments. As a result, we do not expect to achieve liquidity in our investments in the near-term. However, to pay distributions to our stockholders and to maintain the election to be regulated as a BDC and qualify as a RIC, we may have to dispose of investments if we do not satisfy one or more of the applicable criteria under the respective regulatory frameworks. We may also face other restrictions on our ability to liquidate an investment in a portfolio company to the extent that we have material nonpublic information regarding such portfolio company.
46
Price declines and illiquidity in the corporate debt markets may adversely affect the fair value of our portfolio investments, reducing our net asset value through increased net unrealized depreciation.
As a BDC, we are required to carry our investments at market value or, if no market value is ascertainable, at fair value as determined in good faith by the Board. When an external event such as a purchase transaction, public offering or subsequent equity sale occurs, we use the pricing indicated by the external event to corroborate our valuation. We record decreases in the market values or fair values of our investments as unrealized depreciation. Declines in prices and liquidity in the corporate debt markets may result in significant net unrealized depreciation in our portfolio. The effect of all of these factors on our portfolio may reduce our net asset value by increasing net unrealized depreciation in our portfolio. Depending on market conditions, we could incur substantial realized losses and may suffer additional unrealized losses in future periods, which could have a material adverse effect on our business, financial condition and results of operations.
Our portfolio companies may prepay loans, which prepayment may reduce stated yields if capital returned cannot be invested in transactions with equal or greater expected yields.
The loans that will underlie our portfolio may be callable at any time, and many of them can be repaid with no premium to par. It is not clear at this time when or if any loan might be called. Whether a loan is called will depend both on the continued positive performance of the portfolio company and the existence of favorable financing market conditions that allow such company the ability to replace existing financing with less expensive capital. As market conditions change frequently, it is unknown when, and if, this may be possible for each portfolio company. Risks associated with owning loans include the fact that prepayments may occur at any time, sometimes without premium or penalty, and that the exercise of prepayment rights during periods of declining spreads could cause us to reinvest prepayment proceeds in lower-yielding instruments. In the case of some of these loans, having the loan called early may reduce our achievable yield if the capital returned cannot be invested in transactions with equal or greater expected yields, especially during periods of declining interest rates in the broader market, such in current market conditions.
To the extent original issue discount and payment-in-kind interest constitute a portion of our income, we will be exposed to typical risks associated with such income being required to be included in taxable and accounting income prior to receipt of cash representing such income.
Our investments may include original issue discount, or OID. To the extent original issue discount constitutes a portion of our income, we are exposed to typical risks associated with such income being required to be included in taxable and accounting income prior to receipt of cash, including the following:
• We must include in income each year a portion of the OID that accrues over the life of the obligation, regardless of whether cash representing such income is received by us in the same taxable year. Because any OID or other amounts accrued will be included in investment company taxable income for the year of the accrual, we may be required to make a distribution to our stockholders in order to satisfy our annual distribution requirements, even though we will not have received any corresponding cash amount. As a result, we may have to sell some of our investments at times or at prices that would not be advantageous to us, raise additional debt or equity capital or forgo new investment opportunities.
• The higher yield of OID instruments reflect the payment deferral and credit risk associated with these instruments.
• Even if the accounting conditions for income accrual are met, the borrower could still default when our actual collection is supposed to occur at the maturity of the obligation.
• OID instruments may have unreliable valuations because their continuing accruals require continuing judgments about the collectability of the deferred payments and the value of the collateral.
• OID instruments generally represent a significantly higher credit risk than coupon loans.
• OID income received by us may create uncertainty about the source of our cash distributions to stockholders. For accounting purposes, any cash distributions to stockholders representing OID or market
47
discount income are not treated as coming from paid-in capital, even though the cash to pay them comes from the offering proceeds. Thus, although a distribution of OID or market discount interest comes from the cash invested by the stockholders, Section 19(a) of the 1940 Act does not require that stockholders be given notice of this fact by reporting it as a return of capital.
We are a non-diversified investment company within the meaning of the 1940 Act, and therefore we are not limited by the 1940 Act with respect to the proportion of our assets that may be invested in securities of a single issuer.
We are classified as a non-diversified investment company within the meaning of the 1940 Act, which means that we are not limited by the 1940 Act with respect to the proportion of our assets that we may invest in securities of a single issuer. Our portfolio may be concentrated in a limited number of portfolio companies and industries. Beyond the asset diversification requirements associated with our qualification as a RIC under the Code, we do not have fixed guidelines for diversification. To the extent that we assume large positions in the securities of a small number of issuers, our net asset value may fluctuate to a greater extent than that of a diversified investment company as a result of changes in the financial condition or the market’s assessment of the issuer. We may also be more susceptible to any single economic or regulatory occurrence than a diversified investment company. As a result, the aggregate returns we realize may be significantly adversely affected if a small number of investments perform poorly or if we need to write down the value of any one investment. Additionally, while we are not targeting any specific industries, our investments may be concentrated in relatively few industries. As a result, a downturn in any particular industry in which we are invested could also significantly impact the aggregate returns we realize.
We may hold the debt securities of leveraged companies that may, due to the significant volatility of such companies, enter into bankruptcy proceedings.
Leveraged companies may experience bankruptcy or similar financial distress. The bankruptcy process has a number of significant inherent risks. Many events in a bankruptcy proceeding are the product of contested matters and adversary proceedings and are beyond the control of the creditors. A bankruptcy filing by a portfolio company may adversely and permanently affect the portfolio company. If the proceeding is converted to a liquidation, the value of the issuer may not equal the liquidation value that was believed to exist at the time of the investment. The duration of a bankruptcy proceeding is also difficult to predict, and a creditor’s return on investment can be adversely affected by delays until the plan of reorganization or liquidation ultimately becomes effective. The administrative costs in connection with a bankruptcy proceeding are frequently high and would be paid out of the debtor’s estate prior to any return to creditors. Because the standards for classification of claims under bankruptcy law are vague, our influence with respect to the class of securities or other obligations we own may be lost by increases in the number and amount of claims in the same class or by different classification and treatment. In the early stages of the bankruptcy process, it is often difficult to estimate the extent of, or even to identify, any contingent claims that might be made. In addition, certain claims that have priority by law (for example, claims for taxes) may be substantial.
Our failure to make follow-on investments in our portfolio companies could impair the value of our portfolio.
Following an initial investment in a portfolio company, we may make additional investments in that portfolio company as “follow-on” investments, in seeking to:
• increase or maintain in whole or in part our position as a creditor or equity ownership percentage in a portfolio company;
• exercise warrants, options or convertible securities that were acquired in the original or subsequent financing; or
• preserve or enhance the value of our investment.
We have discretion to make follow-on investments, subject to the availability of capital resources and the provisions of the 1940 Act. Failure on our part to make follow-on investments may, in some circumstances, jeopardize the continued viability of a portfolio company and our initial investment, or may result in a missed opportunity for us to increase our participation in a successful operation. Even if we have sufficient capital to make a desired follow-on investment, we may elect not to make a follow-on investment because we may not want to increase our level of risk,
48
because we prefer other opportunities or because we are inhibited by compliance with BDC requirements or the desire to maintain our RIC status.
Because we will not hold controlling equity interests in the majority of our portfolio companies, we may not be able to exercise control over our portfolio companies or prevent decisions by management of our portfolio companies, which could decrease the value of our investments.
We do not expect to hold controlling equity positions in the majority of our portfolio companies. Our debt investments may provide limited control features such as restrictions on the ability of a portfolio company to assume additional debt or to use the proceeds of our investment for other than certain specified purposes. “Control” under the 1940 Act is presumed at more than 25% equity ownership and may also be present at lower ownership levels where we provide managerial assistance. When we do not acquire a controlling equity position in a portfolio company, we may be subject to the risk that a portfolio company may make business decisions with which we disagree, and that the management and/or stockholders of a portfolio company may take risks or otherwise act in ways that are adverse to our interests. Due to the lack of liquidity of the debt and equity and equity-related investments that we typically hold in our portfolio companies, we may not be able to dispose of our investments in the event we disagree with the actions of a portfolio company and may therefore suffer a decrease in the value of our investments.
Defaults by our portfolio companies will harm our operating results.
A portfolio company’s failure to satisfy financial or operating covenants imposed by us or other lenders could lead to defaults and, potentially, termination of its loans and foreclosure on its assets. This could trigger cross-defaults under other agreements and jeopardize such portfolio company’s ability to meet its obligations under the debt or equity securities that we hold. We may incur expenses to the extent necessary to seek recovery upon default or to negotiate new terms, which may include the waiver of certain financial covenants, with a defaulting portfolio company. In addition, we have invested in and may in the future invest in or obtain significant exposure to “covenant-lite” loans. We use the term “covenant-lite” loans to refer generally to loans that do not have a complete set of financial maintenance covenants. Generally, covenant-lite loans provide borrower companies more freedom to negatively impact lenders because their covenants are incurrence-based, which means they are only tested and can only be breached following an affirmative action of the borrower, rather than by a deterioration in the borrower’s financial condition. Accordingly, because we invest in and have exposure to covenant-lite loans, we may have fewer rights against a borrower and may have a greater risk of loss on such investments as compared to investments in or exposure to loans with financial maintenance covenants.
Further, many of our investments will likely have a principal amount outstanding at maturity, which could result in a substantial loss to us if the borrower is unable to refinance or repay.
Our portfolio companies may incur debt that ranks equally with, or senior to, our investments in such companies.
Although our investments are primarily secured, some investments may be unsecured and subordinated to substantive amounts of senior indebtedness. The portfolio companies in which we invest usually have, or may be permitted to incur, other debt that ranks equally with, or senior to, the debt securities in which we invest. By their terms, such debt instruments may provide that the holders are entitled to receive payment of interest or principal on or before the dates on which we are entitled to receive payments in respect of the debt securities in which we invest. Also, in the event of insolvency, liquidation, dissolution, reorganization or bankruptcy of a portfolio company, holders of debt instruments ranking senior to our investment in that portfolio company would typically be entitled to receive payment in full before we receive any distribution in respect of our investment. After repaying senior creditors, the portfolio company may not have any remaining assets to use for repaying its obligation to us. In the case of debt ranking equally with debt securities in which we invest, we would have to share any distributions on an equal and ratable basis with other creditors holding such debt in the event of an insolvency, liquidation, dissolution, reorganization or bankruptcy of the relevant portfolio company.
Additionally, certain loans that we make to portfolio companies may be secured on a second-priority basis by the same collateral securing senior secured debt of such companies. The first-priority liens on the collateral will secure
49
the portfolio company’s obligations under any outstanding senior debt and may secure certain other future debt that may be permitted to be incurred by the portfolio company under the agreements governing the loans. The holders of obligations secured by first-priority liens on the collateral will generally control the liquidation of, and be entitled to receive proceeds from, any realization of the collateral to repay their obligations in full before us. In addition, the value of the collateral in the event of liquidation will depend on market and economic conditions, the availability of buyers and other factors. There can be no assurance that the proceeds, if any, from sales of all of the collateral would be sufficient to satisfy the loan obligations secured by the second-priority liens after payment in full of all obligations secured by the first-priority liens on the collateral. If such proceeds were not sufficient to repay amounts outstanding under the loan obligations secured by the second-priority liens, then, to the extent not repaid from the proceeds of the sale of the collateral, we will only have an unsecured claim against the portfolio company’s remaining assets, if any.
The rights we may have with respect to the collateral securing the loans we make to our portfolio companies with senior debt outstanding may also be limited pursuant to the terms of one or more intercreditor agreements that we enter into with the holders of such senior debt, including in unitranche transactions. Under a typical intercreditor agreement, at any time that obligations that have the benefit of the first-priority liens are outstanding, any of the following actions that may be taken in respect of the collateral will be at the direction of the holders of the obligations secured by the first-priority liens:
• the ability to cause the commencement of enforcement proceedings against the collateral;
• the ability to control the conduct of such proceedings;
• the approval of amendments to collateral documents;
• releases of liens on the collateral; and
• waivers of past defaults under collateral documents.
We may not have the ability to control or direct such actions, even if our rights are adversely affected. In addition, a bankruptcy court may choose not to enforce an intercreditor agreement or other agreement with creditors.
We may also make unsecured loans to portfolio companies, meaning that such loans will not benefit from any interest in collateral of such companies. Liens on such portfolio companies’ collateral, if any, will secure the portfolio company’s obligations under its outstanding secured debt and may secure certain future debt that is permitted to be incurred by the portfolio company under its secured loan agreements. The holders of obligations secured by such liens will generally control the liquidation of, and be entitled to receive proceeds from, any realization of such collateral to repay their obligations in full before us. In addition, the value of such collateral in the event of liquidation will depend on market and economic conditions, the availability of buyers and other factors. There can be no assurance that the proceeds, if any, from sales of such collateral would be sufficient to satisfy our unsecured loan obligations after payment in full of all secured loan obligations. If such proceeds were not sufficient to repay the outstanding secured loan obligations, then our unsecured claims would rank equally with the unpaid portion of such secured creditors’ claims against the portfolio company’s remaining assets, if any.
We may also make subordinated investments that rank below other obligations of the obligor in right of payment. Subordinated investments are generally more volatile than secured loans and are subject to greater risk of default than senior obligations as a result of adverse changes in the financial condition of the obligor or in general economic conditions. If we make a subordinated investment in a portfolio company, the portfolio company may be highly leveraged, and its relatively high loan-to-value ratio may create increased risks that its operations might not generate sufficient cash flow to service all of its debt obligations.
The disposition of our investments may result in contingent liabilities.
A significant portion of our investments may involve private securities. In connection with the disposition of an investment in private securities, we may be required to make representations about the business and financial affairs of the portfolio company typical of those made in connection with the sale of a business. We may also be required to
50
indemnify the purchasers of such investment to the extent that any such representations turn out to be inaccurate or with respect to potential liabilities. These arrangements may result in contingent liabilities that ultimately result in funding obligations that we must satisfy through our return of distributions previously made to us.
We may be subject to additional risks if we engage in hedging transactions and/or invest in foreign securities.
The 1940 Act generally requires that 70% of our investments be in issuers each of whom, in addition to other requirements, is organized under the laws of, and has its principal place of business in, any state of the United States, the District of Columbia, Puerto Rico, the Virgin Islands or any other possession of the United States. Our investment strategy does not contemplate a significant number of investments in securities of non-U.S. companies. We expect that these investments would focus on the same investments that we make in U.S. growth stage companies and, accordingly, would be complementary to our overall strategy and enhance the diversity of our holdings.
To the extent that these investments are denominated in a foreign currency, we may engage in hedging transactions. Engaging in either hedging transactions or investing in foreign securities would entail additional risks to our stockholders. We may, for example, use instruments such as interest rate swaps, caps, collars and floors, forward contracts or currency options or borrow under a credit facility in foreign currencies to minimize our foreign currency exposure. In each such case, we generally would seek to hedge against fluctuations of the relative values of our portfolio positions from changes in market interest rates or currency exchange rates. Hedging against a decline in the values of our portfolio positions would not eliminate the possibility of fluctuations in the values of such positions or prevent losses if the values of the positions declined. However, such hedging could establish other positions designed to gain from those same developments, thereby offsetting the decline in the value of such portfolio positions. Such hedging transactions could also limit the opportunity for gain if the values of the underlying portfolio positions increased. Moreover, it might not be possible to hedge against an exchange rate or interest rate fluctuation that was so generally anticipated that we would not be able to enter into a hedging transaction at an acceptable price.
While we may enter into such transactions to seek to reduce currency exchange rate and interest rate risks, unanticipated changes in currency exchange rates or interest rates could result in poorer overall investment performance than if we had not engaged in any such hedging transactions. In addition, the degree of correlation between price movements of the instruments used in a hedging strategy and price movements in the portfolio positions being hedged could vary. Moreover, for a variety of reasons, we might not seek to establish a perfect correlation between the hedging instruments and the portfolio holdings being hedged. Any such imperfect correlation could prevent us from achieving the intended hedge and expose us to risk of loss. In addition, it might not be possible to hedge fully or perfectly against currency fluctuations affecting the value of securities denominated in non-U.S. currencies because the value of those securities would likely fluctuate as a result of factors not related to currency fluctuations.
The new market structure applicable to derivatives imposed by the Dodd-Frank Act may affect our ability to use over-the-counter (“OTC”) derivatives for hedging purposes.
The Dodd-Frank Act enacted, and the U.S. Commodity Futures Trading Commission (“CFTC”) and SEC have issued or proposed rules to implement, both broad new regulatory requirements and broad new structural requirements applicable to OTC derivatives markets and, to a lesser extent, listed commodity futures (and futures options) markets. Similar changes are in the process of being implemented in other major financial markets.
Recent and anticipated regulatory changes require that certain types of OTC derivatives, including those that we may use for hedging activities, including interest rate and credit default swaps, be cleared and traded on regulated platforms, and these regulatory changes are expected to apply to foreign exchange transactions in the future. U.S. regulators have also adopted rules requiring us to post collateral with respect to cleared OTC derivatives and rules imposing margin requirements for OTC derivatives executed with registered swap dealers that are not cleared. The margin requirements for cleared and uncleared OTC derivatives may, in order to maintain our exemption from commodity pool operator (“CPO”) registration under the CFTC No-Action Letter 12-40, limit our ability to enter into hedging transactions or to obtain synthetic investment exposures, in either case adversely affecting our ability to
51
mitigate risk. Furthermore, any failure by us to fulfill any collateral requirement (e.g., a so-called “margin call”) may result in a default and could have a material adverse impact on our business, financial condition and results of operations.
The Dodd-Frank Act also imposed requirements relating to real-time public and regulatory reporting of OTC derivative transactions, enhanced documentation requirements, position limits on an expanded array of derivatives, and recordkeeping requirements. Taken as a whole, these changes could significantly increase the cost of using uncleared OTC derivatives to hedge risks, including interest rate and foreign exchange risk; reduce the level of exposure we are able to obtain for risk management purposes through OTC derivatives (including as the result of the CFTC imposing position limits on additional products); reduce the amounts available to us to make non-derivatives investments; impair liquidity in certain OTC derivatives; and adversely affect the quality of execution pricing obtained by us, all of which could adversely impact our investment returns.
We may not realize gains from our equity and equity-related investments.
We may in the future make investments that include warrants or other equity or equity-related securities. In addition, we may from time to time make non-control, equity co-investments in companies in conjunction with private equity sponsors. Our goal is ultimately to realize gains upon our disposition of such equity and equity-related interests. However, the equity and equity-related interests we receive may not appreciate in value and, in fact, may decline in value. Accordingly, we may not be able to realize gains from our equity and equity-related interests, and any gains that we do realize on the disposition of any equity and equity-related interests may not be sufficient to offset any other losses we experience. We also may be unable to realize any value if a portfolio company does not have a liquidity event, such as a sale of the business, recapitalization or public offering, which would allow us to sell the underlying equity interests. We often seek puts or similar rights to give us the right to sell our equity and equity-related securities back to the portfolio company issuer. We may be unable to exercise these put rights for the consideration provided in our investment documents if the issuer is in financial distress.
Our ability to enter into transactions involving derivatives and financial commitment transactions may be limited.
In November 2020, the SEC adopted a rulemaking regarding the ability of a BDC (or a registered investment company) to use derivatives and other transactions that create future payment or delivery obligations. Under the newly adopted rules, BDCs that use derivatives will be subject to a value-at-risk (“VaR”) leverage limit, certain other derivatives risk management program and testing requirements and requirements related to board reporting. These new requirements will apply unless the BDC qualifies as a “limited derivatives user,” under the adopted rules. Under the new rule, a BDC may enter into an unfunded commitment agreement that is not a derivatives transaction, such as an agreement to provide financing to a portfolio company, if the BDC has, among other things, a reasonable belief, at the time it enters into such an agreement, that it will have sufficient cash and cash equivalents to meet its obligations with respect to all of its unfunded commitment agreements, in each case as it becomes due. Collectively, these proposed requirements may limit our ability to use derivatives and/or enter into certain other financial contracts.
Risks Related to an Investment in Our Common Stock
We may not be able to pay distributions, our distributions may not grow over time and/or a portion of our distributions may be a return of capital.
We intend to pay distributions to our stockholders out of assets legally available for distribution. We cannot assure you that we will achieve investment results that will allow us to sustain a specified level of cash distributions or make periodic increases in cash distributions. Our ability to pay distributions might be adversely affected by, among other things, the impact of one or more of the risk factors described herein. If we declare a dividend, and if enough stockholders opt to receive cash distributions rather than participate in our distribution reinvestment plan, we may be forced to sell some of our investments in order to make cash dividend payments. In addition, the inability to satisfy the asset coverage test applicable to us as a BDC could limit our ability to pay distributions. All distributions will be paid at the discretion of the Board and will depend on our earnings, our financial condition, maintenance of our RIC status, compliance with applicable BDC regulations and such other factors as the Board may deem relevant from time to time. We cannot assure you that we will pay distributions to our stockholders.
52
When we make distributions, we will be required to determine the extent to which such distributions are paid out of current or accumulated earnings and profits. Distributions in excess of current and accumulated earnings and profits will be treated as a non-taxable return of capital to the extent of an investor’s basis in our stock and, assuming that an investor holds our stock as a capital asset, thereafter as a capital gain.
Investing in our common stock may involve an above-average degree of risk.
The investments we make in accordance with our investment objective may result in a higher amount of risk than alternative investment options and a higher risk of volatility or loss of principal. Our investments in portfolio companies may be highly speculative and aggressive and, therefore, an investment in our common stock may not be suitable for someone with lower risk tolerance.
Provisions of the Maryland General Corporation Law (the “MGCL”) and our Charter and Bylaws could deter takeover attempts and have an adverse effect on the price of our common stock.
The MGCL and our Charter and Bylaws contain provisions that may discourage, delay or make more difficult a change in control of us or the removal of our directors. We are subject to the Maryland Business Combination Act, subject to any applicable requirements of the 1940 Act. The Board has adopted a resolution exempting from the Maryland Business Combination Act any business combination between us and any other person, subject to prior approval of such business combination by the Board, including approval by a majority of our independent directors. If the resolution exempting business combinations is repealed or the Board does not approve a business combination, the Maryland Business Combination Act may discourage third parties from trying to acquire control of us and increase the difficulty of consummating such an offer. In addition, we may amend our Bylaws to be subject to the Maryland Control Share Acquisition Act, but only if the Board determines that it would be in our best interests, including in light of the Board’s fiduciary obligations, applicable federal and state laws, and the particular facts and circumstances surrounding the Board’s decision. If such conditions are met, and we amend our Bylaws to repeal the exemption from the Maryland Control Share Acquisition Act, the Maryland Control Share Acquisition Act also may make it more difficult for a third party to obtain control of us and increase the difficulty of consummating such a transaction.
We have adopted certain measures that may make it difficult for a third-party to obtain control of us, including provisions of our Charter classifying the Board in three staggered terms and authorizing the Board to classify or reclassify shares of our capital stock in one or more classes or series and to cause the issuance of additional shares of our stock. These provisions, as well as other provisions of our Charter and Bylaws, may delay, defer or prevent a transaction or a change in control that might otherwise be in the best interests of our stockholders.
Our Bylaws include an exclusive forum selection provision, which could limit our stockholders’ ability to obtain a favorable judicial forum for disputes with us or our directors, off icers or other agents.
Our Bylaws require that, unless we consent in writing to the selection of an alternative forum, the Circuit Court for Baltimore City (or, if that court does not have jurisdiction, the United States District Court for the District of Maryland, Northern Division) shall be the sole and exclusive forum for (i) any derivative action or proceeding brought on behalf of the Company (ii) any action asserting a claim of breach of any standard of conduct or legal duty owed by any of the Company’s director, officer or other agent to the Company or to its stockholders, (iii) any action asserting a claim arising pursuant to any provision of the MGCL or the Charter or the Bylaws (as either may be amended from time to time), or (iv) any action asserting a claim governed by the internal affairs doctrine.
This exclusive forum selection provision in our Bylaws will not apply to claims arising under the federal securities laws, including the Securities Act and the Exchange Act. There is uncertainty as to whether a court would enforce such a provision, and investors cannot waive compliance with the federal securities laws and the rules and regulations thereunder. In addition, this provision may increase costs for stockholders in bringing a claim against us or our directors, officers or other agents. Any investor purchasing or otherwise acquiring our shares is deemed to have notice of and consented to the foregoing provision.
53
The exclusive forum selection provision in our Bylaws may limit our stockholders’ ability to obtain a favorable judicial forum for disputes with us or our directors, officers or other agents, which may discourage lawsuits against us and such persons. It is also possible that, notwithstanding such exclusive forum selection provision, a court could rule that such provision is inapplicable or unenforceable. If this occurred, we may incur additional costs associated with resolving such action in another forum, which could materially adversely affect our business, financial condition and results of operations.
We cannot assure you that a market for our common stock will develop or, if one develops, that the market will continue, which would adversely affect the liquidity and price of our common stock.
Our common stock began trading on the Nasdaq Global Select Market under the symbol “TRIN” on January 29, 2021. We cannot assure you that an active trading market will develop for our common stock or, if one develops, that the trading market can be sustained. In addition, we cannot predict the prices at which our common stock will trade. Shares of closed-end investment companies, including BDCs, frequently trade at a discount from their net asset value and our stock may also be discounted in the market. This characteristic of closed-end investment companies is separate and distinct from the risk that our net asset value per share of common stock may decline. We cannot predict whether our common stock will trade at, above or below net asset value. In addition, if our common stock trades below its net asset value, we will generally not be able to sell additional shares of our common stock to the public at its market price without first obtaining the approval of a majority of our stockholders (including a majority of our unaffiliated stockholders) and our independent directors for such issuance.
A stockholder’s interest in us will be diluted if additional shares of our common stock are issued in the future, which could reduce the overall value of an investment in us.
Our stockholders do not have preemptive rights to purchase any shares we issue in the future. Our charter authorizes us to issue up to 200 million shares of common stock. Pursuant to our charter, a majority of our entire Board may amend our charter to increase the number of shares of common stock we may issue without stockholder approval. Our Board may elect to sell additional shares in the future or issue equity interests in private or public offerings. To the extent we issue additional equity interests at or below net asset value, your percentage ownership interest in us may be diluted. In addition, depending upon the terms and pricing of any future offerings and the value of our investments, you may also experience dilution in the book value and fair value of your shares.
Under the 1940 Act, we generally are prohibited from issuing or selling our common stock at a price below net asset value per share, which may be a disadvantage as compared with certain public companies. We may, however, sell our common stock, or warrants, options, or rights to acquire our common stock, at a price below the current net asset value of our common stock if our Board and independent directors determine that such sale is in our best interests and the best interests of our stockholders, and our stockholders, including a majority of those stockholders that are not affiliated with us, approve such sale. In any such case, the price at which our securities are to be issued and sold may not be less than a price that, in the determination of our Board, closely approximates the fair value of such securities (less any distributing commission or discount). If we raise additional funds by issuing common stock or senior securities convertible into, or exchangeable for, our common stock, then the percentage ownership of our stockholders at that time will decrease and you will experience dilution. Stockholders will experience dilution upon the conversion of some or all of the Convertible Notes into shares of our common stock. The existence of the Convertible Notes may also encourage short selling by market participants because the conversion of the Convertible Notes could depress the market price for our common stock.
Sales of substantial amounts of our common stock in the public market may have an adverse effect on the market price of our common stock.
Any future public resale of any shares of our common stock under the Common Stock Registration Rights Agreement and/or the Convertible Notes Registration Rights Agreement, and/or the expiration of applicable lock-up periods, subject to applicable securities laws, sales of substantial amounts of our common stock, or the perception that such sales could occur, could adversely affect the prevailing market prices for our common stock. If this occurs, it could impair our ability to raise additional capital through the sale of equity securities should we desire to do so. We
54
cannot predict what effect, if any, future sales of securities, or the availability of securities for future sales, will have on the market price of our common stock prevailing from time to time.
The market value of our common stock may fluctuate significantly.
The market value and liquidity, if any, of the market for shares of our common stock may be significantly affected by numerous factors, some of which are beyond our control and may not be directly related to our operating performance. These factors include:
• changes in the value of our portfolio of investments and derivative instruments as a result of changes in market factors, such as interest rate shifts, and also portfolio specific performance, such as portfolio company defaults, among other reasons;
• changes in regulatory policies or tax guidelines, particularly with respect to RICs or BDCs;
• loss of RIC or BDC status;
• distributions that exceed our net investment income and net income as reported according to GAAP;
• changes in earnings or variations in operating results;
• changes in accounting guidelines governing valuation of our investments;
• any shortfall in revenue or net income or any increase in losses from levels expected by investors;
• departure of key personnel;
• general economic trends and other external factors; and
• loss of a major funding source.
If we issue preferred stock or convertible debt securities, the net asset value of our common stock may become more volatile.
We cannot assure you that the issuance of preferred stock and/or convertible debt securities would result in a higher yield or return to the holders of our common stock. The issuance of preferred stock or convertible debt would likely cause the net asset value of our common stock to become more volatile. If the dividend rate on the preferred stock, or the interest rate on the convertible debt securities, were to approach the net rate of return on our investment portfolio, the benefit of such leverage to the holders of our common stock would be reduced. If the dividend rate on the preferred stock, or the interest rate on the convertible debt securities, were to exceed the net rate of return on our portfolio, the use of leverage would result in a lower rate of return to the holders of common stock than if we had not issued the preferred stock or convertible debt securities. Any decline in the net asset value of our investment would be borne entirely by the holders of our common stock. Therefore, if the market value of our portfolio were to decline, the leverage would result in a greater decrease in net asset value to the holders of our common stock than if we were not leveraged through the issuance of preferred stock or debt securities. This decline in net asset value would also tend to cause a greater decline in the market price, if any, for our common stock.
There is also a risk that, in the event of a sharp decline in the value of our net assets, we would be in danger of failing to maintain required asset coverage ratios, which may be required by the preferred stock or convertible debt, or our current investment income might not be sufficient to meet the dividend requirements on the preferred stock or the interest payments on the debt securities. In order to counteract such an event, we might need to liquidate investments in order to fund the redemption of some or all of the preferred stock or convertible debt. In addition, we would pay (and the holders of our common stock would bear) all costs and expenses relating to the issuance and ongoing maintenance of the preferred stock, debt securities, convertible debt, or any combination of these securities. Holders of preferred stock or convertible debt may have different interests than holders of common stock and may at times have disproportionate influence over our affairs.
Stockholders will experience dilution in their ownership percentage if they do not participate in our distribution reinvestment plan.
55
All distributions declared in cash payable to stockholders that are participants in our distribution reinvestment plan will generally be automatically reinvested in shares of our common stock if the investor does not elect to opt out of the plan. As a result, stockholders that opt out of our distribution reinvestment plan may experience dilution over time.
Stockholders may experience dilution in the net asset value of their shares if they do not participate in our distribution reinvestment plan and if our shares are trading at a discount to net asset value.
All distributions declared in cash payable to stockholders that are participants in our distribution reinvestment plan will generally be automatically reinvested in shares of our common stock if the investor does not elect to opt out of the plan. As a result, stockholders that opt out of our distribution reinvestment plan may experience accretion to the net asset value of their shares if our shares are trading at a premium to net asset value and dilution if our shares are trading at a discount to net asset value. The level of accretion or discount would depend on various factors, including the proportion of our stockholders who participate in the plan, the level of premium or discount at which our shares are trading and the amount of the distribution payable to stockholders.
Risks Related to the 2025 Notes
The 2025 Notes are unsecured and therefore are effectively subordinated to any secured indebtedness we have currently incurred or may incur in the future.
The 2025 Notes are not secured by any of our assets or any of the assets of our subsidiaries. As a result, the 2025 Notes are effectively subordinated, or junior, to any secured indebtedness or other obligations we or our subsidiaries have currently incurred, including the Credit Facility, and may incur in the future (or any indebtedness that is initially unsecured that we later secure) to the extent of the value of the assets securing such indebtedness. In any liquidation, dissolution, bankruptcy or other similar proceeding, the holders of any of our existing or future secured indebtedness and the secured indebtedness of our subsidiaries may assert rights against the assets pledged to secure that indebtedness in order to receive full payment of their indebtedness before the assets may be used to pay other creditors, including the holders of the 2025 Notes. Secured indebtedness is effectively senior to the 2025 Notes to the extent of the value of the assets securing such indebtedness.
The 2025 Notes are structurally subordinated to the indebtedness and other liabilities of our subsidiaries.
The 2025 Notes are obligations exclusively of us and not of any of our subsidiaries. None of our subsidiaries are a guarantor of the 2025 Notes and the 2025 Notes are not required to be guaranteed by any subsidiaries we may acquire or create in the future. Except to the extent we are a creditor with recognized claims against our subsidiaries, all claims of creditors (including trade creditors) and holders of preferred stock, if any, of our subsidiaries will have priority over our equity interests in such subsidiaries (and therefore the claims of our creditors, including holders of the 2025 Notes) with respect to the assets of such subsidiaries. Even if we are recognized as a creditor of one or more of our subsidiaries, our claims would still be effectively subordinated to any security interests in the assets of any such subsidiary and to any indebtedness or other liabilities of any such subsidiary senior to our claims. Consequently, the 2025 Notes will be structurally subordinated, or junior, to the Credit Facility and all existing and future indebtedness and other obligations (including trade payables) incurred by any of our subsidiaries, financing vehicles or similar facilities and any subsidiaries, financing vehicles or similar facilities that we may in the future acquire or establish.
The 2025 Notes Indenture contains limited protection for holders of the 2025 Notes.
The 2025 Notes Indenture (as defined in this annual report on Form 10-K) offers limited protection to holders of the 2025 Notes. The terms of the 2025 Notes Indenture and the 2025 Notes do not restrict our or any of our subsidiaries’ ability to engage in, or otherwise be a party to, a variety of corporate transactions, circumstances or events that could have an adverse impact on your investment in the 2025 Notes. In particular, the terms of the 2025 Notes Indenture and the 2025 Notes will not place any restrictions on our or our subsidiaries’ ability to:
56
• issue securities or otherwise incur additional indebtedness or other obligations, including (1) any indebtedness or other obligations that would be pari passu, or equal, in right of payment to the 2025 Notes, (2) any indebtedness or other obligations that would be secured and therefore rank effectively senior in right of payment to the 2025 Notes to the extent of the value of the assets securing such indebtedness, (3) indebtedness or other obligations of ours that are guaranteed by one or more of our subsidiaries and which therefore are structurally senior to the 2025 Notes and (4) securities, indebtedness or other obligations incurred by our subsidiaries that would be senior to our equity interests in our subsidiaries and therefore rank structurally senior to the 2025 Notes with respect to the assets of those subsidiaries, in each case other than an incurrence of indebtedness or other obligations that would cause a violation of Section 18(a)(1)(A) as modified by Section 61(a) of the 1940 Act or any successor provisions of the 1940 Act, but giving effect, in either case, to any exemptive relief granted to us by the SEC. Currently, these provisions generally prohibit us from incurring additional borrowings, including through the issuance of additional debt securities, unless our asset coverage, as defined in the 1940 Act, equals at least 150% after such borrowings;
• pay dividends on, or purchase or redeem or make any payments in respect of, capital stock or other securities ranking junior in right of payment to the 2025 Notes;
• sell assets (other than certain limited restrictions on our ability to consolidate, merge or sell all or substantially all of our assets);
• create liens (including liens on the shares of our subsidiaries) or enter into sale and leaseback transactions;
• enter into transactions with affiliates;
• make investments; or
• create restrictions on the payment of dividends or other amounts to us from our subsidiaries.
In addition, the 2025 Notes Indenture does not require us to offer to purchase the 2025 Notes in connection with a change of control or any other event. Furthermore, the terms of the 2025 Notes Indenture and the 2025 Notes do not protect holders of the 2025 Notes in the event that we experience changes (including significant adverse changes) in our financial condition, results of operations or credit ratings, as they do not require that we or our subsidiaries adhere to any financial tests or ratios or specified levels of net worth, revenues, income, cash flow, or liquidity.
Our ability to recapitalize, incur additional debt and take a number of other actions that are not limited by the terms of the 2025 Notes may have important consequences for you as a holder of the 2025 Notes, including making it more difficult for us to satisfy our obligations with respect to the 2025 Notes or negatively affecting the trading value of the 2025 Notes to the extent such a trading market develops for the 2025 Notes.
Certain of our current debt instruments include more protections for their holders than the 2025 Notes Indenture and the 2025 Notes. In addition, other debt we issue or incur in the future could contain more protections for its holders than the 2025 Notes Indenture and the 2025 Notes, including additional covenants and events of default. The issuance or incurrence of any such debt with incremental protections could affect the market for and trading levels and prices of the 2025 Notes to the extent such a market develops for the 2025 Notes.
If we default on our obligations to pay our other indebtedness, we may not be able to make payments on the
2025 Notes.
Any default under the agreements governing our indebtedness or under other indebtedness to which we may be a party, that is not waived by the required lenders or holders and the remedies sought by the holders of such indebtedness could make us unable to pay principal, premium, if any, and interest on the 2025 Notes and substantially decrease the market value of the 2025 Notes.
If we are unable to generate sufficient cash flow and are otherwise unable to obtain funds necessary to meet required payments of principal, premium, if any, and interest on our indebtedness, or if we otherwise fail to comply
57
with the various covenants, including financial and operating covenants, in the instruments governing our indebtedness, we could be in default under the terms of the agreements governing such indebtedness. In the event of such default, the holders of such indebtedness could elect to declare all the funds borrowed thereunder to be due and payable, together with accrued and unpaid interest, the lenders under our current indebtedness or other debt we may incur in the future could elect to terminate their commitments, cease making further loans and institute foreclosure proceedings against our assets, and we could be forced into bankruptcy or liquidation.
If our operating performance declines, we may in the future need to seek to obtain waivers from the required lenders or holders under the agreements governing our indebtedness, or other indebtedness that we may incur in the future, to avoid being in default. If we breach our covenants under the agreements governing our indebtedness and seek a waiver, we may not be able to obtain a waiver from the required lenders or holders. If this occurs, we would be in default and our lenders or debt holders could exercise their rights as described above, and we could be forced into bankruptcy or liquidation.
If we are unable to repay debt, lenders having secured obligations, including Credit Suisse under the Credit Facility, could proceed against the collateral securing the debt. Because the 2025 Notes Indenture has cross-acceleration provisions, and any future debt will likely have, customary cross-default and cross- acceleration provisions, if the indebtedness thereunder, hereunder or under any future credit facility is accelerated, we may be unable to repay or finance the amounts due.
The optional redemption provision may materially adversely affect a holder’s return on the 2025 Notes.
The 2025 Notes are redeemable in whole or in part at any time or from time to time on or after January 16, 2023 at our option. We may choose to redeem the 2025 Notes at times when prevailing interest rates are lower than the interest rate paid on the 2025 Notes. In this circumstance, you may not be able to reinvest the redemption proceeds in a comparable security at an effective interest rate as high as that of the 2025 Notes being redeemed.
A downgrade, suspension or withdrawal of the rating assigned by a rating agency to us and/or the 2025 Notes, if any, could cause the market value of the 2025 Notes to decline significantly.
Any credit ratings assigned to us and/or the 2025 Notes are an assessment by rating agencies of our ability to pay our obligations. Consequently, real or anticipated changes to any such credit ratings will generally affect the market value of the 2025 Notes. These credit ratings, however, may not reflect the potential impact of risks related to market conditions generally or other factors discussed herein that could impact the market value of the 2025 Notes.
Generally, rating agencies base their ratings on such material and information, and such of their own investigations, studies and assumptions, as they deem appropriate. Any such credit ratings should be evaluated independently from similar ratings of other securities or companies. Credit ratings are not a recommendation to buy, sell or hold any security, and may be subject to revision or withdrawal at any time by the issuing organization in its sole discretion. Neither we nor any rating agents undertake any obligation to maintain any credit ratings assigned to us and/or the 2025 Notes or to advise our stockholders or holders of the 2025 Notes of any changes to such credit ratings. There can be no assurance that any credit ratings assigned to us and/or the 2025 Notes will remain for any given period of time.
58
Risks Related to the Convertible Notes
The Convertible Notes are unsecured and therefore are effectively subordinated to any secured indebtedness currently outstanding or that may be incurred in the future and rank pari passu with, or equal to, all outstanding and future unsecured unsubordinated indebtedness issued by us and our general liabilities.
The Convertible Notes are not secured by any of our assets or any of the assets of any of our subsidiaries. As a result, the Convertible Notes are effectively subordinated to any outstanding secured indebtedness as of the date of this annual report on Form 10-K (including the Credit Facility) or that we or our subsidiaries may incur in the future (or any indebtedness that is initially unsecured as to which we subsequently grant a security interest) to the extent of the value of the assets securing such indebtedness. In any liquidation, dissolution, bankruptcy or other similar proceeding, the holders of any of our secured indebtedness or secured indebtedness of our subsidiaries may assert rights against the assets pledged to secure that indebtedness in order to receive full payment of their indebtedness before the assets may be used to pay other creditors, including the holders of the Convertible Notes. As of December 31, 2020, through of our wholly owned subsidiary, Trinity Funding 1, LLC, we had approximately $135 million of borrowings outstanding under the Credit Facility. The indebtedness under the Credit Facility is effectively senior to the Convertible Notes to the extent of the value of the assets securing such indebtedness. In addition, as of December 31, 2020, we had $125 million in aggregate principal amount of the 2025 Notes outstanding, which rank pari passu with the Convertible Notes.
The Convertible Notes are structurally subordinated to the indebtedness and other liabilities of our subsidiaries.
The Convertible Notes are obligations exclusively of Trinity Capital Inc., and not of any of our subsidiaries. None of our subsidiaries is a guarantor of the Convertible Notes, and the Convertible Notes are not required to be guaranteed by any subsidiary we may acquire or create in the future. Any assets of our subsidiaries will not be directly available to satisfy the claims of our creditors, including holders of the Convertible Notes. Except to the extent we are a creditor with recognized claims against our subsidiaries, all claims of creditors of our subsidiaries will have priority over our equity interests in such entities (and therefore the claims of our creditors, including holders of the Convertible Notes) with respect to the assets of such entities. Even if we are recognized as a creditor of one or more of these entities, our claims would still be effectively subordinated to any security interests in the assets of any such entity and to any indebtedness or other liabilities of any such entity senior to our claims. Consequently, the Convertible Notes are structurally subordinated to all indebtedness and other liabilities, including trade payables, of any of our existing or future subsidiaries. Certain of these entities serve as guarantors under the Credit Facility, and in the future our subsidiaries may incur substantial additional indebtedness, all of which is and would be structurally senior to the Convertible Notes.
The Convertible Notes Indenture contains limited protection for holders of the Convertible Notes.
The Convertible Notes Indenture offers limited protection to holders of the Convertible Notes. The terms of the Convertible Notes Indenture and the Convertible Notes do not restrict our or any of our subsidiaries’ ability to engage in, or otherwise be a party to, a variety of corporate transactions, circumstances or events that could have a material adverse impact on the holders’ investment in the Convertible Notes. In particular, the terms of the Convertible Notes Indenture and the Convertible Notes will not place any restrictions on our or our subsidiaries’ ability to:
• issue securities or otherwise incur additional indebtedness or other obligations, including (1) any indebtedness or other obligations that would be equal in right of payment to the Convertible Notes, (2) any indebtedness or other obligations that would be secured and therefore rank effectively senior in right of payment to the Convertible Notes to the extent of the values of the assets securing such debt, (3) indebtedness of ours that is guaranteed by one or more of our subsidiaries and which therefore is structurally senior to the Convertible Notes and (4) securities, indebtedness or obligations issued or incurred by our subsidiaries that would be senior to our equity interests in those entities and therefore rank structurally senior to the Convertible Notes with respect to the assets of our subsidiaries, in each case other than an incurrence of indebtedness or other obligation that would cause a violation of Section 18(a)(1)(A) as modified by such provisions of Section 61(a) of the 1940 Act as may be applicable to us
59
from time to time or any successor provisions, whether or not we continue to be subject to such provisions of the 1940 Act, but giving effect, in each case, to any exemptive relief granted to us by the SEC. Currently, these provisions generally prohibit us from making additional borrowings, including through the issuance of additional debt or the sale of additional debt securities, unless our asset coverage, as defined in the 1940 Act, equals at least 150%;
• pay dividends on, or purchase or redeem or make any payments in respect of, capital stock or other securities ranking junior in right of payment to the Convertible Notes;
• sell assets (other than certain limited restrictions on our ability to consolidate, merge or sell all or substantially all of our assets);
• enter into transactions with affiliates;
• create liens (including liens on the shares of our subsidiaries) or enter into sale and leaseback transactions;
• make investments; or
• create restrictions on the payment of dividends or other amounts to us from our subsidiaries.
Furthermore, the terms of the Convertible Notes Indenture and the Convertible Notes do not protect holders of the Convertible Notes in the event that we experience changes (including significant adverse changes) in our financial condition, results of operations or credit ratings, if any, as they do not require that we or our subsidiaries adhere to any financial tests or ratios or specified levels of net worth, revenues, income, cash flow, or liquidity.
Our ability to recapitalize, incur additional debt (including additional debt that matures prior to the maturity of the Convertible Notes), and take a number of other actions that are not limited by the terms of the Convertible Notes may have important consequences for holders of the Convertible Notes, including making it more difficult for us to satisfy our obligations with respect to the Convertible Notes or negatively affecting the trading value of the Convertible Notes.
Other debt we issue or incur in the future could contain more protections for its holders than the Convertible Notes Indenture and the Convertible Notes, including additional covenants and events of default. The issuance or incurrence of any such debt with incremental protections could affect the market for, trading levels, and prices of the Convertible Notes.
If we default on our obligations to pay our other indebtedness, we may not be able to make payments on the
Convertible Notes.
Any default under the agreements governing our indebtedness or under other indebtedness to which we may be a party, that is not waived by the required lenders or holders and the remedies sought by the holders of such indebtedness could make us unable to pay principal, premium, if any, and interest on the Convertible Notes and substantially decrease the market value of the Convertible Notes.
If we are unable to generate sufficient cash flow and are otherwise unable to obtain funds necessary to meet required payments of principal, premium, if any, and interest on our indebtedness, or if we otherwise fail to comply with the various covenants, including financial and operating covenants, in the instruments governing our indebtedness, we could be in default under the terms of the agreements governing such indebtedness. In the event of such default, the holders of such indebtedness could elect to declare all the funds borrowed thereunder to be due and payable, together with accrued and unpaid interest, the lenders under our current indebtedness or other debt we may incur in the future could elect to terminate their commitments, cease making further loans and institute foreclosure proceedings against our assets, and we could be forced into bankruptcy or liquidation.
If our operating performance declines, we may in the future need to seek to obtain waivers from the required lenders or holders under the agreements governing our indebtedness, or other indebtedness that we may incur in the future, to avoid being in default. If we breach our covenants under the agreements governing our indebtedness
60
and seek a waiver, we may not be able to obtain a waiver from the required lenders or holders. If this occurs, we would be in default and our lenders or debt holders could exercise their rights as described above, and we could be forced into bankruptcy or liquidation.
If we are unable to repay debt, lenders having secured obligations, including Credit Suisse under the Credit Facility, could proceed against the collateral securing the debt. Because the Convertible Notes Indenture will have, and any future debt will likely have, customary cross-default provisions, if the indebtedness thereunder, hereunder or under any future credit facility is accelerated, we may be unable to repay or finance the amounts due.
We may not have, or have the ability to raise, the funds necessary to purchase the Convertible Notes as required upon a fundamental change, and our future debt may contain limitations on our ability to deliver shares of our common stock upon conversion or purchase of the Convertible Notes.
Holders of the Convertible Notes will have the right to require us to purchase their Convertible Notes for cash upon the occurrence of a fundamental change at a purchase price equal to 100% of their principal amount, plus accrued and unpaid interest, if any. As defined in the Convertible Notes Indenture, a fundamental change means the occurrence of either a change in control or, after the initial listing of our common stock on a national securities exchange, the termination of trading of our common stock on any such exchange. We may not have enough available cash or be able to obtain financing at the time we are required to make purchases of Convertible Notes surrendered therefor. In addition, our ability to purchase the Convertible Notes or to deliver shares of our common stock upon conversions of the Convertible Notes may be limited by law, by regulatory authority or by agreements governing our indebtedness. Our failure to purchase Convertible Notes at a time when the purchase is required by the Convertible Notes Indenture or deliver any shares of our common stock upon future conversions of the Convertible Notes as required by the Convertible Notes Indenture would constitute a default under the Convertible Notes Indenture. A default under the Convertible Notes Indenture or the fundamental change itself could also lead to a default under the Credit Facility and/or the 2025 Notes Indenture. If the repayment of the related indebtedness were to be accelerated after any applicable notice or grace periods, we may not have sufficient funds to repay the indebtedness and purchase the Convertible Notes.
The conversion rate of the Convertible Notes may not be adjusted for all dilutive events.
The conversion rate of the Convertible Notes is subject to adjustment upon certain events, including the issuance of certain stock dividends on our common stock, certain issuance of rights or warrants subdivisions, combinations, certain distributions of capital stock, indebtedness or assets, certain cash dividends and certain issuer tender or exchange offers. However, the conversion rate will not be adjusted for other events, such as a third-party tender or exchange offer or an issuance of common stock for cash, that may adversely affect the trading price of the Convertible Notes or the common stock. An event that adversely affects the value of the Convertible Notes may occur, and that event may not result in an adjustment to the conversion rate.
The forced conversion provision may materially adversely affect the holders’ return on the Convertible Notes.
At our option, we may cause the holders to convert all or a portion of the then outstanding principal amount of the Convertible Notes plus accrued but unpaid interest, but excluding the date of such conversion, at any time on or prior to the close of business on the business day immediately preceding the maturity date, if, following the listing of our common stock on a national securities exchange, the closing sale price of our common stock on such national securities exchange for any 30 consecutive trading days exceeds 120% of the conversion price, as may be adjusted. Upon such conversion, we will pay or deliver, as the case may be, cash, shares of our common stock or a combination of cash and shares of our common stock, at our election, per $1,000 principal amount of the Convertible Notes, equal to the conversion rate, and a forced conversion make-whole payment, if any, in cash, as described Convertible Notes Indenture. In this circumstance, the holders may not be able to reinvest the proceeds therefrom in a comparable security at an effective interest rate as high as that of the Convertible Notes.
61
There is currently no public market for the Convertible Notes, and an active trading market may not develop for the Convertible Notes. The failure of a market to develop for the Convertible Notes could adversely affect the liquidity and value of the Convertible Notes.
The Convertible Notes are a new issue of securities, and there is no existing market for the Convertible Notes. We do not intend to apply for listing of the Convertible Notes on any securities exchange or for quotation of the Convertible Notes on any automated dealer quotation system. A market may not develop for the Convertible Notes, and there can be no assurance as to the liquidity of any market that may develop for the Convertible Notes. If an active, liquid market does not develop for the Convertible Notes, the market price and liquidity of the Convertible Notes may be adversely affected. If any of the Convertible Notes are traded after their initial issuance, they may trade at a discount from their initial offering price.
The liquidity of the trading market, if any, and future trading prices of the Convertible Notes will depend on many factors, including, among other things, the price of our common stock, prevailing interest rates, our operating results, financial performance and prospects, the market for similar securities and the overall securities market, and may be adversely affected by unfavorable changes in these factors. Historically, the market for convertible debt has been subject to disruptions that have caused volatility in prices. It is possible that the market for the Convertible Notes will be subject to disruptions that may have a negative effect on the holders of the Convertible Notes, regardless of our operating results, financial performance or prospects.
We have agreed to file a resale registration statement for the Convertible Notes. Under the Convertible Notes Registration Rights Agreement, we are required to register the resale of the Convertible Notes under the Securities Act. Until such a registration statement has been declared effective, holders of the Convertible Notes may not offer or sell the Convertible Notes except pursuant to an exemption from, or in a transaction not subject to, the registration requirements of the Securities Act and applicable state securities laws or pursuant to an effective registration statement. The SEC, however, has broad discretion to determine whether any registration statement will be declared effective and may delay or deny the effectiveness of any such registration statement filed by us for a variety of reasons. Our ability to have declared effective by the SEC a registration statement pertaining to the resale of the Convertible Notes on a timely basis will depend upon our ability to resolve any issues that may be raised by the SEC. No assurance can be given as to when a registration statement with respect to the Convertible Notes will become effective. Failure to have the registration statement become effective could adversely affect the liquidity and price of the Convertible Notes.
The Convertible Notes may bear the restricted legend indefinitely if we issue additional Convertible Notes.
The Convertible Notes Indenture will allow us to issue additional Convertible Notes in the future on the same terms and conditions as the Convertible Notes offered hereby, except for any differences in the issue price and interest accrued prior to the issue date of the additional Convertible Notes; provided that if any such additional notes are not fungible with the Convertible Notes initially offered hereby for U.S. federal income tax purposes, those additional notes will have a separate CUSIP number. Subject to certain exceptions, the Convertible Notes Indenture will provide that the Convertible Notes and any shares of common stock issued upon conversion of the Convertible Notes will bear a restricted securities legend until the date that is one year after the later of last date of original issuance of the Convertible Notes or the last day of issuance of any additional Convertible Notes, or such later date, if any, as may be required by applicable law. We may, but are not required to, remove the restricted securities legend from any global Convertible Notes promptly after such date. However, because the issuance of any additional Convertible Notes would cause such date to be delayed beyond one year after the last date of original issuance of the Convertible Notes offered hereby, any additional Convertible Notes that we issue at a later date will cause the removal of the restricted legend, if at all, to be delayed beyond such date. As a result of the foregoing, your ability to resell in the public market the Convertible Notes and common stock issuable upon conversion of the Convertible Notes may be delayed, which may adversely affect the size of the market for these securities and pricing on re-sales.
62
The accounting for convertible debt securities is subject to uncertainty.
The accounting for convertible debt securities is subject to frequent scrutiny by the accounting regulatory bodies and is subject to change. We cannot predict if or when any such change could be made and any such change could have an adverse impact on our reported or future financial results. Any such impacts could adversely affect the market price of our common stock and in turn negatively impact the market price of the Convertible Notes.
The market value of our common stock and of the Convertible Notes may fluctuate significantly, and this may make it difficult for holders to resell the Convertible Notes or common stock issued upon conversion of the Convertible Notes when holders want or at prices holders find attractive.
There is currently no public market for the Convertible Notes or our common stock and there can be no assurance that a market for the Convertible Notes or our common stock will develop. In addition, the market value and liquidity, if any, of the market for the Convertible Notes or our common stock may be significantly affected by numerous factors, some of which are beyond our control and may not be directly related to our operating performance. In addition, because the Convertible Notes are convertible into our common stock, volatility or depressed prices for our common stock could have a similar effect on the trading price of the Convertible Notes. These factors include:
• changes in the value of our portfolio of investments and derivative instruments as a result of changes in market factors, such as interest rate shifts, and also portfolio specific performance, such as portfolio company defaults, among other reasons;
• changes in regulatory policies or tax guidelines, particularly with respect to RICs or BDCs;
• loss of RIC or BDC status;
• distributions that exceed our net investment income and net income as reported according to GAAP;
• changes in earnings or variations in operating results;
• changes in accounting guidelines governing valuation of our investments;
• any shortfall in revenue or net income or any increase in losses from levels expected by investors;
• departure of key personnel;
• general economic trends and other external factors; and
• loss of a major funding source.
Under the Convertible Notes Registration Rights Agreement, we have agreed to file a resale registration statement for the Convertible Notes and any shares of common stock to be issued upon conversion of the Convertible Notes. Under the Convertible Notes Registration Rights Agreement, we are required to register the resale of the Convertible Notes and such shares under the Securities Act. Until any such resale registration statement has been declared effective, holders of the Convertible Notes and such shares may not offer or sell the Convertible Notes and such shares except pursuant to an exemption from, or in a transaction not subject to, the registration requirements of the Securities Act and applicable state securities laws or pursuant to an effective registration statement. The SEC, however, has broad discretion to determine whether any registration statement will be declared effective and may delay or deny the effectiveness of any such resale registration statement filed by us for a variety of reasons. Our ability to have declared effective by the SEC a registration statement pertaining to the resale of the Convertible Notes and/or any shares of common stock to be issued upon conversion of the Convertible Notes on a timely basis will depend upon our ability to resolve any issues that may be raised by the SEC. No assurance can be given as to when any such resale registration statement with respect to the Convertible Notes and/or any shares of common stock to be issued upon conversion of the Convertible Notes will become effective. Failure to have any such resale registration statement become effective could adversely affect the liquidity and price of the Convertible Notes and/or any shares of common stock issued upon conversion of the Convertible Notes, as applicable.
63
Future sales of our common stock in the public market or the issuance of securities senior to our common stock could adversely affect the trading price of our common stock and the value of the Convertible Notes and our ability to raise funds in new stock offerings.
Future sales of substantial amounts of our common stock or equity-related securities in the public market, or the perception that such sales could occur, could adversely affect the prevailing market value of our common stock and the value of the Convertible Notes and could impair our ability to raise capital through future offerings of our securities, should we decide to offer them. No prediction can be made as to the effect that future sales of shares of common stock, or the availability of shares of common stock for future sale, will have on the trading price of our common stock or the value of the Convertible Notes.
Holders of the Convertible Notes will not be entitled to any rights with respect to our common stock, but will be subject to all changes made with respect to our common stock.
Holders of the Convertible Notes will not be entitled to any rights with respect to our common stock (including, without limitation, voting rights or rights to receive any dividends or other distributions on our common stock), but will be subject to all changes affecting our common stock. Holders will only be entitled to rights in respect of our common stock if and when we deliver shares of our common stock upon conversion for their Convertible Notes and, to a limited extent, under the conversion rate adjustments applicable to the Convertible Notes. For example, in the event that an amendment is proposed to our charter or bylaws requiring stockholder approval and the record date for determining the stockholders of record entitled to vote on the amendment occurs prior to a holder’s conversion of Convertible Notes, the holder will not be entitled to vote on the amendment, although the holder will nevertheless be subject to any changes in the powers, preferences or rights of our common stock that result from such amendment.
Upon conversion of the Convertible Notes, holders may receive less valuable consideration than expected because the market value or net asset value per share of our common stock may decline after holders exercise their conversion right but before we settle our conversion obligation.
Under the Convertible Notes, a converting holder may be exposed to fluctuations in the market value or net asset value per share of our common stock during the period from the date such holder surrenders its Convertible Notes for conversion until the date we settle our conversion obligation.
Because we may satisfy our conversion obligation solely in shares of our common stock upon conversion of the Convertible Notes, under such circumstances we will deliver shares of our common stock, together with cash for any fractional share, on the second business day following the relevant conversion date. Accordingly, if the market value or net asset value per share of our common stock decreases during this period, the market value of the shares of our common stock that holders receive will be adversely affected and would be less than the conversion value of the Convertible Notes on the conversion date.
The adjustment to the conversion rate for Convertible Notes converted in connection with a make-whole adjustment event may not adequately compensate holders for any lost value of their Convertible Notes as a result of such transaction.
Following a make-whole adjustment event, if a holder elects to convert its Convertible Notes in connection with such corporate transaction, we will increase the conversion rate by an additional number of shares of our common stock upon conversion in certain circumstances. As defined in the Convertible Notes Indenture, a make-whole adjustment event means any change of control and any termination of trading of our common stock on any national securities exchange. The increase in the conversion rate will be determined based on the date on which the make-whole adjustment event occurs or becomes effective and the price paid (or deemed to be paid) per share of our common stock in the make-whole adjustment event, as described in the Convertible Notes Indenture. The adjustment to the conversion rate for Convertible Notes converted in connection with a make-whole adjustment event may not adequately compensate holders for any lost value of their Convertible Notes as a result of such transaction. In addition, if the price paid (or deemed to be paid) per share of our common stock in the make-whole adjustment event is greater than $20.00 per share or less than $13.01 per share (in each case, subject to adjustment), no increase in the conversion rate will be made. Moreover, in no event will the conversion rate per $1,000 principal amount of
64
Convertible Notes exceed the maximum conversion rate described further in the Convertible Notes Indenture, which is subject to adjustment as described in such section.
Our obligation to increase the conversion rate upon the occurrence of a make-whole adjustment event could be considered a penalty, in which case the enforceability thereof would be subject to general principles of reasonableness of economic remedies.
Some significant restructuring transactions may not constitute a fundamental change, in which case we would not be obligated to offer to purchase the Convertible Notes.
Upon the occurrence of a fundamental change, holders have the right to require us to purchase their Convertible Notes. However, the fundamental change provisions will not afford protection to holders in the event of other transactions that could adversely affect the Convertible Notes. For example, transactions such as leveraged recapitalizations, refinancings, restructurings, or acquisitions initiated by us may not constitute a fundamental change requiring us to repurchase the Convertible Notes. In addition, holders may not be entitled to require us to purchase their Convertible Notes upon a fundamental change in certain circumstances involving a significant change in the composition of our Board, or in connection with a proxy contest where our Board does not endorse a dissident slate of directors but approves them for purposes of the definition of “continuing directors” as set forth in the Convertible Notes Indenture. In the event of any such transaction, the holders would not have the right to require us to purchase their Convertible Notes, even though each of these transactions could increase the amount of our indebtedness, or otherwise adversely affect our capital structure or any credit ratings, thereby adversely affecting the holders.
Provisions of the Convertible Notes could discourage an acquisition of us by a third party.
Certain provisions of the Convertible Notes could make it more difficult or more expensive for a third party to acquire us. Upon the occurrence of certain transactions constituting a fundamental change, holders of the Convertible Notes will have the right, at their option, to require us to purchase for cash all of their Convertible Notes or any portion of the principal amount of such Convertible Notes in integral multiples of $1,000. We may also be required to increase the conversion rate in the event of certain transactions constituting a make-whole adjustment event. These provisions could discourage an acquisition of us by a third party.
A downgrade, suspension or withdrawal of the rating assigned by a rating agency to us and/or the Convertible Notes, if any, could cause the market value of the Convertible Notes to decline significantly.
Any credit ratings assigned to us and/or the Convertible Notes are an assessment by rating agencies of our ability to pay our obligations. Consequently, real or anticipated changes to any such credit ratings will generally affect the market value of the Convertible Notes. These credit ratings, however, may not reflect the potential impact of risks related to market conditions generally or other factors discussed herein that could impact the market value of the Convertible Notes.
If an investment grade rating is not maintained with respect to the Convertible Notes, additional interest of 0.75% per annum will accrue on the Convertible Notes until such time as the Convertible Notes have received an investment grade rating of “BBB-” (or its equivalent) or better. An explanation of the significance of a credit rating may be obtained from the rating agency. Generally, rating agencies base their ratings on such material and information, and such of their own investigations, studies and assumptions, as they deem appropriate. A credit rating should be evaluated independently from similar ratings of other securities or companies. A credit rating is not a recommendation to buy, sell or hold securities and may be subject to revision or withdrawal at any time. There can be no assurance that a credit rating will remain for any given period of time.
Conversions of the Convertible Notes will dilute the ownership interest of our existing stockholders, including holders who had previously converted their Convertible Notes, if shares of our common stock are issued upon conversions of the Convertible Notes.
The conversion of some or all of the Convertible Notes into shares of our common stock will dilute the ownership interests of our existing stockholders. Any sales of our common stock issuable upon such conversion
65
could adversely affect prevailing market prices of our common stock. In addition, the existence of the Convertible Notes may encourage short selling by market participants because the conversion of the Convertible Notes could depress the market price of our common stock.
If the Convertible feature of the Convertible Notes is deemed to be greater than incidental and investment in the Convertible Notes by Benefit Plan Investors is “significant” within the Plan Asset Regulation, we could be subject to ERISA fiduciary duties and other provisions of ERISA.
Under certain circumstances, our underling assets could be treated as “plan assets” of employee benefit plans subject to the Employee Retirement Income Security Act of 1974, as amended (“ERISA”) or section 4975 of the Code (“Benefit Plan Investors”). This could occur if the convertibility feature of the Convertible Notes were to be treated as greater than “incidental,” and, as such, the Convertible Notes were deemed to be equity under the ERISA’s plan asset regulation (DOL Reg. section 2510.3-101 as modified by Section 3(42) of ERISA, the “Plan Asset Regulation”). If investment by Benefit Plan Investors in the Convertible Notes is “significant” and the Convertible Notes were deemed equity interests, in each case under the Plan Asset Regulation and an exception to the Plan Asset Regulation did not apply, we and our management would be subject to ERISA fiduciary duties and certain transactions we might enter into, or may have entered into, in the ordinary course of our business might constitute non-exempt “prohibited transactions” under section 406 of ERISA or section 4975 of the Code and might have to be rescinded at significant cost to us.
If the Convertible Notes are issued with original issue discount and a bankruptcy petition were filed by or against us, holders of the Convertible Notes may receive a lesser amount for their claim than they would have been entitled to receive under the Convertible Notes Indenture.
If the Convertible Notes are issued with original issue discount and a bankruptcy petition were filed by or against us under the United States Bankruptcy Code after the issuance of the Convertible Notes, the claim by any holder of the Convertible Notes for the principal amount of the Convertible Notes may be limited to an amount equal to the sum of: the original issue price for the Convertible Notes and that portion of any original issue discount that does not constitute “unmatured interest” for purposes of the United States Bankruptcy Code.
Any original issue discount that was not amortized as of the date of the bankruptcy filing would constitute unmatured interest. Accordingly, holders of the Convertible Notes under these circumstances may receive a lesser amount than they would be entitled to under the terms of the Convertible Notes Indenture, even if sufficient funds are available.
Holders may be subject to tax if we make or fail to make certain adjustments to the conversion rate of the Convertible Notes, even though the holders did not receive a corresponding cash distribution.
The conversion rate of the Convertible Notes is subject to adjustment in certain circumstances, including the payment of cash dividends. If the conversion rate is adjusted as a result of a distribution that is taxable to our common stockholders, such as a cash dividend, a holder may be deemed to have received a dividend subject to U.S. federal income tax without the receipt of any cash. In addition, a failure to adjust (or to adjust adequately) the conversion rate after an event that increases a holder’s proportionate interest in us could be treated as a deemed taxable dividend to the holder. If a make-whole adjustment event occurs on or prior to the business day immediately preceding the stated maturity date of the Convertible Notes, under some circumstances, we will increase the conversion rate for the Convertible Notes converted in connection with the make-whole adjustment event. Such increase may also be treated as a distribution subject to U.S. federal income tax as a dividend. In addition, if a holder is a non-U.S. holder, such holder may be subject to U.S. federal withholding tax in connection with such a deemed distribution. If withholding tax is paid on a holder’s behalf as a result of an adjustment to the conversion rate of the Convertible Notes, the withholding agent may offset such payments against payments of cash and common stock on the Convertible Notes. Holders are urged to consult their tax advisor with respect to the U.S. federal income tax consequences resulting from an adjustment to the conversion rate of the Convertible Notes.
66
Because the Convertible Notes will initially be held in book-entry form, holders must rely on DTC’s procedures to receive communications relating to the Convertible Notes and exercise their rights and remedies.
We will initially issue the Convertible Notes in the form of one or more global notes registered in the name of Cede & Co., as nominee of DTC. Beneficial interests in global notes will be shown on, and transfers of global notes will be effected only through, the records maintained by DTC. Except in limited circumstances, we will not issue certificated Convertible Notes. Accordingly, if a holder owns a beneficial interest in a global note, then the holder will not be considered an owner or holder of the Convertible Notes. Instead, DTC or its nominee will be the sole holder of the Convertible Notes. Unlike persons who have certificated Convertible Notes registered in their names, owners of beneficial interests in global notes will not have the direct right to act on our solicitations for consents or requests for waivers or other actions from holders. Instead, those beneficial owners will be permitted to act only to the extent that they have received appropriate proxies to do so from DTC or, if applicable, a DTC participant. The applicable procedures for the granting of these proxies may not be sufficient to enable owners of beneficial interests in global notes to vote on any requested actions on a timely basis. In addition, notices and other communications relating to the Convertible Notes will be sent to DTC. We expect DTC to forward any such communications to DTC participants, which in turn would forward such communications to indirect DTC participants. But we can make no assurances that holders timely receive any such communications.
67
U.S. Federal Income Tax Risks
We cannot predict how tax reform legislation will affect us, our investments, or our stockholders, and any such legislation could adversely affect our business.
Legislative or other actions relating to taxes could have a negative effect on us. The rules dealing with U.S. federal income taxation are constantly under review by persons involved in the legislative process and by the Internal Revenue Service (“IRS”) and the U.S. Treasury Department. The U.S. House of Representatives and U.S. Senate passed tax reform legislation in December 2017 (the “2017 Tax Act”), which the President signed into law shortly thereafter. Such legislation made many changes to the Code, including, among other things, significant changes to the taxation of business entities, the deductibility of interest expense, and the tax treatment of capital investment. Such legislation could significantly and negatively affect our ability to qualify as a RIC and have adverse U.S. federal income tax consequences to us and our stockholders. Additionally, the U.S. Treasury and IRS are in the process of issuing regulations and administrative interpretations of the 2017 Tax Act, and any such regulations, interpretations, any court decisions interpreting the 2017 Tax Act or the regulations or administrative interpretations thereunder, or any other changes in the tax laws could similarly, significantly and negatively affect our ability to qualify for tax treatment as a RIC or the U.S. federal income tax consequences to us and our stockholders of such qualification, or could have other adverse consequences. Stockholders are urged to consult with their tax advisor regarding tax legislative, regulatory, or administrative developments and proposals and their potential effect on an investment in our securities.
For any period that we do not qualify as a “publicly offered regulated investment company,” as defined in the Code, U.S. stockholders that are individuals, trusts or estates will be taxed as though they received a distribution of some of our expenses.
A “publicly offered regulated investment company” is a RIC whose shares are either (i) continuously offered pursuant to a public offering, (ii) regularly traded on an established securities market or (iii) held by at least 500 persons at all times during the taxable year. No assurance can be provided that we will qualify as a publicly offered regulated investment company for any taxable year. For any period that we are not a publicly offered regulated investment company, for purposes of computing the taxable income of a non- corporate U.S. stockholder, (i) our earnings will be computed without taking into account such non-corporate U.S. stockholder’s allocable portion of our affected expenses, (ii) such non-corporate U.S. stockholder’s allocable portion of our affected expenses will be treated as an additional distribution to the stockholder, (iii) such non-corporate U.S. stockholder will be treated as having paid or incurred the allocable portion of our affected expenses for the calendar year, and (iv) such allocable portion of our affected expenses will be deductible by such stockholder only to the extent permitted under the limitations described below. For non-corporate U.S. stockholders, including individuals, trusts, and estates, significant limitations generally apply to the deductibility of certain affected expenses of a non-publicly offered regulated investment company. In particular, these expenses, which are treated as “miscellaneous itemized deductions,” are currently not deductible by individuals (and beginning in 2026, will be deductible only to the extent they exceed 2% of such a stockholder’s adjusted gross income), and are not deductible for alternative minimum tax purposes.
We will be subject to corporate-level U.S. federal income tax if we are unable to qualify or maintain qualification as a RIC under Subchapter M of the Code.
We intend to elect to be treated as a RIC under Subchapter M of the Code for our fiscal year ending December 31, 2020, and intend to qualify annually thereafter; however, no assurance can be given that we will be able to qualify for and maintain RIC status. To qualify for RIC tax treatment under the Code and to be relieved of U.S. federal taxes on income and gains distributed to our stockholders, we must meet certain requirements, including source-of-income, asset-diversification and annual distribution requirements. The annual distribution requirement applicable to RICs is satisfied if we timely distribute at least 90% of our net ordinary income and net short-term capital gains in excess of net long-term capital losses, if any, to our stockholders on an annual basis. To the extent we use debt financing, we will be subject to certain asset coverage ratio requirements under the 1940 Act and may be subject to financial covenants under loan and credit agreements, each of which could, under certain circumstances, restrict us from making annual distributions necessary to receive RIC tax treatment. If we are unable to obtain cash from other sources, we may fail to qualify to be taxed as a RIC and, thus, may be subject to corporate-level U.S. federal income
68
tax on our entire taxable income without regard to any distributions made by us. In order to be taxed as a RIC, we must also meet certain asset-diversification requirements at the end of each calendar quarter. Failure to meet these tests may result in our having to dispose of certain investments quickly in order to prevent the loss of RIC status. Because most of our investments are in private or thinly traded public companies, any such dispositions could be made at disadvantageous prices and may result in substantial losses. If we fail to be taxed as a RIC for any reason and become subject to corporate-level U.S. federal income tax, the resulting corporate taxes could substantially reduce our net assets, the amount of income available for distributions to stockholders and the amount of our distributions and the amount of funds available for new investments. Such a failure would have a material adverse effect on us and our stockholders.
We may have difficulty paying our required distributions if we recognize income before, or without, receiving cash representing such income.
For U.S. federal income tax purposes, we may be required to recognize taxable income in circumstances in which we do not receive a corresponding payment in cash. For example, since we will likely hold debt obligations that are treated under applicable tax rules as having OID (such as debt instruments with PIK, secondary market purchases of debt securities at a discount to par, interest or, in certain cases, increasing interest rates or debt instruments that were issued with warrants), we must include in income each year a portion of the OID that accrues over the life of the obligation, regardless of whether cash representing such income is received by us in the same taxable year. We may also have to include in income other amounts that we have not yet received in cash, such as unrealized appreciation for foreign currency forward contracts and deferred loan origination fees that are paid after origination of the loan or are paid in non-cash compensation such as warrants or stock. Furthermore, we may invest in non-U.S. corporations (or other non-U.S. entities treated as corporations for U.S. federal income tax purposes) that could be treated under the Code and U.S. Treasury regulations as “passive foreign investment companies” and/or “controlled foreign corporations.” The rules relating to investment in these types of non-U.S. entities are designed to ensure that U.S. taxpayers are either, in effect, taxed currently (or on an accelerated basis with respect to corporate- level events) or taxed at increased tax rates at distribution or disposition. In certain circumstances this could require us to recognize income where we do not receive a corresponding payment in cash.
Unrealized appreciation on derivatives, such as foreign currency forward contracts, may be included in taxable income while the receipt of cash may occur in a subsequent period when the related contract expires. Any unrealized depreciation on investments that the foreign currency forward contracts are designed to hedge are not currently deductible for tax purposes. This can result in increased taxable income whereby we may not have sufficient cash to pay distributions or we may opt to retain such taxable income and pay a 4% U.S. federal excise tax. In such cases we could still rely upon the “spillback provisions” to maintain RIC tax treatment.
We anticipate that a portion of our income may constitute OID or other income required to be included in taxable income prior to receipt of cash. Further, we may elect to amortize market discounts with respect to debt securities acquired in the secondary market and include such amounts in our taxable income in the current year, instead of upon disposition, as an election not to do so would limit our ability to deduct interest expenses for U.S. federal income tax purposes. Because any OID or other amounts accrued will be included in our investment company taxable income for the year of the accrual, we may be required to make a distribution to our shareholders in order to satisfy the Annual Distribution Requirement, even if we will not have received any corresponding cash amount. As a result, we may have difficulty meeting the Annual Distribution Requirement necessary to maintain RIC tax treatment under the Code. We may have to sell some of our investments at times and/or at prices we would not consider advantageous, raise additional debt or equity capital, make a partial share distribution, or forgo new investment opportunities for this purpose. If we are not able to obtain cash from other sources, and choose not to make a qualifying share distribution, we may fail to qualify for RIC tax treatment and thus become subject to corporate-level U.S. federal income tax.
69
We may choose to pay a portion of our distributions in our own stock, in which case you may be required to pay tax in excess of the cash you receive.
We may distribute taxable distributions that are payable in part in our stock. In accordance with certain applicable Treasury regulations and a revenue procedure issued by the IRS, a RIC may treat a distribution of its own stock as fulfilling its RIC distribution requirements if each stockholder may elect to receive his or her entire distribution in either cash or stock of the RIC, subject to a limitation that the aggregate amount of cash to be distributed to all stockholders must be at least 20% (which has been temporarily reduced to 10% for distributions declared on or after April 1, 2020, and on or before December 31, 2020) of the aggregate declared distribution. If too many stockholders elect to receive cash, the cash available for distribution must be allocated among the shareholders electing to receive cash (with the balance of the distribution paid in stock). In no event will any stockholder, electing to receive cash, receive the lesser of (a) the portion of the distribution such shareholder has elected to receive in cash or (b) an amount equal to his or her entire distribution times the percentage limitation on cash available for distribution. If these and certain other requirements are met, for U.S. federal income tax purposes, the amount of the dividend paid in stock will be equal to the amount of cash that could have been received instead of stock. Taxable stockholders receiving such distributions will be required to include the full amount of the dividend as ordinary income (or as long-term capital gain or qualified dividend income to the extent such distribution is properly reported as such) to the extent of our current and accumulated earnings and profits for U.S. federal income tax purposes.
As a result of receiving distributions in the form of our common stock, a U.S. stockholder may be required to pay tax with respect to such distributions in excess of any cash received. If a U.S. stockholder sells the stock such stockholder receives as a dividend in order to pay this tax, the sales proceeds may be less than the amount included in income with respect to the dividend, depending on the market price of our stock at the time of the sale. Furthermore, with respect to non-U.S. stockholders, we may be required to withhold U.S. federal tax with respect to such distributions, including in respect of all or a portion of such dividend that is payable in shares of our common stock. In addition, if a significant number of our stockholders determine to sell shares of our stock in order to pay taxes owed on distributions, it may put downward pressure on the trading price of shares of our common stock.
70
General Risk Factors
We are subject to risks related to corporate social responsibility.
Our business faces increasing public scrutiny related to environmental, social and governance (“ESG”) activities. We risk damage to our brand and reputation if we fail to act responsibly in a number of areas, such as environmental stewardship, corporate governance and transparency and considering ESG factors in our investment processes. Adverse incidents with respect to ESG activities could impact the value of our brand, the cost of our operations and relationships with investors, all of which could adversely affect our business and results of operations. Additionally, new regulatory initiatives related to ESG could adversely affect our business.
Additionally, new regulatory initiatives related to ESG that are applicable to us and our portfolio companies could adversely affect our business. In May 2018, the European Commission adopted an “action plan on financing sustainable growth.” The action plan is, among other things, designed to define and reorient investment toward sustainability. The action plan contemplates establishing EU labels for green financial products; increasing disclosure requirements in the financial services sector around ESG and strengthening the transparency of companies on their ESG policies and introducing a ‘green supporting factor’ in the EU prudential rules for banks and insurance companies to incorporate climate risks into banks’ and insurance companies’ risk management policies. There is a risk that a significant reorientation in the market following the implementation of these and further measures could be adverse to our portfolio companies if they are perceived to be less valuable as a consequence of, e.g., their carbon footprint or “greenwashing” (i.e., the holding out of a product as having green or sustainable characteristics where this is not, in fact, the case). We and our portfolio companies are subject to the risk that similar measures might be introduced in other jurisdictions in the future. Additionally, compliance with any new laws or regulations increases our regulatory burden and could make compliance more difficult and expensive, affect the manner in which we or our portfolio companies conduct our businesses and adversely affect our profitability.
There are significant financial and other resources necessary to comply with the requirements of being a public entity.
We are subject to the reporting requirements of the Exchange Act and certain requirements of the Sarbanes-Oxley Act (as defined in this annual report on Form 10-K). These requirements may place a strain on our systems and resources. The Exchange Act requires that we file annual, quarterly and current reports with respect to our business and financial condition. The Sarbanes-Oxley Act requires that we maintain effective disclosure controls and procedures and internal controls over financial reporting, which are discussed below. In order to maintain and improve the effectiveness of our disclosure controls and procedures and internal controls, significant resources and management oversight will be required. We have implemented procedures, processes, policies and practices for the purpose of addressing the standards and requirements applicable to public companies. These activities may divert management’s attention from other business concerns, which could have a material adverse effect on our business, financial condition, results of operations and cash flows. We incur significant additional annual expenses related to these steps and, among other things, directors’ and officers’ liability insurance, director fees, reporting requirements of the SEC, transfer agent fees, additional administrative expenses, increased auditing and legal fees and similar expenses.
The systems and resources necessary to comply with public company reporting requirements will increase further once we cease to be an “emerging growth company” under the Jumpstart Our Business Startups Act of 2012 (the “JOBS Act”). As long as we remain an emerging growth company, we intend to take advantage of certain exemptions from various reporting requirements that are applicable to other public companies, including not being required to comply with the auditor attestation requirements of Section 404 of the Sarbanes-Oxley Act. We will remain an emerging growth company for up to five years following an IPO or until the earliest of (i) the last day of the first fiscal year in which our annual gross revenues exceed $1.07 billion, (ii) December 31 of the fiscal year that we become a “large accelerated filer” as defined in Rule 12b-2 under the Exchange Act which would occur if the market value of our common stock that is held by non-affiliates exceeds $700.0 million as of the last business day of our most recently completed second fiscal quarter and we have been publicly reporting for at least 12 months or (iii) the date on which we have issued more than $1.0 billion in non-convertible debt securities during the preceding three-year period.
71
We may experience fluctuations in our operating results.
We may experience fluctuations in our operating results due to a number of factors, including our ability or inability to make investments in companies that meet our investment criteria, the interest rate payable on the debt securities we acquire, the default rate on such securities, the level of our expenses, variations in and the timing of the recognition of realized and unrealized gains or losses, the degree to which we encounter competition in our markets and general economic conditions. As a result of these factors, results for any period should not be relied upon as being indicative of performance in future periods.
Changes in laws or regulations governing our operations may adversely affect our business or cause us to alter our business strategy.
We and our portfolio companies are subject to regulation at the local, state and federal level. These laws and regulations, as well as their interpretation, may change from time to time, including as the result of interpretive guidance or other directives from the U.S. President and others in the executive branch, and new laws, regulations and interpretations may also come into effect, including those governing the types of investments we or our portfolio companies are permitted to make, any of which could have a material adverse effect on our business. In particular, on July 21, 2010, the Dodd-Frank Wall Street Reform and Consumer Protection Act, or the Dodd-Frank Act, became law. The Dodd-Frank Act impacts many aspects of the financial services industry. Many of the provisions of the Dodd-Frank Act have been implemented, while others will still require final rulemaking by regulatory authorities. President Trump and certain members of Congress have indicated that they will seek to amend or repeal portions of the Dodd-Frank Act, among other federal laws, and drastically reduce the role of regulatory agencies, such as the Consumer Financial Protection Bureau, which may create regulatory uncertainty in the near term. While the impact of the Dodd- Frank Act, and U.S. federal tax reform legislation enacted in December 2017, on us and our portfolio companies may not be known for an extended period of time, the Dodd-Frank Act and U.S. federal tax reform, including future rules implementing its provisions and the interpretation of those rules, along with other legislative and regulatory proposals directed at the financial services industry or affecting taxation that are proposed or pending in the U.S. Congress, may negatively impact the operations, cash flows or financial condition of us or our portfolio companies, impose additional costs on us or our portfolio companies, intensify the regulatory supervision of us or our portfolio companies or otherwise adversely affect our business or the business of our portfolio companies. In addition, if we do not comply with applicable laws and regulations, we could lose any licenses that we then hold for the conduct of our business and may be subject to civil fines and criminal penalties.
Additionally, changes to the laws and regulations governing our operations, including those associated with RICs, may cause us to alter our investment strategy in order to avail ourselves of new or different opportunities or result in the imposition of corporate-level U.S. federal income taxes on us. Such changes could result in material differences to the strategies and plans set forth in this annual report on Form 10-K and may shift our investment focus from the areas of expertise of our investment professionals to other types of investments in which our investment professionals may have little or no expertise or experience. Any such changes, if they occur, could have a material adverse effect on our results of operations and the value of your investment.
Over the last several years, there also has been an increase in regulatory attention to the extension of credit outside of the traditional banking sector, raising the possibility that some portion of the non-bank financial sector will be subject to new regulation. While it cannot be known at this time whether any regulation will be implemented or what form it will take, increased regulation of non-bank credit extension could negatively impact our operations, cash flows or financial condition, impose additional costs on us, intensify the regulatory supervision of us or otherwise adversely affect our business, financial condition and results of operations.
There is uncertainty surrounding potential legal, regulatory and policy changes by new presidential administrations in the United States that may directly affect financial institutions and the global economy.
As a result of the United States presidential election, which occurred on November 3, 2020 and subsequent senate runoff elections, the Democratic Party controls the executive and legislative branches of government. Changes in federal policy, including tax policies, and at regulatory agencies occur over time through policy and personnel changes following elections, which lead to changes involving the level of oversight and focus on the financial services industry or
72
the tax rates paid by corporate entities. The nature, timing and economic and political effects of potential changes to the current legal and regulatory framework affecting financial institutions remain highly uncertain. Uncertainty surrounding future changes may adversely affect our operating environment and therefore our business, financial condition, results of operations and growth prospects.
Terrorist attacks, acts of war, global health emergencies or natural disasters may impact the businesses in which we invest and harm our business, operating results and financial condition.
Terrorist acts, acts of war, global health emergencies or natural disasters may disrupt our operations, as well as the operations of the businesses in which we invest. Such acts have created, and continue to create, economic and political uncertainties and have contributed to global economic instability. Future terrorist activities, military or security operations, global health emergencies or natural disasters could further weaken the domestic/global economies and create additional uncertainties, which may negatively impact the businesses in which we invest directly or indirectly and, in turn, could have a material adverse impact on our business, operating results and financial condition. Losses from terrorist attacks, global health emergencies and natural disasters are generally uninsurable.
73
Item 1B. Unresolved Staff Comments
None.
We do not own any real estate or other physical properties materially important to our operations. Currently, we lease office space in Chandler, Arizona for our corporate headquarters. We believe that our office facilities are suitable and adequate for our business as it is contemplated to be conducted.
We are not currently subject to any material legal proceedings, nor, to our knowledge, are any material legal proceedings threatened against us. From time to time, we may be a party to certain legal proceedings in the ordinary course of business, including proceedings relating to the enforcement of our rights under contracts with our portfolio companies. Furthermore, third parties may seek to impose liability on us in connection with the activities of our portfolio companies. Our business is also subject to extensive regulation, which may result in regulatory proceedings against us. While the outcome of any future legal or regulatory proceedings cannot be predicted with certainty, we do not expect that any such future proceedings will have a material effect upon our financial condition or results of operations.
Item 4. Mine Safety Disclosures
Not Applicable.
74
Item 5. Market for Registrant’s Common Equity, Related Stockholder Matters and Issuer Purchases of Equity Securities
Common Stock
Our common stock began trading on the Nasdaq Global Select Market on January 29, 2021 under the symbol “TRIN” in connection with our IPO of shares of our common stock. See “Item 7. Management’s Discussion and Analysis of Financial Condition and Results of Operations — Recent Developments — Initial Public Offering.” Shares of BDCs may trade at a market price that is less than the value of the net assets attributable to those shares. The possibility that our shares of common stock will trade at a discount from net asset value per share or at premiums that are unsustainable over the long term are separate and distinct from the risk that our net asset value per share will decrease. It is not possible to predict whether our common stock will trade at, above, or below net asset value per share. See “Item 1A. Risk Factors—Risks Related to an Investment in Our Common Stock.” On March 3, 2021, the last reported closing sales price of our common stock on the Nasdaq Global Select Market was $15.26 per share, which represented a premium of approximately 17.1% to our net asset value per share of $13.03 as of December 31, 2020.
Prior to our IPO, the shares of our common stock were offered and sold in transactions exempt from registration under the Securities Act. As such, there was no public market for shares of our common stock during the year ended December 31, 2020.
Holders
As of March 3, 2021, there were approximately 213 holders of record of our common stock, which did not include stockholders for whom shares are held in “nominee” or “street name.”
Distributions
To obtain and maintain our tax treatment as a RIC, we must, among other things, timely distribute (or be treated as distributing) in each taxable year dividends of an amount equal to at least 90% of our investment company taxable income (which includes, among other items, dividends, interest, the excess of any net short-term capital gains over net long-term capital losses, as well as other taxable income, excluding any net capital gains reduced by deductible expenses) and 90% of our net tax-exempt income (which is the excess of our gross tax-exempt interest income over certain disallowed deductions) for that taxable year. As a RIC, we generally will not be subject to corporate-level U.S. federal income tax on our investment company taxable income and net capital gains that we distribute to stockholders. In addition, to avoid the imposition of a nondeductible 4% U.S. federal excise tax, we must timely distribute (or be treated as distributing) in each calendar year an amount at least equal to the sum of: (i) 98% of our net ordinary income, excluding certain ordinary gains and losses, recognized during a calendar year; (ii) 98.2% of our capital gain net income, adjusted for certain ordinary gains and losses, recognized for the twelve-month period ending on October 31 of such calendar year; and (iii) 100% of any income or net capital gains that we recognized in preceding years, but were not distributed in such years, and on which we paid no U.S. federal income tax.
We generally intend to make quarterly distributions and to distribute, out of assets legally available for distribution, substantially all of our available earnings, as determined by the Board in its sole discretion and in accordance with RIC requirements.
75
The following table summarizes distributions declared for the year ended December 31, 2020:
Declaration Date | | Record Date | | Payment Date | | Per Share Amount | |
May 14, 2020 | | May 29, 2020 | | June 5, 2020 | | $ | 0.22 |
August 12, 2020 | | August 21, 2020 | | September 4, 2020 | | | 0.27 |
November 12, 2020 | | November 20, 2020 | | December 4, 2020 | | | 0.27 |
December 22, 2020 | | December 30, 2020 | | January 15, 2021 | | | 0.27 |
Total | | | | | | $ | 1.03 |
Distribution Reinvestment Plan
We have adopted an “opt out” distribution reinvestment plan for our stockholders. As a result, if we declare a dividend, then stockholders’ cash distributions will be automatically reinvested in additional shares of our common stock, unless they specifically “opt out” of the distribution reinvestment plan so as to receive cash distributions. Stockholders who receive distributions in the form of shares of our common stock generally are subject to the same U.S. federal income tax consequences as are stockholders who elect to receive their distributions in cash.
Sales of Unregistered Securities
During the year ended December 31, 2020, we issued a total of 271,414 shares of our common stock pursuant to our distribution reinvestment plan. On January 15, 2021, we issued 87,710 shares of our common stock in connection with the dividend declared on December 22, 2020. These issuances were not subject to the registration requirements of the Securities Act. The aggregate value of the shares of our common stock issued pursuant to our distribution reinvestment plan during the year ended December 31, 2020 was approximately $3.4 million and the value of our common shares issued in January 2021 was approximately $1.1 million.
Equity Compensation Plan Information
See “Item 10. Executive Compensation” and “Item 12. Security Ownership of Certain Beneficial Owners and Management and Related Stockholder Matters.”
Information furnished under Part II. Item 5 of the Form 10-K shall not be deemed to be “soliciting material” or to be “filed” with the SEC or subject to Regulation 14A or 14C, or to the liabilities of Section 18 of the Exchange Act.
76
Item 6. Selected Financial Data
The selected financial and other data as of and for the year ended December 31, 2020 and for the period August 12, 2019 (date of inception) to December 31, 2019 is derived from our consolidated financial statements that have been audited by Ernst & Young, LLP, an independent registered public accounting firm. We were formed on August 12, 2019 and commenced operations on January 16, 2020. Prior to January 16, 2020, we had no operations, except for matters relating to our formation and organization as a BDC. As a result, there are no significant financial results for comparative purposes. The selected financial and other data should be read in conjunction with “Management’s Discussion and Analysis of Financial Condition and Results of Operations” and the consolidated financial statements and related notes included elsewhere herein.
| | | |
|
| For the Period | | |
| | | | | | of August 12, 2019 | | |
| | Year Ended | | | (date of inception) | | ||
(in thousands, except share and per share amounts) | | December 31, 2020 |
| | to December 31, 2019 | | ||
Investment income: | | | | | | | | |
Interest income | | $ | 51,255 | | | $ | — | |
Fee income | | | 3,709 | | | | — | |
Total investment income | | | 54,964 | | | | — | |
Operating expenses: | | | | | | | | |
Interest expense and other debt financing costs | | | 16,773 | | | | — | |
Compensation and benefits | | | 10,433 | | | | — | |
Professional fees | | | 2,283 | | | | | |
General and administrative | | | 2,104 | | | | 524 | |
Total operating expense | | | 31,593 | | | | 524 | |
Net investment income | | | 23,371 | | | | — | |
Net realized gain/(loss) on investments | | | (9,403) | | | | — | |
Net change in unrealized appreciation (depreciation) on investments | | | (4,966) | | | | — | |
Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds | | | (15,114) | | | | — | |
Net increase in net assets resulting from operations | | $ | (6,112) | | | $ | (524) | |
Net investment income per common share (basic and diluted) | | $ | 1.29 | | | $ | N/M | |
Net increase/(decrease) in net assets resulting from operations attributable to common stock per share (basic and diluted) | | $ | (0.34) | | | $ | N/M | |
Weighted-average shares outstanding - basic and diluted | | | 18,092,494 | | | | 10 | |
Distributions declared per common share: | | $ | 1.03 | | | $ | n/a | |
77
|
| | |
|
| For the Period |
| |
| | | | | | of August 12, 2019 | | |
| | Year Ended | | | (date of inception) | | ||
(dollars in thousands) | | December 31, 2020 |
| | to December 31, 2019 |
| ||
Balance sheet data: |
| | | |
| | | |
Investments, at value | | $ | 493,651 | | | $ | — | |
Cash and cash equivalents | | | 61,101 | | | | — | |
Total assets | | | 559,708 | | | | 6,202 | |
Total liabilities | | | 320,960 | | | | 6,726 | |
Total net assets | | | 238,748 | | | | (524) | |
| | | | | | | | |
Other Data: | | | | | | | | |
Number of portfolio companies at period end | | | 80 | | | | — | |
Effective yield on secured loan investments (1) | | | 12.5 | % | | | — | % |
Effective yield on equipment financing investments (1) | | | 14.9 | % | | | — | % |
Total return based on change in NAV (2) | | | (6.1) | % | | | — | % |
Total debt investments, at value | | | 443,219 | | | | — | |
Total warrant investments, at value | | | 17,778 | | | | — | |
Total equity investments, at value | | | 32,654 | | | | — | |
Unfunded commitments (3) | | | 116 | | | | — | |
Net asset value per share (4) | | $ | 13.03 | | | $ | (52,418.20) | |
N/M – Not Material
| (1) | Effective yield is calculated based on our average secured loan and equipment financing investments at cost at the end of each period and includes amortization of deferred fees and accretion of original issue discount, but excludes all other fee income. The weighted-average annual effective yield is higher than what an investor in shares of our common stock will realize on its investment because it does not reflect any debt investments on non-accrual status, our expenses or any sales load paid by an investor. For information on our investments on non-accrual status. See "Item 7. Management's Discussion and Analysis of Financial Condition and Results of Operations — Portfolio Asset Quality". |
| (2) | The total return equals the change in the ending net asset value over the beginning of the period price per share plus distributions paid per share during the period, divided by the beginning price assuming the distribution is reinvested on the date of issuance. The total return does not reflect any sales load that must be paid by investors. |
| (3) | Amount represents unfunded commitments, which have been requested by the portfolio company and unencumbered by milestones. Amount excludes unfunded commitments which have not been requested or are not available due to the borrower having not met certain milestones. |
| (4) | Based on common shares outstanding at period end. |
78
Item 7. Management’s Discussion and Analysis of Financial Condition and Results of Operations
The following discussion and analysis or our financial condition and results of operations should be read together with the consolidated financial statements and the related notes that are included in Item 8 of Part II of this annual report on Form 10-K. This discussion contains forward-looking statements based upon current expectations that involve risks and uncertainties. Our actual results may differ materially from those anticipated in these forward-looking statements as a result of various factors, including those set forth under the section entitled “Risk Factors.” Please also see the section entitled “Cautionary Note Regarding Forward-Looking Statements.”
Overview
We are a specialty lending company providing debt, including loans and equipment financings, to growth stage companies, including venture-backed companies and companies with institutional equity investors. We are an internally managed, closed-end, non-diversified management investment company that has elected to be regulated as a business development company (“BDC”) under the Investment Company Act of 1940, as amended (“the1940 Act”). We also intend to elect to be treated, and intend to qualify annually thereafter, as a regulated investment company (“RIC”) under Subchapter M of the Internal Revenue Code of 1986, as amended (the “Code”) for U.S. federal income tax purposes. As a BDC and a RIC, we are required to comply with certain regulatory requirements.
Our investment objective is to generate current income and, to a lesser extent, capital appreciation through our investments. We seek to achieve our investment objective by making investments consisting primarily of term loans and equipment financings and, to a lesser extent, working capital loans, equity and equity-related investments. In addition, we may obtain warrants or contingent exit fees at funding from many of our portfolio companies, providing an additional potential source of investment returns. We generally are required to invest at least 70% of our total assets in qualifying assets in accordance with the 1940 Act but may invest up to 30% of our total assets in non-qualifying assets, as permitted by the 1940 Act.
We target investments in growth stage companies, which are typically private companies, including venture-backed companies and companies with institutional equity investors. We define “growth stage companies” as companies that have significant ownership and active participation by sponsors, such as institutional investors or private equity firms, and expected annual revenues of up to $100.0 million. Subject to the requirements of the 1940 Act, we are not limited to investing in any particular industry or geographic area and seek to invest in under-financed segments of the private credit markets.
We invest in debt, including loans and equipment financings, that may have initial interest-only periods of up to 24 months and may then fully amortize over a total term of up to 60 months and are typically secured by a blanket first lien, a specific asset lien on mission critical assets, or a blanket second lien. We may also make a limited number of direct equity and equity-related investments in conjunction with our debt investments.
Our History
Trinity Capital Inc. was incorporated under the general corporation laws of the State of Maryland on August 12, 2019 and commenced operations on January 16, 2020. Prior to January 16, 2020, we had no operations, except for matters relating to our formation and organization as a BDC.
On January 16, 2020, through a series of transactions (the “Formation Transactions”), we acquired Trinity Capital Investment, LLC ( “TCI, LLC”), Trinity Capital Fund II, L.P. (“Fund II”), Trinity Capital Fund III, L.P. (“Fund III”), Trinity Capital Fund IV, L.P. (“Fund IV”) and Trinity Sidecar Income Fund, L.P. (“Sidecar Fund,” and collectively, the “Legacy Funds”) and all of their respective assets (the “Legacy Assets”), including their respective investment portfolios (the “Legacy Portfolio”), as well as Trinity Capital Holdings, LLC (“Trinity Capital Holdings”), a holding company whose subsidiaries managed and/or had the right to receive fees from certain of the Legacy Funds. In order to complete these transactions we used a portion of the proceeds from our private equity offering and private debt offering that occurred on January 16, 2020 (refer to "Item 8. Consolidated Financial Statements and Supplementary Data - Note 1. Organization and Basis of Presentation" for further discussion of these transactions).
79
The Legacy Funds were merged with and into the Company, and we issued 9,183,185 shares of our common stock for an aggregate amount of approximately $137.7 million and paid approximately $108.7 million in cash to the Legacy Funds’ investors, which included the general partners/managers of the Legacy Funds (the “Legacy Investors”), to acquire the Legacy Funds and all of their respective assets, including the Legacy Portfolio. Our senior management team, led by Steven L. Brown, comprises the majority of the senior management team that managed the Legacy Funds and sourced the Legacy Portfolio.
As part of the Formation Transactions, we also acquired 100% of the equity interests of Trinity Capital Holdings for an aggregate purchase price of $10.0 million, which was comprised of 533,332 shares of our common stock, totaling approximately $8.0 million, and approximately $2.0 million in cash. In connection with the acquisition of such equity interests, the Company also assumed a $3.5 million severance related liability with respect to a former member of certain general partners of certain Legacy Funds. In connection with the acquisition of Trinity Capital Holdings, approximately $13.5 million (consisting of the aggregate purchase price and severance related liability assumed) was expensed to Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds in the Consolidated Statements of Operations. As a result of the Formation Transactions, Trinity Capital Holdings became a wholly owned subsidiary of the Company.
On February 2, 2021, we completed our initial public offering of 8,006,291 shares of our common stock at a price of $14.00 per share, inclusive of the underwriters option to purchase additional shares, which was exercised in full. Our common stock began trading on the Nasdaq Global Select Market on January 29, 2021 under the symbol “TRIN.” Proceeds from this offering were primarily used to pay down a portion of our existing indebtedness outstanding under the Credit Facility.
COVID-19 Developments
In March 2020, the outbreak of COVID-19 was recognized as a pandemic by the World Health Organization. Shortly thereafter, the President of the United States declared a National Emergency throughout the United States attributable to such pandemic. The pandemic has become increasingly widespread in the United States, including in the markets in which the Company primarily operates. During the year ended December 31, 2020, and subsequent to December 31, 2020, the COVID-19 pandemic has had a significant impact on the U.S. and global economy.
We have and continue to assess the impact of the COVID-19 pandemic on our portfolio companies. We cannot predict the full impact of the COVID-19 pandemic, including its duration in the United States and worldwide, the effectiveness of governmental responses designed to mitigate strain on businesses and the economy, and the magnitude of the economic impact of the outbreak, including with respect to the travel restrictions with a view to partially or fully reopening their economies, many cities world-wide have since experienced a surge in the reported number of cases, hospitalizations and deaths related to the COVID-19 pandemic. These increases have led to the re-introduction of restrictions and business shutdowns in certain states, counties and cities in the United States and globally and could continue to lead to the re-introduction of such restrictions and business shutdowns elsewhere. Additionally, as of February 2021, travelers from the United States are not allowed to visit Canada, Australia or the majority of countries in Europe, Asia, Africa and South America. These continued travel restrictions may prolong the global economic downturn. In addition, although the Federal Food and Drug Administration authorized vaccines for emergency use starting in December 2020, it remains unclear when the restrictions that were imposed to slow the spread of the virus will be lifted entirely. The delay in distributing vaccines could lead people to continue to self-isolate and not participate in the economy at pre-pandemic levels for a prolonged period of time. Even after the COVID-19 pandemic subsides, the U.S. economy and most other major global economies may continue to experience a recession, and we anticipate our business operations could be materially adversely affected by a prolonged recession in the United States and other major markets. As such, we are unable to predict the duration of any business and supply-chain disruptions, the extent to which the COVID-19 pandemic will negatively affect our portfolio companies’ operating results or the impact that such disruptions may have on our results of operations and financial condition. Though the magnitude of the impact remains to be seen, we expect our portfolio companies and, by extension, our operating results to be adversely impacted by the COVID-19 pandemic and, depending on the duration and extent of the disruption to the operations of our portfolio companies, we expect that certain portfolio companies will experience financial distress and may possibly default on their financial obligations to us and their other capital providers. Some of our portfolio companies have significantly curtailed business operations, furloughed or laid off employees and terminated service providers, and deferred capital
80
expenditures, which could impair their business on a permanent basis and additional portfolio companies may take similar actions. We continue to closely monitor our portfolio companies, which includes assessing each portfolio company’s operational and liquidity exposure and outlook; however, any of these developments would likely result in a decrease in the value of our investment in any such portfolio company. In addition, to the extent that the impact to our portfolio companies results in reduced interest payments or permanent impairments on our investments, we could see a decrease in our net investment income, which would increase the percentage of our cash flows dedicated to our debt obligations and could impact the amount of any future distributions to our stockholders.
Critical Accounting Policies
The Company’s financial statements are prepared in accordance with generally accepted accounting principles in the United States of America (“GAAP”) and pursuant to Regulation S-X under the Securities Act of 1933, as amended (the “Securities Act”). The Company follows accounting and reporting guidance as determined by the Financial Accounting Standards Board (“FASB”), in FASB Accounting Standards Codification (“ASC”) 946, Financial Services — Investment Companies.
The preparation of our financial statements in accordance with GAAP requires us to make estimates and assumptions that affect the reported amounts of assets, liabilities, revenues and expenses. Changes in the economic environment, financial markets and any other parameters used in determining such estimates could cause actual results to differ materially. Valuation of investments, income recognition, realized / unrealized gains or losses and U.S. federal income taxes are considered to be our critical accounting policies and estimates. For additional information, please refer to “Note 2 - Summary of Significant Accounting Policies” in the notes to the consolidated financial statements included with this annual report on Form 10-K.
Valuation of Investments
The most significant estimate inherent in the preparation of the Company’s consolidated financial statements is the valuation of investments and the related amounts of unrealized appreciation and depreciation of investments recorded. The Company’s investments are carried at fair value in accordance with the 1940 Act and ASC 946 and measured in accordance with ASC 820, Fair Value Measurements and Disclosures (“ASC 820”). ASC 820 defines fair value, establishes a framework for measuring fair value, establishes a fair value hierarchy based on the observability of inputs used to measure fair value, and provides disclosure requirements for fair value measurements. ASC 820 requires the Company to assume that each of the portfolio investments is sold in a hypothetical transaction in the principal or, as applicable, most advantageous market using market participant assumptions as of the measurement date. Market participants are defined as buyers and sellers in the principal market that are independent, knowledgeable and willing and able to transact. The Company values its investments at fair value as determined in good faith by the Company’s Board of Directors (the “Board”) in accordance with the provisions of ASC 820 and the 1940 Act.
While the Board is ultimately and solely responsible for determining the fair value of the Company’s investments, the Company has engaged independent valuation firms to provide the Company with valuation assistance with respect to its investments. The Company engages independent valuation firms on a discretionary basis. Specifically, on a quarterly basis, the Company will identify portfolio investments with respect to which an independent valuation firm will assist in valuing certain investments. The Company selects these portfolio investments based on a number of factors, including, but not limited to, the potential for material fluctuations in valuation results, size, credit quality and the time lapse since the last valuation of the portfolio investment by an independent valuation firm.
Investments recorded on the Company’s Consolidated Statements of Assets and Liabilities as of December 31, 2020 are categorized based on the inputs to the valuation techniques as follows:
Level 1 — Investments whose values are based on unadjusted quoted prices for identical assets in an active market that the Company has the ability to access (examples include investments in active exchange-traded equity securities and investments in most U.S. government and agency securities).
81
Level 2 — Investments whose values are based on quoted prices in markets that are not active or model inputs that are observable either directly or indirectly for substantially the full term of the investment.
Level 3 — Investments whose values are based on prices or valuation techniques that require inputs that are both unobservable and significant to the overall fair value measurement (for example, investments in illiquid securities issued by privately held companies). These inputs reflect management’s own assumptions about the assumptions a market participant would use in pricing the investment.
Given the nature of lending to venture capital-backed growth stage companies, substantially all of the Company’s investments in these portfolio companies are considered Level 3 assets under ASC 820 because there is no known or accessible market or market indexes for these investment securities to be traded or exchanged. The Company uses an internally developed portfolio investment rating system in connection with its investment oversight, portfolio management and analysis and investment valuation procedures. This system takes into account both quantitative and qualitative factors of the portfolio companies. Due to the inherent uncertainty of determining the fair value of investments that do not have a readily available market value, the fair value of the Company’s investments may fluctuate from period to period. Because of the inherent uncertainty of valuation, these estimated values may differ significantly from the values that would have been reported had a ready market for the investments existed, and it is reasonably possible that the difference could be material.
Fair value estimates are made at discrete points in time based on relevant information. These estimates may be subjective in nature and involve uncertainties and matters of significant judgment and, therefore, cannot be determined with precision. The carrying amounts of the Company’s financial instruments, consisting of cash, investments, receivables, payables and other liabilities approximate the fair values of such items due to the short-term nature of these instruments.
Income Recognition
Interest Income
The Company recognizes interest income on an accrual basis and recognizes it as earned in accordance with the contractual terms of the loan agreement to the extent that such amounts are expected to be collected. Original issue discount (“OID”) initially includes the estimated fair value of detachable equity warrants obtained in conjunction with the origination of debt securities, and is accreted into interest income over the term of the loan as a yield enhancement based on the effective yield method. In addition, the Company may also be entitled to an end-of-term (“EOT”) fee. Debt EOT fees to be paid at the termination of the financing arrangements are accreted into interest income over the contractual life of the debt based on the effective yield method. As of December 31, 2020, Trinity Capital had an EOT payment receivable of approximately $37.9 million, which is included as a component of the cost basis of the Company’s current debt securities.
Income related to application or origination payments, net of related expenses, and generally collected in advance, includes loan commitment and facility fees for due diligence, as well as fees for transaction services rendered by the Company to borrowers. Loan and commitment fees in excess of the related expenses are amortized into interest income over the contractual life of the loan. In certain loan arrangements, warrants or other equity interests are received from the borrower as additional origination fees. The Company recognizes nonrecurring fees over the remaining term of the loan commencing in the quarter relating to specific loan modifications.
When a portfolio company pays off their outstanding indebtedness prior to the scheduled maturity date, then the acceleration of the accretion of the OID and EOT is recognized as interest income.
Fee Income
The Company recognizes one-time fee income, including, but not limited to, structuring fees, prepayment penalties, and exit fees related to a change in ownership of the portfolio company, as other income when earned. These fees are
82
generally earned when the portfolio company enters into an equipment financing arrangement or pays off their outstanding indebtedness prior to the scheduled maturity.
Portfolio Composition and Investment Activity
Portfolio Composition
As of December 31, 2020, our investment portfolio had an aggregate fair value of approximately $493.7 million and was comprised of approximately $320.7 million in secured loans, $122.5 million in equipment financings, and $50.5 million in equity and equity-related investments, including warrants, across 80 portfolio companies.
A summary of the composition of our investment portfolio at cost and fair value as a percentage of total investments as of December 31, 2020 are shown in following table:
|
| |
| Fair |
|
Type | | Cost | | Value |
|
Secured Loans |
| 65.1% | | 65.0% | |
Equipment Financings |
| 24.7% | | 24.8% | |
Equity | | 6.6% | | 6.6% | |
Warrants |
| 3.6% | | 3.6% | |
Total |
| 100.0% | | 100.0% | |
The following table shows the composition of our investment portfolio by geographic region at cost and fair value as a percentage of total investments as of December 31, 2020. The geographic composition is determined by the location of the corporate headquarters of the portfolio company.
|
| |
| Fair | |
Geographic Region | | Cost | | Value | |
United States | | | | | |
West |
| 49.6% | | 48.8% | |
Northeast |
| 26.4% | | 25.9% | |
Midwest |
| 9.5% | | 8.9% | |
Mountain |
| 6.8% | | 6.9% | |
Southeast |
| 2.2% | | 3.6% | |
South |
| 0.1% | | 0.4% | |
Canada |
| 5.4% | | 5.5% | |
Total |
| 100.0% | | 100.0% | |
83
Set forth below is a table showing the industry composition of our investment portfolio at cost and fair value as a percentage of total investments as of December 31, 2020:
|
| |
| Fair |
|
Industry | | Cost | | Value |
|
Manufacturing |
| 20.8% | | 20.2% | |
Professional, Scientific, and Technical Services |
| 15.6% | | 16.0% | |
Retail Trade |
| 15.7% | | 15.4% | |
Finance and Insurance |
| 7.0% | | 7.2% | |
Information |
| 6.4% | | 6.2% | |
Rental and Leasing Services |
| 5.8% | | 5.9% | |
Utilities |
| 5.4% | | 5.5% | |
Pharmaceutical |
| 3.5% | | 4.9% | |
Wholesale Trade |
| 4.8% | | 4.8% | |
Agriculture, Forestry, Fishing and Hunting | | 4.2% | | 4.2% | |
Real Estate |
| 3.5% | | 3.5% | |
Health Care and Social Assistance |
| 2.9% | | 2.3% | |
Educational Services |
| 1.9% | | 2.0% | |
Construction | | 2.0% | | 1.4% | |
Administrative and Support and Waste Management and Remediation Services |
| 0.5% | | 0.5% | |
Total |
| 100.0% | | 100.0% | |
As of December 31, 2020, our debt investments had a weighted average time to maturity of approximately 3.0 years. Additional information regarding our portfolio is set forth in the schedule of investments and the related notes thereto included with this annual report on Form 10-K.
Investment Activity
During the year ended December 31, 2020, in addition to $417.0 million in investments we acquired in connection with the Formation Transactions, we made an aggregate of approximately $144.3 million of investments in 18 new portfolio companies and approximately $95.7 million of investments in 18 existing portfolio companies. During the year ended December 31, 2020, we received an aggregate of $160.9 million in proceeds from repayments of our investments including proceeds of approximately $108.8 million from early repayments.
The following table provides a summary of the changes in the investment portfolio for the year ended December 31, 2020 (in thousands):
| | | | | | | | | | | Year Ended | |
| | | | | | | | | | | December 31, 2020 | |
Fair Value as of January 1, 2020 | | | | | | | | | | | $ | — |
Formation Transactions acquisitions | | | | | | | | | | | | 417,023 |
Purchases | | | | | | | | | | | | 238,564 |
Non-cash conversion | | | | | | | | | | | | 1,263 |
Proceeds from Paydowns and Sales | | | | | | | | | | | | (52,111) |
Proceeds from early repayments | | | | | | | | | | | | (108,790) |
Amortization and Accretion | | | | | | | | | | | | 11,788 |
Net Realized Gain (Loss) | | | | | | | | | | | | (9,403) |
Third Party Participation (1) | | | | | | | | | | | | 283 |
Change in Unrealized Appreciation (Depreciation) | | | | | | | | | | | | (4,966) |
Fair Value as of December 31, 2020 | | | | | | | | | | | $ | 493,651 |
84
| (1) | Certain third parties have rights to 17,485 shares of Nanotherapeutics common stock at a fair value of approximately $0.6 million as of December 31, 2020. The activity related to these shares and the related liability is recorded against unrealized appreciation/(depreciation). |
The level of our investment activity can vary substantially from period to period depending on many factors, including the amount of debt, including loans and equipment financings, and equity capital required by growth stage companies, the general economic environment and market conditions, including as a result of the COVID-19 pandemic, and the competitive environment for the types of investments we make.
Portfolio Asset Quality
Our portfolio management team uses an ongoing investment risk rating system to characterize and monitor our outstanding loans and equipment financings. Our portfolio management team monitors and, when appropriate, recommends changes to the investment risk ratings. Our Investment Committee reviews the recommendations and/or changes to the investment risk ratings, which are submitted on a quarterly basis to the Board and its Audit Committee.
For our investment risk rating system, we review seven different criteria and, based on our review of such criteria, we assign a risk rating on a scale of 1 to 5, as set forth in the following illustration.
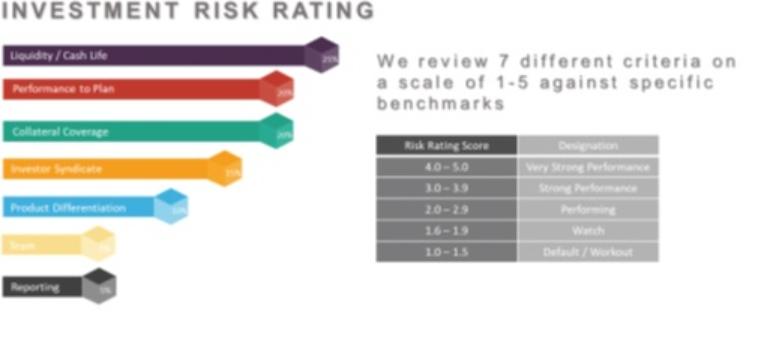
The following table shows the distribution of our loan and equipment financing investments on the 1 to 5 investment risk rating scale range at fair value as of December 31, 2020 (dollars in thousands):
|
| |
| Investments at |
| Percentage of |
| |
Investment Risk Rating Scale Range | | Designation | | Fair Value | | Total Portfolio |
| |
4.0 - 5.0 | | Very Strong Performance | | $ | 92,519 |
| 20.9% | |
3.0 - 3.9 | | Strong Performance | |
| 212,969 |
| 48.0% | |
2.0 - 2.9 | | Performing | |
| 116,895 |
| 26.4% | |
1.6 - 1.9 | | Watch | |
| 19,230 |
| 4.3% | |
1.0 - 1.5 | | Default/Workout | |
| 1,606 |
| 0.4% | |
Total | | | | $ | 443,219 |
| 100.0% | |
As of December 31, 2020, our loan and equipment financing investments had a weighted average risk rating score of 3.2.
Debt Investments on Non-Accrual Status
When a debt security becomes 90 days or more past due, or if our management otherwise does not expect that principal, interest, and other obligations due will be collected in full, we will generally place the debt security on non-
85
accrual status and cease recognizing interest income on that debt security until all principal and interest due has been paid or we believe the borrower has demonstrated the ability to repay its current and future contractual obligations. Any uncollected interest is reversed from income in the period that collection of the interest receivable is determined to be doubtful. However, we may make exceptions to this policy if the investment has sufficient collateral value and is in the process of collection.
As of December 31, 2020, loans to three portfolio companies were on non-accrual status with a total cost of approximately $3.4 million, and a total fair market value of approximately $2.2 million, or 0.5%, of the fair value of the Company’s investment portfolio.
Results of Operations
The following discussion and analysis of our results of operations encompasses our consolidated results for the year ended December 31, 2020. We were formed on August 12, 2019 and commenced operations on January 16, 2020. Prior to January 16, 2020, we had no operations, except for matters relating to our formation and organization as a BDC. As a result, there are no significant financial results for comparative purposes.
Investment Income
The following table sets forth the components of investment income (in thousands):
| | Year Ended | |
|
| December 31, 2020 | |
Stated interest income | | $ | 38,179 |
Amortization of original issue discount | |
| 10,750 |
Acceleration of amortization of original issue discount | | | 2,326 |
Prepayment penalty and related fees | | | 2,032 |
Other fee income | | | 1,677 |
Total investment income | | $ | 54,964 |
We generate revenues primarily in the form of investment income from the investments we hold, generally in the form of interest income from our debt securities. Investment income represents interest income recognized as earned in accordance with the contractual terms of the loan agreement. Interest income from original issue discount (“OID”) represents the estimated fair value of detachable equity warrants obtained in conjunction with the origination of debt securities, including loans and equipment financings and is accreted into interest income over the term of the loan as a yield enhancement. Interest income from payment-in-kind (“PIK”) represents contractually deferred interest added to the loan balance recorded on an accrual basis to the extent such amounts are expected to be collected.
Loan and commitment fees in excess of related expenses are amortized into interest income over the contractual life of the loan. The Company also recognizes certain fees as one-time fee income, including, but not limited to, prepayment penalties, fees related to select covenant default, late-payment fees, structuring fees and exit fees related to a change in ownership of the portfolio company.
For the year ended December 31, 2020, total investment income was approximately $55.0 million, which represents an approximate effective yield of 14.0% on the average investments during such period.
Operating Expenses
Our operating expenses are comprised of interest and fees on our borrowings, employee compensation and general and administrative expenses. Our operating expenses totaled approximately $31.6 million for the year ended December 31, 2020.
86
Interest and Fees on our Borrowings
Interest and fees on our borrowings totaled approximately $16.8 million for the year ended December 31, 2020, which is primarily comprised of interest and fees related to the Credit Facility, the 2025 Notes and the Convertible Notes. We had a weighted average cost of debt, comprised of interest and fees, of approximately 6.6% for the year ended December 31, 2020.
Employee Compensation and Benefits
Employee compensation and benefits totaled approximately $10.4 million for the year ended December 31, 2020. As of December 31, 2020, the Company had 34 employees.
The Board has approved the 2019 Trinity Capital Inc. Long-Term Incentive Plan and the Trinity Capital Inc. 2019 Non-Employee Director Restricted Stock Plan, each to be effective upon receipt of exemptive relief from the SEC and stockholder approval of such plans. We have applied for an exemptive order from the SEC to permit us to issue certain securities under such plans. If such exemptive relief and stockholder approval are obtained, the Compensation Committee may award such securities in such amounts and on such terms as the Compensation Committee determines and consistent with any exemptive order the SEC may issue and the terms of such plans, as applicable. The SEC is not obligated to grant an exemptive order to allow this practice and will do so only if it determines that such practice is consistent with stockholder interests and does not involve overreaching by management or our Board. We cannot provide any assurance that we will receive such exemptive relief from the SEC or such stockholder approval.
Professional Fees Expenses
Professional fees expenses include legal fees, accounting fees, third-party valuation fees, and talent acquisition fees. Our professional fees expenses totaled approximately $2.3 million for the year ended December 31, 2020.
General and Administrative Expenses
General and administrative expenses include insurance premiums, rent, taxes and other various expenses related to our ongoing operations. Our general and administrative expenses totaled approximately $2.1 million for the year ended December 31, 2020.
Net Investment Income
As a result of approximately $55.0 million in total investment income as compared to approximately $31.6 million in total expenses, net investment income for the year ended December 31, 2020 was approximately $23.4 million or $1.29 per share.
Net Realized Gains and Losses
Realized gains or losses are measured by the difference between the net proceeds from the sale or redemption of an investment or a financial instrument and the cost basis of the investment or financial instrument, without regard to unrealized appreciation or depreciation previously recognized, and includes investments written-off during the period. For the year ended December 31, 2020, we realized net losses on investments of approximately $9.4 million primarily related to the exit of two loans during the year.
87
The net realized gains (losses) from the sales, repayments, or exits of investments were comprised of the following (in thousands):
| | Year Ended | |
|
| December 31, 2020 | |
Net realized gain (loss) on investments: | | |
|
Gross realized gains | | $ | 1,350 |
Gross realized losses | |
| (10,753) |
Total net realized gains/(losses) on investments | | $ | (9,403) |
Net Change in Unrealized Appreciation / (Depreciation) from Investments
Net change in unrealized appreciation (depreciation) from investments primarily reflects the net change in the fair value of the investment portfolio and financial instruments and the reclassification of any prior period unrealized appreciation or depreciation on exited investments and financial instruments to realized gains or losses.
Net unrealized appreciation and depreciation on investments is comprised of the following (in thousands):
| | Year Ended | |
|
| December 31, 2020 | |
Gross unrealized appreciation | | $ | 15,162 |
Gross unrealized depreciation | |
| (19,845) |
Third party participation (1) | | | (283) |
Net unrealized appreciation/depreciation reclassified related to net realized gains or losses (2) | |
| — |
Total net unrealized gains (losses) on investments | | $ | (4,966) |
| (1) | Certain third parties have rights to 17,485 shares of Nanotherapeutics common stock at a fair value of approximately $0.6 million as of December 31, 2020. The activity related to these shares and the related liability is recorded against unrealized appreciation (depreciation). |
| (2) | Investments were recorded at their fair values in the Formation Transactions on January 16, 2020, therefore no reclassification of unrealized appreciation (depreciation) was recorded during the year ended December 31, 2020. |
The changes in net unrealized appreciation/(depreciation) from investments during the year ended December 31, 2020 consisted of the following (in thousands):
|
| Net Unrealized | |
| | Appreciation | |
Portfolio Company |
| (Depreciation) | |
Nanotherapeutics, Inc. | | $ | 6,976 |
Hospitalists Now, Inc. | |
| 1,314 |
Instart Logic, Inc. | |
| 978 |
GrubMarket, Inc. | |
| 960 |
Lucidworks, Inc. | |
| 703 |
Birchbox, Inc. | | | (1,335) |
Untuckit, Inc. | | | (1,867) |
Project Frog, Inc. | | | (2,915) |
Workwell Prevention & Care Inc. | |
| (2,977) |
Atieva, Inc. | |
| (3,021) |
Other, net | |
| (3,782) |
Total | | $ | (4,966) |
88
Financial Condition, Liquidity and Capital Resources
Our liquidity and capital resources are generated primarily from the net proceeds of offerings of our securities, including the Private Offerings, borrowings under the Credit Facility, the Convertible Notes offering and cash flows from our operations, including investment sales and repayments, as well as income earned on investments and cash equivalents. Our primary use of our funds includes investments in portfolio companies, payments of interest on our outstanding debt, and payments of fees and other operating expenses we incur. We also expect to use our funds to pay distributions to our stockholders. We have used, and expect to continue to use, our borrowings, including under the Credit Facility or any future credit facility, and proceeds from the turnover of our portfolio to finance our investment objectives and activities.
We may, from time to time, enter into additional credit facilities, increase the size of our existing Credit Facility, or issue additional securities in private or public offerings. Any such incurrence or issuance would be subject to prevailing market conditions, our liquidity requirements, contractual and regulatory restrictions, and other factors.
For the year ended December 31, 2020, we experienced a net increase in cash and cash equivalents in the amount of $61.1 million, which is the net result of $211.3 million of cash provided by our financing activities offset by $58.2 million of cash used in our operating activities and $92.0 million used in investing activities.
The $58.2 million of net cash used in our operating activities resulted primarily from the $239.8 million of cash used for the purchase of investments partially offset by cash proceeds totaling $160.9 million from the sales and repayments of debt and equity investments. The $92.0 million used in investing activities was primarily related to $89.5 million used for the acquisition of the Legacy Funds in the Formation Transactions, $2.2 million used in the acquisition of Trinity Capital Holdings and $0.3 million for the acquisition of capital assets.
During the year ended December 31, 2020, net cash provided by financing activities of $211.3 million was primarily provided from proceeds from the issuance of our common stock of $125.0 million, proceeds of $125.0 million from the issuance of our 2025 Notes, and net proceeds of $48.7 million from the issuance of our Convertible Notes, partially offset by net repayments under our Credit Facility of $55.0 million and distributions paid of $10.4 million.
As of December 31, 2020, we had $86.7 million in available liquidity, including $44.7 million in unrestricted cash and cash equivalents. We had available borrowing capacity of $42.0 million under the Credit Facility, subject to its terms and regulatory requirements. We primarily invest cash on hand in interest bearing deposit accounts. As of December 31, 2020, we had approximately $16.4 million of restricted cash which consists of approximately $15.7 million related to the Credit Facility covenants, and approximately $0.7 million held in escrow related to the payout of a settlement with a former member of certain general partners of certain of the Legacy Funds.
In January 2020, in connection with the Formation Transactions, we became a party to, and assumed, the Credit Facility through our wholly owned subsidiary, Trinity Funding 1, LLC. The Credit Facility matures on January 8, 2022, unless extended, and we have the ability to borrow up to an aggregate of $300.0 million. In addition, borrowings under the Credit Facility are subject to floating interest rates based on LIBOR, generally bearing interest at a rate of the three-month LIBOR plus 3.25%. During the year ended December 31, 2020, we repaid approximately $85.0 million and borrowed an additional $30.0 million under the Credit Facility. As of December 31, 2020, approximately $135.0 million was outstanding under the Credit Facility.
In January 2020, we completed the Private Common Stock Offering in reliance upon the available exemptions from the registration requirements of the Securities Act, pursuant to which we issued and sold 8,333,333 shares of our common stock for aggregate gross proceeds of approximately $125.0 million. A portion of the proceeds of the Private Common Stock Offering were used to complete the Formation Transactions and repay a portion of the outstanding borrowings under the Credit Facility.
In January 2020, concurrent with the completion of the Private Common Stock Offering, we completed the 144A Note Offering in reliance upon the available exemptions from the registration requirements of the Securities Act, pursuant to which we issued and sold $125.0 million in aggregate principal amount of the unsecured 2025 Notes
89
that mature on January 16, 2025, unless repurchased or redeemed in accordance with their terms prior to such date and bear interest at a fixed rate of 7.00% per year payable quarterly on March 15, June 15, September 15 and December 15 of each year. A portion of the proceeds of the 144A Note Offering were used to complete the Formation Transactions and repay a portion of the outstanding borrowings under the Credit Facility. Aggregate estimated offering expenses in connection with the transaction, including the fees and commissions, were approximately $4.8 million. As of December 31, 2020, we had $125 million in aggregate principal amount of 2025 Notes outstanding.
In December 2020, we issued $50.0 million in aggregate principal amount of the Convertible Notes. The sale generated net proceeds of $47.0 million, including $1.7 million of debt issuance costs and $1.3 million of original issue discount. The Convertible Notes bear interest at a rate of 6.00% per year, payable semiannually in arrears on May 1 and November 1, of each year. The Convertible Notes mature on December 11, 2025, unless earlier converted by noteholders or purchased by the Company at the noteholders option upon the occurrence of a fundamental change, as defined in the indenture governing the Convertible Notes. As of December 31, 2020, we had $50.0 million in aggregate principal amount of Convertible Notes outstanding.
Refer to “Item 8. Financial Statements and Supplementary Data – Note 5 – Borrowings” included in the notes to our consolidated financial statements appearing elsewhere in this report for a discussion of our borrowings.
Reduced Asset Coverage Requirements
In accordance with the 1940 Act, with certain limited exceptions, we are only allowed to incur borrowings, issue debt securities or issue preferred stock, if immediately after the borrowing or issuance, the ratio of total assets (less total liabilities other than indebtedness) to total indebtedness plus preferred stock, is at least 150%. On September 27, 2019, the Board, including a “required majority” (as such term is defined in Section 57(o) of the 1940 Act) and our initial stockholder approved the application to us of the 150% minimum asset coverage ratio set forth in Section 61(a)(2) of the 1940 Act. As a result, effective September 28, 2019, the asset coverage ratio under the 1940 Act applicable to us decreased from 200% to 150%, permitting us to potentially borrow $2 for investment purposes of every $1 of investor equity. As of December 31, 2020, our asset coverage ratio was approximately 177.0% and our asset coverage ratio per unit was approximately $1,770.
Commitments and Off-Balance Sheet Arrangements
Other than contractual commitments with respect to our portfolio companies and other legal contingencies incurred in the normal course of our business, we do not have any off-balance sheet financings or liabilities as of December 31, 2020.
The Company’s commitments and contingencies consist primarily of unfunded commitments to extend credit in the form of loans to the Company’s portfolio companies. A portion of these unfunded contractual commitments as of December 31, 2020 are dependent upon the portfolio company reaching certain milestones before the debt commitment becomes available. Furthermore, the Company’s credit agreements with its portfolio companies generally contain customary lending provisions that allow the Company relief from funding obligations for previously made commitments in instances where the underlying portfolio company experiences materially adverse events that affect the financial condition or business outlook for the company. Since a portion of these commitments may expire without being withdrawn, unfunded contractual commitments do not necessarily represent future cash requirements. As such, the Company’s disclosure of unfunded contractual commitments includes only those which are available at the request of the portfolio company and unencumbered by milestones. As of December 31, 2020, the Company had outstanding unfunded commitments of approximately $0.1 million to one portfolio company, Dandelion, Inc. The Company will fund its future unfunded commitments from the same sources it uses to fund its investment commitments that are funded at the time they are made (which are typically through existing cash and cash equivalents and borrowings under the Credit Facility).
In the normal course of business, the Company enters into contracts that provide a variety of representations and warranties, and general indemnifications. Such contracts include those with certain service providers, brokers and trading counterparties. Any exposure to the Company under these arrangements is unknown as it would involve future
90
claims that may be made against the Company; however, based on the Company’s experience, the risk of loss is remote and no such claims are expected to occur. As such, the Company has not accrued any liability in connection with such indemnifications.
Contractual Obligations
A summary of our contractual payment obligations as of December 31, 2020, is as follows:
|
| Payments Due by Period |
|
| | ||||||||||
| | Less than 1 | | | | | | | | | | | | | |
| | year |
| 1 - 3 years |
| 4 - 5 years |
| After 5 years |
| Total | |||||
Credit Facility (2) | | $ | — | | $ | 135,000 | | $ | — | | $ | — | | $ | 135,000 |
7.00% Notes |
| | — |
| | — |
| | 125,000 |
| | — |
| | 125,000 |
Convertible Notes | | | — | | | — | | | 50,000 | | | — | | | 50,000 |
Operating Leases (1) |
| | 225 |
| | 845 |
| | 751 | | | 1,619 |
| | 3,440 |
Total Contractual Obligations | | $ | 225 | | $ | 135,845 | | $ | 175,751 | | $ | 1,619 | | $ | 313,440 |
| (1) | Relates to lease for the Company's office, which expires on July 31, 2022 and is subject to a five-year extension option, plus the lease the Company signed for a new space in downtown Phoenix, Arizona with an estimated commencement date in mid-2021. The Company has recorded the current lease as a right-of-use asset and lease liability in its financial statements, and will record the new lease as such upon its commencement date in mid-2021. No right of use asset or corresponding lease liability has been recorded on the new lease as the lease has not commenced. |
| (2) | On February 3, 2021, we repaid $90.0 million under the Credit Facility from proceeds received from the initial public offering of our common stock. See “Recent Developments.” |
Distributions
We intend to pay quarterly distributions to our stockholders out of assets legally available for distribution. All distributions will be paid at the discretion of the Board and will depend on our earnings, financial condition, maintenance of our tax treatment as a RIC, compliance with applicable BDC regulations and such other factors as the Board may deem relevant from time to time.
The following table summarizes our cash distributions per share that have been authorized by the board. All distributions represent ordinary income as the Company’s taxable earnings exceeded distributions.
Declaration Date | | Record Date | | Payment Date | | Per Share Amount | |
May 14, 2020 | | May 29, 2020 | | June 5, 2020 | | $ | 0.22 |
August 12, 2020 | | August 21, 2020 | | September 4, 2020 | | | 0.27 |
November 12, 2020 | | November 20, 2020 | | December 4, 2020 | | | 0.27 |
December 22, 2020 | | December 30, 2020 | | January 15, 2021 | | | 0.27 |
Total | | | | | | $ | 1.03 |
Related Party Transactions
As discussed herein, the Legacy Funds were merged with and into the Company and we issued 9,183,185 shares of our common stock at $15.00 per share for a total value of approximately $137.7 million and paid approximately $108.7 million in cash to the Legacy Investors, which include the general partners/managers of the Legacy Funds. In addition, as part of the Formation Transactions, we acquired 100% of the equity interests of Trinity Capital Holdings for shares of our common stock and cash. Members of our management, including Steven L. Brown, Kyle Brown, Gerald Harder and Ron Kundich, owned 100% of the equity interests in Trinity Capital Holdings and controlling interests in the general partners/managers of the Legacy Funds.
91
As a result of the Formation Transactions, Messrs. S. Brown, K. Brown, Harder and Kundich collectively received (i) 533,332 shares of the Company’s common stock valued at approximately $8.0 million and approximately $2.0 million in cash in exchange for their equity interests in Trinity Capital Holdings, and (ii) 377,441 shares of the Company’s common stock valued at approximately $5.7 million for their limited partner and general partner interests in the Legacy Funds.
We have entered into indemnification agreements with our directors and executive officers. The indemnification agreements are intended to provide our directors and executive officers with the maximum indemnification permitted under Maryland law and the 1940 Act. Each indemnification agreement provides that we shall indemnify the director or executive officer who is a party to the agreement, or an “Indemnitee,” including the advancement of legal expenses, if, by reason of his or her corporate status, the Indemnitee is, or is threatened to be, made a party to or a witness in any threatened, pending, or completed proceeding, to the maximum extent permitted by Maryland law and the 1940 Act.
Recent Developments
Initial Public Offering
On February 2, 2021, the Company completed its initial public offering of 8,006,291 shares of its common stock at a price of $14.00 per share, inclusive of the underwriters option to purchase additional shares with net proceeds of approximately $105.4 million. The Company’s shares of common stock began trading on the Nasdaq Global Select Market on January 29, 2021 under the symbol “TRIN.” Proceeds from this offering were primarily used to pay down a portion of our existing indebtedness under the Credit Facility.
Credit Facility Paydown
On February 3, 2021, the Company repaid $90.0 million of its existing indebtedness under the Credit Facility using proceeds from its initial public offering. As of March 4, 2021, the Company had $45.0 million in borrowings outstanding under the Credit Facility.
Item 7A. Quantitative and Qualitative Disclosures About Market Risk
Uncertainty with respect to the economic effects of the COVID-19 pandemic has introduced significant volatility in the financial markets, and the effect of the volatility could materially impact our market risks, including those listed below. We are subject to financial market risks, including valuation risk and interest rate risk.
Valuation Risk
Our investments may not have a readily available market price, and we value these investments at fair value as determined in good faith by the Board of Directors in accordance with our valuation policy. There is no single standard for determining fair value in good faith. As a result, determining fair value requires that judgment be applied to the specific facts and circumstances of each portfolio investment while employing a consistently applied valuation process for the types of investments we make. Due to the inherent uncertainty of determining the fair value of investments that do not have a readily available market value, the fair value of our investments may fluctuate from period to period, including as a result of the impact of the COVID-19 pandemic on the economy and financial and capital markets. Because of the inherent uncertainty of valuation, these estimated values may differ significantly from the values that would have been used had a ready market for the investments existed, and it is possible that the difference could be material.
Interest Rate Risk
Interest rate sensitivity and risk refer to the change in earnings that may result from changes in the level of interest rates. To the extent that we borrow money to make investments, including under the Credit Facility or any future financing arrangement, our net investment income will be affected by the difference between the rate at which we
92
borrow funds and the rate at which we invest these funds. In periods of rising interest rates, our cost of borrowing funds would increase, which may reduce our net investment income. As a result, there can be no assurance that a significant change in market interest rates will not have a material adverse effect on our net investment income.
As of December 31, 2020, approximately 25.3% of our debt investments at fair value represented floating-rate investments based on PRIME, and approximately 74.7% of our debt investments at fair value represented fixed-rate investments. In addition, borrowings under the Credit Facility are subject to floating interest rates based on LIBOR, generally bearing interest at a rate of the three-month LIBOR plus 3.25%.
Based on our Consolidated Statements of Operations as of December 31, 2020, the following table shows the annualized impact on net income of hypothetical base rate changes in the PRIME rate on our debt investments (considering interest rate floors for floating rate instruments) and the hypothetical base rate changes in the three-month LIBOR on our Credit Facility and there are no changes in our investment and borrowing structure (in thousands):
|
| Interest |
| Interest |
| Net | |||
| | Income | | Expense | | Income/(Loss) | |||
Up 300 basis points | | $ | 2,656 | | $ | 4,050 | | $ | (1,394) |
Up 200 basis points | | $ | 1,523 | | $ | 2,700 | | $ | (1,177) |
Up 100 basis points | | $ | 603 | | $ | 1,350 | | $ | (747) |
Down 100 basis points | | $ | — | | $ | (292) | | $ | 292 |
Down 200 basis points | | $ | — | | $ | (292) | | $ | 292 |
Down 300 basis points | | $ | — | | $ | (292) | | $ | 292 |
Currency Risk
In addition, any investments we make that are denominated in a foreign currency will be subject to risks associated with changes in currency exchange rates. These risks include the possibility of significant fluctuations in the foreign currency markets, the imposition or modification of foreign exchange controls and potential illiquidity in the secondary market. These risks will vary depending upon the currency or currencies involved. As of December 31, 2020, we had one foreign domiciled portfolio. Our exposure to currency risk related to this investment is minimal as payments from such portfolio company are received in U.S. dollars. No other investments as of December 31, 2020 were subject to currency risk.
Hedging
We do not currently engage in any hedging activities. However, we may, in the future, hedge against interest rate and currency exchange rate fluctuations by using standard hedging instruments such as futures, options and forward contracts subject to the requirements of the 1940 Act. While hedging activities may insulate us against adverse changes in interest rates, they may also limit our ability to participate in benefits of lower interest rates with respect to our portfolio of investments with fixed interest rates. We may also borrow funds in local currency as a way to hedge our non-U.S. denominated investments.
93
Item 8. Consolidated Financial Statements and Supplementary Data
INDEX TO CONSOLIDATED FINANCIAL STATEMENTS
Error! Bookmark not defined. | |
Consolidated Statements of Assets and Liabilities as of December 31, 2020 and December 31, 2019 | 96 |
97 | |
98 | |
99 | |
Consolidated Schedule of Investments as of December 31, 2020 | 101 |
115 |
94
Report of Independent Registered Public Accounting Firm
To the Shareholders and the Board of Directors of Trinity Capital Inc.
Opinion on the Financial Statements
We have audited the accompanying consolidated statement of assets and liabilities of Trinity Capital Inc. (the Company), including the consolidated schedule of investments, as of December 31, 2020 and the statement of assets and liabilities as of December 31, 2019, the related consolidated statements of operations, changes in net assets and cash flows for the year ended December 31, 2020 and for the period August 12, 2019 (date of inception) to December 31, 2019, and the related notes (collectively referred to as the “consolidated financial statements”). In our opinion, the consolidated financial statements present fairly, in all material respects, the financial position of the Company at December 31, 2020 and 2019, and the results of its operations, changes in its net assets, and its cash flows for the year ended December 31, 2020 and for the period August 12, 2019 (date of inception) to December 31, 2019, in conformity with U.S. generally accepted accounting principles.
Basis for Opinion
These financial statements are the responsibility of the Company’s management. Our responsibility is to express an opinion on the Company’s financial statements based on our audits. We are a public accounting firm registered with the Public Company Accounting Oversight Board (United States) (PCAOB) and are required to be independent with respect to the Company in accordance with the U.S. federal securities laws and the applicable rules and regulations of the Securities and Exchange Commission and the PCAOB.
We conducted our audits in accordance with the standards of the PCAOB. Those standards require that we plan and perform the audit to obtain reasonable assurance about whether the financial statements are free of material misstatement, whether due to error or fraud. The Company is not required to have, nor were we engaged to perform, an audit of the Company’s internal control over financial reporting. As part of our audits we are required to obtain an understanding of internal control over financial reporting but not for the purpose of expressing an opinion on the effectiveness of the Company’s internal control over financial reporting. Accordingly, we express no such opinion.
Our audits included performing procedures to assess the risks of material misstatement of the financial statements, whether due to error or fraud, and performing procedures that respond to those risks. Such procedures included examining, on a test basis, evidence regarding the amounts and disclosures in the financial statements. Our procedures included confirmation of investments owned as of December 31, 2020, by correspondence with the underlying investee companies, or by other appropriate auditing procedures where confirmation was not received. Our audits also included evaluating the accounting principles used and significant estimates made by management, as well as evaluating the overall presentation of the financial statements. We believe that our audits provide a reasonable basis for our opinion.
/s/ Ernst & Young LLP
We have served as the Company’s auditor since 2019.
Los Angeles, California
March 4, 2021
95
TRINITY CAPITAL INC.
Consolidated Statements of Assets and Liabilities
(In thousands, except share and per share data)
|
| December 31, |
| December 31, | ||
| | 2020 | | 2019 | ||
|
| | | | | |
ASSETS |
| |
|
| |
|
Investments at fair value: |
| |
|
| |
|
Control investments (cost of $57,072 and $0, respectively) | | $ | 48,730 | | $ | — |
Affiliate investments (cost of $20,653 and $0, respectively) | |
| 27,650 | |
| — |
Non-control / Non-affiliate investments (cost of $420,611 and $0, respectively) | |
| 417,271 | |
| — |
Total investments (cost of $498,336 and $0, respectively) | |
| 493,651 | |
| — |
Cash and cash equivalents | |
| 44,656 | |
| — |
Restricted cash | |
| 16,445 | |
| — |
Interest receivable | |
| 3,468 | |
| — |
Deferred financing costs | |
| — | |
| 3,525 |
Deferred offering costs | |
| — | |
| 2,677 |
Prepaid expenses | |
| 744 | |
| — |
Other assets | |
| 744 | |
| — |
Total assets | | $ | 559,708 | | $ | 6,202 |
| |
|
| |
|
|
LIABILITIES | |
|
| |
|
|
Credit facility, net of $2,107 and $0, respectively, of unamortized deferred financing costs | | $ | 132,893 | | $ | — |
Notes payable, net of $4,697, and $0, respectively, of unamortized deferred financing costs | |
| 120,303 | |
| — |
Convertible notes payable, net of $3,448, and $0, respectively, of unamortized deferred financing costs and discount | | | 46,552 | | | |
Accounts payable and accrued liabilities | |
| 7,309 | |
| 5,668 |
Due to related party | |
| — | |
| 1,058 |
Distribution payable | | | 4,947 | | | |
Other liabilities | |
| 8,956 | |
| — |
Total liabilities | |
| 320,960 | |
| 6,726 |
| |
|
| |
|
|
Commitments and contingencies (Note 6) | |
|
| |
|
|
| |
|
| |
|
|
NET ASSETS | |
|
| |
|
|
Common stock, $0.001 par value per share (200,000,000 authorized, 18,321,274 and 10 shares issued and outstanding as of December 31, 2020 and December 31, 2019, respectively) | |
| 18 | |
| — |
Paid-in capital in excess of par | |
| 263,366 | |
| — |
Distributable earnings/(accumulated loss) | |
| (24,636) | |
| (524) |
Total net assets | |
| 238,748 | |
| (524) |
Total liabilities and net assets | | $ | 559,708 | | $ | 6,202 |
NET ASSET VALUE PER SHARE | | $ | 13.03 | | $ | (52,418.20) |
See accompanying notes to consolidated financial statements.
96
TRINITY CAPITAL INC.
Consolidated Statements of Operations
(In thousands, except share and per share data)
|
| | | | For the Period | |
| | For the | | of August 12, 2019 | ||
| | Year Ended | | (date of inception) | ||
|
| December 31, 2020 |
| to December 31, 2019 | ||
INVESTMENT INCOME: |
| |
| | |
|
Interest income: |
| |
| | |
|
Control investments | | $ | 3,661 | | $ | — |
Affiliate investments | |
| 1,191 | |
| — |
Non-Control / Non-Affiliate investments | |
| 46,403 | |
| — |
Total interest income | | | 51,255 | | | — |
Fee income: | | | | | | |
Non-Control / Non-Affiliate investments | | | 3,709 | | | — |
Total fee income | | | 3,709 | | | — |
Total investment income | |
| 54,964 | |
| — |
| |
|
| |
|
|
EXPENSES: | |
|
| |
|
|
Interest expense and other debt financing costs | |
| 16,773 | |
| — |
Compensation and benefits | |
| 10,433 | |
| — |
Professional fees | | | 2,283 | | | — |
General and administrative | |
| 2,104 | |
| 524 |
Total expenses | |
| 31,593 | |
| 524 |
| |
|
| |
|
|
NET INVESTMENT INCOME | |
| 23,371 | |
| (524) |
| |
|
| |
|
|
NET REALIZED GAIN/(LOSS) FROM INVESTMENTS: | |
|
| |
|
|
Control investments | |
| — | |
| — |
Affiliate investments | |
| — | |
| — |
Non-Control / Non-Affiliate investments | |
| (9,403) | |
| — |
Net realized loss from investments | |
| (9,403) | |
| — |
| |
|
| |
|
|
NET CHANGE IN UNREALIZED APPRECIATION/(DEPRECIATION) FROM INVESTMENTS: | |
|
| |
|
|
Control investments | |
| (8,342) | |
| — |
Affiliate investments | |
| 6,997 | |
| — |
Non-Control / Non-Affiliate investments | |
| (3,621) | |
| — |
Net change in unrealized appreciation/(depreciation) from investments | |
| (4,966) | |
| — |
| |
|
| |
|
|
NET INCREASE/(DECREASE) IN NET ASSETS RESULTING FROM OPERATIONS BEFORE FORMATION COSTS | |
| 9,002 | |
| (524) |
Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds | |
| (15,114) | |
| — |
NET INCREASE/(DECREASE) IN NET ASSETS RESULTING FROM OPERATIONS | | $ | (6,112) | | $ | (524) |
| |
|
| |
|
|
NET INVESTMENT INCOME PER SHARE - BASIC AND DILUTED | | $ | 1.29 | | $ | N/M |
| |
|
| |
|
|
NET INCREASE/(DECREASE) IN NET ASSETS RESULTING FROM OPERATIONS PER SHARE - BASIC AND DILUTED | | $ | (0.34) | | | N/M |
| |
|
| |
|
|
WEIGHTED AVERAGE SHARES OUTSTANDING - BASIC AND DILUTED | |
| 18,092,494 | |
| 10 |
N/M – not material
See accompanying notes to consolidated financial statements.
97
TRINITY CAPITAL INC.
Consolidated Statements of Changes in Net Assets
(In thousands, except share and per share data)
|
| |
| | |
| | |
| Distributable |
| | | |
| | | | | | | Paid In Capital | | Earnings | | | | ||
| | Common Stock | | in Excess of | | (Accumulated | | Total | ||||||
| | Shares | | Par Value | | Par Value | | Loss) | | Net Assets | ||||
Balance as of August 12, 2019 (date of inception) |
| — | | $ | — | | $ | — | | $ | — | | $ | — |
Issuance of common stock, net of issuance costs |
| 10 | |
| — | |
| — | |
| — | |
| — |
Net increase/(decrease) in net assets resulting from operations: |
|
| |
|
| |
|
| |
|
| |
| |
Net investment income/(loss) |
| — | |
| — | |
| — | |
| (524) | |
| (524) |
Balance as of December 31, 2019 |
| 10 | | | — | | | — | | | (524) | | | (524) |
Issuance of shares related to Formation Transaction (1) |
| 9,716,517 | |
| 10 | |
| 145,738 | |
| — | |
| 145,748 |
Issuance of common stock, net of issuance costs |
| 8,333,333 | |
| 8 | |
| 114,463 | |
| — | |
| 114,471 |
Distributions to stockholders | | — | |
| — | |
| — | | | (18,738) | | | (18,738) |
Net increase/(decrease) in net assets resulting from operations: |
|
| |
|
| |
|
| |
|
| |
| |
Net investment income/(loss) |
| — | |
| — | |
| — | |
| 23,371 | |
| 23,371 |
Net realized gain/(loss) from investments |
| — | |
| — | |
| — | |
| (9,403) | |
| (9,403) |
Net unrealized appreciation/(depreciation) from investments |
| — | |
| — | |
| — | |
| (4,966) | |
| (4,966) |
Equity component of convertible notes | | — | | | — | | | 462 | | | — | | | 462 |
Issuance of common stock pursuant to distribution reinvestment plan | | 271,414 | | | — | | | 3,441 | | | — | | | 3,441 |
Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds |
| — | |
| — | |
| — | |
| (15,114) | |
| (15,114) |
Tax reclassification | | — | | | — | | | (738) | | | 738 | | | — |
Balance as of December 31, 2020 |
| 18,321,274 | | $ | 18 | | $ | 263,366 | | $ | (24,636) | | $ | 238,748 |
| (1) | See “Note 1 - Organization and Basis of Presentation.” |
See accompanying notes to consolidated financial statements.
98
TRINITY CAPITAL INC.
Consolidated Statement of Cash Flows
(In thousands)
|
| | |
| For the Period August 12, 2019 | |
| | For the Year Ended | | (date of inception) | ||
|
| December 31, 2020 |
| to December 31, 2019 | ||
Cash flows from operating activities: |
| |
|
| |
|
Net decrease in net assets resulting from operations | | $ | (6,112) | | $ | (524) |
Adjustments to reconcile net decrease in net assets resulting from operations to net cash provided by/(used in) operating activities: | |
|
| |
|
|
Purchase of investments, net of deferred fees of $1.4 million | |
| (239,827) | |
| — |
Proceeds from sales and paydowns of investments | |
| 160,901 | |
| — |
Net change in unrealized depreciation from investments | |
| 4,966 | |
| — |
Net realized gain/(loss) from investments | |
| 9,403 | |
| — |
Accretion of original issue discounts and end of term payments on investments | |
| (11,788) | |
| — |
Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds | |
| 15,114 | |
| — |
Amortization of deferred financing costs | |
| 3,025 | |
| — |
Depreciation of fixed assets | |
| 50 | |
| — |
Change in operating assets and liabilities | |
| | |
|
|
Increase in interest receivable | |
| (2,355) | |
| — |
Increase in prepaid expenses | | | (608) | | | — |
Increase in other assets | |
| (331) | |
| — |
Increase in accounts payable and accrued liabilities | |
| 6,003 | |
| 384 |
Increase/(Decrease) in due to related party | |
| (1,058) | |
| 140 |
Increase in other liabilities | |
| 4,391 | |
| — |
Net cash used in operating activities | |
| (58,226) | |
| — |
| |
|
| |
|
|
Cash flows used in investing activities: | |
| | |
|
|
Formation Transactions of Legacy Funds, net of cash acquired (1) | |
| (89,515) | |
| — |
Acquisition of Trinity Capital Holdings | |
| (2,211) | |
| — |
Acquisition of fixed assets | |
| (253) | |
| — |
Net cash used in investing activities | |
| (91,979) | |
| — |
| |
|
| |
|
|
Cash flows provided by/(used in) financing activities | |
|
| |
|
|
Issuance of common stock | |
| 125,000 | |
| — |
Common stock issuance costs | |
| (10,529) | |
| — |
Distributions paid | |
| (10,350) | |
| — |
Proceeds from issuance of convertible notes, net of original issue discount | | | 48,688 | | | |
Financing costs paid related to convertible notes | |
| (1,703) | |
| — |
Proceeds from issuance of notes payable | |
| 125,000 | |
| — |
Financing costs paid related to notes payable | |
| (5,775) | |
| — |
Proceeds under credit facility | | | 30,000 | | | — |
Repayments under credit facility | |
| (85,000) | |
| — |
Financing costs paid related to credit facility | |
| (4,025) | |
| — |
Net cash provided by financing activities | |
| 211,306 | |
| — |
| |
|
| |
|
|
Net increase in cash, cash equivalents and restricted cash | |
| 61,101 | |
| — |
Cash, beginning of period | |
| — | |
| — |
Cash, cash equivalents and restricted cash at end of period | | $ | 61,101 | | $ | — |
99
| |
|
| |
|
|
| | | |
| For the Period August 12, 2019 | |
| | For the Year Ended | | (date of inception) | ||
| | December 31, 2020 |
| to December 31, 2019 | ||
Supplemental and non-cash investing and financing activities: | | | | | | |
Cash paid for interest | | $ | 12,856 | | $ | — |
Shares issued to Trinity Capital Holdings (1) | | $ | 8,000 | | $ | — |
Assumption of severance liability (1) | | $ | 3,508 | | $ | — |
Shares issued to the Legacy Investors as part of the Formation Transactions (1) | | $ | 137,748 | | $ | — |
Issuance of common stock pursuant to distribution reinvestment plan | | $ | 3,441 | | $ | — |
Non-cash settlement of investments | | $ | 1,262 | | $ | — |
Deferred offering costs | | $ | — | | $ | 2,677 |
Deferred financing cost | | | — | | | 3,525 |
| | $ | — | | $ | 6,202 |
Due to related party for offering and financing cost | | $ | — | | $ | 918 |
Accounts payable and accrued liabilities | | | — | | | 5,284 |
| | $ | — | | $ | 6,202 |
The following table provides a reconciliation of cash and cash equivalents and restricted cash reported within the Consolidated Statements of Assets and Liabilities that sum to the total of the same such amounts on the Consolidated Statement of Cash Flows:
| | As of December 31, | ||||
|
| 2020 |
| 2019 | ||
Cash and cash equivalents | | $ | 44,656 | | $ | — |
Restricted cash | | | 16,445 | | | — |
Total cash, cash equivalents and restricted cash shown in the Consolidated Statements of Cash Flows | | $ | 61,101 | | $ | — |
| (1) | See Formation Transactions under “Note 1 - Organization and Basis of Presentation” |
See accompanying notes to consolidated financial statements.
100
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of Investment (3) |
| Maturity Date |
| Interest Rate (4) |
| Principal |
| Cost |
| Fair Value (6) | |||
Debt Securities | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | |
Administrative and Support and Waste Management and Remediation (2) |
| |
| | |
| | |
| | |
| |||
SeaOn Environmental, LLC | | Equipment Financing | | January 1, 2023 | | Fixed interest rate 9.0%; EOT 12.0% | | $ | 2,134 | | $ | 2,370 | | $ | 2,328 |
| | | | | | | | | | | | | | | |
Sub-total: Administrative and Support and Waste Management and Remediation (1.0%)* |
| | $ | 2,134 | | $ | 2,370 | | $ | 2,328 | |||||
| | | | | | | | | | | | | | | |
Agriculture, Forestry, Fishing and Hunting (2) | |
| |
| |
| |
|
| |
|
| |
|
|
Bowery Farming, Inc. | | Equipment Financing | | January 1, 2023 | | Fixed interest rate 8.5%; EOT 8.5% | | $ | 2,481 | | $ | 2,742 | | $ | 2,574 |
| | Equipment Financing | | February 1, 2023 | | Fixed interest rate 8.7%; EOT 8.5% | |
| 2,453 | |
| 2,650 | |
| 2,684 |
| | Equipment Financing | | May 1, 2023 | | Fixed interest rate 8.7%; EOT 8.5% | |
| 3,054 | |
| 3,259 | |
| 3,303 |
| | Equipment Financing | | January 1, 2024 | | Fixed interest rate 7.5%; EOT 8.5% | | | 10,000 | | | 9,912 | | | 9,912 |
Total Bowery Farming, Inc. | | | | | |
| |
| 17,988 | |
| 18,563 | |
| 18,473 |
| | | | | | | | | | | | | | | |
Robotany, Inc. |
| Equipment Financing | | January 1, 2024 |
| Fixed interest rate 7.6%; EOT 22.0% | | $ | 1,667 |
| $ | 1,720 |
| $ | 1,709 |
| | | | | | | | | | | | | | | |
Sub-total: Agriculture, Forestry, Fishing and Hunting (8.5%)* | | |
| | $ | 19,655 | | $ | 20,283 | | $ | 20,182 | |||
| | | | | | | | | | | | | | | |
Construction | |
| |
| |
| |
|
| |
|
| |
|
|
Dandelion Energy, Inc. |
| Equipment Financing | | April 1, 2024 |
| Fixed interest rate 9.0%; EOT 12.5% | | $ | 460 | | $ | 467 | | $ | 471 |
| | Equipment Financing | | November 1, 2024 | | Fixed interest rate 9.2%; EOT 12.5% | | | 545 | | | 551 | | | 551 |
| | Equipment Financing (14) | | December 1, 2024 | | Fixed interest rate 9.1%; EOT 12.5% | | | 558 | | | 563 | | | 563 |
| | Equipment Financing | | January 1, 2025 | | Fixed interest rate 9.2%; EOT 12.5% | | | 791 | | | 791 | | | 791 |
Total Dandelion Energy, Inc. | | | | | | | | | 2,354 | | | 2,372 | | | 2,376 |
| | | | | | | | | | | | | | | |
Project Frog, Inc. (7) | | Secured Loan | | May 1, 2023 | | Fixed interest rate 12.0% | | $ | 4,128 | | $ | 4,045 | | $ | 4,029 |
| | | | | | | | | | | | | | | |
Sub-total: Construction (2.7%)* | | | | | |
| | $ | 6,482 | | $ | 6,417 | | $ | 6,405 |
| | | | | | | | | | | | | | | |
Educational Services (2) | | | | | | | | | | | | | | | |
Examity, Inc. | | Secured Loan | | February 1, 2022 | | Fixed interest rate 11.5%; EOT 8.0% | | $ | 3,280 | | $ | 4,028 | | $ | 3,994 |
| | Secured Loan | | February 1, 2022 | | Fixed interest rate 11.5%; EOT 4.0% | |
| 3,516 | |
| 1,775 | |
| 1,775 |
| | Secured Loan | | January 1, 2023 | | Fixed interest rate 12.25%; EOT 4.0% | |
| 1,658 | |
| 1,005 | |
| 1,004 |
Total Examity, Inc. | | | | | |
| |
| 8,454 | | | 6,808 | |
| 6,773 |
| | | | | | | | | | | | | | | |
Qubed, Inc. dba Yellowbrick | | Secured Loan | | October 1, 2023 | | Variable interest rate PRIME + 8.3% or Floor rate 11.5%; EOT 5.0% (9) | | $ | 1,906 | | $ | 1,950 | | $ | 1,957 |
| | Secured Loan | | October 1, 2023 | | Fixed interest rate 11.5%; EOT 4.0% | |
| 476 | |
| 481 | |
| 493 |
Total Qubed, Inc. dba Yellowbrick | | | | | |
| |
| 2,382 | | | 2,431 | |
| 2,450 |
| | | | | | | | | | | | | | | |
Sub-total: Educational Services (3.9%)* | | | | |
|
| | $ | 10,836 | | $ | 9,239 | | $ | 9,223 |
101
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of Investment (3) |
| Maturity Date |
| Interest Rate (4) |
| Principal |
| Cost |
| Fair Value (6) | |||
| | | | | | | | | | | | | | | |
Debt Securities, Continued | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | |
Finance and Insurance (2) | |
| |
|
|
| |
|
| |
|
| |
|
|
DailyPay, Inc. | | Secured Loan | | November 1, 2024 | | Variable interest rate PRIME + 7.0% or Floor rate 12.0%; EOT 6.0% (9) | | $ | 20,000 | | $ | 19,800 | | $ | 20,062 |
| | Secured Loan | | January 1, 2025 | | Variable interest rate PRIME + 7.0% or Floor rate 12.0%; EOT 6.0% (9) | | | 5,000 | | | 4,939 | | | 4,939 |
Total DailyPay, Inc. | | | | | | | | | 25,000 | | | 24,739 | | | 25,001 |
| | | | | | | | | | | | | | | |
Petal Card, Inc. | | Secured Loan | | December 1, 2023 |
| Fixed interest rate 11.0%; EOT 3.0% | | $ | 10,000 | | $ | 9,998 | | $ | 10,116 |
| | | | | | | | | | | | | | | |
Sub-total: Finance and Insurance (14.7%)* | | | | |
|
| | $ | 35,000 | | $ | 34,737 | | $ | 35,117 |
| | | | | | | | | | | | | | | |
Health Care and Social Assistance (2) | |
| | |
|
| |
|
| |
|
| |
|
|
Lark Technologies, Inc. | | Secured Loan | | April 1, 2025 | | Variable interest rate PRIME + 8.3% or Floor rate 11.5%; EOT 4.0% (9) | | $ | 5,000 | | $ | 4,809 | | $ | 4,874 |
| | | | | | | | | | | | | | | |
WorkWell Prevention & Care Inc. | | Secured Loan | | March 1, 2024 |
| Fixed interest rate 8.0%; EOT 10.0% | | $ | 3,370 | | $ | 3,608 | | $ | 3,493 |
| | Secured Loan | | March 1, 2024 |
| Fixed interest rate 8.0%; EOT 10.0% | |
| 700 | |
| 734 | |
| 693 |
Total WorkWell Prevention & Care Inc. (7) | | | | |
|
| |
| 4,070 | |
| 4,342 | |
| 4,186 |
| | | | | | | | | | | | | | | |
Sub-total: Health Care and Social Assistance (3.8%)* | | | | |
|
| | $ | 9,070 | | $ | 9,151 | | $ | 9,060 |
| | | | | | | | | | | | | | | |
Information (2) | |
| | |
|
| |
|
| |
|
| |
|
|
Firefly Systems, Inc. | | Equipment Financing | | February 1, 2023 |
| Fixed interest rate 9.0%; EOT 10.0% | | $ | 3,946 | | $ | 4,080 | | $ | 4,052 |
| | Equipment Financing | | September 1, 2023 | | Fixed interest rate 9.0%; EOT 10.0% | | | 3,208 | | | 3,308 | | | 3,307 |
| | Equipment Financing | | October 1, 2023 | | Fixed interest rate 9.0%; EOT 10.0% | | | 386 | | | 396 | | | 396 |
Total Firefly Systems, Inc. | | | | | | | | | 7,540 | | | 7,784 | | | 7,755 |
| | | | | | | | | | | | | | | |
Gobiquity, Inc. | | Equipment Financing | | April 1, 2022 |
| Fixed interest rate 7.5%; EOT 20.0% | | $ | 296 | | $ | 394 | | $ | 395 |
| | | | | | | | | | | | | | | |
Hytrust, Inc. | | Secured Loan | | February 1, 2021 |
| Fixed interest rate 11.1%; EOT 10.5% | | $ | 194 | | $ | 717 | | $ | 621 |
| | | | | | | | | | | | | | | |
Oto Analytics, Inc. |
| Secured Loan | | March 1, 2023 |
| Fixed interest rate 11.5%; EOT 6.0% | | $ | 7,294 |
| $ | 7,755 |
| $ | 7,735 |
| | | | | | | | | | | | | | | |
RapidMiner, Inc. |
| Secured Loan | | April 1, 2024 |
| Fixed interest rate 12.0%; EOT 7.5% | | $ | 10,000 |
| $ | 10,099 |
| $ | 10,113 |
| | | | | | | | | | | | | | | |
Smule, Inc. | | Secured Loan | | January 1, 2022 |
| Fixed interest rate 0.0% (17) | | $ | 145 | | $ | 145 | | $ | 145 |
| | | | | | | | | | | | | | | |
STS Media, Inc. (11) |
| Secured Loan | | May 1, 2022 |
| Fixed interest rate 11.9%; EOT 4.0% | | $ | 7,811 |
| $ | 737 |
| $ | 100 |
| | | | | | | | | | | | | | | |
Unitas Global, Inc. |
| Equipment Financing | | July 1, 2021 |
| Fixed interest rate 9.0%; EOT 12.0% | | $ | 580 |
| $ | 938 |
| $ | 921 |
|
| Equipment Financing | | April 1, 2021 |
| Fixed interest rate 7.8%; EOT 6.0% | | | 53 |
| | 76 |
| | 74 |
Total Unitas Global, Inc. | | | | |
|
| | | 633 |
| | 1,014 | |
| 995 |
| | | | | | | | | | | | | | | |
Sub-total: Information (11.7%)* | | | | |
|
| | $ | 33,913 | | $ | 28,645 | | $ | 27,859 |
102
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of Investment (3) |
| Maturity Date |
| Interest Rate (4) |
| Principal |
| Cost |
| Fair Value (6) | |||
Debt Securities, Continued | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | |
Manufacturing (2) | |
| |
|
|
| | |
|
| |
|
| |
|
AyDeeKay LLC | | Secured Loan | | August 1, 2024 |
| Variable interest rate PRIME + 7.5% or Floor rate 10.8%; EOT 3.0% (9) | | $ | 12,000 | | $ | 11,893 | | $ | 11,779 |
| | | | | | | | | | | | | | | |
BHCosmetics, LLC | | Equipment Financing | | March 1, 2021 |
| Fixed interest rate 8.9%; EOT 5.0% | | $ | 106 | | $ | 165 | | $ | 165 |
| | Equipment Financing | | April 1, 2021 |
| Fixed interest rate 8.7%; EOT 5.0% | |
| 159 | |
| 217 | |
| 218 |
Total BHCosmetics, LLC | | | | | | | |
| 265 | |
| 382 | |
| 383 |
| | | | | | | | | | | | | | | |
Footprint International Holding, Inc. |
| Equipment Financing | | March 1, 2024 |
| Fixed interest rate 10.3%; EOT 8.0% | | $ | 14,771 |
| $ | 15,244 |
| $ | 15,352 |
| | Secured Loan | | July 1, 2024 | | Fixed interest rate 12.0%; EOT 9.0% | | | 7,000 | | | 7,095 | | | 7,177 |
Total Footprint International Holding, Inc. | | | | | | | | | 21,771 | | | 22,339 | | | 22,529 |
| | | | | | | | | | | | | | | |
Happiest Baby, Inc. | | Equipment Financing | | September 1, 2022 |
| Fixed interest rate 8.4%; EOT 9.5% | | $ | 924 | | $ | 1,031 | | $ | 998 |
| | Equipment Financing | | November 1, 2022 |
| Fixed interest rate 8.6%; EOT 9.5% | |
| 748 | |
| 822 | |
| 830 |
| | Equipment Financing | | January 1, 2023 |
| Fixed interest rate 8.6%; EOT 9.5% | |
| 719 | |
| 775 | |
| 786 |
| | Equipment Financing | | June 1, 2023 |
| Fixed interest rate 8.2%; EOT 9.5% | |
| 901 | |
| 953 | |
| 955 |
| | Equipment Financing | | January 1, 2024 | | Fixed interest rate 7.8%; EOT 9.5% | | | 1,248 | | | 1,270 | | | 1,278 |
Total Happiest Baby, Inc. | | | | |
|
| |
| 4,540 | |
| 4,851 | |
| 4,847 |
| | | | | | | | | | | | | | | |
Health-Ade, LLC | | Equipment Financing | | February 1, 2022 |
| Fixed interest rate 9.4%; EOT 15.0% | | $ | 1,361 | | $ | 1,887 | | $ | 1,877 |
| | Equipment Financing | | April 1, 2022 |
| Fixed interest rate 8.6%; EOT 15.0% | |
| 784 | |
| 1,031 | |
| 1,030 |
| | Equipment Financing | | July 1, 2022 |
| Fixed interest rate 9.1%; EOT 15.0% | |
| 1,956 | |
| 2,436 | |
| 2,441 |
Total Health-Ade, LLC |
|
|
|
|
|
|
| | 4,101 |
| | 5,354 |
| | 5,348 |
| | | | | | | | | | | | | | | |
Mainspring Energy, Inc. | | Secured Loan | | August 1, 2023 | | Fixed interest rate 11.0%; EOT 3.8% | | $ | 8,592 | | $ | 8,759 | | $ | 8,801 |
| | Secured Loan | | December 1, 2024 | | Fixed interest rate 11.0%; EOT 3.8% | | | 5,500 | | | 5,267 | | | 5,267 |
Total Mainspring Energy, Inc. | | | | | | | | | 14,092 | | | 14,026 | | | 14,068 |
| | | | | | | | | | | | | | | |
Miyoko's Kitchen |
| Equipment Financing | | September 1, 2022 |
| Fixed interest rate 8.8%; EOT 9.0% | | $ | 580 | | $ | 617 | | $ | 618 |
| | Equipment Financing | | March 1, 2023 | | Fixed interest rate 8.9%; EOT 9.0% | | | 867 | | | 889 | | | 896 |
Total Miyoko's Kitchen | | | | | | | | | 1,447 | | | 1,506 | | | 1,514 |
| | | | | | | | | | | | | | | |
Molekule, Inc. | | Equipment Financing | | January 1, 2024 | | Fixed interest rate 8.8%; EOT 10.0% | | $ | 2,526 | | $ | 2,571 | | $ | 2,588 |
| | Equipment Financing | | April 1, 2024 | | Fixed interest rate 9.0%; EOT 10.0% | | | 542 | | | 550 | | | 554 |
| | Equipment Financing | | July 1, 2024 | | Fixed interest rate 8.8%; EOT 10.0% | | | 879 | | | 879 | | | 881 |
Total Molekule, Inc. | | | | | | | | | 3,947 | | | 4,000 | | | 4,023 |
| | | | | | | | | | | | | | | |
Second Nature Brands, Inc. | | Equipment Financing | | April 1, 2024 | | Fixed interest rate 9.7%; EOT 11.50% | | $ | 2,196 | | $ | 2,157 | | $ | 2,144 |
| | | | | | | | | | | | | | | |
Store Intelligence, Inc. (8) | | Secured Loan | | June 1, 2024 |
| Fixed interest rate 12.0%; EOT 7.8% | | $ | 12,001 | | $ | 12,232 | | $ | 11,884 |
| | | | | | | | | | | | | | | |
The Fynder Group, Inc. | | Equipment Financing | | May 1, 2024 | | Fixed interest rate 9.1%; EOT 10.0% | | $ | 612 | | $ | 604 | | $ | 604 |
| | | | | | | | | | | | | | | |
Vertical Communications, Inc. |
| Secured Loan | | November 1, 2024 |
| Fixed interest rate 9.5%; EOT 26.4% | | $ | 12,000 |
| $ | 12,937 |
| $ | 12,787 |
| | Secured Loan | | July 1, 2022 | | Fixed interest rate 9.5% | | | 807 | | | 807 | | | 816 |
Total Vertical Communications, Inc. (7) | | | | | | | |
| 12,807 | |
| 13,744 | |
| 13,603 |
| | | | | | | | | | | | | | | |
Sub-total: Manufacturing (38.9%)* |
|
| |
|
|
| | $ | 89,779 | | $ | 93,088 | | $ | 92,726 |
103
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of Investment (3) |
| Maturity Date |
| Interest Rate (4) |
| Principal |
| Cost |
| Fair Value (6) | |||
Debt Securities, Continued | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | |
Pharmaceutical (2) |
|
| |
|
|
| |
|
| |
|
| |
|
|
Zosano Pharma Corporation |
| Equipment Financing | | April 1, 2022 |
| Fixed interest rate 9.4%; EOT 12.0% | | $ | 2,256 |
| $ | 2,756 |
| $ | 2,530 |
|
| Equipment Financing | | July 1, 2022 |
| Fixed interest rate 9.7%; EOT 12.0% | | | 1,501 |
| | 1,757 |
| | 1,642 |
|
| Equipment Financing | | January 1, 2023 |
| Fixed interest rate 9.9%; EOT 12.0% | | | 1,608 |
| | 1,769 |
| | 1,710 |
|
| Equipment Financing | | April 1, 2023 |
| Fixed interest rate 9.9%; EOT 12.0% | | | 1,787 |
| | 1,919 |
| | 1,884 |
|
| Equipment Financing | | May 1, 2023 |
| Fixed interest rate 10.5%; EOT 12.0% | | | 1,316 |
| | 1,420 |
| | 1,384 |
Total Zosano Pharma Corporation |
|
| |
|
|
| | | 8,468 |
| | 9,621 |
| | 9,150 |
| | | | | | | | | | | | | | | |
Sub-total: Pharmaceutical (3.8%)* |
|
| |
|
|
| | $ | 8,468 | | $ | 9,621 | | $ | 9,150 |
| | | | | | | | | | | | | | | |
Professional, Scientific, and Technical Services (2) |
|
| |
|
|
| |
|
| |
|
| |
|
|
Augmedix, Inc. |
| Secured Loan | | April 1, 2023 |
| Fixed interest rate 12.0%; EOT 6.5% | | $ | 9,422 | | $ | 9,602 | | $ | 9,629 |
| | | | | | | | | | | | | | | |
BackBlaze, Inc. |
| Equipment Financing | | January 1, 2023 |
| Fixed interest rate 7.2%; EOT 11.5% | | $ | 907 | | $ | 1,042 | | $ | 1,046 |
|
| Equipment Financing | | April 1, 2023 |
| Fixed interest rate 7.4%; EOT 11.5% | |
| 117 | |
| 131 | |
| 132 |
|
| Equipment Financing | | June 1, 2023 |
| Fixed interest rate 7.4%; EOT 11.5% | |
| 905 | |
| 1,001 | |
| 1,006 |
|
| Equipment Financing | | August 1, 2023 |
| Fixed interest rate 7.5%; EOT 11.5% | |
| 180 | |
| 196 | |
| 197 |
|
| Equipment Financing | | September 1, 2023 |
| Fixed interest rate 7.7%; EOT 11.5% | |
| 185 | |
| 201 | |
| 201 |
|
| Equipment Financing | | October 1, 2023 |
| Fixed interest rate 7.5%; EOT 11.5% | |
| 186 | |
| 200 | |
| 201 |
|
| Equipment Financing | | November 1, 2023 |
| Fixed interest rate 7.2%; EOT 11.5% | |
| 621 | |
| 670 | |
| 670 |
|
| Equipment Financing | | December 1, 2023 |
| Fixed interest rate 7.5%; EOT 11.5% | | | 822 |
| | 881 |
| | 881 |
|
| Equipment Financing | | January 1, 2024 |
| Fixed interest rate 7.4%; EOT 11.5% | | | 717 |
| | 764 |
| | 763 |
|
| Equipment Financing | | February 1, 2024 |
| Fixed interest rate 7.4%; EOT 11.5% | | | 732 |
| | 775 |
| | 775 |
|
| Equipment Financing | | March 1, 2024 |
| Fixed interest rate 7.2%; EOT 11.5% | | | 636 |
| | 673 |
| | 672 |
|
| Equipment Financing | | April 1, 2024 |
| Fixed interest rate 7.4%; EOT 11.5% | | | 192 |
| | 201 |
| | 206 |
| | Equipment Financing | | May 1, 2024 | | Fixed interest rate 7.3%; EOT 11.5% | | | 1,246 | | | 1,303 | | | 1,311 |
| | Equipment Financing | | August 1, 2024 | | Fixed interest rate 7.5%; EOT 11.5% | | | 1,336 | | | 1,374 | | | 1,378 |
| | Equipment Financing | | October 1, 2024 | | Fixed interest rate 7.2%; EOT 11.5% | | | 239 | | | 243 | | | 237 |
Total BackBlaze, Inc. |
|
| |
|
|
|
| | 9,021 |
| | 9,655 |
| | 9,676 |
| | | | | | | | | | | | | | | |
Cuebiq, Inc. |
| Secured Loan | | April 1, 2024 |
| Variable interest rate PRIME + 7.3% or Floor rate 12.0%; EOT 4.5% (9) |
| $ | 5,000 |
| $ | 5,030 |
| $ | 4,963 |
| | | | | | | | | | | | | | | |
Edeniq, Inc. |
| Secured Loan | | September 1, 2021 |
| Fixed interest rate 13.0%; EOT 9.5% | | $ | 3,039 |
| $ | 1,102 |
| $ | 859 |
|
| Secured Loan | | September 1, 2021 |
| Fixed interest rate 13.0%; EOT 9.5% | | | 2,282 |
| | 762 |
| | 648 |
Total Edeniq, Inc. (7) (11) |
|
| |
|
|
| | | 5,321 |
| | 1,864 |
| | 1,507 |
| | | | | | | | | | | | | | | |
104
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of Investment (3) |
| Maturity Date |
| Interest Rate (4) |
| Principal |
| Cost |
| Fair Value (6) | |||
Debt Securities, Continued | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | |
Professional, Scientific, and Technical Services, Continued |
|
|
| |
|
| |
|
| |
|
| |||
Incontext Solutions, Inc. |
| Secured Loan | | October 1, 2023 |
| Fixed interest rate 11.75%; EOT 11.4% | | $ | 7,149 |
| $ | 7,401 |
| $ | 6,998 |
| | | | | | | | | | | | | | | |
Matterport, Inc. |
| Secured Loan | | May 1, 2022 |
| Fixed interest rate 11.5%; EOT 5.0% | | $ | 4,870 |
| $ | 5,560 |
| $ | 5,599 |
| | | | | | | | | | | | | | | |
Pendulum Therapeutics, Inc. |
| Equipment Financing | | May 1, 2023 |
| Fixed interest rate 7.7%; EOT 5.0% | | $ | 347 |
| $ | 338 |
| $ | 338 |
|
| Equipment Financing | | August 1, 2023 |
| Fixed interest rate 7.8%; EOT 5.0% | | | 2,084 |
| | 2,147 |
| | 2,164 |
|
| Equipment Financing | | October 1, 2023 |
| Fixed interest rate 7.7%; EOT 5.0% | | | 616 |
| | 620 |
| | 626 |
| | Equipment Financing | | February 1, 2024 | | Fixed interest rate 9.8%; EOT 6.0% | | | 894 | | | 895 | | | 881 |
Total Pendulum Therapeutics, Inc. |
|
| |
|
|
| | | 3,941 | | | 4,000 | | | 4,009 |
| | | | | | | | | | | | | | | |
Reciprocity, Inc. |
| Secured Loan | | October 1, 2024 |
| Variable interest rate PRIME + 8.0% or Floor rate 11.3%; EOT 2.0% (9) | | $ | 10,000 |
| $ | 9,862 |
| $ | 9,805 |
| | | | | | | | | | | | | | | |
Sun Basket, Inc. | | Secured Loan | | December 1, 2024 | | Variable interest rate PRIME + 8.5% or Floor rate 11.8%; EOT 5.0% (9) | | | 18,375 | | | 17,831 | | | 17,831 |
| | | | | | | | | | | | | | | |
Utility Associates, Inc. (11) |
| Secured Loan | | October 1, 2023 |
| Fixed interest rate 11.0% | | $ | 750 |
| $ | 830 |
| $ | 604 |
| | | | | | | | | | | | | | | |
Sub-total: Professional, Scientific, and Technical Services (29.6%)* |
|
| | $ | 73,849 | | $ | 71,635 | | $ | 70,621 | ||||
105
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of Investment (3) |
| Maturity Date |
| Interest Rate (4) |
| Principal |
| Cost |
| Fair Value (6) | |||
Debt Securities, Continued | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | |
Real Estate (2) |
|
|
|
|
|
| | |
|
| |
|
| |
|
Knockaway, Inc. |
| Secured Loan | | December 1, 2023 |
| Fixed interest rate 11.0%; EOT 3.0% | | $ | 10,000 | | $ | 10,103 | | $ | 10,112 |
|
| Secured Loan | | February 1 , 2024 |
| Fixed interest rate 11.0%; EOT 3.0% | |
| 2,500 | |
| 2,519 | |
| 2,549 |
|
| Secured Loan | | March 1, 2024 |
| Fixed interest rate 11.0%; EOT 3.0% | |
| 2,500 | |
| 2,516 | |
| 2,548 |
Total Knockaway, Inc. |
|
| |
|
|
| |
| 15,000 | |
| 15,138 | |
| 15,209 |
| | | | | | | | | | | | | | | |
Wanderjaunt, Inc. |
| Equipment Financing | | June 1, 2023 |
| Fixed interest rate 10.2%; EOT 12.0% | | $ | 387 | | $ | 388 | | $ | 380 |
|
| Equipment Financing | | August 1, 2023 |
| Fixed interest rate 10.2%; EOT 12.0% | |
| 1,230 | |
| 1,313 | |
| 1,296 |
Total Wanderjaunt, Inc. |
|
| |
|
|
| |
| 1,617 | |
| 1,701 | |
| 1,676 |
| | | | | | | | | | | | | | | |
Sub-total: Real Estate (9.6%)* |
|
| | $ | 16,617 | | $ | 16,839 | | $ | 16,885 | ||||
|
|
| |
|
|
| |
|
| |
|
| |
|
|
Rental and Leasing Services(2) |
|
|
|
|
|
| | |
|
| |
|
| |
|
EquipmentShare, Inc. | | Equipment Financing | | July 1, 2023 | | Fixed interest rate 10.7%; EOT 5.0% | | $ | 7,538 | | $ | 7,685 | | $ | 7,730 |
| | Equipment Financing | | August 1, 2023 | | Fixed interest rate 10.1%; EOT 5.0% | | | 864 | | | 879 | | | 884 |
| | Equipment Financing | | September 1, 2023 | | Fixed interest rate 10.2%; EOT 5.0% | | | 1,908 | | | 1,935 | | | 1,944 |
| | Equipment Financing | | October 1, 2023 | | Fixed interest rate 10.4%; EOT 5.0% | | | 3,422 | | | 3,458 | | | 3,470 |
| | Equipment Financing | | October 1, 2024 | | Fixed interest rate 8.3%; EOT 10.0% | | | 429 | | | 435 | | | 435 |
| | Equipment Financing | | November 1, 2023 | | Fixed interest rate 10.4%; EOT 5.0% | | | 811 | | | 818 | | | 818 |
| | Equipment Financing | | November 1, 2023 | | Fixed interest rate 10.5%; EOT 5.0% | | | 2,560 | | | 2,581 | | | 2,581 |
| | Equipment Financing | | December 1, 2023 | | Fixed interest rate 10.1%; EOT 5.0% | | | 2,491 | | | 2,506 | | | 2,506 |
| | Equipment Financing | | January 1, 2024 | | Fixed interest rate 10.1%; EOT 5.0% | | | 1,995 | | | 2,002 | | | 2,002 |
| | Equipment Financing | | January 1, 2024 | | Fixed interest rate 10.5%; EOT 5.0% | | | 797 | | | 799 | | | 799 |
Total EquipmentShare, Inc. | | | | | | | | | 22,815 | | | 23,098 | | | 23,169 |
| | | | | | | | | | | | | | | |
Maxwell Financial Labs, Inc. | | Secured Loan | | November 1, 2024 | | Variable interest rate PRIME + 8.0% or Floor rate 11.25%; EOT 4.0% (9) | | $ | 3,000 | | $ | 2,964 | | $ | 2,964 |
| | Secured Loan | | January 1, 2025 | | Variable interest rate PRIME + 8.0% or Floor rate 11.25%; EOT 4.0% (9) | | | 3,000 | | | 2,938 | | | 2,938 |
Total Maxwell Financial Labs, Inc. | | | | | | | | | 6,000 | | | 5,902 | | | 5,902 |
| | | | | | | | | | | | | | | |
Sub-total: Rental and Leasing Services (12.2%)* |
|
| | $ | 28,815 | | $ | 29,000 | | $ | 29,071 | ||||
| | | | | | | | | | | | | | | |
Retail Trade (2) |
|
| |
|
|
| |
|
| |
|
| |
|
|
Birchbox, Inc. (7) |
| Secured Loan | | July 1, 2024 |
| Fixed interest rate 9.0%; EOT 7.5% | | $ | 10,000 | | $ | 10,433 | | $ | 9,924 |
| | | | | | | | | | | | | | | |
Boosted eCommerce, Inc. (16) | | Secured Loan | | January 1, 2023 | | Variable interest rate PRIME + 7.75% or Floor rate 11.0%; EOT 3.25% (9) | | $ | 5,000 | | $ | 4,933 | | $ | 4,933 |
| | | | | | | | | | | | | | | |
Gobble, Inc. |
| Secured Loan | | July 1, 2023 |
| Fixed interest rate 11.3%; EOT 6.0% | | $ | 3,443 | | $ | 3,544 | | $ | 3,556 |
|
| Secured Loan | | July 1, 2023 |
| Fixed interest rate 11.5%; EOT 6.0% | |
| 1,730 | |
| 1,781 | |
| 1,795 |
Total Gobble Inc. |
|
| |
|
|
| |
| 5,173 | |
| 5,325 | |
| 5,351 |
| | | | | | | | | | | | | | | |
Madison Reed, Inc. |
| Secured Loan | | May 1, 2024 |
| Variable interest rate PRIME + 6.0% or Floor rate 10.3%; EOT 4.0% (9) | | $ | 17,500 | | $ | 17,471 | | $ | 17,835 |
| | | | | | | | | | | | | | | |
Portofino Labs, Inc. (16) | | Secured Loan | | July 1, 2025 | | Variable interest rate PRIME + 8.25% or Floor rate 11.5%; EOT 4.0% (9) | | $ | 2,000 | | $ | 1,984 | | $ | 1,984 |
| | | | | | | | | | | | | | | |
Super73, Inc. (16) | | Secured Loan | | January 1, 2025 | | Variable interest rate PRIME + 7.3% or Floor rate 11.8%; EOT 4.0% (9) | | $ | 5,500 | | $ | 5,416 | | $ | 5,416 |
| | | | | | | | | | | | | | | |
UnTuckIt, Inc. |
| Secured Loan | | June 1, 2024 |
| Fixed interest rate 12.0%; EOT 5.0% | | $ | 20,000 | | $ | 21,098 | | $ | 19,230 |
| | | | | | | | | | | | | | | |
Sub-total: Retail Trade (27.1%)* |
|
| |
|
|
| | $ | 65,173 | | $ | 66,660 | | $ | 64,673 |
106
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of Investment (3) |
| Maturity Date |
| Interest Rate (4) |
| Principal |
| Cost |
| Fair Value (6) | |||
Debt Securities, Continued | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | |
Utilities (2) |
|
| |
|
|
| |
|
| |
|
| |
|
|
Invenia, Inc. |
| Secured Loan | | January 1, 2023 |
| Fixed interest rate 11.5%; EOT 5.0% | | $ | 6,570 | | $ | 7,042 | | $ | 6,991 |
|
| Secured Loan | | May 1, 2023 |
| Fixed interest rate 11.5%; EOT 5.0% | |
| 3,326 | |
| 3,537 | |
| 3,550 |
|
| Secured Loan | | January 1, 2024 |
| Fixed interest rate 11.5%; EOT 5.0% | |
| 3,000 | |
| 3,058 | |
| 3,165 |
|
| Secured Loan | | February 1, 2024 |
| Fixed interest rate 11.5%; EOT 5.0% | |
| 4,000 | |
| 4,103 | |
| 4,200 |
| | Secured Loan | | July 1, 2024 | | Fixed interest rate 11.5%: EOT 5.0% | | | 4,000 | | | 4,043 | | | 4,160 |
| | Secured Loan | | November 1, 2024 | | Fixed interest rate 11.5%: EOT 5.0% | | | 5,000 | | | 5,017 | | | 5,017 |
Total Invenia, Inc. (13) |
|
| |
|
|
| | | 25,896 | | | 26,800 | | | 27,083 |
| | | | | | | | | | | | | | | |
Sub-total: Utilities (11.4%)* |
|
| |
|
|
| | $ | 25,896 | | $ | 26,800 | | $ | 27,083 |
|
|
| |
|
|
| |
|
| |
|
| |
|
|
Wholesale Trade |
|
| |
|
|
| |
|
| |
|
| |
|
|
BaubleBar, Inc. (2) |
| Secured Loan | | March 1, 2023 |
| Fixed interest rate 11.5%; EOT 7.3% | | $ | 5,752 | | $ | 6,576 | | $ | 6,148 |
| | | | | | | | | | | | | | | |
Grandpad, Inc. | | Equipment Financing | | June 1, 2023 | | Fixed interest rate 10.6%; EOT 5.0% | | $ | 2,899 | | $ | 2,907 | | $ | 2,907 |
| | Equipment Financing | | July 1, 2023 | | Fixed interest rate 10.8%; EOT 5.0% | | | 3,672 | | | 3,667 | | | 3,667 |
Total Grandpad, Inc. (16) | | | | | | | | | 6,571 | | | 6,574 | | | 6,574 |
| | | | | | | | | | | | | | | |
GrubMarket, Inc. | | Secured Loan | | July 1, 2024 | | Fixed interest rate 10.5%; EOT 3.0% | | $ | 10,000 | | $ | 9,875 | | $ | 10,114 |
| | | | | | | | | | | | | | | |
Sub-total: Wholesale Trade (9.6%)* |
|
| |
|
|
| | $ | 22,323 | | $ | 23,025 | | $ | 22,836 |
| | | | | | | | | | | | | | | |
Total: Debt Securities (186.0%)* (15) |
|
| |
|
|
| | $ | 448,010 | | $ | 447,510 | | $ | 443,219 |
107
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of |
| Expiration Date |
| Series |
| Shares |
| Strike Price |
| Cost |
| Fair Value (6) | |||
Warrant Investments | |
| | | |
| |
| |
| | |
| | |
| |
| | | | | | | | | | | | | | | |
| |
Agriculture, Forestry, Fishing and Hunting (2) | |
| |
| |
| |
| | |
| | |
| | |
|
Bowery Farming, Inc. | | Warrant | | June 10, 2029 | | Common Stock | | 68,863 | | $ | 5.08 | | $ | 410 | | $ | 403 |
| | Warrant | | December 22, 2030 | | Common Stock | | 29,925 | | $ | 6.24 | | $ | 160 | | $ | 160 |
Total Bowery Farming, Inc. | | | | | | | | | | | | | | 570 | | | 563 |
| | | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | | | |
Robotany, Inc. | | Warrant | | July 19, 2029 | | Common Stock | | 262,870 | | $ | 0.26 | | $ | 128 | | $ | 92 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Agriculture, Forestry, Fishing and Hunting (0.3%)* | |
| | | |
| | | $ | 698 | | $ | 655 | ||||
| | | | | | | | | | | | | | | | | |
Construction (2) | |
| |
| |
| | | |
| | |
|
| |
|
|
Project Frog, Inc. (7) | | Warrant | | July 26, 2026 | | Preferred Series AA | | 391,990 | | $ | 0.19 | | $ | 18 | | $ | 2 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Construction (0.0%)* | |
| | | |
| | | |
| | | $ | 18 | | $ | 2 |
| | | | | | | | | | | | | | | | | |
Educational Services (2) | |
| | | |
| | | |
| | |
|
| |
|
|
Qubed, Inc. dba Yellowbrick | | Warrant | | September 28, 2028 | | Common Stock | | 222,222 | | $ | 0.90 | | $ | 120 | | $ | 593 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Educational Services (0.2%)* | |
| | | |
| |
| |
| | | $ | 120 | | $ | 593 |
| | | | | | | | | | | | | | | | | |
Finance and Insurance (2) | |
| | | |
| |
| |
| | |
|
| |
|
|
DailyPay, Inc. | | Warrant | | September 30, 2030 | | Common Stock | | 89,264 | | $ | 3.00 | | $ | 151 | | $ | 206 |
| | | | | | | | | | | | | | | | | |
Petal Card, Inc. | | Warrant | | November 27, 2029 | | Preferred Series B | | 250,268 | | $ | 1.32 | | $ | 147 | | $ | 350 |
| | | | | | | | | | | | | | | | | |
Realty Mogul, Co | | Warrant | | December 18, 2027 | | Preferred Series B | | 234,421 | | $ | 3.88 | | $ | 285 | | $ | 25 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Finance and Insurance (0.2%)* | |
| | | |
| | | |
| | | $ | 583 | | $ | 581 |
| | | | | | | | | | | | | | | | | |
Health Care and Social Assistance (2) | |
| | | |
| | | |
| | |
|
| |
|
|
Lark Technologies, Inc. | | Warrant | | September 30, 2030 | | Common Stock | | 76,231 | | $ | 1.76 | | $ | 177 | | $ | 163 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Health Care and Social Assistance (0.1%)* | | | |
| | | |
| | | $ | 177 | | $ | 163 | ||
| | | | | | | | | | | | | | | | | |
Information (2) | |
| | | |
| | | |
| | |
|
| |
|
|
Convercent, Inc. | | Warrant | | November 30, 2025 | | Preferred Series 1 | | 3,139,579 | | $ | 0.16 | | $ | 924 | | $ | 610 |
| | | | | | | | | | | | | | | | | |
Figg, Inc. (12) | | Warrant | | March 31, 2028 | | Common Stock | | 935,198 | | $ | 0.07 | | $ | — | | $ | — |
| | | | | | | | | | | | | | | | | |
Everalbum, Inc. | | Warrant | | July 29, 2026 | | Preferred Series A | | 851,063 | | $ | 0.10 | | $ | 24 | | $ | 6 |
| | | | | | | | | | | | | | | | | |
Firefly Systems, Inc. | | Warrant | | January 29, 2030 | | Common Stock | | 133,147 | | $ | 1.14 | | $ | 282 | | $ | 132 |
| | | | | | | | | | | | | | | | | |
Gtxcel, Inc. | | Warrant | | September 24, 2025 | | Preferred Series C | | 1,000,000 | | $ | 0.21 | | $ | 83 | | $ | 4 |
| | Warrant | | September 24, 2025 | | Preferred Series D | | 1,000,000 | | $ | 0.21 | |
| 83 | |
| 12 |
Total Gtxcel, Inc. | |
| | | |
| | | |
| | |
| 166 | |
| 16 |
| | | | | | | | | | | | | | | | | |
Hytrust, Inc. | | Warrant | | June 23, 2026 | | Preferred Series D2 | | 424,808 | | $ | 0.82 | | $ | 172 | | $ | — |
| | | | | | | | | | | | | | | | | |
Lucidworks, Inc. | | Warrant | | June 27, 2026 | | Preferred Series D | | 619,435 | | $ | 0.77 | | $ | 806 | | $ | 1,509 |
| | | | | | | | | | | | | | | | | |
Oto Analytics, Inc. | | Warrant | | August 31, 2028 | | Preferred Series B | | 1,018,718 | | $ | 0.79 | | $ | 295 | | $ | 221 |
| | | | | | | | | | | | | | | | | |
RapidMiner, Inc. | | Warrant | | March 25, 2029 | | Preferred Series C-1 | | 11,624 | | $ | 60.22 | | $ | 528 | | $ | 357 |
| | | | | | | | | | | | | | | | | |
STS Media, Inc.(12) | | Warrant | | March 15, 2028 | | Preferred Series C | | 20,210 | | $ | 24.74 | | $ | — | | $ | — |
| | | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | | | |
Sub-Total: Information (1.2%)* |
|
| | |
|
|
|
| |
| | | $ | 3,197 | | $ | 2,851 |
108
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of |
| Expiration Date |
| Series |
| Shares |
| Strike Price |
| Cost |
| Fair Value (6) | |||
Warrant Investments, Continued | |
| | | |
| |
| |
| | |
| | |
| |
| | | | | | | | | | | | | | | |
| |
Manufacturing (2) | |
| | | |
| |
| |
| | |
|
| |
|
|
Atieva, Inc. (13) | | Warrant | | March 31, 2027 | | Preferred Series D | | 390,016 | | $ | 5.13 | | $ | 3,067 | | $ | 1,053 |
| | Warrant | | September 8, 2027 | | Preferred Series D | | 195,008 | | $ | 5.13 | |
| 1,533 | |
| 526 |
Total Atieva, Inc. | |
| | | |
| | | |
| | |
| 4,600 | |
| 1,579 |
| | | | | | | | | | | | | | | | | |
AyDeeKay LLC | | Warrant | | March 30, 2028 | | Preferred Series G | | 6,250 | | $ | 35.42 | | $ | 31 | | $ | 32 |
| | | | | | | | | | | | | | | | | |
Footprint International Holding, Inc. | | Warrant | | February 14, 2030 | | Common Stock | | 26,852 | | $ | 0.31 | | $ | 5 | | $ | 81 |
| | Warrant | | June 22, 2030 | | Common Stock | | 10,836 | | $ | 0.31 | |
| 4 | |
| 33 |
Total Footprint International Holding, Inc. | | | | | | | | | | | | | | 9 | | | 114 |
| | | | | | | | | | | | | | | | | |
Happiest Baby, Inc. | | Warrant | | May 16, 2029 | | Common Stock | | 182,554 | | $ | 0.33 | | $ | 193 | | $ | 126 |
| | | | | | | | | | | | | | | | | |
Hexatech, Inc. (12) | | Warrant | | April 2, 2022 | | Preferred Series A | | 226 | | $ | 2.77 | | $ | — | | $ | — |
| | | | | | | | | | | | | | | | | |
Lensvector, Inc. | | Warrant | | December 30, 2021 | | Preferred Series C | | 85,065 | | $ | 1.18 | | $ | 32 | | $ | — |
| | | | | | | | | | | | | | | | | |
Mainspring Energy, Inc. | | Warrant | | July 9, 2029 | | Common Stock | | 140,186 | | $ | 1.15 | | $ | 283 | | $ | 394 |
| | Warrant | | November 20, 2030 | | Common Stock | | 81,294 | | $ | 1.15 | | | 226 | | | 229 |
Total Mainspring Energy, Inc. | | | | | | | | | | | | | | 509 | | | 623 |
| | | | | | | | | | | | | | | | | |
Molekule, Inc. | | Warrant | | June 19, 2030 | | Preferred Series C-1 | | 32,051 | | | 3.12 | | $ | 16 | | $ | 23 |
| | | | | | | | | | | | | | | | | |
SBG Labs, Inc. | | Warrant | | June 29, 2023 | | Preferred Series A-1 | | 42,857 | | $ | 0.70 | | $ | 13 | | $ | 10 |
| | Warrant | | September 18, 2024 | | Preferred Series A-1 | | 25,714 | | $ | 0.70 | |
| 8 | |
| 6 |
| | Warrant | | January 14, 2024 | | Preferred Series A-1 | | 21,492 | | $ | 0.70 | |
| 7 | |
| 5 |
| | Warrant | | March 24, 2025 | | Preferred Series A-1 | | 12,155 | | $ | 0.70 | |
| 4 | |
| 3 |
| | Warrant | | October 10, 2023 | | Preferred Series A-1 | | 11,150 | | $ | 0.70 | |
| 4 | |
| 3 |
| | Warrant | | May 6, 2024 | | Preferred Series A-1 | | 11,145 | | $ | 0.70 | |
| 4 | |
| 3 |
| | Warrant | | June 9, 2024 | | Preferred Series A-1 | | 7,085 | | $ | 0.70 | |
| 2 | |
| 2 |
| | Warrant | | May 20, 2024 | | Preferred Series A-1 | | 342,857 | | $ | 0.70 | |
| 110 | |
| 80 |
| | Warrant | | March 26, 2025 | | Preferred Series A-1 | | 200,000 | | $ | 0.70 | |
| 65 | |
| 48 |
Total SBG Labs, Inc. | |
| | | |
| |
| |
|
| |
| 217 | |
| 160 |
| | | | | | | | | | | | | | | | | |
The Fynder Group, Inc. | | Warrant | | October 14, 2030 | | Common Stock | | 107,190 | | $ | 0.49 | | $ | 201 | | $ | 282 |
| | | | | | | | | | | | | | | | | |
Vertical Communications, Inc. (7) (12) | | Warrant | | July 11, 2026 | | Preferred Series A | | 828,479 | | $ | 1.00 | | $ | — | | $ | — |
| | | | | | | | | | | | | | | | | |
Sub-Total: Manufacturing (1.2%)* | |
| | | |
| |
| |
|
| | $ | 5,808 | | $ | 2,939 |
109
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of |
| Expiration Date |
| Series |
| Shares |
| Strike Price |
| Cost | | Fair Value (6) | |||
Warrant Investments, Continued | |
| | | |
| |
| |
| | |
| | |
| |
| | | | | | | | | | | | | | | | | |
Pharmaceutical (2) | |
| | | |
| |
| |
|
| |
|
| |
|
|
Nanotherapeutics, Inc. (8) | | Warrant | | November 14, 2021 | | Common Stock | | 67,961 | | $ | 1.03 | | $ | 1,122 | | $ | 2,216 |
| | | | | | | | | | | | | | | | | |
Zosano Pharma Corporation | | Warrant | | September 25, 2025 | | Common Stock | | 75,000 | | $ | 3.59 | | $ | 69 | | $ | 18 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Pharmaceutical (0.9%)* | |
| | | |
| |
| |
|
| | $ | 1,191 | | $ | 2,234 |
| | | | | | | | | | | | | | | |
| |
Professional, Scientific, and Technical Services (2) | |
| | | |
| |
| |
|
| |
|
| |
|
|
Augmedix, Inc. | | Warrant | | September 3, 2029 | | Preferred Series B | | 580,383 | | $ | 2.88 | | $ | 449 | | $ | 379 |
| | | | | | | | | | | | | | | | | |
Continuity, Inc. | | Warrant | | March 29, 2026 | | Preferred Series C | | 1,588,806 | | $ | 0.25 | | $ | 21 | | $ | 45 |
| | | | | | | | | | | | | | | | | |
Crowdtap, Inc. | | Warrant | | December 16, 2025 | | Preferred Series B | | 442,233 | | $ | 1.09 | | $ | 42 | | $ | 140 |
| | Warrant | | November 30, 2027 | | Preferred Series B | | 100,000 | | $ | 1.09 | |
| 9 | |
| 32 |
Total Crowdtap, Inc. | |
| | | |
| | | |
| | |
| 51 | |
| 172 |
| | | | | | | | | | | | | | | | | |
Dynamics, Inc. | | Warrant | | March 10, 2024 | | Common Stock | | 17,000 | | $ | 10.59 | | $ | 86 | | $ | — |
| | | | | | | | | | | | | | | | | |
E La Carte, Inc. | | Warrant | | July 28, 2027 | | Common Stock | | 497,183 | | $ | 0.30 | | $ | 186 | | $ | 123 |
| | Warrant | | July 28, 2027 | | Preferred Series A | | 104,284 | | $ | 7.49 | |
| 15 | |
| 34 |
| | Warrant | | July 28, 2027 | | Preferred Series AA-1 | | 106,841 | | $ | 7.49 | |
| 15 | |
| 1 |
Total E La Carte, Inc. | |
| | | |
| | | |
| | |
| 216 | |
| 158 |
| | | | | | | | | | | | | | | | | |
Edeniq, Inc. | | Warrant | | December 23, 2026 | | Preferred Series B | | 2,685,501 | | $ | 0.22 | | $ | — | | $ | — |
| | Warrant | | December 23, 2026 | | Preferred Series B | | 2,184,672 | | $ | 0.01 | |
| — | |
| — |
| | Warrant | | March 12, 2028 | | Preferred Series C | | 5,106,972 | | $ | 0.44 | |
| — | |
| — |
| | Warrant | | October 15, 2028 | | Preferred Series C | | 3,850,294 | | $ | 0.01 | |
| — | |
| — |
Total Edeniq, Inc. (7)(12) | |
| | | |
| | | |
| | |
| — | |
| — |
| | | | | | | | | | | | | | | | | |
Fingerprint Digital, Inc. | | Warrant | | April 29, 2026 | | Preferred Series B | | 48,102 | | $ | 10.39 | | $ | 165 | | $ | 84 |
| | | | | | | | | | | | | | | | | |
Hologram, Inc. | | Warrant | | January 27, 2030 | | Common Stock | | 193,054 | | $ | 0.26 | | $ | 49 | | $ | 33 |
| | | | | | | | | | | | | | | | | |
Hospitalists Now, Inc. | | Warrant | | March 30, 2026 | | Preferred Series D2 | | 135,807 | | $ | 5.89 | | $ | 71 | | $ | 272 |
| | Warrant | | December 6, 2026 | | Preferred Series D2 | | 750,000 | | $ | 5.89 | |
| 391 | |
| 1,505 |
Total Hospitalists Now, Inc. | |
| | | |
| | | |
| | |
| 462 | |
| 1,777 |
| | | | | | | | | | | | | | | | | |
Incontext Solutions, Inc. | | Warrant | | September 28, 2028 | | Preferred Series AA-1 | | 332,858 | | $ | 1.47 | | $ | 34 | | $ | 47 |
| | | | | | | | | | | | | | | | | |
Matterport, Inc. | | Warrant | | April 20, 2028 | | Common Stock | | 143,813 | | $ | 1.43 | | $ | 434 | | $ | 603 |
| | | | | | | | | | | | | | | | | |
Pendulum Therapeutics, Inc. | | Warrant | | October 9, 2029 | | Preferred Series B | | 55,263 | | $ | 1.90 | | $ | 44 | | $ | 65 |
| | Warrant | | July 15, 2030 | | Preferred Series B | | 36,842 | | $ | 1.90 | | | 36 | | | 43 |
Total Pendulum Therapeutics, Inc. | | | | | | | | | | | | |
| 80 | |
| 108 |
| | | | | | | | | | | | | | | | | |
Reciprocity, Inc. | | Warrant | | September 25, 2030 | | Common Stock | | 114,678 | | $ | 4.17 | | $ | 99 | | $ | 145 |
| | | | | | | | | | | | | | | | | |
Resilinc, Inc. | | Warrant | | December 15, 2025 | | Preferred Series A | | 589,275 | | $ | 0.51 | | $ | 40 | | $ | 100 |
| | | | | | | | | | | | | | | | | |
| | | | | | | | | | | | | | | | | |
Saylent Technologies, Inc. | | Warrant | | March 31, 2027 | | Preferred Series C | | 24,096 | | $ | 9.96 | | $ | 108 | | $ | 94 |
| | | | | | | | | | | | | | | | | |
Sun Basket, Inc. | | Warrant | | October 5, 2027 | | Preferred Series C-2 | | 249,306 | | $ | 6.02 | | $ | 111 | | $ | 343 |
| | Warrant | | December 31, 2030 | | Common Stock | | 118,678 | | $ | 0.89 | | | 545 | | | 546 |
| | | | | | | | | | | | | | 656 | | | 889 |
| | | | | | | | | | | | | | | | | |
Utility Associates, Inc. | | Warrant | | June 30, 2025 | | Preferred Series A | | 92,511 | | $ | 4.54 | | $ | 55 | | $ | 4 |
| | Warrant | | May 1, 2026 | | Preferred Series A | | 60,000 | | $ | 4.54 | |
| 36 | |
| 3 |
| | Warrant | | May 22, 2027 | | Preferred Series A | | 200,000 | | $ | 4.54 | |
| 120 | |
| 8 |
Total Utility Associates, Inc. | |
| | | |
| | | |
| | |
| 211 | |
| 15 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Professional, Scientific, and Technical Services (2.0%)* | | | | | | | | | $ | 3,161 | | $ | 4,649 | ||||
110
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of |
| Expiration Date |
| Series |
| Shares |
| Strike Price |
| Cost |
| Fair Value (6) | |||
Warrant Investments, Continued | |
| | | |
| |
| |
| | |
| | |
| |
| | | | | | | | | | | | | | | |
| |
Real Estate (2) | |
| | | |
| |
| |
|
| |
|
| |
|
|
Egomotion Corporation | | Warrant | | December 10, 2028 | | Preferred Series A | | 60,786 | | $ | 1.32 | | $ | — | | $ | 53 |
| | Warrant | | June 29, 2028 | | Preferred Series A | | 121,571 | | $ | 1.32 | | | 219 | | | 106 |
Total Egomotion Corporation | | | | | | | | | | | | | | 219 | | | 159 |
| | | | | | | | | | | | | | | | | |
Knockaway, Inc. | | Warrant | | May 24, 2029 | | Preferred Series B | | 87,955 | | $ | 8.53 | | $ | 209 | | $ | 272 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Real Estate (0.2%)* | | | | | |
| |
| | |
| | $ | 428 | | $ | 431 |
| | | | | | | | | | | | | | | | | |
Rental and Leasing Services (2) | |
| | | |
| |
| | |
| |
|
| |
|
|
| | | | | | | | | | | | | | | | | |
Maxwell Financial Labs, Inc. | | Warrant | | October 7, 2030 | | Common Stock | | 106,735 | | $ | 0.29 | | $ | 21 | | $ | 33 |
| | Warrant | | December 22, 2030 | | Common Stock | | 110,860 | | $ | 0.29 | | | 34 | | | 34 |
Total Maxwell Financial Labs, Inc. | | | | | | | | | | | | | | 55 | | | 67 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Rental and Leasing Services (0.0%)* | | | | | |
| |
| | |
| | $ | 55 | | $ | 67 |
| | | | | | | | | | | | | | | | | |
Retail Trade (2) | |
| | | |
| |
| | |
| |
|
| |
|
|
Boosted eCommerce, Inc. (16) | | Warrant | | December 14, 2030 | | Preferred Series A-1 | | 759,263 | | $ | 0.84 | | $ | 259 | | $ | 259 |
| | | | | | | | | | | | | | | | | |
Gobble, Inc. | | Warrant | | May 9, 2028 | | Common Stock | | 74,635 | | $ | 1.20 | | $ | 73 | | $ | 63 |
| | Warrant | | December 27, 2029 | | Common Stock | | 10,000 | | $ | 1.22 | |
| 617 | |
| 467 |
Total Gobble, Inc. | | | | | |
| | | |
| | |
| 690 | |
| 530 |
| | | | | | | | | | | | | | | | | |
Madison Reed, Inc. | | Warrant | | March 23, 2027 | | Preferred Series C | | 194,553 | | $ | 2.57 | | $ | 185 | | $ | 241 |
| | Warrant | | July 18, 2028 | | Common Stock | | 43,158 | | $ | 0.99 | |
| 71 | |
| 78 |
| | Warrant | | May 19, 2029 | | Common Stock | | 36,585 | | $ | 1.23 | |
| 56 | |
| 62 |
Total Madison Reed, Inc. | | | | | |
| | | |
| | |
| 312 | |
| 381 |
| | | | | | | | | | | | | | | | | |
Portofino Labs, Inc. (16) | | Warrant | | December 31, 2030 | | Common Stock | | 39,659 | | $ | 1.53 | | $ | 15 | | $ | 15 |
| | | | | | | | | | | | | | | | | |
Super73, Inc. (16) | | Warrant | | December 31, 2030 | | Common Stock | | 177,305 | | $ | 3.16 | | $ | 105 | | $ | 105 |
| | | | | | | | | | | | | | | | | |
Trendly, Inc. | | Warrant | | August 10, 2026 | | Preferred Series A | | 245,506 | | $ | 1.14 | | $ | 222 | | $ | 256 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Retail Trade (0.6%)* | | | | | |
| | | |
| | | $ | 1,603 | | $ | 1,546 |
| | | | | | | | | | | | | | | | | |
Wholesale Trade (2) | |
| | | |
| | | |
| | |
|
| |
|
|
BaubleBar, Inc. | | Warrant | | March 29, 2027 | | Preferred Series C | | 531,806 | | $ | 1.96 | | $ | 638 | | $ | 207 |
| | Warrant | | April 20, 2028 | | Preferred Series C | | 60,000 | | $ | 1.96 | |
| 72 | |
| 23 |
Total BaubleBar, Inc. | | | | | |
| | | |
| | |
| 710 | |
| 230 |
| | | | | | | | | | | | | | | | | |
GrubMarket, Inc. | | Warrant | | June 15, 2030 | | Common Stock | | 405,000 | | $ | 1.10 | | $ | 116 | | $ | 837 |
| | | | | | | | | | | | | | | | | |
Sub-Total: Wholesale Trade (0.4%)* | | | | | | | | | | | | | $ | 826 | | $ | 1,067 |
| | | | | | | | | | | | | | | | | |
Total: Warrant Investments (7.4%)* (15) | | | | | | | | | | | | | $ | 17,865 | | $ | 17,778 |
111
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
Portfolio Company (1) |
| Type of |
| Shares / Principal |
| Series |
| Cost |
| Fair Value (6) | |||
Equity Investments | |
| | |
| |
| |
| | |
| |
Construction (2) | |
| | |
| |
| |
| | |
| |
Project Frog, Inc. |
| Equity |
| | 8,118,527 |
| Preferred Series AA-1 | | $ | 702 | | $ | 36 |
|
| Equity |
| | 6,300,134 |
| Preferred Series BB | |
| 2,667 | |
| 449 |
Total Project Frog, Inc. (7) |
|
|
| | |
|
| |
| 3,369 | |
| 485 |
|
|
|
| | |
|
| |
|
| |
|
|
Sub-Total: Construction (0.2%)* |
|
|
| | |
|
| | $ | 3,369 | | $ | 485 |
|
|
|
| | |
|
| |
|
| |
|
|
Health Care and Social Assistance (2) |
|
|
| | |
|
| |
|
| |
|
|
WorkWell Prevention & Care Inc. |
| Equity |
| | 7,000,000 |
| Common Stock | | $ | 51 | | $ | — |
|
| Equity |
| | 3,450 |
| Preferred Series P | |
| 3,450 | |
| 657 |
|
|
|
| $ | 1,470 |
| Convertible Notes (10) | |
| 1,519 | |
| 1,542 |
Total WorkWell Prevention & Care Inc. (7) |
|
|
| | |
|
| |
| 5,020 | |
| 2,199 |
|
|
|
| | |
|
| |
|
| |
|
|
Sub-Total: Health Care and Social Assistance (0.9%)* |
|
|
| | |
|
| | $ | 5,020 | | $ | 2,199 |
|
|
|
| | |
|
| |
|
| |
|
|
Manufacturing (2) |
|
|
| | |
|
| |
|
| |
|
|
Store Intelligence, Inc. (8) | | Equity | | | 1,430,000 | | Preferred Series A | | $ | 608 | | $ | 694 |
|
|
|
| | |
|
| |
|
| |
|
|
Vertical Communications, Inc. |
| Equity |
| | 3,892,485 |
| Preferred Series 1 (12) | | $ | — | | $ | — |
|
| Equity |
| $ | 5,500,000 |
| Convertible Notes (10) | |
| 3,966 | |
| 3,350 |
Total Vertical Communications, Inc. (7) |
|
|
| | |
|
| |
| 3,966 | |
| 3,350 |
|
|
|
| | |
|
| |
|
| |
|
|
Sub-Total: Manufacturing (1.7%)* |
|
|
| | |
|
| | $ | 4,574 | | $ | 4,044 |
|
|
|
| | |
|
| |
|
| |
|
|
Pharmaceutical (2) |
|
|
| | |
|
| |
|
| |
|
|
Nanotherapeutics, Inc. (8) |
| Equity |
| | 382,277 |
| Common Stock (18) | | $ | 6,691 | | $ | 12,856 |
| | | | | | | | | | | | | |
Sub-Total: Pharmaceutical (5.4%)* |
|
|
| | |
|
| | $ | 6,691 | | $ | 12,856 |
|
|
|
| | |
|
| |
|
| |
|
|
Professional, Scientific, and Technical Services (2) |
|
|
| | |
|
| |
|
| |
|
|
Dynamics, Inc. |
| Equity |
| | 17,726 |
| Preferred Series A | | $ | 390 | | $ | — |
| | Equity | | | 15,000 | | Common Stock | | | — | | | — |
Total Dynamics, Inc. | | | | | | | | | | 390 | | | — |
|
|
|
| | |
|
| |
|
| |
|
|
Edeniq, Inc. |
| Equity |
| | 7,807,499 |
| Preferred Series B (12) | | $ | — | | $ | — |
|
| Equity |
| | 2,441,082 |
| Preferred Series C (12) | |
| — | |
| — |
|
| Equity |
| $ | 1,303,373 |
| Convertible Notes (10)(12) | |
| — | |
| — |
Total Edeniq, Inc. (7) |
|
|
| | |
|
| |
| — | |
| — |
|
|
|
| | |
|
| |
|
| |
|
|
Instart Logic, Inc. |
| Equity |
| $ | 2,600,000 |
| Convertible Notes (10) | | $ | 2,646 | | $ | 3,625 |
|
|
|
| | |
|
| |
|
| |
|
|
Sub-Total: Professional, Scientific, and Technical Services (1.5%)* |
| | | $ | 3,036 | | $ | 3,625 | |||||
| | | | | | | | | | | | | |
Retail Trade (2) | | | | | | | | | | | | | |
Birchbox, Inc. (7) | | Equity | | | 3,140,927 | | Preferred Series D | | $ | 10,271 | | $ | 9,445 |
|
|
|
| |
|
|
| | | | | | |
Sub-Total: Retail Trade (4.0%)* | | | | | | | | | $ | 10,271 | | $ | 9,445 |
| | | | | | | | | | | | | |
Total: Equity Investments (13.7%)* (15) |
|
|
| |
|
|
| | $ | 32,961 | | $ | 32,654 |
|
|
|
| |
|
|
| |
|
| |
|
|
Total Investment in Securities (207.2%)* |
|
|
| |
|
|
| | $ | 498,336 | | $ | 493,651 |
|
|
|
| |
|
|
| |
|
| |
|
|
Cash, Cash Equivalents, and Restricted Cash |
|
|
| |
|
|
| |
|
| |
|
|
Goldman Sachs Financial Square Government Institutional Fund | |
|
|
| | $ | 60,284 | | $ | 60,284 | |||
Other cash accounts |
|
|
| |
|
|
| |
| 817 | |
| 817 |
Cash, Cash Equivalents, and Restricted Cash (25.6%)* |
|
|
| |
|
|
| |
| 61,101 | |
| 61,101 |
|
|
|
| |
|
|
| |
|
| |
|
|
Total Portfolio Investments and Cash and Cash Equivalents (232.9% of net assets) |
|
|
| |
|
|
| | $ | 559,437 | | $ | 554,752 |
|
|
|
| |
|
|
| |
|
| |
|
|
112
TRINITY CAPITAL INC.
Consolidated Schedule of Investments
December 31, 2020
(In thousands, except share and per share data)
* | Value as a percent of net assets |
| (1) | All portfolio companies are located in North America. As of December 31, 2020, the Company had one foreign domiciled portfolio in Canada. The Company generally acquires its investments in private transactions exempt from registration under the Securities Act of 1933, as amended (the “Securities Act”). These investments are generally subject to certain limitations on resale and may be deemed to be “restricted securities” under the Securities Act. |
| (2) | Trinity Capital uses the North American Industry Classification System (“NAICS”) code for classifying the industry grouping of its portfolio companies. |
| (3) | All debt investments are income producing unless otherwise noted. All equity and warrant investments are non-income producing unless otherwise noted. Equipment financed under our equipment financing investments relates to operational equipment essential to revenue production for the portfolio company in the industry noted. |
| (4) | Interest rate is the fixed or variable rate of the debt investments and does not include any original issue discount, end-of-term (“EOT”) payment, or any additional fees related to such investments, such as deferred interest, commitment fees, prepayment fees or exit fees. EOT payments are contractual payments due in cash at the maturity date of the loan, including upon prepayment, and are a fixed rate determined at the inception of the loan. At the end of the term of certain equipment financings, the borrower has the option to purchase the underlying assets at fair market value in certain cases subject to a cap, or return the equipment and pay a restocking fee. The fair values of the financed assets have been estimated as a percentage of original cost for purpose of the EOT payment value. The EOT payment is amortized and recognized as non-cash income over the loan or equipment financing prior to its payment. |
| (5) | Principal is net of repayments, if any, as per the terms of the debt instrument’s contract. |
| (6) | All investments were valued at fair value using Level 3 significant unobservable inputs as determined in good faith by the Company’s board of directors. |
| (7) | This investment is deemed to be a “Control Investment.” Control Investments are defined by the Investment Company Act of 1940, as amended, as investments in companies in which the Company owns more than 25% of the voting securities or maintains greater than 50% of the board representation. As defined in the Investment Company Act, Trinity Capital is deemed to be an “Affiliated Person” of this portfolio company. See “Note 3 – Investments” in the accompanying notes to the Financial Statements. |
| (8) | This investment is deemed to be a “Affiliate Investment.” Affiliate Investments are defined by the Investment Company Act of 1940, as amended, as investments in companies in which the Company owns between 5% and 25% of the voting securities. As defined in the Investment Company Act, Trinity Capital is deemed to be an “Affiliated Person” of this portfolio company. See “Note 3 – Investments” in the accompanying notes to the Financial Statements. |
| (9) | The interest rate on variable interest rate investments represents a benchmark rate plus spread. The benchmark interest rate is subject to interest rate floors. The benchmark rate PRIME was 3.25% as of December 31, 2020. |
| (10) | Convertible notes represent investments through which the Company will participate in future equity rounds at preferential rates. There are no principal or interest payments made against the note unless conversion does not take place. |
113
| (11) | Debt is on non-accrual status as of December 31, 2020 and is therefore considered non-income producing. |
| (12) | Investment has zero cost basis as it was purchased at a fair market value of zero as part of the Formation Transaction. |
| (13) | Indicates an asset that the Company deems as a “non-qualifying asset” under section 55(a) by the Investment Company Act of 1940, as amended. The Company’s percentage of non-qualifying assets represents 5.1% of the Company’s total assets as of December 31, 2020. Qualifying assets must represent at least 70% of the Company’s total assets at the time of acquisition of any additional non-qualifying assets. |
| (14) | Investment has an unfunded commitment as of December 31, 2020 (see “Note 6 – Commitments and Contingencies”). The fair value of the investment includes the impact of the fair value of any unfunded commitments. |
| (15) | All of the Company’s debt, warrant and equity securities are pledged as collateral supporting the amounts outstanding under the credit agreement with Credit Suisse AG (see “Note 5 – Borrowings”), except as noted. |
| (16) | Investment is not pledged as collateral supporting amounts outstanding under the credit agreement with Credit Suisse AG. |
| (17) | Investment is considered non-income producing. |
| (18) | Certain third parties have rights to 17,485 shares of Nanotherapeutics common stock at a fair value of approximately $0.6 million as of December 31, 2020. |
114
TRINITY CAPITAL INC.
NOTES TO CONSOLIDATED FINANCIAL STATEMENTS (UNAUDITED)
Note 1. Organization and Basis of Presentation
Trinity Capital Inc., formed on August 12, 2019 as a Maryland corporation, is a specialty lending company focused on providing debt, including loans and equipment financings, to growth stage companies, including venture-backed companies and companies with institutional equity investors. The Company commenced operations on January 16, 2020. Prior to January 16, 2020, the Company had no operations, except for matters relating to its formation and organization as a business development company (“BDC”).
The Company is an internally managed, closed-end, non-diversified management investment company that has elected to be regulated as a BDC under the Investment Company Act of 1940, as amended (the “1940 Act”). The Company intends to elect to be treated, and intends to qualify annually thereafter, as a regulated investment company (a “RIC”) under Subchapter M of the Internal Revenue Code of 1986, as amended (the “Code”), for U.S. federal income tax purposes.
On September 27, 2019, the Company was initially capitalized with the issuance of 10 shares of its common stock for $150 to its sole stockholder. On January 16, 2020, the Company completed a series of transactions, including a private equity offering, a private debt offering, and the acquisition of Trinity Capital Investment, LLC (“TCI”), Trinity Capital Fund II, L.P. (“Fund II”), Trinity Capital Fund III, L.P. (“Fund III”), Trinity Capital Fund IV, L.P. (“Fund IV”), and Trinity Sidecar Income Fund, L.P. (“Sidecar Fund”) (collectively the “Legacy Funds”) through mergers of the Legacy Funds with an into the Company (the “Formation Transactions”). See “Formation Transactions” below.
The Company’s common stock began trading on the Nasdaq Global Select Market on January 29, 2021 under the symbol “TRIN” in connection with its initial public offering of shares of its common stock (“IPO”). See “Note 14 – Subsequent Events.”
Basis of Presentation
The Company’s consolidated financial statements are prepared in accordance with generally accepted accounting principles in the United States of America (“GAAP”) and pursuant to the requirements for reporting on Form 10-K and Regulation S-X. As an investment company, the Company follows accounting and reporting guidance determined by the Financial Accounting Standards Board (“FASB”), in Accounting Standards Codification, as amended (“ASC”) Topic 946 - Financial Services – Investment Companies (“ASC 946”).
Formation Transactions
The Formation Transactions were accounted for as a business combination in accordance with FASB ASC 805, Business Combinations (“ASC 805”), and as a result the assets acquired, and liabilities assumed were recorded at fair values as of January 16, 2020. Transaction costs related to the acquisition of a business are expensed as incurred and excluded from the fair value of the consideration transferred.
On January 16, 2020, the Company completed a private equity offering (the “Private Common Stock Offering”) of shares of its common stock pursuant to which it issued and sold 7,000,000 shares for gross proceeds of approximately $105.0 million. On January 29, 2020, an over-allotment option related to the Private Common Stock Offering was exercised in full and the Company issued and sold an additional 1,333,333 shares of its common stock for gross proceeds of approximately $20 million. As a result, the Company issued and sold an aggregate of 8,333,333 shares of its common stock for total aggregate gross proceeds of approximately $125 million.
On January 16, 2020, concurrent with the initial closing of the Private Common Stock Offering, the Company completed a private debt offering (the “144A Note Offering” and together with the Private Common Stock Offering, the “Private Offerings”) of $105.0 million in aggregate principal amount of the Company’s unsecured 7.00% Notes due
115
2025 (the “2025 Notes”). On January 29, 2020, an over-allotment option related to the 144A Note Offering was exercised in full and on the Company issued and sold an additional $20 million in aggregate principal amount of the Notes. As a result, the Company issued and sold $125 million in aggregate principal amount of the Notes. See “Note 5 - Borrowings” and “Note 7 – Stockholder’s Equity.”
On January 16, 2020, immediately following the consummation of the Private Offerings, the Company used a portion of the proceeds of the Private Offerings to acquire, through the Formation Transactions, the Legacy Funds and Trinity Capital Holdings, LLC (“Trinity Capital Holdings”). Each member/limited partner of the Legacy Funds was given the option to elect to receive cash and or shares of the Company’s common stock in exchange for its limited partner interests or membership interests, as applicable. The general partners, managers or managing members of the Legacy Funds received only shares in exchange for their interests held in such capacities. As a result of the Formation Transactions, the Legacy Funds were merged with and into the Company.
As consideration for the partnership and membership interests in the Legacy Funds, the Company issued 9,183,185 shares of its common stock at $15.00 per share for a total value of approximately $137.7 million and paid approximately $108.7 million in cash to the Legacy Investors totaling approximately $246.4 million. The acquisition consideration of the Formation Transactions was based on valuations as of September 30, 2019, as adjusted for assets that were disposed of by the Legacy Funds, as well as earnings, capital contributions and distributions paid to the members/limited partners, and material events affecting the portfolio companies of the Legacy Funds subsequent to September 30, 2019 and through the closing date of the Formation Transactions.
A summary of the fair value of the assets acquired and liabilities assumed from the Legacy Funds as of the acquisition date is as follows (in thousands):
Investments acquired |
| $ | 417,023 |
Interest receivable and other assets acquired |
| | 1,191 |
Accounts payable and accrued liabilities assumed |
| | (680) |
Customer deposits assumed |
| | (4,250) |
Credit facility assumed |
| | (190,000) |
Financing fees related to credit facility acquired |
| | 1,900 |
Cash acquired |
| | 19,183 |
Total net assets acquired | | $ | 244,367 |
The total merger consideration of the Legacy Funds of approximately $246.4 million exceeded the fair value of the net assets acquired as of the acquisition date, and as a result, the Company included a loss of approximately $2.1 million in Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds in the Consolidated Statements of Operations. During the year ended December 31, 2020, upon filing the final tax returns for the Legacy Funds, the Company reversed approximately $0.4 million of accrued liabilities assumed related to expected tax expense of the Legacy Funds.
Additionally, as part of the Formation Transactions, the Company also used a portion of the proceeds of the Private Offerings to acquire 100% of the equity interests of Trinity Capital Holdings, the sole member of Trinity Management IV, LLC, the investment manager to Fund IV and the sub-adviser to Fund II and Fund III, the Company issued 533,332 shares of common stock at $15.00 per share for a total value of approximately $8.0 million and paid approximately $2.0 million in cash. The Company also assumed a $3.5 million severance related liability with respect to a former member of certain general partners of certain Legacy Funds. Prior to the completion of the Formation Transactions, Trinity Capital Holdings acquired approximately $0.2 million of certain net assets from Trinity SBIC Management, LLC, the investment manager to Fund II and Fund III.
In connection with the acquisition of Trinity Capital Holdings, approximately $13.5 million (consisting of the aggregate purchase price and severance related liability assumed) was expensed to Costs related to the acquisition of Trinity Capital Holdings and Legacy Funds in the Consolidated Statements of Operations. Under ASC 805, such amount represents the settlement price, based on the estimated fair value of the future profits and cash flows that would otherwise have been contractually due to Trinity Capital Holdings, had the underlying management agreements with
116
each of the Legacy Funds not been canceled in order to enter into the Formation Transactions and operate the Company as an internally managed BDC.
Principles of Consolidation
Under ASC 946, the Company is precluded from consolidating portfolio company investments, including those in which it has a controlling interest, unless the portfolio company is another investment company. An exception to this general principle occurs if the Company holds a controlling interest in an operating company that provides all or substantially all of its services directly to the Company or to its portfolio companies. None of the portfolio investments made by the Company qualify for this exception. Therefore, the Company’s investment portfolio is carried on the Consolidated Statements of Assets and Liabilities at fair value, as discussed further in “Note 3 - Investments,” with any adjustments to fair value recognized as "Net unrealized appreciation (depreciation) from investments" on the Consolidated Statements of Operations.
The Company’s consolidated operations include the activities of its wholly owned subsidiary, Trinity Funding 1, LLC (“TF1”). On January 16, 2020, in connection with the Formation Transactions, the Company acquired TF1 through Fund II and became a party to, and assumed, a $300 million credit agreement (as amended, the “Credit Facility”) with Credit Suisse AG (“Credit Suisse”) through TF1. TF1 was formed on August 14, 2019 as a Delaware limited liability company with Fund II as its sole equity member. TF1 is a special purpose bankruptcy-remote entity and is a separate legal entity from the Company. Any assets conveyed to TF1 are not available to creditors of the Company or any other entity other than TF1’s lenders. TF1 is consolidated for financial reporting purposes and in accordance with GAAP, and the portfolio investments held by this subsidiary are included in the Company’s consolidated financial statements and recorded at fair value. All intercompany balances and transactions have been eliminated.
Note 2. Summary of Significant Accounting Policies
Use of Estimates
The preparation of financial statements in conformity with GAAP requires management to make estimates and assumptions that affect the reported amounts of assets and liabilities and disclosure of contingent assets and liabilities at the date of the financial statements. These estimates and assumptions also affect the reported amounts of revenues, costs and expenses during the reporting period. Management evaluates these estimates and assumptions on a regular basis. Actual results could differ materially from those estimates.
Investment Transactions
Loan originations are recorded on the date of the legally binding commitment. Realized gains or losses are recorded using the specific identification method as the difference between the net proceeds received, excluding prepayment fees, if any, and the amortized cost basis of the investment without regard to unrealized gains or losses previously recognized, and include investments written off during the period, net of recoveries. The net change in unrealized gains or losses primarily reflects the change in investment fair values as of the last business day of the reporting period and also includes the reversal of previously recorded unrealized gains or losses with respect to investments realized during the period.
Valuation of Investments
The most significant estimate inherent in the preparation of the Company’s consolidated financial statements is the valuation of investments and the related amounts of unrealized appreciation and depreciation of investments recorded.
The Company’s investments are carried at fair value in accordance with the 1940 Act and ASC 946 and measured in accordance with ASC 820, Fair Value Measurements and Disclosures (“ASC 820”). ASC 820 defines fair value, establishes a framework for measuring fair value, establishes a fair value hierarchy based on the observability of inputs used to measure fair value, and provides disclosure requirements for fair value measurements. ASC 820 requires the
117
Company to assume that each of the portfolio investments is sold in a hypothetical transaction in the principal or, as applicable, most advantageous market using market participant assumptions as of the measurement date. Market participants are defined as buyers and sellers in the principal market that are independent, knowledgeable and willing and able to transact. The Company values its investments at fair value as determined in good faith pursuant to a consistent valuation policy by the Company’s Board of Directors (the “Board”) in accordance with the provisions of ASC 820 and the 1940 Act.
While the Board is ultimately and solely responsible for determining the fair value of the Company’s investments, the Company has engaged independent valuation firms to provide the Company with valuation assistance with respect to its investments. The Company engages independent valuation firms on a discretionary basis. Specifically, on a quarterly basis, the Company will identify portfolio investments with respect to which an independent valuation firm will assist in valuing. The Company selects these portfolio investments based on a number of factors, including, but not limited to, the potential for material fluctuations in valuation results, size, credit quality and the time lapse since the last valuation of the portfolio investment by an independent valuation firm.
Investments recorded on the Company’s Consolidated Statements of Assets and Liabilities are categorized based on the inputs to the valuation techniques as follows:
Level 1 — Investments whose values are based on unadjusted quoted prices for identical assets in an active market that the Company has the ability to access (examples include investments in active exchange-traded equity securities and investments in most U.S. government and agency securities).
Level 2 — Investments whose values are based on quoted prices in markets that are not active or model inputs that are observable either directly or indirectly for substantially the full term of the investment.
Level 3 — Investments whose values are based on prices or valuation techniques that require inputs that are both unobservable and significant to the overall fair value measurement (for example, investments in illiquid securities issued by privately held companies). These inputs reflect management’s own assumptions about the assumptions a market participant would use in pricing the investment.
Given the nature of lending to venture capital-backed growth stage companies, substantially all of the Company’s investments in these portfolio companies are considered Level 3 assets under ASC 820 because there is no known or accessible market or market indexes for these investment securities to be traded or exchanges. The Company uses an internally developed portfolio investment rating system in connection with its investment oversight, portfolio management and analysis and investment valuation procedures. This system takes into account both quantitative and qualitative factors of the portfolio companies. Due to the inherent uncertainty of determining the fair value of investments that do not have a readily available market value, the fair value of the Company’s investments may fluctuate from period to period. Because of the inherent uncertainty of valuation, these estimated values may differ significantly from the values that would have been reported had a ready market for the investments existed, and it is reasonably possible that the difference could be material.
Debt Securities
The debt securities identified on the Consolidated Schedule of Investments are secured loans and equipment financings made to growth stage companies.
For portfolio investments in debt securities for which the Company has determined that third-party quotes or other independent pricing are not available, the Company generally estimates the fair value based on the assumptions that hypothetical market participants would use to value the investment in a current hypothetical sale using an income approach.
118
In its application of the income approach to determine the fair value of debt securities, the Company bases its assessment of fair value on projections of the discounted future free cash flows that the security will likely generate, including analyzing the discounted cash flows of interest and principal amounts for the security, as set forth in the associated loan and equipment financing agreements, as well as market yields and the financial position and credit risk of the portfolio company (the “Hypothetical Market Yield Method”). The discount rate applied to the future cash flows of the security is based on the calibrated yield implied by the terms of the Company’s investment adjusted for changes in market yields and performance of the subject company. The Company’s estimate of the expected repayment date of its loans and equipment financings securities is either the maturity date of the instrument or the anticipated pre-payment date, depending on the facts and circumstances. The Hypothetical Market Yield Method analysis also considers changes in leverage levels, credit quality, portfolio company performance, market yield movements, and other factors. If there is deterioration in credit quality or if a security is in workout status, the Company may consider other factors in determining the fair value of the security, including, but not limited to, the value attributable to the security from the enterprise value of the portfolio company or the proceeds that would most likely be received in a liquidation analysis.
Equity-Related Securities and Warrants
Often the Company is issued warrants by issuers as yield enhancements. These warrants are recorded as assets at estimated fair value on the grant date. Depending on the facts and circumstances, the Company usually utilizes a combination of one or several forms of the market approach as well as contingent claim analyses (a form of option analysis) to estimate the fair value of the securities as of the measurement date. As part of its application of the market approach, the Company estimates the enterprise value of a portfolio company utilizing customary pricing multiples, based on the development stage of the underlying issuers, or other appropriate valuation methods, such as considering recent transactions in the equity securities of the portfolio company or third-party valuations that are assessed to be indicative of fair value of the respective portfolio company, and, if appropriate based on the facts and circumstances performs an allocation of the enterprise value to the equity securities utilizing a contingent claim analysis and/or other waterfall calculation by which it allocates the enterprise value across the portfolio company’s securities in order of their preference relative to one another.
Fair value estimates are made at discrete points in time based on relevant information. These estimates may be subjective in nature and involve uncertainties and matters of significant judgment and, therefore, cannot be determined with precision. The carrying amounts of the Company’s financial instruments, consisting of cash, investments, receivables, payables and other liabilities approximate the fair values of such items due to the short-term nature of these instruments. Refer to “Note 4 – Fair Value of Financial Instruments” for further discussion.
Cash, Cash Equivalents and Restricted Cash
Cash, cash equivalents and restricted cash consist of funds deposited with financial institutions and short-term (original maturity of three months for less) liquid investments in money market deposit accounts. Cash equivalents are classified as Level I assets and are valued using the Net Asset Value (“NAV”) per share of the money market fund. As of December 31, 2020, cash, cash equivalents and restricted cash consisted of $61.1 million of which $60.3 million is held in the Goldman Sachs Financial Square Government Institutional Fund. Cash held in demand deposit accounts may exceed the Federal Deposit Insurance Corporation (“FDIC”) insured limit and therefore is subject to credit risk. All of the Company’s cash deposits are held at large established high credit quality financial institutions, and management believes that the risk of loss associated with any uninsured balances is remote. As of December 31, 2020, restricted cash consisted of approximately $15.7 million related to the Credit Facility covenants (See “Note 5 – Borrowings”), and approximately $0.7 million held in escrow related to the payout of a severance related liability assumed as part of the Formation Transactions with respect to a former member of certain general partners of certain Legacy Funds.
Other Assets
Other assets generally consist of fixed assets net of accumulated depreciation, right of use asset, security deposits and other assets.
119
Equity Offering Costs
A portion of the net proceeds of the Private Common Stock Offering was used to pay for offering costs of such offering. Offering costs charged against the proceeds from the Private Common Stock Offering were approximately $10.6 million during the year ended December 31, 2020.
Debt Issuance Costs
The Company records costs related to the issuance of debt obligations as deferred debt financing costs. These costs are deferred and amortized using the effective yield method for the Credit Facility, the 2025 Notes and the Convertible Notes (as defined below), over the stated maturity life of the obligations. As of December 31, 2020, there were $2.1 million, $4.7 million and $1.7 million of deferred financing costs netted against the Credit Facility, the 2025 Notes and the Convertible Notes balances, respectively, on the Company’s Consolidated Statements of Assets and Liabilities. As of December 31, 2019, deferred financing costs were approximately $3.5 million relating to the Credit Facility and the 2025 Notes.
Income Recognition
Interest Income
The Company recognizes interest income on an accrual basis and recognizes it as earned in accordance with the contractual terms of the loan agreement to the extent that such amounts are expected to be collected. Original issue discount (“OID”) initially includes the estimated fair value of detachable equity warrants obtained in conjunction with the origination of debt securities and is accreted into interest income over the term of the loan as a yield enhancement based on the effective yield method. In addition, the Company may also be entitled to an end-of-term (“EOT”) fee. EOT fees to be paid at the termination of the debt agreements are accreted into interest income over the contractual life of the debt based on the effective yield method. As of December 31, 2020, the EOT payment receivable of approximately $37.9 million is included as a component of the cost basis of the Company’s current debt securities.
Income related to application or origination payments, net of related expenses, and generally collected in advance, includes loan commitment and facility fees for due diligence, as well as fees for transaction services rendered by the Company to borrowers. Loan and commitment fees in excess of the related expenses are amortized into interest income over the contractual life of the loan. In certain loan arrangements, warrants or other equity interests are received from the borrower as additional origination fees. The Company recognizes nonrecurring fees over the remaining term of the loan commencing in the quarter relating to specific loan modifications.
When a portfolio company pre-pays their indebtedness prior to the scheduled maturity date, then the acceleration of the unaccreted OID and EOT is recognized as interest income.
Fee Income
The Company recognizes one-time fee income, including, but not limited to, structuring fees, prepayment penalties, and exit fees related to a change in ownership of the portfolio company, as other income when earned. These fees are generally earned when the portfolio company enters into an equipment financing arrangement or pays off their outstanding indebtedness prior to the scheduled maturity.
Non-Accrual Policy
When a debt security becomes 90 days or more past due, or if management otherwise does not expect that principal, interest, and other obligations due will be collected in full, the Company will generally place the debt security on non-accrual status and cease recognizing interest income on that debt security until all principal and interest due has been paid or the Company believes the borrower has demonstrated the ability to repay its current and future contractual obligations. Any uncollected interest is reversed from income in the period that collection of the interest receivable is
120
determined to be doubtful. However, the Company may make exceptions to this policy if the investment has sufficient collateral value and is in the process of collection.
As of December 31, 2020, loans to three portfolio companies were on non-accrual status with a total cost of approximately $3.4 million, and a total fair value of approximately $2.2 million, or 0.5%, of the total fair value of the Company’s investment portfolio.
Net Realized Gains or Losses
Realized gains or losses are measured by the difference between the net proceeds from the sale or redemption of an investment or a financial instrument and the cost basis of the investment or financial instrument, without regard to unrealized appreciation or depreciation previously recognized, and includes investments written-off during the period net of recoveries and realized gains or losses from in-kind redemptions. Net proceeds excludes any prepayment penalties, exit fees, and OID and EOT acceleration. Prepayment penalties and exit fees received at the time of sale or redemption are included in fee income on the Consolidated Statements of Operations. OID and EOT acceleration is included in interest income on the Consolidated Statement of Operations.
Net Unrealized Appreciation or Depreciation
Net unrealized appreciation or depreciation reflects the net change in the fair value of the investment portfolio and financial instruments and the reclassification of any prior period unrealized appreciation or depreciation on exited investments and financial instruments to realized gains or losses.
Earnings Per Share
Basic earnings per share (“EPS”) is computed by dividing net income available to common stockholders by the weighted-average number of common shares outstanding for the period. Other potentially dilutive common shares, and the related impact to earnings are considered when calculating earnings per share on a diluted basis. Potential common shares associated with the conversion option embedded in the Convertible Notes are anti-dilutive when the Company’s average NAV is below the conversion price.
Income Taxes
The Company intends to elect to be treated for U.S. federal tax purposes as a RIC under Subchapter M of the Code and operate in a manner so as to qualify annually thereafter for the tax treatment applicable to RICs. As a RIC, the Company generally will not pay corporate-level income tax on the portion of its taxable income distributed to stockholders, generally required to be at least 90% of its investment company taxable income (which is generally its net ordinary taxable income and realized net short-term capital gains in excess of realized net long-term capital losses) and 90% of its tax-exempt income to maintain its RIC status (pass-through tax treatment for amounts distributed).
The Company evaluates tax positions taken in the course of preparing the Company’s tax returns to determine whether the tax positions are “more-likely-than-not” to be sustained by the applicable tax authority in accordance with ASC Topic 740, Income Taxes (“ASC 740”), as modified by ASC 946. Tax benefits of positions not deemed to meet the more-likely-than-not threshold, or uncertain tax positions, would be recorded as tax expense in the current year. It is the Company’s policy to recognize accrued interest and penalties related to uncertain tax benefits in income tax expense. The Company has no material uncertain tax positions as of December 31, 2020. All the Company’s tax returns remain subject to examination by U.S. federal and state tax authorities.
Distributions
Distributions to common stockholders are recorded on the record date. The amount to be paid out as a distribution is determined by the Board each quarter and is generally based upon the earnings estimated by management. Net realized capital gains, if any, are distributed at least annually, although the Company may decide to retain such capital gains for investment.
121
Note 3. Investments
The Company provides debt, including loans and equipment financings, to growth stage companies, including venture capital-backed companies and companies with institutional equity investors, primarily in the United States. The Company’s investment strategy includes making investments consisting primarily of term loans and equipment financings, and, to a lesser extent, working capital loans, equity and equity-related investments. In addition, the Company may obtain warrants or contingent exit fees at funding from many of the portfolio companies.
Debt Securities
The Company’s debt securities primarily consist of direct investments in interest-bearing secured loans and equipment financings to privately held companies based in the United States. Secured loans are generally secured by a blanket first lien or a blanket second lien on the assets of the portfolio company. Equipment financings typically include a specific asset lien on mission critical assets as well as a second lien on the assets of the portfolio company. These debt securities typically have a term of between three and five years from the original investment date. Certain of the debt securities are “covenant-lite” loans, which generally are loans that do not have a complete set of financial maintenance covenants and have covenants that are incurrence-based, meaning they are only tested and can only be breached following an affirmative action of the borrower rather than by a deterioration in the borrower’s financial condition. The equipment financings in the investment portfolio generally have fixed interest rates. The loans in the investment portfolio generally have fixed interest rates or floating interest rates subject to interest rate floors. Both equipment financings and loans generally include an EOT payment.
The specific terms of each debt security vary depending on the creditworthiness of the portfolio company and the projected value of the financed assets. Companies with stronger creditworthiness may receive an initial period of lower financing factor, which is analogous to an interest-only period on a traditional term loan. Equipment financings may include upfront interim payments and security deposits. Equipment financing arrangements have various structural protections, including customary default penalties, information and reporting rights, material adverse change or investor abandonment provisions, consent rights for any additions or changes to senior debt, and, as needed, intercreditor agreements with cross-default provisions to protect the Company’s second lien positions.
Warrant Investments
In connection with the Company’s debt investments, the Company may receive equity warrants in the portfolio company. Warrants received in connection with a debt investment typically include a potentially discounted contract price to exercise, and thus, as a portfolio company appreciates in value, the Company may achieve additional investment return from this equity interest. The warrants are typically contain provisions that protect the Company as a minority-interest holder, as well as secured or unsecured put rights, or rights to sell such securities back to the portfolio company, upon the occurrence of specified events. In certain cases, the Company may also obtain follow-up rights in connection with these equity interests, which allow the Company to participate in future financing rounds.
Equity Investments
In specific circumstances, the Company may seek to make direct equity investments in situations where it is appropriate to align the interests of the Company with key management and stockholders of the portfolio company, and to allow for participation in the appreciation in the equity values of portfolio company. These equity investments are generally made in connection with debt investments. The Company seeks to maintain fully diluted equity positions in the portfolio companies of 5% to 50% and may have controlling equity interests in some instances.
122
Portfolio Industry Classification
The Company’s portfolio investments are in companies conducting business in a variety of industries. The following table summarizes the composition of the Company’s portfolio investments by industry at cost and fair value and as a percentage of the total portfolio as of December 31, 2020 (dollars in thousands):
| | Cost | | Fair Value | | ||||||
Industry |
| Amount |
| % |
| Amount |
| % | | ||
Manufacturing | | $ | 103,471 |
| 20.8% | | $ | 99,709 |
| 20.2% | |
Professional, Scientific, and Technical Services | |
| 77,831 |
| 15.6% | |
| 78,893 |
| 16.0% | |
Retail Trade | |
| 78,534 |
| 15.7% | |
| 75,664 |
| 15.4% | |
Finance and Insurance | |
| 35,320 |
| 7.0% | |
| 35,699 |
| 7.2% | |
Information | |
| 31,843 |
| 6.4% | |
| 30,709 |
| 6.2% | |
Rental and Leasing Services | |
| 29,055 |
| 5.8% | |
| 29,138 |
| 5.9% | |
Utilities | | | 26,800 |
| 5.4% | | | 27,083 | | 5.5% | |
Pharmaceutical | |
| 17,503 |
| 3.5% | |
| 24,240 |
| 4.9% | |
Wholesale Trade | |
| 23,850 |
| 4.8% | |
| 23,903 |
| 4.8% | |
Agriculture, Forestry, Fishing and Hunting | |
| 20,981 |
| 4.2% | |
| 20,837 |
| 4.2% | |
Real Estate | |
| 17,267 |
| 3.5% | |
| 17,316 |
| 3.5% | |
Health Care and Social Assistance | | | 14,348 |
| 2.9% | | | 11,422 | | 2.3% | |
Educational Services | | | 9,359 |
| 1.9% | | | 9,816 | | 2.0% | |
Construction | |
| 9,804 |
| 2.0% | |
| 6,894 |
| 1.4% | |
Administrative and Support and Waste Management and Remediation Services | |
| 2,370 |
| 0.5% | |
| 2,328 |
| 0.5% | |
Total | | $ | 498,336 |
| 100.0% | | $ | 493,651 |
| 100.0% | |
The geographic composition is determined by the location of the corporate headquarters of the portfolio company. The following table summarizes the composition of the Company’s portfolio investments by geographic region of the United States and other countries at cost and fair value and as a percentage of the total portfolio as of December 31, 2020 (dollars in thousands):
| | Cost |
| Fair Value |
| ||||||
Geographic Region |
| Amount |
| % |
| Amount |
| % | | ||
United States: | | | | | | | | | | | |
West | | $ | 247,204 |
| 49.6% | | $ | 241,096 |
| 48.8% | |
Northeast | |
| 131,692 |
| 26.4% | |
| 127,801 |
| 25.9% | |
Midwest | |
| 47,324 |
| 9.5% | |
| 44,092 |
| 8.9% | |
Mountain | |
| 33,842 |
| 6.8% | |
| 33,969 |
| 6.9% | |
Southeast | |
| 11,011 |
| 2.2% | |
| 17,834 |
| 3.6% | |
South | |
| 463 |
| 0.1% | |
| 1,777 |
| 0.4% | |
Canada | |
| 26,800 |
| 5.4% | |
| 27,082 |
| 5.5% | |
Total | | $ | 498,336 |
| 100.0% | | $ | 493,651 |
| 100.0% | |
The following table summarizes the composition of the Company’s portfolio investments by investment type at cost and fair value and as a percentage of the total portfolio as of December 31, 2020 (dollars in thousands):
| | Cost | | Fair Value |
| ||||||
Investment |
| Amount |
| % |
| Amount |
| % |
| ||
Secured Loan | | $ | 324,544 | | 65.1% | | $ | 320,718 |
| 65.0% | |
Equipment Financing | |
| 122,966 | | 24.7% | | | 122,501 |
| 24.8% | |
Equity | |
| 32,961 | | 6.6% | | | 32,654 |
| 6.6% | |
Warrants | |
| 17,865 | | 3.6% | | | 17,778 |
| 3.6% | |
Total | | $ | 498,336 | | 100.0% | | $ | 493,651 |
| 100.0% | |
123
The Company classifies its investment portfolio in accordance with the requirements of the 1940 Act. Under the 1940 Act, (a) “Control Investments” are defined as investments in which Trinity Capital owns more than 25% of the voting securities or has rights to maintain greater than 50% of the board representation, (b) “Affiliate Investments” are defined as investments in which the Company owns between 5% and 25% (inclusive) of the voting securities and does not have rights to maintain greater than 50% of the board representation, and (c) “Non-Control/Non-Affiliate Investments” are defined as investments that are neither Control Investments nor Affiliate Investments.
The following table summarizes the Company’s control and affiliated investments including realized gains and losses and changes in unrealized appreciation and depreciation for the year ended December 31, 2020 (in thousands, except share data):
| | | | As of December 31, 2020 | | Year Ended December 31, 2020 | |||||||||||||
| | | | | | | | | | | | | | | Net change in | | | | |
| | | | | | | | | | | | | | | Unrealized | | | | |
| | | | | | | | | | | | Interest | | (Depreciation)/ | | Realized | |||
Portfolio Company |
| Investment(1) |
| Fair Value |
| Principal |
| Shares |
| Income |
| Appreciation |
| Gain/(Loss) | |||||
Control Investments |
| |
|
| |
|
|
|
| |
|
| |
|
| |
| ||
Birchbox, Inc. | | | | | | | | | | | | | | | | | | ||
| | Secured Loan, June 1, 2024, Fixed Interest |
| |
|
| |
| |
| | |
| | |
| | |
|
| | Rate 9.0%; EOT 3.0% | | $ | 9,924 |
| $ | 10,000 | | n/a | | $ | 1,289 | | $ | (509) | | $ | — |
| | Preferred Series D | |
| 9,445 |
| $ | — | | 3,140,927 | |
| — | |
| (826) | |
| — |
| |
| |
|
|
| |
| |
| |
|
| |
|
| |
|
|
Edeniq, Inc. | | | | | | | | | | | | | | | | | | ||
| | Secured Loan, June 1, 2021, Fixed Interest | | |
|
| |
| |
| | |
| | |
| | |
|
| | Rate 13.0%; EOT 9.5% | | | 859 |
| $ | 3,039 | | n/a | | $ | — | | $ | (243) | | $ | — |
| | Secured Loan, September 1, 2021, Fixed Interest | |
| |
| |
| |
| |
|
| |
|
| |
|
|
| | Rate 13.0%; EOT 9.5% | |
| 648 |
| $ | 2,282 | | n/a | |
| — | |
| (114) | |
| — |
| | Warrants, December 23, 2026, Preferred Series B | |
| — |
| | n/a | | 2,685,501 | |
| — | |
| — | |
| — |
| | Warrants, December 23, 2026, Preferred Series B | |
| — |
| | n/a | | 2,184,672 | |
| — | |
| — | |
| — |
| | Warrants, March 12, 2028, Preferred Series C | |
| — |
| | n/a | | 5,106,972 | |
| — | |
| — | |
| — |
| | Warrants, October 15, 2028, Preferred Series C | |
| — |
| | n/a | | 3,850,294 | |
| — | |
| — | |
| — |
| | Preferred Series B | |
| — |
| | n/a | | 7,807,499 | |
| — | |
| — | |
| — |
| | Preferred Series C | |
| — |
| | n/a | | 2,441,082 | |
| — | |
| — | |
| — |
| | Convertible Note | |
| — |
| $ | 1,303 | | n/a | |
| — | |
| — | |
| — |
| |
| |
| |
| |
| |
| |
|
| |
|
| |
|
|
Project Frog, Inc. | | | | | | | | | | | | | | | | | | ||
| | Secured Loan, May 1, 2023, Fixed Interest | |
|
|
| |
| |
| |
|
| |
|
| |
|
|
| | Rate 12.0% | |
| 4,029 |
| $ | 4,128 | | n/a | |
| 552 | |
| (16) | |
| — |
| | Warrants, July 26, 2026, Preferred Series AA | |
| 2 |
| | n/a | | 391,990 | |
| — | |
| (16) | |
| — |
| | Preferred Series AA-1 | |
| 36 |
| | n/a | | 8,118,527 | |
| — | |
| (666) | |
| — |
| | Preferred Series BB | |
| 449 |
| | n/a | | 6,300,134 | |
| — | |
| (2,218) | |
| — |
| | | | | | | | | | | | | | | | | | ||
Vertical Communications, Inc. | | | | | | | | | | | | | | | | | | ||
| | Secured Loan, November 1, 2024, Fixed Interest | |
|
|
| |
| |
| |
|
| |
|
| |
|
|
| | Rate 9.5%; EOT 26.4% | |
| 12,787 |
| $ | 12,000 | | n/a | |
| 1,378 | |
| (150) | |
| — |
| | Secured Loan, July 1, 2022, Fixed Interest | |
| |
| | | |
| |
|
| |
|
| |
|
|
| | Rate 9.5% | |
| 816 |
| $ | 807 | | n/a | |
| 47 | |
| 9 | |
| — |
| | Warrants, July 11, 2026, Preferred Series A | |
| — |
| | n/a | | 828,479 | |
| — | |
| — | |
| — |
| | Preferred Series 1 | |
| — |
| | n/a | | 3,892,485 | |
| — | |
| — | |
| — |
| | Convertible Notes | |
| 3,350 |
| | 5,500 | | n/a | |
| — | |
| (616) | |
| — |
| |
| |
|
|
| |
| |
| |
|
| |
|
| |
|
|
WorkWell Prevention and Care Inc. | | | | | | | | | | | | | | | | | | ||
| | Secured Loan, March 1, 2024, Fixed Interest | |
|
|
| |
| |
| |
|
| |
|
| |
|
|
| | Rate 8.0%; EOT 10.0% | |
| 3,493 |
| $ | 3,370 | | n/a | |
| 320 | |
| (115) | |
| — |
| | Secured Loan, March 1, 2024, Fixed Interest | |
|
|
| | | |
| |
|
| |
| | |
|
|
| | Rate 8.0%; EOT 10.0% | |
| 693 |
| $ | 700 | | n/a | |
| 75 | |
| (41) | |
| — |
| | Common Stock | |
| — |
| | n/a | | 7,000,000 | |
| — | |
| (51) | |
| — |
| | Preferred Series P | |
| 657 |
| | n/a | | 3,450 | |
| — | |
| (2,793) | |
| — |
| | Convertible Note | |
| 1,542 |
| | 1,470 | | n/a | |
| — | |
| 23 | |
| — |
Total Control Investments | | $ | 48,730 |
| |
| |
| | $ | 3,661 | | $ | (8,342) | | $ | — | ||
| |
| |
|
|
| |
| |
| |
|
| |
|
| |
|
|
Affiliate Investments | |
|
|
| |
| |
| |
|
| |
|
| |
|
| ||
Nanotherapeutics, Inc. | | | | | | | | | | | | | | | | | | ||
| | Warrants, November 14, 2021, Common Stock | |
| 2,216 |
| | n/a | | 67,961 | |
| — | |
| 1,094 | |
| — |
| | Common Stock (2) | |
| 12,856 |
| | n/a | | 382,277 | |
| — | |
| 6,165 | |
| — |
| | | | | | | | | | | | | | | | | | ||
Store Intelligence, Inc. | | | | | | | | | | | | | | | | | | ||
| | Secured Loan, June 1, 2024, Fixed Interest | |
|
|
| |
| |
| |
|
| |
|
| |
|
|
| | Rate 12.0%; EOT 7.8% | |
| 11,884 |
| $ | 12,001 | | n/a | |
| 1,191 | |
| (348) | |
| — |
| | Preferred Series A | |
| 694 |
| | n/a | | 1,430,000 | |
| — | |
| 86 | |
| — |
Total Affiliate Investments | | $ | 27,650 |
| |
| |
| | $ | 1,191 | | $ | 6,997 | | $ | — | ||
| |
| |
|
|
| |
| |
| |
|
| |
|
| |
|
|
Total Control and Affiliate Investments | | $ | 76,380 |
| |
| |
| | $ | 4,852 | | $ | (1,345) | | $ | — | ||
| (1) | This schedule should be read in conjunction with the Consolidated Schedule of Investments and notes to the financial statements. Supplemental information can be located within the Consolidated Schedule of Investments including cost of investments and if the investments are income producing. |
124
| (2) | Certain third parties have rights to 17,485 shares of Nanotherapeutics common stock at a fair value of approximately $0.6 million as of December 31, 2020. |
Unconsolidated Significant Subsidiaries
In accordance with Rule 10-01(b)(1) of Regulation S-X, as amended, the Company must determine which of its unconsolidated controlled portfolio companies, if any, are considered “significant subsidiaries.” In evaluating these unconsolidated controlled portfolio companies, there are two significance tests utilized per Rule 1-02(w) of Regulation S-X to determine if any of the Company’s Control Investments (as defined in “Note 2 - Summary of Significant Accounting Policies”) are considered significant subsidiaries: the investment test, and the income test. As of December 31, 2020, the Company did not have any significant subsidiaries.
Certain Risk Factors
In the ordinary course of business, the Company manages a variety of risks including market risk, credit risk and liquidity risk. The Company identifies, measures and monitors risk through various control mechanisms, including trading limits and diversifying exposures and activities across a variety of instruments, markets and counterparties.
Market risk is the risk of potential adverse changes to the value of financial instruments because of changes in market conditions, including as a result of changes in the credit quality of a particular issuer, credit spreads, interest rates, and other movements and volatility in security prices or commodities. In particular, the Company may invest in issuers that are experiencing or have experienced financial or business difficulties (including difficulties resulting from the initiation or prospect of significant litigation or bankruptcy proceedings), which involves significant risks. The Company manages its exposure to market risk through the use of risk management strategies and various analytical monitoring techniques.
The Company’s investments may, at any time, include securities and other financial instruments or obligations that are illiquid or thinly traded, making purchase or sale of such securities and financial instruments at desired prices or in desired quantities difficult. Furthermore, the sale of any such investments may be possible only at substantial discounts, and it may be extremely difficult to value any such investments accurately.
The Company’s investments consist of growth stage companies, many of which have relatively limited operating histories and also may experience variation in operating results. Many of these companies conduct business in regulated industries and could be affected by the changes in government regulations. Most of the Company’s borrowers will need additional capital to satisfy their continuing working capital needs and other requirements, and in many instances, to service the interest and principal payments on the debt.
Concentrations of Credit Risk
Credit risk is the risk of default or non-performance by portfolio companies, equivalent to the investment’s carrying amount. The top three industries of the Company’s portfolio companies as of December 31, 2020, are in the “Manufacturing,” “Professional, Scientific, and Technical Services” and “Retail Trade” sectors. Industry and sector concentrations will vary from period to period based on portfolio activity.
As of December 31, 2020, the Company’s ten largest portfolio companies represented approximately 42.5% of the total fair value of the Company’s investments in portfolio companies. As of December 31, 2020, the Company had 14 portfolio companies that represented 5% or more of the Company’s net assets. The Company did not have any investments as of December 31, 2019.
125
Note 4. Fair Value of Financial Instruments
ASC 820 defines fair value, establishes a framework for measuring fair value, and establishes a fair value hierarchy based on the quality of inputs used to measure fair value and enhances disclosure requirements for fair value measurements. The Company accounts for its investments at fair value.
In accordance with ASC 820, the Company has categorized its investments based on the priority of the inputs to the valuation technique into a three-level fair value hierarchy. The fair value hierarchy gives the highest priority to quoted prices in active markets for identical investments (Level 1) and the lowest priority to unobservable inputs (Level 3). See “Note 2 - Summary of Significant Accounting Policies.”
As required by ASC 820, when the inputs used to measure fair value fall within different levels of the hierarchy, the level within which the fair value measurement is categorized is based on the lowest level input that is significant to the fair value measurement in its entirety. For example, a Level 3 fair value measurement may include inputs that are observable (Levels 1 and 2) and unobservable (Level 3). Therefore, unrealized appreciation and depreciation related to such investments categorized within the Level 3 tables below may include changes in fair value that are attributable to both observable inputs (Levels 1 and 2) and unobservable inputs (Level 3).
As of December 31, 2020, the Company’s portfolio investments consisted primarily of investments in secured loans and equipment financings. All of the Company’s portfolio investments were categorized as Level 3 as of December 31, 2020. The Company held no portfolio investments as of December 31, 2019.
The fair value determination of each portfolio investment categorized as Level 3 required one or more of the following unobservable inputs:
| ● | Financial information obtained from each portfolio company, including unaudited statements of operations and balance sheets for the most recent period available as compared to budgeted numbers; |
| ● | Current and projected financial condition of the portfolio company; |
| ● | Current and projected ability of the portfolio company to service its debt obligations; |
| ● | Type and amount of collateral, if any, underlying the investment; |
| ● | Current financial ratios (e.g., fixed charge coverage ratio, interest coverage ratio and net debt/EBITDA ratio) applicable to the investment; |
| ● | Current liquidity of the investment and related financial ratios (e.g., current ratio and quick ratio); |
| ● | Pending debt or capital restructuring of the portfolio company; |
| ● | Projected operating results of the portfolio company; |
| ● | Current information regarding any offers to purchase the investment; |
| ● | Current ability of the portfolio company to raise any additional financing as needed; |
| ● | Changes in the economic environment, which may have a material impact on the operating results of the portfolio company; |
| ● | Internal occurrences that may have an impact (both positive and negative) on the operating performance of the portfolio company; |
| ● | Qualitative assessment of key management; |
126
| ● | Contractual rights, obligations or restrictions associated with the investment; and |
| ● | Time to exit. |
The use of significant unobservable inputs creates uncertainty in the measurement of fair value as of the reporting date. The significant unobservable inputs used in the fair value measurement of the Company’s investments, are (i) earnings before interest, tax, depreciation, and amortization (“EBITDA”) and revenue multiples (both projected and historic), and (ii) volatility assumptions. Significant increases (decreases) in EBITDA and revenue multiple inputs in isolation would result in a significantly higher (lower) fair value measurement. Similarly, significant increases (decreases) in volatility inputs in isolation would result in a significantly higher (lower) fair value assessment. On the contrary, significant increases (decreases) in weighted average cost of capital inputs in isolation would result in a significantly lower (higher) fair value measurement. However, due to the nature of certain investments, fair value measurements may be based on other criteria, such as third-party appraisals of collateral and fair values as determined by independent third parties, which are not presented in the tables below.
The following table provides a summary of the significant unobservable inputs used to fair value the Level 3 portfolio investments as of December 31, 2020 (dollars in thousands):
|
| Fair Value as of |
| |
| |
| |
| |
| |
| | December 31, | | Valuation Techniques/ | | Unobservable | | | | Weighted | | |
Investment Type |
| 2020 |
| Methodologies |
| Inputs (1) |
| Range |
| Average (2) |
| |
|
| | | | | | | | | | | |
Debt investments | | $ | 330,184 |
| Discounted Cash Flows |
| Hypothetical Market Yield |
| 9.5% - 31.2% | | 15.1 | % |
| |
|
|
|
|
|
|
|
|
|
| |
| |
| 99,053 |
| Originated within the past three months |
| Origination Market Yield |
| 12.9% - 15.2% | | 14.2 | % |
| | | | | | | | | | | | |
| |
| 2,211 |
| Liquidation Scenario |
| Probability Weighting of Alternative Outcomes |
| 60.0% - 90.0% | | n/a | |
| | | | | | | | | | | | |
| |
| 11,771 |
| Transactions Precedent(6) |
| Transaction Price |
| n/a | | n/a | |
| |
|
|
|
|
|
|
| |
|
| |
Equity investments | |
| 3,623 |
| Liquidation Scenario |
| Probability Weighting of Alternative Outcomes |
| 30.0% - 70.0% |
| n/a | |
| | | | | | | | | | | | |
| | | 5,550 | | Market Approach |
| Revenue Multiple Only (3) | | 0.5 - 0.9 | | 0.7 | |
| | | | | | | | | | | | |
| |
| 23,481 |
| Market Approach |
| Revenue Multiple (3) |
| 0.36x - 3.0x | | 1.8 | x |
| |
|
|
|
|
| Company Specific Adjustment (4) |
| (17.5)% - 150.0% | | 74.9 | % |
| | | | | | | Volatility (5) | | 45.0% - 80.0% | | 59.8 | % |
| |
|
|
|
|
| Risk-Free Interest Rate |
| 0.1% - 0.2% | | 0.1 | % |
| |
|
|
|
|
| Estimated Time to Exit (in years) |
| 0.5 - 2.0 |
| 1.1 | |
| |
|
|
|
|
|
|
| |
|
| |
Warrants | |
| 15,133 |
| Market Approach |
| Revenue Multiple (3) |
| 0.3x - 20.75x |
| 3.2 | x |
| | | | | | | EBITDA Multiple | | n/a | | 10.9 | x |
| |
|
|
|
|
| Company Specific Adjustment (4) |
| (50.0)% - 10.0% | | (13.1) | % |
| |
|
|
| |
| Volatility (5) |
| 20.0% - 104.7% | | 53.4 | % |
| |
|
|
|
|
| Risk-Free Interest Rate |
| 0.1% - 3.0% | | 0.9 | % |
| |
|
|
|
|
| Estimated Time to Exit (in years) |
| 0.2 - 10.0 |
| 3.3 | |
| | | | | | | | | | | | |
| | | 2,645 | | Black Scholes Option Pricing Model | | Volatility (5) | | 46.8% - 132.3% | | 52.0 | % |
| | | | | | | Risk-Free Interest Rate | | 0.1% - 0.7% | | 0.1 | % |
| | | | | | | Estimated Time to Exit (in years) | | 0.5 - 7.3 | | 0.8 | |
| | | | | | | | | | | | |
Total Level Three Investments | | $ | 493,651 |
|
|
|
|
|
|
|
| |
| (1) | The significant unobservable inputs used in the fair value measurement of the Company’s debt securities are hypothetical market yields and premiums/(discounts). The hypothetical market yield is defined as the exit price of an investment in a hypothetical market to hypothetical market participants where buyers and sellers are willing participants. The significant unobservable inputs used in the fair value measurement of the Company’s equity and warrant securities are revenue multiples and portfolio company specific adjustment factors. Additional inputs used in the option pricing model (“OPM”) include industry volatility, risk free interest rate and estimated time to exit. Significant increases (decreases) in the inputs in isolation would result in a significantly higher (lower) fair value measurement, depending on the materiality of the investment. For some investments, additional consideration may be given to data from the last round of financing or merger/acquisition events near the measurement date. |
127
| (2) | Weighted averages are calculated based on the fair market value of each investment. |
| (3) | Represents amounts used when the Company has determined that market participants would use such multiples when pricing the investments. |
| (4) | Represents amounts used when the Company has determined market participants would take into account these discounts when pricing the investments. |
| (5) | Represents the range of industry volatility used by market participants when pricing the investment. |
| (6) | Represents investments where there is an observable transaction or pending event for the investment. |
The following table provides a summary of changes in the debt, including loans and equipment financings (collectively “Debt”), equity and equity warrants fair value of the Company’s Level 3 portfolio investments for the year ended December 31, 2020 (in thousands):
| | Type of Investment | ||||||||||
| | | | | | | | Equity | | | | |
|
| Debt |
| Equity |
| Warrants |
| Total | ||||
Fair Value as of January 1, 2020 | | $ | — | | $ | — | | $ | — | | $ | — |
Formation Transactions acquisitions | |
| 375,858 | |
| 24,066 | |
| 17,099 | |
| 417,023 |
Purchases, net of deferred fees of $1.4 million | |
| 234,418 | |
| 2,170 | |
| 1,976 | |
| 238,564 |
Non-cash conversion | | | (10,148) | | | 10,879 | | | 532 | | | 1,263 |
Proceeds from Paydowns and Sales | |
| (157,046) | |
| (3,855) | |
| — | |
| (160,901) |
Amortization and Accretion | |
| 11,788 | |
| — | |
| — | |
| 11,788 |
Net Realized Gain/(Loss) | |
| (7,361) | |
| (300) | |
| (1,742) | |
| (9,403) |
Third Party Participation (1) | | | — | | | 283 | | | — | | | 283 |
Change in Unrealized Appreciation/(Depreciation) | |
| (4,290) | |
| (589) | |
| (87) | |
| (4,966) |
Fair Value as of December 31, 2020 | | $ | 443,219 | | $ | 32,654 | | $ | 17,778 | | $ | 493,651 |
| | | | | | | | | | | | |
Net change in unrealized appreciation/depreciation on Level 3 investments still held as of December 31, 2020 | | $ | (4,290) | | $ | (589) | | $ | (87) | | $ | (4,966) |
| (1) | Certain third parties have rights to 17,485 shares of Nanotherapeutics common stock at a fair value of approximately $0.6 million as of December 31, 2020. The activity related to these shares and the related liability is recorded against unrealized appreciation (depreciation). |
During the year ended December 31, 2020, there were no transfers into or out of Level 3.
Fair Value of Financial Instruments Carried at Cost
As of December 31, 2020, the carrying value of the Credit Facility is approximately $132.9 million, net of unamortized deferred financing costs of $2.1 million. The carrying value of the Company’s Credit Facility as of December 31, 2020 approximates the fair value, which was estimated using a market yield approach with Level 3 inputs.
As discussed in “Note 5 - Borrowings,” as of December 31, 2020, the 2025 Notes have a fixed interest rate with a carrying value of approximately $120.3 million, net of unamortized deferred financing costs of $4.7 million. The fair value of the 2025 Notes as of December 31, 2020 was $131.4 million, which was estimated using a relative market yield approach with Level 3 inputs.
As of December 31, 2020, the carrying value of the Convertible Notes is approximately $46.6 million, net of unamortized deferred financing costs and discount of $3.4 million. The Convertible Notes have a fixed interest rate as discussed in “Note 5 – Borrowings.” The cost of the Convertible Notes as of December 31, 2020 approximates the fair value, based on the recent funding.
128
The fair value amounts have been measured as of the reporting date and have not been reevaluated or updated for purposes of these financial statements subsequent to that date. As such, the fair values of these financial instruments subsequent to the reporting date may be different than amounts reported.
Note 5. Borrowings
Credit Suisse Credit Facility
On January 9, 2020, TF1 and its affiliates borrowed $190.0 million under the Credit Facility. On January 16, 2020, in connection with the Formation Transactions, through its wholly owned subsidiary, TF1, the Company became a party to, and assumed, the Credit Facility with Credit Suisse. During the year ended December 31, 2020, the Company borrowed an additional $30.0 million and made repayments of $85.0 million to Credit Suisse. The Company incurred approximately $4.0 million of financing costs in connection with the Credit Facility that were capitalized and deferred using the straight-line method over the life of the facility. As of December 31, 2020, unamortized deferred financing costs related to the Credit Facility were $2.1 million and presented as a direct deduction from the carrying amount of the debt liability on the Consolidated Statements of Assets and Liabilities.
The Credit Facility matures on January 8, 2022, unless extended. Borrowings under the Credit Facility bear interest at a rate of the three-month London Interbank Offered Rate (“LIBOR”) plus 3.25%. The Credit Facility is collateralized by all investments held by TF1 and permits an advance rate of up to 65% of eligible investments. The Company has the ability to borrow up to an aggregate of $300.0 million, and the Credit Facility borrowing base contains certain criteria for eligible investments and includes concentration limits as defined in the Credit Facility. As of December 31, 2020, the Company had $135.0 million in borrowings outstanding under the Credit Facility and a borrowing availability of approximately $42.0 million.
The summary information regarding the Credit Facility is as follows (dollars in thousands):
| | Year Ended | | |
| | December 31, 2020 |
| |
Stated interest expense | | $ | 5,052 |
|
Amortization of deferred financing costs | | | 1,918 | |
Total interest and amortization of deferred financing costs | | $ | 6,970 | |
| | | | |
Weighted average effective interest rate | |
| 5.6 | % |
Weighted average outstanding balance | | $ | 126,271 | |
The Credit Facility contains covenants that, among other things, require the Company to maintain minimum tangible net worth and leverage ratios, minimum cash balance of $15.0 million, and a cash reserve of 60 days for interest.
2025 Notes
Concurrent with the completion of a private common stock offering, on January 16, 2020, the Company completed the “144A Note Offering” of $105.0 million in aggregate principal amount of the unsecured 2025 Notes in reliance upon the available exemptions from the registration requirements of the Securities Act of 1933, as amended (the “Securities Act”). Keefe, Bruyette & Woods, Inc. (“KBW”), as the initial purchaser, exercised in full its option to purchase or place additional Notes and on January 29, 2020 the Company issued and sold an additional $20.0 million in aggregate principal amount of the 2025 Notes. As a result, the Company issued and sold a total of $125.0 million in aggregate principal amount of the 2025 Notes pursuant to the 144A Note Offering.
The 2025 Notes were issued pursuant to an Indenture dated as of January 16, 2020 (the “Base Indenture”), between the Company and U.S. Bank National Association, as trustee (the “Trustee”), and a First Supplemental Indenture, dated as of January 16, 2020 (the “First Supplemental Indenture” and together with the Base Indenture, the “2025 Notes
129
Indenture”), between the Company and the Trustee. The 2025 Notes mature on January 16, 2025 (the “Maturity Date”), unless repurchased or redeemed in accordance with their terms prior to such date. The 2025 Notes are redeemable, in whole or in part, at any time, or from time to time, at the Company’s option, on or after January 16, 2023 at a redemption price equal to 100% of the outstanding principal amount thereof, plus accrued and unpaid interest to, but excluding, the date of redemption. The holders of the 2025 Notes do not have the option to have the notes repaid or repurchased by the Company prior to the Maturity Date.
The 2025 Notes bear interest at a fixed rate of 7.00% per year payable quarterly on March 15, June 15, September 15 and December 15 of each year, commencing on March 15, 2020. The 2025 Notes are direct, general unsecured obligations of the Company and rank pari passu, or equal in right of payment with all of the Company’s existing and future unsecured indebtedness or other obligations that are not so subordinated.
Concurrently with the closing of the 144A Note Offering on January 16, 2020, the Company entered into a registration rights agreement (the “2025 Notes Registration Rights Agreement”) for the benefit of the purchasers of the 2025 Notes in the 144A Note Offering. Pursuant to the terms of the 2025 Notes Registration Rights Agreement, the Company filed with the SEC a registration statement registering the public resale of the 2025 Notes by the holders thereof that elected to include their Notes in such registration statement, which was declared effective on October 20, 2020. Under the 2025 Notes Registration Rights Agreement, the Company is obligated to use its commercially reasonable efforts to continuously maintain such registration statement’s effectiveness under the Securities Act, subject to certain permitted blackout periods, for the period described in the 2025 Notes Registration Rights Agreement.
Aggregate offering costs in connection with the 2025 Notes issuance, including the underwriter’s discount and commissions, were approximately $5.8 million which were capitalized and deferred. As of December 31, 2020, unamortized deferred financing costs related to the 2025 Notes were $4.7 million and were included in the Notes payable on the Consolidated Statements of Assets and Liabilities.
For the year ended December 31, 2020, the components of interest expense and related fees for the 2025 Notes are as follows (in thousands):
| | Year Ended | ||
| | December 31, 2020 | ||
Stated interest expense | | $ | 8,385 | |
Amortization of deferred financing costs |
| | 1,078 | |
Total interest and amortization of deferred financing costs | | $ | 9,463 | |
| | | | |
Weighted average effective interest rate | | | 7.9 | % |
Convertible Notes due 2025
On December11, 2020, the Company completed a private offering (the “Private Convertible Note Offering”) of $50 million in aggregate principal amount of its unsecured 6.00% Convertible Notes due 2025 (the “Convertible Notes”) in reliance upon the available exemptions from the registration requirements of the Securities Act. KBW acted as the initial purchaser and placement agent in connection with the Private Convertible Note Offering pursuant to a purchase/placement agreement dated December 4, 2020 by and between the Company and KBW.
The Convertible Notes were issued pursuant to the Base Indenture and a Second Supplemental Indenture, dated as of December 11, 2020 (the “Second Supplemental Indenture” and together with the Base Indenture, the “Convertible Notes Indenture”), between the Company and the Trustee.
The Convertible Notes bear interest at a fixed rate of 6.00% per year, subject to additional interest upon certain events, payable semiannually in arrears on May 1 and November 1 of each year, beginning on May 1, 2021. If an investment grade rating is not maintained with respect to the Convertible Notes, additional interest of 0.75% per annum will accrue on the Convertible Notes until such time as the Convertible Notes have received an investment grade rating of “BBB-” (or its equivalent) or better. The rating remained unchanged as of December 31, 2020. The Convertible Notes
130
mature on December 11, 2025 (the “Convertible Notes Maturity Date”), unless earlier converted or repurchased in accordance with their terms.
Holders may convert their Convertible Notes, at their option, at any time on or prior to the close of business on the business day immediately preceding the Convertible Notes Maturity Date. The conversion rate is initially 66.6667 shares of the Company’s common stock, per $1,000 principal amount of the Convertible Notes (equivalent to an initial conversion price of approximately $15.00 per share of common stock). The conversion rate will be subject to adjustment in some events but will not be adjusted for any accrued and unpaid interest. In addition, following certain corporate events, further described in the Convertible Note Indenture, that occur prior to the Convertible Notes Maturity Date, the Company will increase the conversion rate for a holder who elects to convert its Convertible Notes in connection with such a corporate event in certain circumstances. Upon conversion of the Convertible Notes, the Company will pay or deliver, as the case may be, cash, shares of common stock, or a combination of cash and shares of common stock, at the Company’s election, per $1,000 principal amount of the Convertible Notes, equal to the then existing conversion rate.
At the Company’s option, it may cause holders to convert all or a portion of the then outstanding principal amount of the Convertible Notes plus accrued but unpaid interest, at any time on or prior to the close of business on the business day immediately preceding the Convertible Notes Maturity Date, if the closing sale price of the Company’s common stock for any 30 consecutive trading days exceeds 120% of the conversion price, as may be adjusted. Upon such conversion, the Company will pay or deliver, as the case may be, cash, shares of common stock, or a combination of cash and shares of common stock, at the Company’s election, per $1,000 principal amount of the Convertible Notes, equal to the then existing conversion rate, and a forced conversion make-whole payment (as defined in the Second Supplemental Indenture), if any, in cash.
The Company may not redeem the Convertible Notes at its option prior to maturity. In addition, if the Company undergoes a fundamental change (as defined in the Second Supplemental Indenture), holders may require the Company to repurchase for cash all or part of such holders’ Convertible Notes at a repurchase price equal to 100% of the principal amount of the Convertible Notes to be repurchased, plus accrued and unpaid interest to, but excluding, the fundamental change repurchase date.
The Convertible Notes are direct unsecured obligations of the Company and rank pari passu, or equal, in right of payment with all of the Company’s existing and future unsecured indebtedness or other obligations that are not so subordinated, including, without limitation, the 2025 Notes, and senior in right of payment to all of the Company’s future indebtedness or other obligations that are expressly subordinated, or junior, in right of payment to the Convertible Notes.
Concurrently with the closing of the Convertible Note Offering, on December 11, 2020, the Company entered into a registration rights agreement (the “Convertible Notes Registration Rights Agreement”) for the benefit of the holders of the Convertible Notes and the shares of common stock issuable upon conversion thereof. Under the Convertible Notes Registration Rights Agreement and subject to the terms and conditions set forth therein, the Company has agreed to use its commercially reasonable efforts to file with or confidentially submit to the SEC a registration statement registering resales of the Convertible Notes under the Securities Act by the holders thereof, within 180 days after December 11, 2020 (the “Convertible Notes Issue Date”) (or if such 180th day is not a business day, the next succeeding business day). The Company has also agreed to use its commercially reasonable efforts to cause such resale registration statement related to the Convertible Notes to be declared effective by the SEC at the earliest possible time after the initial submission or filing thereof, but in no event later than 270 days after the Convertible Notes Issue Date (or if such 270th day is not a business day, the next succeeding business day), and to continuously maintain such resale registration statement’s effectiveness under the Securities Act, subject to certain permitted blackout periods, for the period described in the Convertible Notes Registration Rights Agreement.
In addition, under the Convertible Notes Registration Rights Agreement and subject to the terms and conditions set forth therein, the Company has agreed to file with or confidentially submit to the SEC a registration statement registering under the Securities Act resales of the shares of common stock to be issued upon the conversion of the Convertible Notes, including shares issued by stock dividend, stock distribution, stock split or otherwise thereupon at the time of such submission or filing, as soon as reasonably practicable after the later of (i) the completion of an initial public
131
offering of the Company’s equity or equity-linked securities, including the Company’s common stock, and the listing of such securities on a national securities exchange (collectively, an “IPO”) and (ii) the date that is 180 days after the Convertible Notes Issue Date (or, if such 180th day is not a business day, the next succeeding business day). The Company has also agreed to use its commercially reasonable efforts to cause such resale registration statement related to the shares of common stock to be issued upon Conversion of the Convertible Notes to be declared effective by the SEC no later than six months after the completion of an IPO and concurrently therewith cause such shares of common stock to be listed on a national securities exchange, and to continuously maintain such resale registration statement’s effectiveness under the Securities Act, subject to certain permitted blackout periods, for the period described in the Convertible Notes Registration Rights Agreement.
Nevertheless, the Company can offer no assurance that it will file any such resale registration statements, that the SEC will ever declare either of such resale registration statements effective, or that the shares of common stock issued upon conversion of the Convertible Notes will ever be listed on a national securities exchange.
Aggregate offering costs in connection with the Convertible Note Offering, including the initial purchaser and placement agent discount and commissions, were approximately $1.6 million which were capitalized and deferred. As of December 31, 2020, unamortized deferred financing costs related to the Convertible Notes were $1.6 million and were included in the Convertible Notes payable on the Consolidated Statements of Assets and Liabilities.
The Convertible Notes are accounted for in accordance with ASC 470-20 Debt Instruments with Conversion and Other Options. In accounting for the Convertible Notes, the Company estimated at the time of issuance that the values of the debt and the embedded conversion feature of the Convertible Notes were approximately 99.1% and 0.9%, respectively. The original issue discount of 0.9%, or approximately $0.5 million, attributable to the conversion feature of the Convertible Notes was recorded in “capital in excess of par value” in the Consolidated Statements of Assets and Liabilities. As a result, the Company records interest expense comprised of both stated interest expense as well as the original issue discount resulting in an estimated effective interest rate of approximately 7.1% annualized.
As of December 31, 2020, the components of the carrying value of the Convertible Notes were as follows (in thousands):
| | Year Ended | | |
| | December 31, 2020 | | |
Principal amount of debt | | $ | 50,000 | |
Unamortized debt issuance cost | | | (1,672) | |
Original issue discount related to equity component, net of accretion | | | (467) | |
Original issue discount, net of accretion | | | (1,308) | |
Carrying value of Convertible Notes | | $ | 46,552 | |
For the year ended December 31, 2020, the components of interest expense and related fees for the Convertible Notes were as follows (in thousands):
| | Year Ended | ||
| | December 31, 2020 | ||
Stated interest expense | | $ | 175 | |
Amortization of deferred financing costs and original issue discount |
| | 29 | |
Total interest and amortization of deferred financing costs and original issue discount | | $ | 204 | |
| | | | |
Weighted average effective interest rate | | | 7.1 | % |
As of December 31, 2020, the Company was in compliance with the terms of the Credit Facility, the 2025 Notes Indenture, and the Convertible Notes Indenture.
132
Note 6. Commitments and Contingencies
Unfunded Commitments
The Company’s commitments and contingencies consist primarily of unused commitments to extend credit in the form of loans or equipment financings to the Company’s portfolio companies. A portion of unfunded contractual commitments as of December 31, 2020 are generally dependent upon the portfolio company reaching certain milestones before the commitment becomes available. Furthermore, the Company’s credit agreements contain customary lending provisions that allow the Company relief from funding obligations for previously made commitments in instances where the underlying portfolio company experiences materially adverse events that affect the financial condition or business outlook for the Company. Since a portion of these commitments may expire without being withdrawn, unfunded contractual commitments do not necessarily represent future cash requirements. As such, the Company’s disclosure of unfunded contractual commitments as of December 31, 2020 includes only those commitments which are available at the request of the portfolio company and are unencumbered by milestones or additional lending provisions.
As of December 31, 2020, the Company had outstanding unfunded commitments of approximately $0.1 million to one portfolio company, Dandelion, Inc. As of December 31, 2020, the Company had sufficient liquidity (through cash on hand and available borrowings under the Credit Facility) to fund such unfunded commitments should the need arise.
In the normal course of business, the Company enters into contracts that provide a variety of representations and warranties, and general indemnifications. Such contracts include those with certain service providers, brokers and trading counterparties. Any exposure to the Company under these arrangements is unknown as it would involve future claims that may be made against the Company; however, based on the Company’s experience, the risk of loss is remote and no such claims are expected to occur. As such, the Company has not accrued any liability in connection with such indemnifications.
Leases
Effective January 1, 2019, FASB ASU 2016-02, Leases (Topic 842) (“ASU 2016-02”) required that a lessee evaluate its leases to determine whether they should be classified as operating or financing leases. The Company identified one significant operating lease for its office space. The lease commenced February 21, 2017 and expires July 31, 2022. The lease contains a five-year extension option for a final expiration date of July 31, 2027 which the company does not expect to exercise.
The total lease expense incurred for the year ended December 31, 2020 was approximately $0.2 million. As of December 31, 2020, the right of use asset and the lease liability was $0.3 million and $0.4 million, respectively. As of December 31, 2020, the remaining lease term was 1.5 years and the discount rate was 3.25%. The Company has also entered into a lease for new office space with an estimated commencement date in mid-2021 and a lease term of eight years. A right of use asset and corresponding lease liability will be recorded upon commencement of the lease, and future minimum payments under the term of the new lease have been included in the table below.
The following table shows future minimum payments under the Company’s operating leases as of December 31, 2020 (in thousands):
For the Years Ended December 31, |
| | Total |
2021 | | $ | 225 |
2022 |
| | 484 |
2023 |
| | 361 |
2023 | | | 371 |
2024 | | | 380 |
Thereafter | | | 1,619 |
Total | | $ | 3,440 |
133
Legal Proceedings
The Company may, from time to time, be involved in litigation arising out of its operations in the normal course of business or otherwise. Furthermore, third parties may try to seek to impose liability on the Company in connection with the activities of its portfolio companies. As of December 31, 2020, there are no material legal matters or material litigation pending of which the Company is aware.
Note 7. Stockholder’s Equity
The Company authorized 200,000,000 shares of its common stock with a par value of $0.001 per share. On September 27, 2019, the Company was initially capitalized with the issuance of 10 shares of its common stock for an aggregate purchase price of $150 to its sole shareholder.
Private Common Stock Offerings
On January 16, 2020, the Company completed a private offering of shares of its common stock (the “Private Common Stock Offering”) in reliance upon the available exemptions from the registration requirements of the Securities Act, pursuant to which the Company issued and sold 7,000,000 shares of its common stock for aggregate gross proceeds of approximately $105.0 million. KBW acted as the initial purchaser and placement agent in connection with the Private Common Stock Offering pursuant to a purchase/placement agreement, dated January 8, 2020 by and between the Company and KBW. KBW exercised in full its option to purchase or place additional shares and on January 29, 2020 the Company issued and sold an additional 1,333,333 shares of its common stock. As a result, the Company issued and sold a total of 8,333,333 shares of its common stock pursuant to the Private Common Stock Offering for aggregate net proceeds of approximately $114.4 million, net of offering costs of approximately $10.6 million.
Concurrently with the closing of the Private Common Stock Offering, on January 16, 2020, the Company entered into a registration rights agreement for the benefit of the purchasers of the shares of the Company’s common stock in the Private Common Stock Offering and the Legacy Investors (as defined below) that received shares of the Company’s common stock in connection with the Formation Transactions that were not the Company’s directors, officers and affiliates.
On December 15, 2020, at the Company’s 2020 annual meeting of stockholders, the Company’s stockholders approved amending and restating such registration rights agreement to change the registration deadline described below to December 31, 2021 from December 31, 2020. No other changes were made to the registration rights agreement, which as so amended and restated became effective on December 15, 2020 (the “Common Stock Registration Rights Agreement”).
Absent an amendment approved in accordance with the terms of the Common Stock Registration Rights Agreement, the Company is obligated to use commercially reasonable efforts to cause (i) a resale registration statement (the “Resale Registration Statement”) registering the public resale of the shares of the Company’s common stock issued in the Private Common Stock Offering and the Formation Transactions, and the shares of the Company’s common stock issues in respect thereof whether by contingent dividend, stock dividend, stock distribution, stock split, or otherwise, except for such shares issued to the Company’s directors, officers and affiliates (the “Registrable Shares”), to be declared effective by the SEC as soon as practicable after the initial filing of the Resale Registration Statement, but in no event later than December 31, 2021 and (ii) the Registrable Shares to be listed on a national securities exchange concurrently with the effectiveness of the Resale Registration Statement. Under the Common Stock Registration Rights Agreement, the Company is also obligated to use commercially reasonable efforts to continuously maintain the Resale Registration Statement’s effectiveness under the Securities Act, subject to certain permitted blackout periods, for the period described in the Common Stock Registration Rights Agreement.
134
Formation Transactions
On January 16, 2020, immediately following the initial closings of the Private Offerings, the Company used the proceeds from the Private Offerings to complete the Formation Transactions, pursuant to which the Company acquired and assumed all of the assets and liabilities of the Legacy Funds through mergers of the Legacy Funds with and into the Company. In consideration for the Legacy Funds, the Company issued 9,183,185 shares of common stock at $15.00 per share for a total value of approximately $137.7 million and paid approximately $108.7 million in cash to the Legacy Funds’ investors, which included the general partners/managers of the Legacy Funds (the “Legacy Investors”). The acquisition consideration of the Formation Transactions was based on valuations as of December 31, 2019, as adjusted for assets that were disposed of by the Legacy Funds, as well as earnings, capital contributions and distributions paid to the members/limited partners, and material events affecting the portfolio companies of the Legacy Funds subsequent to December 31, 2019 and through the closing date of the Formation Transactions.
As part of the Formation Transactions, the Company also used a portion of the proceeds of the Private Offerings to acquire 100% of the equity interests of Trinity Capital Holdings, LLC (“Trinity Capital Holdings”) for an aggregate purchase price of $10.0 million, which was comprised of 533,332 shares of its common stock totaling approximately $8.0 million and approximately $2.0 million in cash. As a result of this transaction, Trinity Capital Holdings became a wholly owned subsidiary of the Company. Refer to “Note 1 – Organization and Basis of Presentation” for further details.
Long-Term Incentive Plan
The Board has approved the 2019 Trinity Capital Inc. Long-Term Incentive Plan and the Trinity Capital Inc. 2019 Non-Employee Director Restricted Stock Plan, each to be effective upon receipt of exemptive relief from the SEC and stockholder approval of such plans. The Company has applied for an exemptive order from the SEC to permit us to issue securities under such plans. If such exemptive relief and stockholder approval are obtained, the Compensation Committee may award such securities in such amounts and on such terms as the Compensation Committee determines and consistent with any exemptive order the SEC may issue and the terms of such plans, as applicable. The SEC is not obligated to grant an exemptive order to allow this practice and will do so only if it determines that such practice is consistent with stockholder interests and does not involve overreaching by management or the Board. The Company cannot provide any assurance that such exemptive relief from the SEC or such stockholder approval will be received.
Distribution Reinvestment Plan
The Company’s distribution reinvestment plan (“DRIP”) provides for the reinvestment of distributions in the form of common stock on behalf of its stockholders, unless a stockholder has elected to receive distributions in cash. As a result, if the Company declares a cash distribution, its stockholders who have not “opted out” of the DRIP by the opt out date will have their cash distribution automatically reinvested into additional shares of the Company’s common stock. The share requirements of the DRIP may be satisfied through the issuance of common shares or through open market purchases of common shares by the DRIP plan administrator. Newly issued shares will be valued based upon the final closing price of the Company’s common stock on the valuation date determined for each distribution by the Board.
The Company’s DRIP is administered by its transfer agent on behalf of the Company’s record holders and participating brokerage firms. Brokerage firms and other financial intermediaries may decide not to participate in the Company’s DRIP but may provide a similar distribution reinvestment plan for their clients. For the year ended December 31, 2020, the Company issued 271,414 shares of common stock for a total of approximately $3.4 million under the DRIP.
135
Distributions
The following table reflects the distributions per share that the Company has paid, including shares issued under the DRIP, on its common stock during the year ended December 31, 2020 ($ in thousands except per share):
Declaration Date | | Record Date | | Payment Date | | Per Share Amount | |
May 14, 2020 | | May 29, 2020 | | June 5, 2020 | | $ | 0.22 |
August 12, 2020 | | August 21, 2020 | | September 4, 2020 | | | 0.27 |
November 12, 2020 | | November 20, 2020 | | December 4, 2020 | | | 0.27 |
December 22, 2020 | | December 30, 2020 | | January 15, 2021 | | | 0.27 |
Total | | | | | | $ | 1.03 |
Note 8. Earnings Per Share
In accordance with the provisions of ASC Topic 260 – Earnings per Share (“ASC 260”), basic earnings per share is computed by dividing net income available to common stockholders by the weighted-average number of common shares outstanding for the period. Other potentially dilutive common shares, and the related impact to earnings are considered when calculating earnings per share on a diluted basis. Potential common shares associated with the conversion option embedded in the Convertible Notes are anti-dilutive when the Company’s average NAV is below the conversion price. The following table sets forth the computation of the weighted average basic and diluted net increase (decrease) in net assets per share from operations for the year ended December 31, 2020 (in thousands except shares and per share information):
| | | |
| | Year Ended | |
|
| December 31, 2020 | |
Net increase/(decrease) in net assets resulting from operations | | $ | (6,112) |
Weighted average common shares outstanding | |
| 18,092,494 |
Net increase/(decrease) in net assets resulting from operations per common share - basic and diluted | | $ | (0.34) |
For the year ended December 31, 2020, the effect of the Convertible Notes was anti-dilutive and, accordingly, was excluded from the calculation of diluted earnings per share.
Note 9. Income Taxes
The Company intends to elect to be treated for U.S. federal tax purposes as a RIC under Subchapter M of the Code and operate in a manner so as to qualify annually thereafter for the tax treatment applicable to RICs. As a RIC, the Company generally will not pay corporate-level income tax on the portion of its taxable income distributed to stockholders, generally required to be at least 90% of its investment company taxable income (which is generally its net ordinary taxable income and realized net short-term capital gains in excess of realized net long-term capital losses) and 90% of its tax-exempt income to maintain its RIC status (pass-through tax treatment for amounts distributed). The amount to be paid out as a distribution is determined by the Board each quarter and is based upon the annual earnings estimated by the management of the Company. To the extent the Company’s earnings fall below the amount of dividend distributions declared, however, a portion of the total amount of the Company’s distributions for the fiscal year may be deemed a return of capital for tax purposes to the Company’s stockholders.
Because federal income tax regulations differ from accounting principles generally accepted in the United States, distributions in accordance with tax regulations may differ from net investment income and realized gains recognized for financial reporting purposes. Differences may be permanent or temporary in nature. Permanent differences are reclassified among capital accounts in the financial statements to reflect their appropriate tax character. Temporary
136
differences arise when certain items of income, expense, gain or loss are recognized at some time in the future. Also, recent tax legislation requires that income be recognized for tax purposes no later than when recognized for financial reporting purposes.
During the year ended December 31, 2020, the Company reclassified for book purposes amounts arising from permanent book to tax differences primarily related to nondeductible expenses for income tax purposes as follows:
| | | Year Ended |
| | December 31, 2020 | |
Additional paid-in capital | | $ | (738) |
Distributable earnings/(accumulated loss) | | | 738 |
The Company has available $7.1 million of capital losses, which can be used to offset future capital gains. All of these losses are permitted to carry forward for an unlimited period.
For income tax purposes distributions paid to shareholders are reported as ordinary income, return of capital, long-term capital gains, or a combination thereof. The tax character of distributions paid for the year ended December 31, 2020 was ordinary income in the amount of approximately $18.7 million with no distributions made from long-term capital gain. No distributions were paid during the period ended December 31, 2019 as the Company had no operations and had no income subject to distribution.
As of December 31, 2020, the components of distributable earnings on a tax basis detailed below differ from the amounts reflected in the Company’s Consolidated Statements of Assets and Liabilities by temporary book or tax differences primarily arising from the tax treatment of costs related to the acquisition of Trinity Capital Holdings and Legacy Funds and deferral of organization costs.
| | | Year Ended |
| | December 31, 2020 | |
Accumulated capital gains/(losses) | | $ | (7,077) |
Other temporary differences | | | (14,200) |
Undistributed ordinary income | | | 1,607 |
Unrealized appreciation/(depreciation) | | | (4,966) |
Components of distributable earnings | | $ | (24,636) |
| | | |
The following table sets forth the tax cost basis and the estimated aggregate gross unrealized appreciation and depreciation from investments for federal income tax purposes (in thousands):
| | Year Ended | |
| | December 31, 2020 | |
Tax Cost of Investments | | $ | 498,336 |
| | | |
Unrealized appreciation (2) | | $ | 14,879 |
Unrealized depreciation | | | (19,845) |
Net unrealized/(appreciation) depreciation reversed related to net realized gains or losses (1) | | | — |
Net unrealized appreciation/(depreciation) from investments | | $ | (4,966) |
| (1) | The net unrealized (appreciation) depreciation reversed related to net realized gains or losses represents the unrealized appreciation or depreciation recorded on the related asset at the end of the prior period. Investments were recorded at their fair values in the Formation Transactions on January 16, 2020, therefore no reversal of unrealized appreciation (depreciation) was recorded during the year ended December 31, 2020. |
137
| (2) | Certain third parties have rights to 17,485 shares of Nanotherapeutics common stock at a fair value of approximately $0.6 million as of December 31, 2020. The activity related to these shares and the related liability is recorded against unrealized appreciation/(depreciation). |
As of December 31, 2020, the components of distributable earnings on a tax basis detailed below differ from the amounts reflected in the Company’s Consolidated Statements of Assets and Liabilities by temporary book or tax differences primarily arising from the treatment of costs related to the acquisition of Trinity Capital Holdings and Legacy Funds and deferral of organizational cost.
In order for the Company not to be subject to federal excise taxes, it must distribute annually an amount at least equal to the sum of (i) 98% of its ordinary income (taking into account certain deferrals and elections), (ii) 98.2% of its net capital gains from the current year and (iii) any undistributed ordinary income and net capital gains from preceding year on which it paid corporate-level U.S. federal income tax. The Company, at its discretion, may carry forward taxable income in excess of calendar year distributions and pay a 4% excise tax on this income. If the Company chooses to do so, this generally would increase expenses and reduce the amount available to be distributed to stockholders. The Company will accrue excise tax on estimated undistributed taxable income as required on an annual basis. For the period ended December 31, 2020, the Company recorded an expense for excise tax of approximately $0.1 million.
The Company evaluates tax positions taken in the course of preparing the Company’s tax returns to determine whether the tax positions are “more-likely-than-not” to be sustained by the applicable tax authority in accordance with ASC Topic 740, Income Taxes (“ASC 740”), as modified by ASC 946. Tax benefits of positions not deemed to meet the more-likely-than-not threshold, or uncertain tax positions, would be recorded as tax expense in the current year. It is the Company’s policy to recognize accrued interest and penalties related to uncertain tax benefits in income tax expense.
Based on the analysis of the Company’s tax position, the Company has no uncertain tax positions that met the recognition or measurement criteria as of December 31, 2020. The Company does not anticipate any significant increase or decrease in unrecognized tax benefits for the next twelve months. All of the Company’s tax returns remain subject to examination by U.S. federal and state tax authorities.
138
Note 10. Financial Highlights
We were formed on August 12, 2019 and commenced operations on January 16, 2020. Prior to January 16, 2020, we had no operations, except for matters relating to our formation and organization as a BDC. As a result, there are no significant financial results for comparative purposes. The following presents financial highlights for the year ended December 31, 2020 (in thousands except share and per share information):
| | | | |
| | | | |
| | Year Ended | | |
| | December 31, 2020 | | |
Per Share Data: | | |
| |
Net asset value, beginning of period (1) | | $ | 14.97 | |
| | | | |
Net investment income (2) | |
| 1.29 | |
Net realized and unrealized gains/(losses) on investments (3) | |
| (0.81) | |
Costs related to acquisition of Trinity Capital Holdings and Legacy Funds | |
| (0.82) | |
Net decrease in net assets resulting from operations | |
| (0.34) | |
| | | | |
Offering costs | |
| (0.58) | |
Other (10) | | | (0.02) | |
Equity component of convertible notes | | | 0.03 | |
Distributions | | | (1.03) | |
Total increase/(decrease) in net assets | | | (1.94) | |
| | | | |
Net asset value, end of period | | $ | 13.03 | |
| | | | |
Shares outstanding, end of period | |
| 18,321,274 | |
Weighted average shares outstanding (2) | |
| 18,092,494 | |
Total return based on net asset value (4) (7) (8) | |
| (6.1) | % |
| | | | |
Ratio/Supplemental Data: | |
|
| |
Net assets, end of period* | | $ | 238,748 | |
Ratio of total expenses to average net assets (5) | |
| 14.3 | % |
Ratio of net investment income to average net assets (5) | |
| 10.5 | % |
Ratio of interest and credit facility expenses to average net assets (5) | |
| 7.6 | % |
Portfolio turnover rate (6) (8) | |
| 36.5 | % |
Asset coverage ratio (9) | |
| 177.0 | % |
* Rounded to nearest thousand
| (1) | The net asset value as of January 16, 2020 (commencement of operations) is calculated based on the initial common stock purchase price of $15.00 per share less the accumulated loss of $0.03 per share from August 12, 2019 (the date of inception) through December 31, 2019. |
| (2) | Calculated based upon weighted average shares outstanding for the period from January 16, 2020 (commencement of operations) through December 31, 2020. |
| (3) | Net realized and unrealized gains (losses) on investments include rounding adjustments to reconcile the change in net asset value per share. |
| (4) | Total return based on net asset value is calculated as the change in net asset value per share during the period plus declared distributions per share during the period, divided by the beginning net asset value per share. |
| (5) | Annualized. |
139
| (6) | Portfolio turnover rate is calculated using the lesser of year-to-date cash sales/repayments or year-to-date cash purchases over the average of the total investments at fair value. |
| (7) | Total return excluding costs related to acquisition of Trinity Capital Holdings and the Legacy Funds would have been (0.6%). |
| (8) | Not annualized. |
| (9) | Based on outstanding debt of $310.0 million as of December 31, 2020. |
| (10) | Includes the impact of the different share amounts as a result of calculating certain per share data based on the weighted-average basic shares outstanding during the period and certain per share data based on the shares outstanding as of a period end or transaction date. |
Senior Securities
Information about the Company’s senior securities (including debt securities and other indebtedness) is shown in the following table as of December 31, 2020. No senior securities were outstanding as of December 31, 2019.
Class and Period | | Total | | Asset | | Involuntary | | Average | ||
Credit Facility | | | | | | | | | | |
December 31, 2020 | | $ | 135,000 | | $ | 1,770 | | - | | na |
December 31, 2019 | | | - | | | - | | - | | na |
| | | | | | | | | | |
2025 Notes | | | | | | | | | | |
December 31, 2020 | | $ | 125,000 | | $ | 1,770 | | - | | na |
December 31, 2019 | | | - | | | - | | - | | na |
| | | | | | | | | | |
Convertible Notes | | | | | | | | | | |
December 31, 2020 | | $ | 50,000 | | $ | 1,770 | | - | | na |
December 31, 2019 | | | - | | | - | | - | | na |
| | | | | | | | | | |
Total | | | | | | | | | | |
December 31, 2020 | | $ | 310,000 | | $ | 1,770 | | - | | na |
December 31, 2019 | | | - | | | - | | - | | na |
| (1) | Total amount of each class of senior securities outstanding at the end of the period presented. |
| (2) | Asset coverage per unit is the ratio of the carrying value of total assets, less all liabilities excluding indebtedness represented by senior securities in this table to the aggregate amount of senior securities representing indebtedness. Asset coverage per unit is express in terms of dollar amounts per $1,000 of indebtedness and is calculated on a consolidated basis. |
| (3) | The amount to which such class of senior security would be entitled upon the Company’s involuntary liquidation in preference to any security junior to it. The “—” in this column indicates information that the SEC expressly does not require to be disclosed for certain types of senior securities. |
| (4) | Not applicable because the senior securities are not registered for public trading. |
140
Note 11. Related Party Transactions
As of December 31, 2019, the Company had payables to an affiliate of approximately $1.1 million related to organizational and offering cost expenses, which are included in Due to related party on the Consolidated Statements of Assets and Liabilities. The Company repaid these amounts during the quarter ended March 31, 2020.
Through the Formation Transactions, the Company acquired 100% of the equity interests of Trinity Capital Holdings and the Legacy Funds were merged with and into the Company. Members of the Company’s management, including Steven L. Brown, Kyle Brown, Gerald Harder and Ron Kundich, owned 100% of the equity interests in Trinity Capital Holdings and controlling interests in the general partners/managers of the Legacy Funds.
As a result of the Formation Transactions, Messrs. S. Brown, K. Brown, Harder and Kundich collectively received (i) 533,332 shares of the Company’s common stock valued at approximately $8.0 million and approximately $2.0 million in cash in exchange for their equity interests in Trinity Capital Holdings, and (ii) 377,441 shares of the Company’s common stock valued at approximately $5.7 million for their limited partner and general partner interests in the Legacy Funds.
During the year ended December 31, 2020, certain related parties received distributions from the Company relating to their shares held. Refer to “Note 7 – Stockholder’s Equity” for further details on the Company’s Distribution Reinvestment Plan and the distributions declared.
The Company has entered into indemnification agreements with its directors and executive officers. The indemnification agreements are intended to provide the Company’s directors and executive officers the maximum indemnification permitted under Maryland law and the 1940 Act. Each indemnification agreement provides that the Company shall indemnify the director or executive officer who is a party to the agreement, or an “Indemnitee,” including the advancement of legal expenses, if, by reason of his or her corporate status, the Indemnitee is, or is threatened to be, made a party to or a witness in any threatened, pending, or completed proceeding, to the maximum extent permitted by Maryland law and the 1940 Act.
The Company and its executives and directors are covered by Directors and Officers Insurance, with the directors and officers being indemnified by us to the maximum extent permitted by Maryland law subject to the restrictions of the 1940 Act.
Note 12. Selected Quarterly Data (Unaudited)
The following tables set forth certain quarterly financial information for each of the last four quarters, or since the Company began operations. This information was derived from the Company’s unaudited consolidated financial statements. Results for any quarter are not necessarily indicative of results for the full year or for any further quarter.
| | | | | | | | | ||||
| | | | | | | | | ||||
| | Quarter Ended | | Quarter Ended | | Quarter Ended | | Quarter Ended | ||||
|
| March 31, 2020 |
| June 30, 2020 |
| September 30, 2020 |
| December 31, 2020 | ||||
Total investment income | | $ | 12,248 | | $ | 13,847 | | $ | 13,529 | | $ | 15,340 |
Net investment income | | | 5,708 | | | 6,761 | | | 5,616 | | | 5,286 |
Net increase/(decrease) in net assets resulting from operations | | | (35,051) | | | 6,882 | | | 12,334 | | | 9,723 |
Net increase/(decrease) in net assets resulting from Net Investment income per common share | | $ | 0.32 | | $ | 0.37 | | $ | 0.31 | | $ | 0.29 |
Net increase/(decrease) in net assets resulting from operations per common share | | $ | (1.97) | | $ | 0.38 | | $ | 0.68 | | $ | 0.53 |
141
Note 13. Recent Accounting Pronouncements
In February 2016, the FASB issued ASU 2016-02, Leases (Topic 842) (“ASU 2016-02”) which requires lessees to recognize on the balance sheet a right-of-use asset, representing its right to use the underlying asset for the lease term, and a lease liability for all leases with terms greater than 12 months. The guidance also requires qualitative and quantitative disclosures designed to assess the amount, timing, and uncertainty of cash flows arising from leases. The standard requires the use of a modified retrospective transition approach, which includes a number of optional practical expedients that entities may elect to apply. The guidance is effective for annual periods beginning after December 15, 2020, and interim periods therein. Early adoption is permitted. The Company adopted ASU 2016-02 effective January 1, 2020. Under ASU 2016-02, the Company evaluates leases to determine if the leases are considered financing or operating leases. The Company currently has one operating lease for office space for which the Company recognized a right-of-use asset and a lease liability for the operating lease obligation included in Other assets and Other liabilities, respectively, in the Consolidated Statements of Assets and Liabilities. Non-lease components (maintenance, property tax, insurance and parking) are not included in the lease cost. The lease expense is presented as a single lease cost that is amortized on a straight-line basis over the life of the lease. Refer to “Note 6 – Commitments and Contingencies” for further discussion regarding the lease obligation.
In March 2020, the FASB issued ASU 2020-04, “Reference rate reform (Topic 848) - Facilitation of the effects of reference rate reform on financial reporting.” The amendments in this update provide optional expedients and exceptions for applying U.S. GAAP to certain contracts and hedging relationships that reference LIBOR or another reference rate expected to be discontinued due to reference rate reform and became effective upon issuance for all entities. ASU 2020-04 is elective and is effective on March 12, 2020 through December 31, 2022. The Company does not plan on adopting, as it expects that the adoption of this guidance will not have a material impact on its consolidated financial statements.
In May 2020, the SEC adopted rule amendments that will impact the requirement of investment companies, including BDCs, to disclose the financial statements of certain of their portfolio companies or acquired funds (the “Final Rules”). The Final Rules adopted a new definition of “significant subsidiary” set forth in Rule l-02(w)(2) of Regulation S-X under the Securities Act. Rules 3-09 and 4-08(g) of Regulation S-X require investment companies to include separate financial statements or summary financial information, respectively, in such investment company's periodic reports for any portfolio company that meets the definition of “significant subsidiary.” The Final Rules amend the definition of “significant subsidiary” in a manner that is intended to more accurately capture those portfolio companies that are more likely to materially impact the financial condition of an investment company. The Final Rules were effective on January l, 2021, but voluntary compliance was permitted in advance of the effective date. The Company elected to comply with the Final Rules effective June 30, 2020 which did not have a material impact on the consolidated financial statements.
In August 2020, the FASB issued ASU 2020-06, Debt – Debt with Conversion and Other Options (“ASU 2020-06”) under which the accounting for convertible instruments will be simplified by removing major separation models required under current GAAP. Accordingly, more convertible instruments will be reported as a single liability or equity with no separate accounting for embedded conversion features. Certain settlement conditions that are required for equity contracts to qualify for the derivative scope exception will be removed and, as a result, more equity contracts will qualify for the scope exception. ASU 2020-06 will also simplify the diluted earnings-per-share calculation in certain areas. ASU 2020-06 will be effective for years beginning after December 31, 2021, including interim periods within those fiscal years. Early adoption will be permitted for fiscal periods beginning after December 15, 2020 (including interim periods within the same fiscal year). The Company will early adopt ASU 2020-06 on January 1, 2021, and does not expect the adoption to materially impact the consolidated financial statements other than no longer separately accounting for the embedded conversion feature.
142
Note 14. Subsequent Events
The Company’s management evaluated subsequent events through the date of issuance of the consolidated financial statements included herein. Other than the items below, there have been no subsequent events that occurred during the period that would require recognition or disclosure.
Initial Public Offering
On February 2, 2021, the Company completed its initial public offering of 8,006,291 shares of its common stock at a price of $14.00 per share, inclusive of the underwriters option to purchase additional shares, which was exercised in full. Total net proceeds were approximately $105.4 million. The Company’s shares of common stock began trading on the Nasdaq Global Select Market on January 29, 2021 under the symbol “TRIN.” Proceeds from this offering were primarily used to pay down a portion of existing indebtedness under the Credit Facility.
Credit Facility Paydown
On February 3, 2021, the Company repaid $90.0 million of its existing indebtedness under the Credit Facility using proceeds from its initial public offering. As of March 4, 2021, the Company had $45.0 million in borrowings outstanding under the Credit Facility.
143
Item 9. Changes in and Disagreements with Accountants on Accounting and Financial Disclosure
None.
Item 9A. Controls and Procedures
Evaluation of Disclosure Controls and Procedures
In accordance with Rules 13a-15(b) and 15d-15(b) under the Exchange Act, we, under the supervision and with the participation of our Chief Executive Officer and Chief Financial Officer, carried out an evaluation of the effectiveness of our disclosure controls and procedures (as defined in Rule 13a-15(e) and Rule 15d-15(e) under the Exchange Act) as of the end of the period covered by this annual report on Form 10-K and determined that our disclosure controls and procedures are effective as of the end of the period covered by this annual report on Form 10-K.
Management’s Report on Internal Control Over Financial Reporting
Our management is responsible for establishing and maintaining adequate internal control over financial reporting (as defined in Rules 13a-15(f) and 15d-15(f) of the Exchange Act). Under the supervision and with the participation of management, including the Chief Executive Officer and Chief Financial Officer, we conducted an evaluation of the effectiveness of our internal control over financial reporting based on the criteria established in Internal Control—Integrated Framework (2013) issued by the Committee of Sponsoring Organizations of the Treadway Commission (2013 COSO Framework). Based on our evaluation under the framework in Internal Control—Integrated Framework, management concluded that our internal control over financial reporting was effective as of December 31, 2020.
Because of its inherent limitations, internal control over financial reporting may not prevent or detect misstatements. Also, projections of any evaluation of effectiveness to future periods are subject to the risk that controls may become inadequate because of changes in conditions, or that the degree of compliance with the policies or procedures may deteriorate.
This annual report on Form 10-K does not include an attestation report of the company’s registered public accounting firm pursuant to the rules of the Securities and Exchange Commission.
Changes in Internal Control Over Financial Reporting
There have been no changes in our internal control over financial reporting (as defined in Rules 13a-15(f) and 15d-15(f) under the Exchange Act) that occurred during the year ended December 31, 2020 that have materially affected, or are reasonably likely to materially affect, our internal control over financial reporting.
None.
144
Item 10. Directors, Executive Officers and Corporate Governance
The information required by Item 10 is hereby incorporated by reference from our definitive Proxy Statement relating to our 2021 Annual Meeting of Stockholders, to be filed with the Securities and Exchange Commission within 120 days following the end of our fiscal year.
The Company has adopted a code of business conduct and ethics that applies to directors, officers and employees. The code of business conduct and ethics is available on the Company’s website at www.ir.trincapinvestment.com/governance/governance-documents. The Company will report any amendments to or waivers of a required provision of the code of business conduct and ethics on the Company’s website or in a Current Report on Form 8-K.
Item 11. Executive Compensation
The information required by Item 11 is hereby incorporated by reference from our definitive Proxy Statement relating to our 2021 Annual Meeting of Stockholders, to be filed with the Securities and Exchange Commission within 120 days following the end of our fiscal year.
Item 12. Security Ownership of Certain Beneficial Owners and Management and Related Stockholder Matters
The information required by Item 12 is hereby incorporated by reference from our definitive Proxy Statement relating to our 2021 Annual Meeting of Stockholders, to be filed with the Securities and Exchange Commission within 120 days following the end of our fiscal year.
Item 13. Certain Relationships and Related Transactions and Director Independence
The information required by Item 13 is hereby incorporated by reference from our definitive Proxy Statement relating to our 2021 Annual Meeting of Stockholders, to be filed with the Securities and Exchange Commission within 120 days following the end of our fiscal year.
Item 14. Principal Accountant Fees and Services
The information required by Item 14 is hereby incorporated by reference from our definitive Proxy Statement relating to our 2021 Annual Meeting of Stockholders, to be filed with the Securities and Exchange Commission within 120 days following the end of our fiscal year.
145
Item 15. Exhibits and Financial Statement Schedules
The following financial statements of the “Company” are filed herewith:
Consolidated Statements of Assets and Liabilities as of December 31, 2020 and December 31, 2019 | |
Consolidated Schedule of Investments as of December 31, 2020 | |
The following exhibits are filed as part of this annual report on Form 10-K or hereby incorporated by reference to exhibits previously filed with the SEC:
Exhibit |
| Description of Exhibits |
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
|
146
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
| ||
21.1 | | List of Subsidiaries |
| | Trinity Capital Holdings, LLC (Delaware) |
| | Trinity Funding 1, LLC (Delaware) |
| ||
| ||
| ||
32.1* |
| |
|
147
* Filed herewith.
# Management contract or compensatory plan or arrangement.
Not applicable.
148
Pursuant to the requirements of Section 13 or 15(d) of the Securities Exchange Act of 1934, as amended, the registrant has duly caused this report to be signed on its behalf by the undersigned, thereunto duly authorized.
| TRINITY CAPITAL INC. | |
| | |
Dated: March 4, 2021 | By: | /s/ Steven L. Brown |
| | Steven L. Brown |
| | Chairman and Chief Executive Officer |
| | (Principal Executive Officer) |
| | |
Dated: March 4, 2021 | By: | /s/ David Lund |
| | David Lund |
| | Chief Financial Officer and Treasurer |
| | (Principal Financial and Accounting Officer) |
Each person whose signature appears below constitutes and appoints Steven L. Brown and David Lund, and each of them, such person’s true and lawful attorney-in-act and agent, with full power of substitution and revocation, for such person and in such person’s name, place and stead, in any and all capacities, to sign one or more Annual Reports on Form 10-K for the year ended December 31, 2020, and any and all amendments thereto, and to file same with all exhibits thereto, and other documents in connection therewith, with the Securities and Exchange Commission, granting unto said attorneys-in-fact and agents, and each of them, full power and authority to do and perform each and every act and thing requisite and necessary to be done in connection therewith, as fully to all intents and purposes as such person might or could do in person, hereby ratifying and confirming all that said attorneys-in-fact and agents and each of them, or their or his substitutes, may lawfully do or cause to be done hereof.
Pursuant to the requirements of the Securities Exchange Act of 1934, this Report has been signed below by the following persons on behalf of the Registrant in the capacities on March 4, 2021.
/s/ Steven L. Brown | | /s/ Kyle Brown |
Chairman and Chief Executive Officer | | President and Chief Investment Officer |
| | |
/s/ Richard R. Ward | | /s/ Michael E. Zacharia |
Director | | Director |
| | |
/s/ Edmund G. Zito | | /s/ Ronald E. Estes |
Director | | Director |
149
